- Index
- Preface
- Overview
- Using the Command-Line Interface
- Assigning the Switch IP Address and Default Gateway
- Configuring Cisco IOS Configuration Engine
- Administering the Switch
- Configuring Web-Based Authentication
- Clustering Switches
- Managing Switch Stacks
- Configuring SDM Templates
- Configuring Switch-Based Authentication
- Configuring IEEE 802.1x Port-Based Authentication
- Configuring Interface Characteristics
- Configuring VLANs
- Configuring VTP
- Configuring Voice VLAN
- Configuring STP
- Configuring MSTP
- Configuring Optional Spanning-Tree Features
- Configuring Flex Links and the MAC Address-Table Move Update Feature
- Configuring DHCP Features and IP Source Guard
- Configuring Dynamic ARP Inspection
- Configuring IGMP Snooping and MVR
- Configuring Port-Based Traffic Control
- Configuring UDLD
- Configuring CDP
- Configuring LLDP, LLDP-MED, and Wired Location Service
- Configuring SPAN and RSPAN
- Configuring RMON
- Configuring System Message Logging
- Configuring SNMP
- Configuring Cisco IOS IP SLAs Operations
- Configuring Network Security with ACLs
- Configuring QoS
- Configuring Static IP Unicast Routing
- Configuring IPv6 Host
- Configuring IPv6 MLD Snooping
- Configuring EtherChannels and Link-State Tracking
- Troubleshooting
- Configuring Online Diagnostics
- Working with the Cisco IOS File System, Configuration Files, and Software Images
- Supported MIBs
- Unsupported Commands in Cisco IOS Release 12.2(55)SE
- Recommendations for Upgrading a Catalyst 2950 Switch to a Catalyst 2960 Switch
- Understanding Interface Types
- Using the Switch USB Ports (Catalyst 2960-S Switches Only)
- Using Interface Configuration Mode
- Using the Ethernet Management Port (Catalyst 2960-S Only)
- Configuring Ethernet Interfaces
- Default Ethernet Interface Configuration
- Setting the Type of a Dual-Purpose Uplink Port
- Configuring Interface Speed and Duplex Mode
- Configuring IEEE 802.3x Flow Control
- Configuring Auto-MDIX on an Interface
- Configuring a Power Management Mode on a PoE Port
- Budgeting Power for Devices Connected to a PoE Port
- Configuring Power Policing
- Adding a Description for an Interface
- Configuring Layer 3 SVIs
- Configuring the System MTU
- Monitoring and Maintaining the Interfaces
Configuring Interface Characteristics
This chapter defines the types of Catalyst 2960 and 2960-S interfaces and describes how to configure them.
- Understanding Interface Types
- Using the Switch USB Ports (Catalyst 2960-S Switches Only)
- Using Interface Configuration Mode
- Using the Ethernet Management Port (Catalyst 2960-S Only)
- Configuring Ethernet Interfaces
- Configuring Layer 3 SVIs
- Configuring the System MTU
- Monitoring and Maintaining the Interfaces

Note![]() For complete syntax and usage information for the commands used in this chapter, see the switch command reference for this release and the Cisco IOS Interface Command Reference, Release 12.2 from the Cisco.com page under Documentation > Cisco IOS Software Release > 12.2 Mainline > Command References.
For complete syntax and usage information for the commands used in this chapter, see the switch command reference for this release and the Cisco IOS Interface Command Reference, Release 12.2 from the Cisco.com page under Documentation > Cisco IOS Software Release > 12.2 Mainline > Command References.
Understanding Interface Types
This section describes the different types of supported interfaces with references to chapters that contain more detailed information about configuring these interfaces.

Note![]() The stack ports on the rear of the switch are not Ethernet ports and cannot be configured.
The stack ports on the rear of the switch are not Ethernet ports and cannot be configured.
- Port-Based VLANs
- Switch Ports
- Switch Virtual Interfaces
- EtherChannel Port Groups
- Dual-Purpose Uplink Ports
- Power over Ethernet Ports
- Connecting Interfaces
Port-Based VLANs

