- Index
- Preface
- Overview
- Using the Command-Line Interface
- Assigning the Switch IP Address and Default Gateway
- Configuring Cisco IOS Configuration Engine
- Administering the Switch
- Configuring Web-Based Authentication
- Clustering Switches
- Managing Switch Stacks
- Configuring SDM Templates
- Configuring Switch-Based Authentication
- Configuring IEEE 802.1x Port-Based Authentication
- Configuring Interface Characteristics
- Configuring VLANs
- Configuring VTP
- Configuring Voice VLAN
- Configuring STP
- Configuring MSTP
- Configuring Optional Spanning-Tree Features
- Configuring Flex Links and the MAC Address-Table Move Update Feature
- Configuring DHCP Features and IP Source Guard
- Configuring Dynamic ARP Inspection
- Configuring IGMP Snooping and MVR
- Configuring Port-Based Traffic Control
- Configuring UDLD
- Configuring CDP
- Configuring LLDP, LLDP-MED, and Wired Location Service
- Configuring SPAN and RSPAN
- Configuring RMON
- Configuring System Message Logging
- Configuring SNMP
- Configuring Cisco IOS IP SLAs Operations
- Configuring Network Security with ACLs
- Configuring QoS
- Configuring Static IP Unicast Routing
- Configuring IPv6 Host
- Configuring IPv6 MLD Snooping
- Configuring EtherChannels and Link-State Tracking
- Troubleshooting
- Configuring Online Diagnostics
- Working with the Cisco IOS File System, Configuration Files, and Software Images
- Supported MIBs
- Unsupported Commands in Cisco IOS Release 12.2(55)SE
- Recommendations for Upgrading a Catalyst 2950 Switch to a Catalyst 2960 Switch
- Understanding ACLs
- Configuring IPv4 ACLs
Configuring Network Security with ACLs
This chapter describes how to configure network security on the Catalyst 2960 and 2960-S switches by using access control lists (ACLs), also referred to as access lists. Unless otherwise noted, the term switch refers to a standalone switch and a switch stack.

Note![]() Stacking is supported only on Catalyst 2960-S switches running the LAN base image.
Stacking is supported only on Catalyst 2960-S switches running the LAN base image.

Note![]() If the switch is running the LAN Lite image, you can configure ACLs, but you cannot attach them to physical interfaces. When it is running either the LAN Lite or LAN base image, you can attach ACLs to VLAN interfaces to filter traffic to the CPU.
If the switch is running the LAN Lite image, you can configure ACLs, but you cannot attach them to physical interfaces. When it is running either the LAN Lite or LAN base image, you can attach ACLs to VLAN interfaces to filter traffic to the CPU.
In this chapter, references to IP ACLs are specific to IP Version 4 (IPv4) ACLs.
For complete syntax and usage information for the commands used in this chapter, see the command reference for this release, the “Configuring IP Services” section in the “IP Addressing and Services” chapter of the Cisco IOS IP Configuration Guide, Release 12.2, and the Cisco IOS IP Command Reference, Volume 1 of 3: Addressing and Services, Release 12.2. The Cisco IOS documentation is available from the Cisco.com page under Documentation > Cisco IOS Software > 12.2 Mainline > Configuration Guides or Command References.
Understanding ACLs
Packet filtering can help limit network traffic and restrict network use by certain users or devices. ACLs filter traffic as it passes through a switch and permit or deny packets crossing specified interfaces. An ACL is a sequential collection of permit and deny conditions that apply to packets. When a packet is received on an interface, the switch compares the fields in the packet against any applied ACLs to verify that the packet has the required permissions to be forwarded, based on the criteria specified in the access lists. One by one, it tests packets against the conditions in an access list. The first match decides whether the switch accepts or rejects the packets. Because the switch stops testing after the first match, the order of conditions in the list is critical. If no conditions match, the switch rejects the packet. If there are no restrictions, the switch forwards the packet; otherwise, the switch drops the packet. The switch can use ACLs on all packets it forwards.
You configure access lists on a switch to provide basic security for your network. If you do not configure ACLs, all packets passing through the switch could be allowed onto all parts of the network. You can use ACLs to control which hosts can access different parts of a network or to decide which types of traffic are forwarded or blocked. For example, you can allow e-mail traffic to be forwarded but not Telnet traffic.
An ACL contains an ordered list of access control entries (ACEs). Each ACE specifies permit or deny and a set of conditions the packet must satisfy in order to match the ACE. The meaning of permit or deny depends on the context in which the ACL is used.
The switch supports IP ACLs and Ethernet (MAC) ACLs:
- IP ACLs filter IPv4 traffic, including TCP, User Datagram Protocol (UDP), Internet Group Management Protocol (IGMP), and Internet Control Message Protocol (ICMP).
- Ethernet ACLs filter non-IP traffic.

Note![]() MAC ACLs are supported only when the switch is running the LAN base image.
MAC ACLs are supported only when the switch is running the LAN base image.
This switch also supports quality of service (QoS) classification ACLs. For more information, see the “Classification Based on QoS ACLs” section.
These sections contain this conceptual information:
Supported ACLs
- Port ACLs access-control traffic entering a Layer 2 interface. The switch does not support port ACLs in the outbound direction. You can apply only one IP access list and one MAC access list to a Layer 2 interface. For more information, see the “Port ACLs” section.
- Router ACLs access-control routed traffic between VLANs and are applied to Layer 3 interfaces in a specific direction (inbound or outbound). For more information, see the “Router ACLs” section.

