FlexVPN is Cisco’s
implementation of the IKEv2 standard featuring a unified paradigm and CLI that
combines site to site, remote access, hub and spoke topologies and partial
meshes (spoke to spoke direct). FlexVPN offers a simple but modular framework
that extensively uses the tunnel interface paradigm while remaining compatible
with legacy VPN implementations using the crypto maps.
The FlexVPN server
provides the server side functionality of FlexVPN. The FlexVPN client
establishes a secure IPsec VPN tunnel between a FlexVPN client and another
FlexVPN server.
NHRP is an Address
Resolution Protocol (ARP)-like protocol that alleviates nonbroadcast
multiaccess (NBMA) network problems. With NHRP, NHRP entities attached to an
NBMA network dynamically learn the NBMA address of the other entities that are
part of that network, allowing these entities to directly communicate without
requiring traffic to use an intermediate hop.
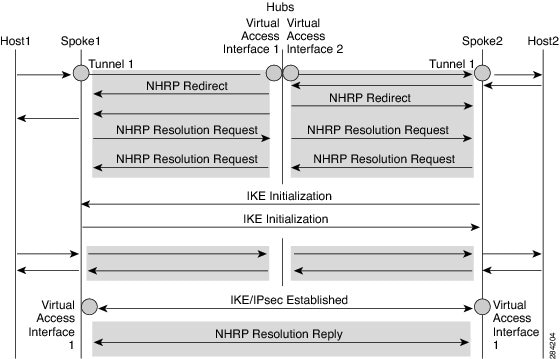
The FlexVPN Spoke to
Spoke feature integrates NHRP and FlexVPN client (spoke) to establish a direct
crypto channel with another client in an existing FlexVPN network. The
connections are built using virtual tunnel interfaces (VTI), IKEv2 and NHRP,
where NHRP is used for resolving the FlexVPN clients in the network.
The following is
recommended in FlexVPN:
- Routing entries are not
exchanged between spokes.
- Different profiles are used
for the spokes and the
config-exchange
command is not configured for the spokes.
The FlexVPN IPv6
Direct Spoke to Spoke feature supports the use of IPv6 addresses for FlexVPN
spokes. The support for IPv6 addresses provides support for IPv6 over IPv4,
IPv4 over IPv6, and IPv6 over IPv6 transports.

Note |
Spoke to Spoke FlexVPN does not support dynamic AAA authorization.
|

 Feedback
Feedback