Note![]() Stacking is supported only on Catalyst 2960-S switches running the LAN base image.
Stacking is supported only on Catalyst 2960-S switches running the LAN base image.
A VLAN is a switched network that is logically segmented by function, team, or application, without regard to the physical location of the users. For more information about VLANs, see the Chapter1, “Configuring VLANs” Packets received on a port are forwarded only to ports that belong to the same VLAN as the receiving port. Network devices in different VLANs cannot communicate with one another without a Layer 3 device to route traffic between the VLANs.
VLAN partitions provide hard firewalls for traffic in the VLAN, and each VLAN has its own MAC address table. A VLAN comes into existence when you configure a local port to be associated with the VLAN, when the VLAN Trunking Protocol (VTP) learns of its existence from a neighbor on a trunk, or when a user creates a VLAN.
To configure VLANs, use the vlan vlan-id global configuration command to enter VLAN configuration mode. The VLAN configurations for normal-range VLANs (VLAN IDs 1 to 1005) are saved in the VLAN database. If VTP is version 1 or 2, you must first set VTP mode to transparent to configure extended-range VLANs (VLAN IDs 1006 to 4094). Extended-range VLANs created in transparent mode are not added to the VLAN database but are saved in the switch running configuration. With VTP version 3, you can create extended-range VLANs in client or server mode. These VLANs are saved in the VLAN database.
VLANs can be formed with ports across the stack. The VLAN database is downloaded to all switches in a stack, and all switches in the stack build the same VLAN database. The running configuration and the saved configuration are the same for all switches in a stack.

Note![]() Stacking is supported only on Catalyst 2960-S switches running the LAN base image.
Stacking is supported only on Catalyst 2960-S switches running the LAN base image.
Add ports to a VLAN by using the switchport interface configuration commands:
Switch Ports
Switch ports are Layer 2-only interfaces associated with a physical port. Switch ports belong to one or more VLANs. You use switch ports for managing the physical interface and associated Layer 2 protocols.
A switch port can be an access port or a trunk port. You can configure a port as an access port or trunk port or let the Dynamic Trunking Protocol (DTP) operate on a per-port basis to set the switchport mode by negotiating with the port on the other end of the link.
Configure switch ports by using the switchport interface configuration commands.

Note![]() When you change a Layer 3 interface into Layer 2 mode, the configuration information related to the affected interface might be lost, and the interface is returned to its default configuration.
When you change a Layer 3 interface into Layer 2 mode, the configuration information related to the affected interface might be lost, and the interface is returned to its default configuration.
For detailed information about configuring access port and trunk port characteristics, see Chapter1, “Configuring VLANs”
Access Ports
An access port belongs to and carries the traffic of only one VLAN (unless it is configured as a voice VLAN port). Traffic is received and sent in native formats with no VLAN tagging. Traffic arriving on an access port is assumed to belong to the VLAN assigned to the port.
If an access port receives an 802.1Q tagged packet, the packet is dropped, and the source address is not learned.
- Static access ports are manually assigned to a VLAN (or through a RADIUS server for use with IEEE 802.1x). For more information, see the “802.1x Authentication with VLAN Assignment” section.
- VLAN membership of dynamic access ports is learned through incoming packets. By default, a dynamic access port is not a member of any VLAN. Traffic forwarding to and from the port is enabled only when the port VLAN membership is discovered. Dynamic access ports on the switch are assigned to a VLAN by a VLAN Membership Policy Server (VMPS). The VMPS can be a Catalyst 6500 series switch. The Catalyst 2960 or 2960-S switch cannot be a VMPS server.
You can also configure an access port with an attached Cisco IP Phone to use one VLAN for voice traffic and another VLAN for data traffic from a device attached to the phone. For more information about voice VLAN ports, see Chapter1, “Configuring Voice VLAN”
Trunk Ports
A trunk port carries the traffic of multiple VLANs and by default is a member of all VLANs in the VLAN database.
The switch supports only 802.1Q trunk ports. An 802.1Q trunk port supports simultaneous tagged and untagged traffic. The trunk port is assigned a default port VLAN ID (PVID), and all untagged traffic travels on the port default PVID. All untagged traffic and tagged traffic with a NULL VLAN ID belong to the port default PVID. A packet with a VLAN ID equal to the outgoing port default PVID is sent untagged. All other traffic is sent with a VLAN tag.
Although by default, a trunk port is a member of every VLAN known to the VTP, you can limit VLAN membership by configuring an allowed list of VLANs for each trunk port. The list of allowed VLANs affects only the associated trunk port. By default, all possible VLANs (VLAN ID 1 to 4094) are in the allowed list. A trunk port can become a member of a VLAN only if VTP knows of the VLAN and if the VLAN is enabled. If VTP learns of a new, enabled VLAN and the VLAN is in the allowed list, the trunk port automatically becomes a member of that VLAN. Traffic is forwarded to and from the trunk port for that VLAN. If VTP learns of an enabled VLAN that is not in the allowed list for a trunk port, the port does not become a member of the VLAN, and traffic for the VLAN is not forwarded to or from the port.
For more information about trunk ports, see Chapter1, “Configuring VLANs”
Switch Virtual Interfaces
A switch virtual interface (SVI) represents a VLAN of switch ports as one interface to the routing or bridging function in the system. You can associate only one SVI with a VLAN. You configure an SVI for a VLAN only to route between VLANs or to provide IP host connectivity to the switch.
By default, an SVI is created for the default VLAN (VLAN 1) to permit remote switch administration. Additional SVIs must be explicitly configured.