Note![]() Router ACLs are supported only on SVIs.
Router ACLs are supported only on SVIs.
You can use input port ACLs and router ACLs on the same switch. However, a port ACL takes precedence over a router ACL.
- When an input router ACL and input port ACL exist in a switch virtual interface (SVI), incoming packets received on ports to which a port ACL is applied are filtered by the port ACL. Incoming routed IP packets received on other ports are filtered by the router ACL. Other packets are not filtered.
- When an output router ACL and input port ACL exist in an SVI, incoming packets received on the ports to which a port ACL is applied are filtered by the port ACL. Outgoing routed IP packets are filtered by the router ACL. Other packets are not filtered.
Port ACLs
Port ACLs are ACLs that are applied to Layer 2 interfaces on a switch. Port ACLs are supported only on physical interfaces and not on EtherChannel interfaces and can be applied only on interfaces in the inbound direction. These access lists are supported:
- Standard IP access lists using source addresses
- Extended IP access lists using source and destination addresses and optional protocol type information
- MAC extended access lists using source and destination MAC addresses and optional protocol type information

Note![]() MAC ACLs are supported only when the switch is running the LAN base image.
MAC ACLs are supported only when the switch is running the LAN base image.
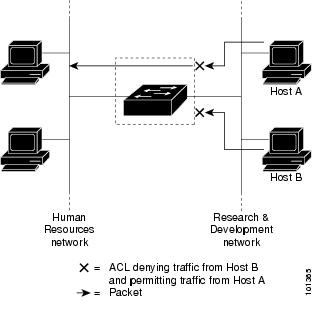
The switch examines ACLs associated with all inbound features configured on a given interface and permits or denies packet forwarding based on how the packet matches the entries in the ACL. In this way, ACLs control access to a network or to part of a network. Figure 1-1 is an example of using port ACLs to control access to a network when all workstations are in the same VLAN. ACLs applied at the Layer 2 input would allow Host A to access the Human Resources network, but prevent Host B from accessing the same network. Port ACLs can only be applied to Layer 2 interfaces in the inbound direction.
Figure 1-1 Using ACLs to Control Traffic to a Network
When you apply a port ACL to a trunk port, the ACL filters traffic on all VLANs present on the trunk port. When you apply a port ACL to a port with voice VLAN, the ACL filters traffic on both data and voice VLANs.
With port ACLs, you can filter IP traffic by using IP access lists and non-IP traffic by using MAC addresses. You can filter both IP and non-IP traffic on the same Layer 2 interface by applying both an IP access list and a MAC access list to the interface.

Note![]() You cannot apply more than one IP access list and one MAC access list to a Layer 2 interface. If an IP access list or MAC access list is already configured on a Layer 2 interface and you apply a new IP access list or MAC access list to the interface, the new ACL replaces the previously configured one.
You cannot apply more than one IP access list and one MAC access list to a Layer 2 interface. If an IP access list or MAC access list is already configured on a Layer 2 interface and you apply a new IP access list or MAC access list to the interface, the new ACL replaces the previously configured one.
Router ACLs
You can apply router ACLs on switch virtual interfaces (SVIs), which are Layer 3 interfaces to VLANs. You apply router ACLs on interfaces for specific directions (inbound or outbound). You can apply one router ACL in each direction on an interface.
An ACL can be used with multiple features for a given interface, and one feature can use multiple ACLs. When a single router ACL is used by multiple features, it is examined multiple times.
Supported access lists for IPv4 traffic:
- Standard IP access lists use source addresses for matching operations.
- Extended IP access lists use source and destination addresses and optional protocol information for matching operations.
As with port ACLs, the switch examines ACLs associated with features configured on a given interface. However, you can apply only inbound port ACLs, while router ACLs are supported in both directions. As packets enter the switch on an interface, ACLs associated with all inbound features configured on that interface are examined. After packets are routed and before they are forwarded to the next hop, all ACLs associated with outbound features configured on the egress interface are examined.
ACLs permit or deny packet forwarding based on how the packet matches the entries in the ACL and can be used to control access to a network or to part of a network. In Figure 1-1, ACLs applied at the router input allow Host A to access the Human Resources network but prevent Host B from accessing the same network.
Handling Fragmented and Unfragmented Traffic
IP packets can be fragmented as they cross the network. When this happens, only the fragment containing the beginning of the packet contains the Layer 4 information, such as TCP or UDP port numbers, ICMP type and code, and so on. All other fragments are missing this information.
Some ACEs do not check Layer 4 information and therefore can be applied to all packet fragments. ACEs that do test Layer 4 information cannot be applied in the standard manner to most of the fragments in a fragmented IP packet. When the fragment contains no Layer 4 information and the ACE tests some Layer 4 information, the matching rules are modified:
- Permit ACEs that check the Layer 3 information in the fragment (including protocol type, such as TCP, UDP, and so on) are considered to match the fragment regardless of what the missing Layer 4 information might have been.
- Deny ACEs that check Layer 4 information never match a fragment unless the fragment contains Layer 4 information.
Consider access list 102, configured with these commands, applied to three fragmented packets:

Note![]() In the first and second ACEs in the examples, the eq keyword after the destination address means to test for the TCP-destination-port well-known numbers equaling Simple Mail Transfer Protocol (SMTP) and Telnet, respectively.
In the first and second ACEs in the examples, the eq keyword after the destination address means to test for the TCP-destination-port well-known numbers equaling Simple Mail Transfer Protocol (SMTP) and Telnet, respectively.
- Packet A is a TCP packet from host 10.2.2.2., port 65000, going to host 10.1.1.1 on the SMTP port. If this packet is fragmented, the first fragment matches the first ACE (a permit) as if it were a complete packet because all Layer 4 information is present. The remaining fragments also match the first ACE, even though they do not contain the SMTP port information, because the first ACE only checks Layer 3 information when applied to fragments. The information in this example is that the packet is TCP and that the destination is 10.1.1.1.
- Packet B is from host 10.2.2.2, port 65001, going to host 10.1.1.2 on the Telnet port. If this packet is fragmented, the first fragment matches the second ACE (a deny) because all Layer 3 and Layer 4 information is present. The remaining fragments in the packet do not match the second ACE because they are missing Layer 4 information. Instead, they match the third ACE (a permit).
Because the first fragment was denied, host 10.1.1.2 cannot reassemble a complete packet, so packet B is effectively denied. However, the later fragments that are permitted will consume bandwidth on the network and resources of host 10.1.1.2 as it tries to reassemble the packet.
- Fragmented packet C is from host 10.2.2.2, port 65001, going to host 10.1.1.3, port ftp. If this packet is fragmented, the first fragment matches the fourth ACE (a deny). All other fragments also match the fourth ACE because that ACE does not check any Layer 4 information and because Layer 3 information in all fragments shows that they are being sent to host 10.1.1.3, and the earlier permit ACEs were checking different hosts.
ACLs and Switch Stacks

Note![]() Stacking is supported only on Catalyst 2960-S switches running the LAN base image.
Stacking is supported only on Catalyst 2960-S switches running the LAN base image.
ACL support is the same for a switch stack as for a standalone switch. ACL configuration information is propagated to all switches in the stack. All switches in the stack, including the stack master, process the information and program their hardware. (For information about switch stacks, see Chapter1, “Configuring the Switch Stack”)
The stack master performs these ACL functions:
- It processes the ACL configuration and propagates the information to all stack members.
- It distributes the ACL information to any switch that joins the stack.
- If packets must be forwarded by software for any reason (for example, not enough hardware resources), the master switch forwards the packets only after applying ACLs on the packets.
- It programs its hardware with the ACL information it processes.
Stack members perform these ACL functions:
- They receive the ACL information from the master switch and program their hardware.
- They act as standby switches, ready to take over the role of the stack master if the existing master were to fail and they were to be elected as the new stack master.
When a stack master fails and a new stack master is elected, the newly elected master reparses the backed up running configuration. (See Chapter1, “Configuring the Switch Stack”) The ACL configuration that is part of the running configuration is also reparsed during this step. The new stack master distributes the ACL information to all switches in the stack.
Configuring IPv4 ACLs

Note![]() If the switch is running the LAN Lite image, you can configure ACLs, but you cannot attach them to physical interfaces. When running either the LAN Lite or LAN base image, you can attach ACLs to VLAN interfaces to filter traffic to the CPU.
If the switch is running the LAN Lite image, you can configure ACLs, but you cannot attach them to physical interfaces. When running either the LAN Lite or LAN base image, you can attach ACLs to VLAN interfaces to filter traffic to the CPU.
Configuring IP v4ACLs on the switch is the same as configuring IPv4 ACLs on other Cisco switches and routers. The process is briefly described here. For more detailed information on configuring ACLs, see the “Configuring IP Services” section in the “IP Addressing and Services” chapter of the Cisco IOS IP Configuration Guide, Release 12.2. For detailed information about the commands, see the Cisco IOS IP Command Reference, Volume 1 of 3: Addressing and Services, Release 12.2. The Cisco IOS documentation is available from the Cisco.com page under Documentation > Cisco IOS Software > 12.2 Mainline > Configuration Guides or Command References.
The switch does not support these Cisco IOS router ACL-related features:
- Non-IP protocol ACLs (see Table 1-1) or bridge-group ACLs
- IP accounting
- Inbound and outbound rate limiting (except with QoS ACLs)
- Reflexive ACLs or dynamic ACLs (except for some specialized dynamic ACLs used by the switch clustering feature)
- ACL logging
These are the steps to use IP ACLs on the switch:
Step 1![]() Create an ACL by specifying an access list number or name and the access conditions.
Create an ACL by specifying an access list number or name and the access conditions.
Step 2![]() Apply the ACL to interfaces or terminal lines.
Apply the ACL to interfaces or terminal lines.
These sections contain this configuration information:
- Creating Standard and Extended IPv4 ACLs
- Applying an IPv4 ACL to a Terminal Line
- Applying an IPv4 ACL to an Interface
- Hardware and Software Treatment of IP ACLs
- Troubleshooting ACLs
- IPv4 ACL Configuration Examples
Creating Standard and Extended IPv4 ACLs
This section describes IP ACLs. An ACL is a sequential collection of permit and deny conditions. One by one, the switch tests packets against the conditions in an access list. The first match determines whether the switch accepts or rejects the packet. Because the switch stops testing after the first match, the order of the conditions is critical. If no conditions match, the switch denies the packet.
The software supports these types of ACLs or access lists for IPv4:
- Standard IP access lists use source addresses for matching operations.
- Extended IP access lists use source and destination addresses for matching operations and optional protocol-type information for finer granularity of control.
These sections describe access lists and how to create them:
Access List Numbers
The number you use to denote your ACL shows the type of access list that you are creating. Table 1-1 lists the access-list number and corresponding access list type and shows whether or not they are supported in the switch. The switch supports IPv4 standard and extended access lists, numbers 1 to 199 and 1300 to 2699.
|
|
|
|
|---|---|---|

Note![]() In addition to numbered standard and extended ACLs, you can also create standard and extended named IP ACLs by using the supported numbers. That is, the name of a standard IP ACL can be 1 to 99; the name of an extended IP ACL can be 100 to 199. The advantage of using named ACLs instead of numbered lists is that you can delete individual entries from a named list.
In addition to numbered standard and extended ACLs, you can also create standard and extended named IP ACLs by using the supported numbers. That is, the name of a standard IP ACL can be 1 to 99; the name of an extended IP ACL can be 100 to 199. The advantage of using named ACLs instead of numbered lists is that you can delete individual entries from a named list.
Creating a Numbered Standard ACL
Beginning in privileged EXEC mode, follow these steps to create a numbered standard ACL:
Use the no access-list access-list-number global configuration command to delete the entire ACL. You cannot delete individual ACEs from numbered access lists.

Note![]() When creating an ACL, remember that, by default, the end of the ACL contains an implicit deny statement for all packets that it did not find a match for before reaching the end. With standard access lists, if you omit the mask from an associated IP host address ACL specification, 0.0.0.0 is assumed to be the mask.
When creating an ACL, remember that, by default, the end of the ACL contains an implicit deny statement for all packets that it did not find a match for before reaching the end. With standard access lists, if you omit the mask from an associated IP host address ACL specification, 0.0.0.0 is assumed to be the mask.
This example shows how to create a standard ACL to deny access to IP host 171.69.198.102, permit access to any others, and display the results.
The switch always rewrites the order of standard access lists so that entries with host matches and entries with matches having a don’t care mask of 0.0.0.0 are moved to the top of the list, above any entries with non-zero don’t care masks. Therefore, in show command output and in the configuration file, the ACEs do not necessarily appear in the order in which they were entered.
After creating a numbered standard IPv4 ACL, you can apply it to terminal lines (see the “Applying an IPv4 ACL to a Terminal Line” section) and to interfaces (see the “Applying an IPv4 ACL to an Interface” section).
Creating a Numbered Extended ACL
Although standard ACLs use only source addresses for matching, you can use extended ACL source and destination addresses for matching operations and optional protocol type information for finer granularity of control. When you are creating ACEs in numbered extended access lists, remember that after you create the ACL, any additions are placed at the end of the list. You cannot reorder the list or selectively add or remove ACEs from a numbered list.
Some protocols also have specific parameters and keywords that apply to that protocol.
These IP protocols are supported (protocol keywords are in parentheses in bold):
Authentication Header Protocol (ahp), Enhanced Interior Gateway Routing Protocol (eigrp), Encapsulation Security Payload (esp), generic routing encapsulation (gre), Internet Control Message Protocol (icmp), Internet Group Management Protocol (igmp), any Interior Protocol (ip), IP in IP tunneling (ipinip), KA9Q NOS-compatible IP over IP tunneling (nos), Open Shortest Path First routing (ospf), Payload Compression Protocol (pcp), Protocol Independent Multicast (pim), Transmission Control Protocol (tcp), or User Datagram Protocol (udp).

Note![]() ICMP echo-reply cannot be filtered. All other ICMP codes or types can be filtered.
ICMP echo-reply cannot be filtered. All other ICMP codes or types can be filtered.
For more details on the specific keywords for each protocol, see these command references:
- Cisco IOS IP Command Reference, Volume 1 of 3: Addressing and Services, Release 12.2
- Cisco IOS IP Command Reference, Volume 2 of 3: Routing Protocols, Release 12.2
- Cisco IOS IP Command Reference, Volume 3 of 3: Multicast, Release 12.2
These documents are available from the Cisco.com page under Documentation > Cisco IOS Software > 12.2 Mainline > Command References.