Note![]() You cannot delete interface VLAN 1.
You cannot delete interface VLAN 1.
SVIs provide IP host connectivity only to the system.Beginning with Cisco IOS release 12.2(55)SE, you can enable routing and configure static routes on SVIs.

Note![]() Static routing is supported on SVIs only when the switch is running the LAN base image.
Static routing is supported on SVIs only when the switch is running the LAN base image.
SVIs are created the first time that you enter the vlan interface configuration command for a VLAN interface. The VLAN corresponds to the VLAN tag associated with data frames on an encapsulated trunk port or the VLAN ID configured for an access port. Configure a VLAN interface for each VLAN for which you want to route traffic, and assign it an IP address. For more information, see the “Manually Assigning IP Information” section.

Note![]() When you create an SVI, it does not become active until it you associate it with a physical port.
When you create an SVI, it does not become active until it you associate it with a physical port.
EtherChannel Port Groups
EtherChannel port groups treat multiple switch ports as one switch port. An EtherChannel port group acts as a single logical port for high-bandwidth connections between switches or between switches and servers. An EtherChannel balances the traffic load across the links in the channel. If a link within the EtherChannel fails, traffic previously carried over the failed link changes to the remaining links.You can group multiple trunk ports into one logical trunk port or multiple access ports into one logical access port. Most protocols operate over either single ports or aggregated switch ports and do not recognize the physical ports within the port group. The DTP, the Cisco Discovery Protocol (CDP), and the Port Aggregation Protocol (PAgP) operate only on physical ports.
When you configure an EtherChannel, you create a port-channel logical interface and assign an interface to the EtherChannel. Use the channel-group interface configuration command to dynamically create the port-channel logical interface. This command binds the physical and logical ports together.
For more information, see Chapter1, “Configuring EtherChannels and Link-State Tracking”
Dual-Purpose Uplink Ports

Note![]() Catalyst 2960-S switches do not have dual-purpose uplink ports.
Catalyst 2960-S switches do not have dual-purpose uplink ports.
Some switches support dual-purpose uplink ports. Each uplink port is considered as a single interface with dual front ends—an RJ-45 connector and a small form-factor pluggable (SFP) module connector. The dual front ends are not redundant interfaces, and the switch activates only one connector of the pair.
By default, the switch dynamically selects the interface type that first links up. However, you can use the media-type interface configuration command to manually select the RJ-45 connector or the SFP module connector. For information about configuring speed and duplex settings for a dual-purpose uplink, see the “Setting the Interface Speed and Duplex Parameters” section.
Each uplink port has two LEDs: one shows the status of the RJ-45 port, and one shows the status of the SFP module port. The port LED is on for whichever connector is active. For more information about the LEDs, see the hardware installation guide.
Power over Ethernet Ports