Note![]() The switch does not support dynamic or reflexive access lists. It also does not support filtering based on the type of service (ToS) minimize-monetary-cost bit.
The switch does not support dynamic or reflexive access lists. It also does not support filtering based on the type of service (ToS) minimize-monetary-cost bit.
Supported parameters can be grouped into these categories: TCP, UDP, ICMP, IGMP, or other IP.
Beginning in privileged EXEC mode, follow these steps to create an extended ACL:
|
|
|
|
|---|---|---|
access-list access-list-number Note If you enter a dscp value, you cannot enter tos or precedence. You can enter both a tos and a precedence value with no dscp. |
Define an extended IPv4 access list and the access conditions. The access-list-number is a decimal number from 100 to 199 or 2000 to 2699. Enter deny or permit to specify whether to deny or permit the packet if conditions are matched. For protocol, enter the name or number of an IP protocol: ahp, eigrp, esp, gre, icmp, igmp, igrp, ip, ipinip, nos, ospf, pcp, pim, tcp, or udp, or an integer in the range 0 to 255 representing an IP protocol number. To match any Internet protocol (including ICMP, TCP, and UDP), use the keyword ip. Note This step includes options for most IP protocols. For additional specific parameters for TCP, UDP, ICMP, and IGMP, see steps 2b through 2e. The source is the number of the network or host from which the packet is sent. The source-wildcard applies wildcard bits to the source. The destination is the network or host number to which the packet is sent. The destination-wildcard applies wildcard bits to the destination. Source, source-wildcard, destination, and destination-wildcard can be specified as:
The other keywords are optional and have these meanings:
|
|
access-list access-list-number { deny | permit } protocol any any [ precedence precedence ] [ tos tos ] [ fragments ] [ time-range time-range-name ] [ dscp dscp ] |
In access-list configuration mode, define an extended IP access list using an abbreviation for a source and source wildcard of 0.0.0.0 255.255.255.255 and an abbreviation for a destination and destination wildcard of 0.0.0.0 255.255.255.255. You can use the any keyword in place of source and destination address and wildcard. |
|
access-list access-list-number { deny | permit } protocol |
Define an extended IP access list by using an abbreviation for a source and a source wildcard of source 0.0.0.0 and an abbreviation for a destination and destination wildcard of destination 0.0.0.0. You can use the host keyword in place of the source and destination wildcard or mask. |
|
access-list access-list-number |
(Optional) Define an extended TCP access list and the access conditions. Enter tcp for Transmission Control Protocol. The parameters are the same as those described in Step 2a, with these exceptions: (Optional) Enter an operator and port to compare source (if positioned after source source-wildcard) or destination (if positioned after destination destination-wildcard) port. Possible operators include eq (equal), gt (greater than), lt (less than), neq (not equal), and range (inclusive range). Operators require a port number (range requires two port numbers separated by a space). Enter the port number as a decimal number (from 0 to 65535) or the name of a TCP port. To see TCP port names, use the ? or see the “Configuring IP Services” section in the “IP Addressing and Services” chapter of the Cisco IOS IP Configuration Guide, Release 12.2. Use only TCP port numbers or names when filtering TCP. |
|
access-list access-list-number |
(Optional) Define an extended UDP access list and the access conditions. Enter udp for the User Datagram Protocol. The UDP parameters are the same as those described for TCP except that the [ operator [ port ]] port number or name must be a UDP port number or name, and the flag and established parameters are not valid for UDP. |
|
access-list access-list-number |
(Optional) Define an extended ICMP access list and the access conditions. Enter icmp for Internet Control Message Protocol. The ICMP parameters are the same as those described for most IP protocols in Step 2a, with the addition of the ICMP message type and code parameters. These optional keywords have these meanings:
|
|
access-list access-list-number |
(Optional) Define an extended IGMP access list and the access conditions. Enter igmp for Internet Group Management Protocol. The IGMP parameters are the same as those described for most IP protocols in Step 2a, with this optional parameter. igmp-type —To match IGMP message type, enter a number from 0 to 15, or enter the message name (dvmrp, host-query, host-report, pim, or trace). |
|
Use the no access-list access-list-number global configuration command to delete the entire access list. You cannot delete individual ACEs from numbered access lists.
This example shows how to create and display an extended access list to deny Telnet access from any host in network 171.69.198.0 to any host in network 172.20.52.0 and to permit any others. (The eq keyword after the destination address means to test for the TCP destination port number equaling Telnet.)
Switch(config)# access-list 102 deny tcp 171.69.198.0 0.0.0.255 172.20.52.0 0.0.0.255 eq telnet
Switch(config)# access-list 102 permit tcp any any
After an ACL is created, any additions (possibly entered from the terminal) are placed at the end of the list. You cannot selectively add or remove access list entries from a numbered access list.

Note![]() When you are creating an ACL, remember that, by default, the end of the access list contains an implicit deny statement for all packets if it did not find a match before reaching the end.
When you are creating an ACL, remember that, by default, the end of the access list contains an implicit deny statement for all packets if it did not find a match before reaching the end.
After creating a numbered extended ACL, you can apply it to terminal lines (see the “Applying an IPv4 ACL to a Terminal Line” section), to interfaces (see the “Applying an IPv4 ACL to an Interface” section).
Resequencing ACEs in an ACL
Sequence numbers for the entries in an access list are automatically generated when you create a new ACL. You can use the ip access-list resequence global configuration command to edit the sequence numbers in an ACL and change the order in which ACEs are applied. For example, if you add a new ACE to an ACL, it is placed at the bottom of the list. By changing the sequence number, you can move the ACE to a different position in the ACL.
For information about the ip access-list resequence command:
http://www.cisco.com/en/US/docs/ios/12_2s/feature/guide/fsaclseq.html#wp1027188
Creating Named Standard and Extended ACLs
You can identify IPv4 ACLs with an alphanumeric string (a name) rather than a number. You can use named ACLs to configure more IPv4 access lists in a router than if you were to use numbered access lists. If you identify your access list with a name rather than a number, the mode and command syntax are slightly different. However, not all commands that use IP access lists accept a named access list.