Note![]() PoE is supported only when the switch is running the LAN base image. Power over Ethernet Plus (PoE+) is supported only on Catalyst 2960-S switches.
PoE is supported only when the switch is running the LAN base image. Power over Ethernet Plus (PoE+) is supported only on Catalyst 2960-S switches.
PoE switch ports automatically supply power to these connected devices (if the switch senses that there is no power on the circuit):
- Cisco pre-standard powered devices (such as Cisco IP Phones and Cisco Aironet access points)
- IEEE 802.3 af-compliant powered devices
- IEEE 802.3 at-compliant powered devices (PoE+ on Catalyst 2960-S switches only)
A powered device can receive redundant power when it is connected only to a PoE switch port and to an AC power source. After the switch detects a powered device, it determines the device power requirements and then grants or denies power to the device. The switch can also sense the real-time power consumption of the device by monitoring and policing the power usage.
Supported Protocols and Standards
The switch uses these protocols and standards to support PoE:
- CDP with power consumption—The powered device notifies the switch of the amount of power it is consuming. The switch does not reply to the power-consumption messages. The switch can only supply power to or remove power from the PoE port.
- Cisco intelligent power management—The powered device and the switch negotiate through power-negotiation CDP messages for an agreed power-consumption level. The negotiation allows a high-power Cisco powered device, which consumes more than 7 W, to operate at its highest power mode. The powered device first boots up in low-power mode, consumes less than 7 W, and negotiates to obtain enough power to operate in high-power mode. The device changes to high-power mode only when it receives confirmation from the switch.
High-power devices can operate in low-power mode on switches that do not support power-negotiation CDP.
Cisco intelligent power management is backward-compatible with CDP with power consumption; the switch responds according to the CDP message that it receives. CDP is not supported on third-party powered devices; therefore, the switch uses the IEEE classification to determine the power usage of the device.
- IEEE 802.3af—The major features of this standard are powered-device discovery, power administration, disconnect detection, and optional powered-device power classification. For more information, see the standard.
- IEEE 802.3at (Catalyst 2960-S only)—This PoE+ standard supports all the features of 802.1af and increases the maximum power available on each PoE port from 15.4 W to 30 W.
Powered-Device Detection and Initial Power Allocation
The switch detects a Cisco pre-standard or an IEEE-compliant powered device when the PoE-capable port is in the no-shutdown state, PoE is enabled (the default), and the connected device is not being powered by an AC adaptor.
After device detection, the switch determines the device power requirements based on its type:
- A Cisco pre-standard powered device does not provide its power requirement when the switch detects it, so a Catalyst 2960 switch allocates 15.4 W as the initial allocation for power budgeting; a Catalyst 2960-S switch allocates 30 W (PoE+).
The initial power allocation is the maximum amount of power that a powered device requires. The switch initially allocates this amount of power when it detects and powers the powered device. As the switch receives CDP messages from the powered device and as the powered device negotiates power levels with the switch through CDP power-negotiation messages, the initial power allocation might be adjusted.
- The switch classifies the detected IEEE device within a power consumption class. Based on the available power in the power budget, the switch determines if a port can be powered. Table 1-1 lists these levels.
|
|
|
|---|---|
The switch monitors and tracks requests for power and grants power only when it is available. The switch tracks its power budget (the amount of power available on the switch for PoE). The switch performs power-accounting calculations when a port is granted or denied power to keep the power budget up to date.
After power is applied to the port, the switch uses CDP to determine the actual power consumption requirement of the connected Cisco powered devices, and the switch adjusts the power budget accordingly. This does not apply to third-party PoE devices. The switch processes a request and either grants or denies power. If the request is granted, the switch updates the power budget. If the request is denied, the switch ensures that power to the port is turned off, generates a syslog message, and updates the LEDs. Powered devices can also negotiate with the switch for more power.
If the switch detects a fault caused by an undervoltage, overvoltage, overtemperature, oscillator-fault, or short-circuit condition, it turns off power to the port, generates a syslog message, and updates the power budget and LEDs.
In a Catalyst 2960-S switch stack, the PoE feature operates the same whether or not the switch is a stack member. The power budget is per-switch and independent of any other switch in the stack. Election of a new stack master does not affect PoE operation. The stack master keeps track of PoE status for all switches and ports in the stack and includes the status in output displays.
Power Management Modes
- auto —The switch automatically detects if the connected device requires power. If the switch discovers a powered device connected to the port and if the switch has enough power, it grants power, updates the power budget, turns on power to the port on a first-come, first-served basis, and updates the LEDs. For LED information, see the hardware installation guide.
If the switch has enough power for all the powered devices, they all come up. If enough power is available for all powered devices connected to the switch, power is turned on to all devices. If there is not enough available PoE, or if a device is disconnected and reconnected while other devices are waiting for power, it cannot be determined which devices are granted or are denied power.
If granting power would exceed the system power budget, the switch denies power, ensures that power to the port is turned off, generates a syslog message, and updates the LEDs. After power has been denied, the switch periodically rechecks the power budget and continues to attempt to grant the request for power.
If a device being powered by the switch is then connected to wall power, the switch might continue to power the device. The switch might continue to report that it is still powering the device whether the device is being powered by the switch or receiving power from an AC power source.
If a powered device is removed, the switch automatically detects the disconnect and removes power from the port. You can connect a nonpowered device without damaging it.
You can specify the maximum wattage that is allowed on the port. If the IEEE class maximum wattage of the powered device is greater than the configured maximum value, the switch does not provide power to the port. If the switch powers a powered device, but the powered device later requests through CDP messages more than the configured maximum value, the switch removes power to the port. The power that was allocated to the powered device is reclaimed into the global power budget. If you do not specify a wattage, the switch delivers the maximum value. Use the auto setting on any PoE port. The auto mode is the default setting.
- static —The switch pre-allocates power to the port (even when no powered device is connected) and guarantees that power will be available for the port. The switch allocates the port configured maximum wattage, and the amount is never adjusted through the IEEE class or by CDP messages from the powered device. Because power is pre-allocated, any powered device that uses less than or equal to the maximum wattage is guaranteed to be powered when it is connected to the static port. The port no longer participates in the first-come, first-served model.
However, if the powered-device IEEE class is greater than the maximum wattage, the switch does not supply power to it. If the switch learns through CDP messages that the powered device needs more than the maximum wattage, the powered device is shutdown.
If you do not specify a wattage, the switch pre-allocates the maximum value. The switch powers the port only if it discovers a powered device. Use the static setting on a high-priority interface.
- never —The switch disables powered-device detection and never powers the PoE port even if an unpowered device is connected. Use this mode only when you want to make sure power is never applied to a PoE-capable port, making the port a data-only port.
For information on configuring a PoE port, see the “Configuring a Power Management Mode on a PoE Port” section.
Power Monitoring and Power Policing
When policing of the real-time power consumption is enabled, the switch takes action when a powered device consumes more power than the maximum amount allocated, also referred to as the cutoff-power value .
When PoE is enabled, the switch senses the real-time power consumption of the powered device and monitors the power consumption of the connected powered device; this is called power monitoring or power sensing. The switch also uses the power policing feature to police the power usage.
Power monitoring is backward-compatible with Cisco intelligent power management and CDP-based power consumption. It works with these features to ensure that the PoE port can supply power to the powered device. For more information about these PoE features, see the “Powered-Device Detection and Initial Power Allocation” section.
The switch senses the power consumption of the connected device as follows:
1.![]() The switch monitors the real-time power consumption on individual ports.
The switch monitors the real-time power consumption on individual ports.
2.![]() The switch records the power consumption, including peak power usage, and reports the information through an SNMP MIB, CISCO-POWER-ETHERNET-EXT-MIB.
The switch records the power consumption, including peak power usage, and reports the information through an SNMP MIB, CISCO-POWER-ETHERNET-EXT-MIB.
3.![]() If power policing is enabled, the switch polices power usage by comparing the real-time power consumption to the maximum power allocated to the device. For more information about the maximum power consumption, also referred to as the cutoff power, on a PoE port, see the “Maximum Power Allocation (Cutoff Power) on a PoE Port” section.
If power policing is enabled, the switch polices power usage by comparing the real-time power consumption to the maximum power allocated to the device. For more information about the maximum power consumption, also referred to as the cutoff power, on a PoE port, see the “Maximum Power Allocation (Cutoff Power) on a PoE Port” section.
If the device uses more than the maximum power allocation on the port, the switch can either turn off power to the port, or the switch can generate a syslog message and update the LEDs (the port LED is now blinking amber) while still providing power to the device based on the switch configuration. By default, power-usage policing is disabled on all PoE ports.
If error recovery from the PoE error-disabled state is enabled, the switch automatically takes the PoE port out of the error-disabled state after the specified amount of time.
If error recovery is disabled, you can manually re-enable the PoE port by using the shutdown and no shutdown interface configuration commands.
4.![]() If policing is disabled, no action occurs when the powered device consumes more than the maximum power allocation on the PoE port, which could adversely affect the switch.
If policing is disabled, no action occurs when the powered device consumes more than the maximum power allocation on the PoE port, which could adversely affect the switch.
Maximum Power Allocation (Cutoff Power) on a PoE Port
When power policing is enabled, the switch determines the cutoff power on the PoE port in this order:
1.![]() Manually when you set the user-defined power level that the switch budgets for the port by using the power inline consumption default wattage global or interface configuration command
Manually when you set the user-defined power level that the switch budgets for the port by using the power inline consumption default wattage global or interface configuration command
2.![]() Manually when you set the user-defined power level that limits the power allowed on the port by using the power inline auto max max-wattage or the power inline static max max-wattage interface configuration command
Manually when you set the user-defined power level that limits the power allowed on the port by using the power inline auto max max-wattage or the power inline static max max-wattage interface configuration command
3.![]() Automatically when the switch sets the power usage of the device by using CDP power negotiation or by the IEEE classification and LLDP power negotiation.
Automatically when the switch sets the power usage of the device by using CDP power negotiation or by the IEEE classification and LLDP power negotiation.
Use the first or second method in the previous list to manually configure the cutoff-power value by entering the power inline consumption default wattage or the power inline [ auto | static max ] max-wattage command. If you do not manually configure the cutoff-power value, the switch automatically determines the value by using CDP power negotiation. If the switch cannot determine the value by using one of these methods, it uses the default value of 15.4 W. On a Catalyst 2960-S switch with PoE+, if you do not manually configure the cutoff-power value, the switch automatically determines it by using CDP power negotiation or the device IEEE classification and LLDP power negotiation. If CDP or LLDP are not enabled, the default value of 30 W is applied. However without CDP or LLDP, the switch does not allow devices to consume more than 15.4 W of power because values from 15400 to 30000 mW are only allocated based on CDP or LLDP requests. If a powered device consumes more than 15.4 W without CDP or LLDP negotiation, the device might be in violation of the maximum current ( Imax) limitation and might experience an Icut fault for drawing more current than the maximum. The port remains in the fault state for a time before attempting to power on again. If the port continuously draws more than 15.4 W, the cycle repeats.