Note![]() The name you give to a standard or extended ACL can also be a number in the supported range of access list numbers. That is, the name of a standard IP ACL can be 1 to 99; the name of an extended IP ACL can be 100 to 199. The advantage of using named ACLs instead of numbered lists is that you can delete individual entries from a named list.
The name you give to a standard or extended ACL can also be a number in the supported range of access list numbers. That is, the name of a standard IP ACL can be 1 to 99; the name of an extended IP ACL can be 100 to 199. The advantage of using named ACLs instead of numbered lists is that you can delete individual entries from a named list.
Consider these guidelines and limitations before configuring named ACLs:
- Not all commands that accept a numbered ACL accept a named ACL. ACLs for packet filters and route filters on interfaces can use a name.
- A standard ACL and an extended ACL cannot have the same name.
- Numbered ACLs are also available, as described in the “Creating Standard and Extended IPv4 ACLs” section.
Beginning in privileged EXEC mode, follow these steps to create a standard ACL using names:
To remove a named standard ACL, use the no ip access-list standard name global configuration command.
Beginning in privileged EXEC mode, follow these steps to create an extended ACL using names:
|
|
|
|
|---|---|---|
Define an extended IPv4 access list using a name, and enter access-list configuration mode. |
||
{ deny | permit } protocol { source [ source-wildcard ] | host source | any } { destination [ destination-wildcard ] | host destination | any } [ precedence precedence ] [ tos tos ] [ established ] [ time-range time-range-name ] |
In access-list configuration mode, specify the conditions allowed or denied. See the “Creating a Numbered Extended ACL” section for definitions of protocols and other keywords. |
|
To remove a named extended ACL, use the no ip access-list extended name global configuration command.
When you are creating standard extended ACLs, remember that, by default, the end of the ACL contains an implicit deny statement for everything if it did not find a match before reaching the end. For standard ACLs, if you omit the mask from an associated IP host address access list specification, 0.0.0.0 is assumed to be the mask.
After you create an ACL, any additions are placed at the end of the list. You cannot selectively add ACL entries to a specific ACL. However, you can use no permit and no deny access-list configuration mode commands to remove entries from a named ACL. This example shows how you can delete individual ACEs from the named access list border-list :
Being able to selectively remove lines from a named ACL is one reason you might use named ACLs instead of numbered ACLs.
After creating a named ACL, you can apply it to interfaces (see the “Applying an IPv4 ACL to an Interface” section).
Using Time Ranges with ACLs
You can selectively apply extended ACLs based on the time of day and the week by using the time-range global configuration command. First, define a time-range name and set the times and the dates or the days of the week in the time range. Then enter the time-range name when applying an ACL to set restrictions to the access list. You can use the time range to define when the permit or deny statements in the ACL are in effect, for example, during a specified time period or on specified days of the week. The time-range keyword and argument are referenced in the named and numbered extended ACL task tables in the previous sections, the “Creating Standard and Extended IPv4 ACLs” section, and the “Creating Named Standard and Extended ACLs” section.
Time-based access lists trigger CPU activity because the new configuration of the access list must be merged with other features and the combined configuration loaded into the TCAM. For this reason, you should be careful not to have several access lists configured to take affect in close succession (within a small number of minutes of each other.)

Note![]() The time range relies on the switch system clock; therefore, you need a reliable clock source. We recommend that you use Network Time Protocol (NTP) to synchronize the switch clock. For more information, see the “Managing the System Time and Date” section.
The time range relies on the switch system clock; therefore, you need a reliable clock source. We recommend that you use Network Time Protocol (NTP) to synchronize the switch clock. For more information, see the “Managing the System Time and Date” section.
Beginning in privileged EXEC mode, follow these steps to configure a time-range parameter for an ACL:
Repeat the steps if you have multiple items that you want in effect at different times.
To remove a configured time-range limitation, use the no time-range time-range-name global configuration command.
This example shows how to configure time ranges for workhours and to configure January 1, 2006, as a company holiday and to verify your configuration.
To apply a time range, enter the time-range name in an extended ACL that can implement time ranges.
This example shows how to create and verify extended access list 188 that denies TCP traffic from any source to any destination during the defined holiday times and permits all TCP traffic during work hours.
This example uses named ACLs to permit and deny the same traffic.
Including Comments in ACLs
You can use the remark keyword to include comments (remarks) about entries in any IP standard or extended ACL. The remarks make the ACL easier for you to understand and scan. Each remark line is limited to 100 characters.
The remark can go before or after a permit or deny statement. You should be consistent about where you put the remark so that it is clear which remark describes which permit or deny statement. For example, it would be confusing to have some remarks before the associated permit or deny statements and some remarks after the associated statements.
To include a comment for IP numbered standard or extended ACLs, use the access-list access-list number remark remark global configuration command. To remove the remark, use the no form of this command.
In this example, the workstation that belongs to Jones is allowed access, and the workstation that belongs to Smith is not allowed access:
For an entry in a named IP ACL, use the remark access-list configuration command. To remove the remark, use the no form of this command.
In this example, the Jones subnet is not allowed to use outbound Telnet:
Applying an IPv4 ACL to a Terminal Line
You can use numbered ACLs to control access to one or more terminal lines. You cannot apply named ACLs to lines. You must set identical restrictions on all the virtual terminal lines because a user can attempt to connect to any of them.
For procedures for applying ACLs to interfaces, see the “Applying an IPv4 ACL to an Interface” section.
Beginning in privileged EXEC mode, follow these steps to restrict incoming and outgoing connections between a virtual terminal line and the addresses in an ACL:
To remove an ACL from a terminal line, use the no access-class access-list-number { in | out } line configuration command.
Applying an IPv4 ACL to an Interface
- Apply an ACL only to inbound Layer 2 ports.
- Apply an ACL to either inbound or outbound VLAN interfaces to filter packets that are intended for the CPU, such as SNMP, Telnet, or web traffic. IPv4 ACLs applied to VLAN interfaces provide switch management security by limiting access to a specific host in the network or to specific applications (SNMP, Telnet, SSH, and so on). ACLs attached to VLAN interfaces do not impact the hardware switching of packets on the VLAN.

Note![]() On switches running the LAN Lite image, you can apply ACLs only to VLAN interfaces and not to physical interfaces.
On switches running the LAN Lite image, you can apply ACLs only to VLAN interfaces and not to physical interfaces.
- Apply an ACL to either outbound or inbound Layer 3 SVIs.
- When controlling access to an interface, you can use a named or numbered ACL.
- If you apply an ACL to a port that is a member of a VLAN, the port ACL takes precedence over an ACL applied to the VLAN interface.
- If you apply an ACL to a Layer 2 interface that is a member of a VLAN, the Layer 2 (port) ACL takes precedence over an input Layer 3 ACL applied to the VLAN interface. The port ACL always filters incoming packets received on the Layer 2 port.
- If you apply an ACL to a Layer 3 interface and routing is not enabled, the ACL only filters packets that are intended for the CPU, such as SNMP, Telnet, or web traffic. You do not have to enable routing to apply ACLs to Layer 2 interfaces.
- When you configure an egress ACL to permit traffic with a particular DSCP value, you must use the original DSCP value instead of a rewritten value.
Beginning in privileged EXEC mode, follow these steps to control access to an interface:
To remove the specified access group, use the no ip access-group { access-list-number | name } { in | out } interface configuration command.
This example shows how to apply access list 2 to a port to filter packets entering the port:
This example shows how to apply access list 3 to filter packets going to the CPU:

Note![]() When you apply the ip access-group interface configuration command to a Layer 3 SVI, the interface must have an IP address. Layer 3 access groups filter packets that are routed or are received by Layer 3 processes on the CPU.
When you apply the ip access-group interface configuration command to a Layer 3 SVI, the interface must have an IP address. Layer 3 access groups filter packets that are routed or are received by Layer 3 processes on the CPU.
For inbound ACLs, after receiving a packet, the switch checks the packet against the ACL. If the ACL permits the packet, the switch continues to process the packet. If the ACL rejects the packet, the switch discards the packet.
For outbound ACLs, after receiving and sending a packet to a controlled interface, the switch checks the packet against the ACL. If the ACL permits the packet, the switch sends the packet. If the ACL rejects the packet, the switch discards the packet.
When you apply an undefined ACL to an interface, the switch acts as if the ACL has not been applied to the interface and permits all packets. Remember this behavior if you use undefined ACLs for network security.
Hardware and Software Treatment of IP ACLs
ACL processing is primarily accomplished in hardware, but requires forwarding of some traffic flows to the CPU for software processing. If the hardware reaches its capacity to store ACL configurations, packets are sent to the CPU for forwarding. The forwarding rate for software-forwarded traffic is substantially less than for hardware-forwarded traffic.
If ACLs cause large numbers of packets to be sent to the CPU, the switch performance can be negatively affected.
When you enter the show ip access-lists privileged EXEC command, the match count displayed does not account for packets that are access controlled in hardware. Use the show access-lists hardware counters privileged EXEC command to obtain some basic hardware ACL statistics for switched packets.
Troubleshooting ACLs
If this ACL manager message appears and [chars] is the access-list name,
The switch has insufficient resources to create a hardware representation of the ACL. The resources include hardware memory and label space but not CPU memory. A lack of available logical operation units or specialized hardware resources causes this problem. Logical operation units are needed for a TCP flag match or a test other than eq (ne, gt, lt, or range) on TCP, UDP, or SCTP port numbers.
- Modify the ACL configuration to use fewer resources.
- Rename the ACL with a name or number that alphanumerically precedes the ACL names or numbers.
To determine the specialized hardware resources, enter the show platform layer4 acl map privileged EXEC command. If the switch does not have available resources, the output shows that index 0 to index 15 are not available.
For more information about configuring ACLs with insufficient resources, see CSCsq63926 in the Bug Toolkit.
For example, if you apply this ACL to an interface:
The flag-related operators are not available. To avoid this issue,
- Move the fourth ACE before the first ACE by using ip access-list resequence global configuration command:
or
Rename the ACL with a name or number that alphanumerically precedes the other ACLs (for example, rename ACL 79 to ACL 1).
You can now apply the first ACE in the ACL to the interface. The switch allocates the ACE to available mapping bits in the Opselect index and then allocates flag-related operators to use the same bits in the TCAM.
IPv4 ACL Configuration Examples
This section provides examples of configuring and applying IPv4 ACLs. For detailed information about compiling ACLs, see the Cisco IOS Security Configuration Guide, Release 12.2 and to the Configuring IP Services” section in the “IP Addressing and Services” chapter of the Cisco IOS IP Configuration Guide, Release 12.2.
This example uses a standard ACL to allow a port access to a specific Internet host with the address 172.20.128.64.
This example uses an extended ACL to deny to a port traffic coming from port 80 (HTTP). It permits all other types of traffic.
Numbered ACLs
This ACL accepts addresses on network 36.0.0.0 subnets and denies all packets coming from 56.0.0.0 subnets. The ACL is applied to packets entering a port.
Extended ACLs
In this example, suppose that you have a network connected to the Internet, and you want any host on the network to be able to form TCP connections to any host on the Internet. However, you do not want IP hosts to be able to form TCP connections to hosts on your network, except to the mail (SMTP) port of a dedicated mail host.
SMTP uses TCP port 25 on one end of the connection and a random port number on the other end. The same port numbers are used throughout the life of the connection. Mail packets coming in from the Internet have a destination port of 25. Because the secure system of the network always accepts mail connections on port 25, the incoming services are controlled.
Named ACLs
This example creates an extended ACL named marketing_group. The marketing_group ACL allows any TCP Telnet traffic to the destination address and wildcard 171.69.0.0 0.0.255.255 and denies any other TCP traffic. It permits any other IP traffic.
The marketing_group ACL is applied to incoming traffic on a port.
Time Range Applied to an IP ACL
This example denies HTTP traffic on IP on Monday through Friday between the hours of 8:00 a.m. and 6:00 p.m (18:00). The example allows UDP traffic only on Saturday and Sunday from noon to 8:00 p.m. (20:00).
Commented IP ACL Entries
In this example of a numbered ACL, the workstation that belongs to Jones is allowed access, and the workstation that belongs to Smith is not allowed access:
In this example of a numbered ACL, the Winter and Smith workstations are not allowed to browse the web:
In this example of a named ACL, the Jones subnet is not allowed access:
In this example of a named ACL, the Jones subnet is not allowed to use outbound Telnet:
Creating Named MAC Extended ACLs
You can filter non-IPv4 traffic on a VLAN or on a Layer 2 interface by using MAC addresses and named MAC extended ACLs. The procedure is similar to that of configuring other extended named ACLs.