Note![]() When a powered device connected to a PoE+ port restarts and sends a CDP or LLDP packet with a power TLV, the switch locks to the power-negotiation protocol of that first packet and does not respond to power requests from the other protocol. For example, if the switch is locked to CDP, it does not provide power to devices that send LLDP requests. If CDP is disabled after the switch has locked on it, the switch does not respond to LLDP power requests and can no longer power on any accessories. In this case, you should restart the powered device.
When a powered device connected to a PoE+ port restarts and sends a CDP or LLDP packet with a power TLV, the switch locks to the power-negotiation protocol of that first packet and does not respond to power requests from the other protocol. For example, if the switch is locked to CDP, it does not provide power to devices that send LLDP requests. If CDP is disabled after the switch has locked on it, the switch does not respond to LLDP power requests and can no longer power on any accessories. In this case, you should restart the powered device.
You can configure the initial power allocation and the maximum power allocation on a port. However, these values are only the configured values that determine when the switch should turn on or turn off power on the PoE port. The maximum power allocation is not the same as the actual power consumption of the powered device. The actual cutoff power value that the switch uses for power policing is not equal to the configured power value.
When power policing is enabled, the switch polices the power usage at the switch port, which is greater than the power consumption of the device. When you manually set the maximum power allocation, you must consider the power loss over the cable from the switch port to the powered device. The cutoff power is the sum of the rated power consumption of the powered device and the worst-case power loss over the cable.
The actual amount of power consumed by a powered device on a PoE port is the cutoff-power value plus a calibration factor of 500 mW (0.5 W). The actual cutoff value is approximate and varies from the configured value by a percentage of the configured value. For example, if the configured cutoff power is 12 W, the actual cutoff-value is 11.4 W, which is 0.05% less than the configured value.
We recommend that you enable power policing when PoE is enabled on your switch. For example, if policing is disabled and you set the cutoff-power value by using the power inline auto max 6300 interface configuration command, the configured maximum power allocation on the PoE port is 6.3 W (6300 mW). The switch provides power to the connected devices on the port if the device needs up to 6.3 W. If the CDP-power negotiated value or the IEEE classification value exceeds the configured cutoff value, the switch does not provide power to the connected device. After the switch turns on power to the PoE port, the switch does not police the real-time power consumption of the device, and the device can consume more power than the maximum allocated amount, which could adversely affect the switch and the devices connected to the other PoE ports.
Because the switch supports internal power supplies and the Cisco Redundant Power System 2300 (also referred to as the RPS 2300), the total amount of power available for the powered devices varies depending on the power supply configuration.
- If a power supply is removed and replaced by a new power supply with less power and the switch does not have enough power for the powered devices, the switch denies power to the PoE ports that are in auto mode in descending order of the port numbers. If the switch still does not have enough power, it denies power to the PoE ports in static mode in descending order of the port numbers.
- If the new power supply supports more power than the previous one and the switch now has more power available, the switch grants power to the PoE ports in static mode in ascending order of the port numbers. If it still has power available, the switch then grants power to the PoE ports in auto mode in ascending order of the port numbers.
For configuration information, see the “Configuring Power Policing” section.
Connecting Interfaces
Devices within a single VLAN can communicate directly through any switch. Ports in different VLANs cannot exchange data without going through a routing device.
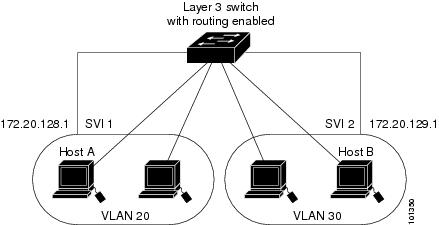
In the configuration shown in Figure 1-1, when Host A in VLAN 20 sends data to Host B in VLAN 30, the data must go from Host A to the switch, to the router, back to the switch, and then to Host B.
Figure 1-1 Connecting VLANs with Layer 2 Switches
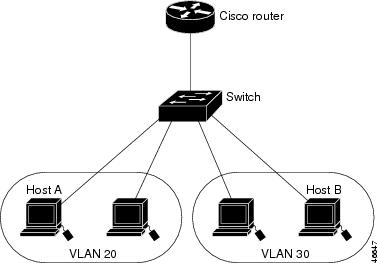
With a standard Layer 2 switch, ports in different VLANs have to exchange information through a router. By using the switch with routing enabled, when you configure both VLAN 20 and VLAN 30 with an SVI to which an IP address is assigned, packets can be sent from Host A to Host B directly through the switch with no need for an external router (Figure 1-2).
Figure 1-2 Connecting VLANs with a Layer 3 Switch
Using the Switch USB Ports (Catalyst 2960-S Switches Only)
The Catalyst 2960-S switch has two USB ports on the front panel:
USB Mini-Type B Console Port
The switch has two console ports available—a USB mini-Type B console connection and an RJ-45 console port. Console output appears on devices connected to both ports, but console input is active on only one port at a time. The USB connector takes precedence over the RJ-45 connector.

Note![]() Windows PCs require a driver for the USB port. See the hardware installation guide for driver installation instructions.
Windows PCs require a driver for the USB port. See the hardware installation guide for driver installation instructions.
Use the supplied USB Type A-to-USB mini-Type B cable to connect a PC or other device to the switch. The connected device must include a terminal emulation application. When the switch detects a valid USB connection to a powered-on device that supports host functionality (such as a PC), input from the RJ-45 console is immediately disabled, and input from the USB console is enabled. Removing the USB connection immediately reenables input from the RJ-45 console connection. An LED on the switch shows which console connection is in use.
Console Port Change Logs
At software startup, a log shows whether the USB or the RJ-45 console is active. Each switch in a stack issues this log. Every switch always first displays the RJ-45 media type.
In the sample output, switch 1 has a connected USB console cable. Because the bootloader did not change to the USB console, the first log from switch 1 shows the RJ-45 console. A short time later, the console changes and the USB console log appears. Switch 2 and switch 3 have connected RJ-45 console cables.
When the USB cable is removed or the PC de-activates the USB connection, the hardware automatically changes to the RJ-45 console interface:
You can configure the console type to always be RJ-45, and you can configure an inactivity timeout for the USB connector.
Configuring the Console Media Type
Beginning in privileged EXEC mode, follow these steps to select the RJ-45 console media type. If you configure the RJ-45 console, USB console operation is disabled, and input always remains with the RJ-45 console.
This configuration applies to all switches in a stack.
|
|
|
|
|---|---|---|
Configure the console media type to always be RJ-45. If you do not enter this command and both types are connected, the default is USB. |
||
This example disables the USB console media type and enables the RJ-45 console media type.
This configuration terminates any active USB console media type in the stack. A log shows that this termination has occurred. This example shows that the console on switch 1 reverted to RJ-45.
At this point no switches in the stack allow a USB console to have input. A log entry shows when a console cable is attached. If a USB console cable is connected to switch 2, it is prevented from providing input.
This example reverses the previous configuration and immediately activates any USB console that is connected.
Configuring the USB Inactivity Timeout
The configurable inactivity timeout reactivates the RJ-45 console port if the USB console port is activated but no input activity occurs on it for a specified time period. When the USB console port is deactivated due to a timeout, you can restore its operation by disconnecting and reconnecting the USB cable.