Note![]() MAC ACLs are supported only when the switch is running the LAN base image.
MAC ACLs are supported only when the switch is running the LAN base image.
For more information about the supported non-IP protocols in the mac access-list extended command, see the command reference for this release.

Note![]() Though visible in the command-line help strings, appletalk is not supported as a matching condition for the deny and permit MAC access-list configuration mode commands.
Though visible in the command-line help strings, appletalk is not supported as a matching condition for the deny and permit MAC access-list configuration mode commands.
Beginning in privileged EXEC mode, follow these steps to create a named MAC extended ACL:
Use the no mac access-list extended name global configuration command to delete the entire ACL. You can also delete individual ACEs from named MAC extended ACLs.
This example shows how to create and display an access list named mac1, denying only EtherType DECnet Phase IV traffic, but permitting all other types of traffic.
Applying a MAC ACL to a Layer 2 Interface
After you create a MAC ACL, you can apply it to a Layer 2 interface to filter non-IP traffic coming in that interface. When you apply the MAC ACL, consider these guidelines:
- You can apply no more than one IP access list and one MAC access list to the same Layer 2 interface. The IP access list filters only IP packets, and the MAC access list filters non-IP packets.
- A Layer 2 interface can have only one MAC access list. If you apply a MAC access list to a Layer 2 interface that has a MAC ACL configured, the new ACL replaces the previously configured one.
Beginning in privileged EXEC mode, follow these steps to apply a MAC access list to control access to a Layer 2 interface:
To remove the specified access group, use the no mac access-group { name} interface configuration command.
This example shows how to apply MAC access list mac1 to a port to filter packets entering the port:

Note![]() The mac access-group interface configuration command is only valid when applied to a physical Layer 2 interface.You cannot use the command on EtherChannel port channels.
The mac access-group interface configuration command is only valid when applied to a physical Layer 2 interface.You cannot use the command on EtherChannel port channels.
After receiving a packet, the switch checks it against the inbound ACL. If the ACL permits it, the switch continues to process the packet. If the ACL rejects the packet, the switch discards it. When you apply an undefined ACL to an interface, the switch acts as if the ACL has not been applied and permits all packets. Remember this behavior if you use undefined ACLs for network security.
Displaying IPv4 ACL Configuration
You can display the ACLs that are configured on the switch, and you can display the ACLs that have been applied to interfaces.
When you use the ip access-group interface configuration command to apply ACLs to a Layer 2 interface, you can display the access groups on the interface. You can also display the MAC ACLs applied to a Layer 2 interface. You can use the privileged EXEC commands as described in Table 1-2 to display this information.
 Feedback
Feedback