Note![]() The configured inactivity timeout applies to all switches in a stack. However, a timeout on one switch does not cause a timeout on other switches in the stack.
The configured inactivity timeout applies to all switches in a stack. However, a timeout on one switch does not cause a timeout on other switches in the stack.
Beginning in privileged EXEC mode, follow these steps to configure an inactivity timeout.
This example configures the inactivity timeout to 30 minutes:
To disable the configuration, use these commands:
If there is no (input) activity on a USB console port for the configured number of minutes, the inactivity timeout setting applies to the RJ-45 port, and a log shows this occurrence:
At this point, the only way to reactivate the USB console port is to disconnect and reconnect the cable.
When the USB cable on the switch has been disconnected and reconnected, a log similar to this appears:
USB Type A Port
The USB Type A port provides access to external USB flash devices, also known as thumb drives or USB keys. The switch supports Cisco 64 MB, 256 MB, 512 MB and 1 GB flash drives. You can use standard Cisco IOS command- line interface (CLI) commands to read, write, erase, and copy to or from the flash device. You can also configure the switch to boot from the USB flash drive.
Beginning in privileged EXEC mode, follow these steps to allow booting from the USB flash device.
|
|
|
|
|---|---|---|
Configure the switch to boot from the USB flash device. The image is the name of the bootable image. |
||
To get information about the USB device, use the show usb { controllers | device | driver | port | tree } privileged EXEC command.
This example configures the switch to boot from the Catalyst 2960-S flash device. The image is the Catalyst 2960-S LAN base image.
To disable booting from flash, enter the no form of the command.
This is sample output from the show usb device command:
This is sample output from the show usb port command:
Using Interface Configuration Mode
The switch supports these interface types:
You can also configure a range of interfaces (see the “Configuring a Range of Interfaces” section).
To configure a physical interface (port) on a Catalyst 2960 switch or a Catalyst 2960-S switch running the LAN Lite image, specify the interface type, module number, and switch port number, and enter interface configuration mode. To configure a port on a Catalyst 2960-S switch running the LAN base image (supporting stacking), specify the interface type, stack member number, module number, and switch port number, and enter interface configuration mode.
- Type —Port types depend on those supported on the switch. Possible types are: Fast Ethernet (fastethernet or fa) for 10/100 Mb/s Ethernet, Gigabit Ethernet (gigabitethernet or gi) for 10/100/1000 Mb/s Ethernet ports, 10-Gigabit Ethernet (tengigabitethernet or te) for 10,000 Mb/s, or small form-factor pluggable (SFP) module Gigabit Ethernet interfaces.
- Stack member number —The number that identifies the switch within the stack. The switch number range is 1 to 4 and is assigned the first time the switch initializes. The default switch number, before it is integrated into a switch stack, is 1. When a switch has been assigned a stack member number, it keeps that number until another is assigned to it.
- Module number — The module or slot number on the switch (always 0).
- Port number—The interface number on the switch. The port numbers always begin at 1, starting with the far left port when facing the front of the switch, for example, gigabitethernet1/0/1. For a switch with 10/100/1000 ports and SFP module ports, SFP module ports are numbered consecutively following the 10/100/1000 ports.
You can identify physical interfaces by looking at the switch. You can also use the show privileged EXEC commands to display information about a specific interface or all the interfaces. The remainder of this chapter primarily provides physical interface configuration procedures.
These examples identify interfaces on a Catalyst 2960-S switch running the LAN base image:
This example identifies an interface on a Catalyst 2960 switch or a Catalyst 2960-S switch running the LAN Lite image:

Note![]() Configuration examples and outputs in this book might not be specific to your switch, particularly regarding the presence of a stack member number.
Configuration examples and outputs in this book might not be specific to your switch, particularly regarding the presence of a stack member number.
Procedures for Configuring Interfaces
These general instructions apply to all interface configuration processes.
Step 1![]() Enter the configure terminal command at the privileged EXEC prompt:
Enter the configure terminal command at the privileged EXEC prompt:
Step 2![]() Enter the interface global configuration command.
Enter the interface global configuration command.
Identify the interface type and the interface number, Gigabit Ethernet port 1 in this example:

Note![]() Entering a space between the interface type and interface number is optional
Entering a space between the interface type and interface number is optional
Step 3![]() Follow each interface command with the configuration commands that the interface requires. The commands that you enter define the protocols and applications that will run on the interface. The commands are collected and applied to the interface when you enter another interface command or enter end to return to privileged EXEC mode.
Follow each interface command with the configuration commands that the interface requires. The commands that you enter define the protocols and applications that will run on the interface. The commands are collected and applied to the interface when you enter another interface command or enter end to return to privileged EXEC mode.
You can also configure a range of interfaces by using the interface range or interface range macro global configuration commands. Interfaces configured in a range must be the same type and must be configured with the same feature options.
Step 4![]() After you configure an interface, verify its status by using the show privileged EXEC commands listed in the “Monitoring and Maintaining the Interfaces” section.
After you configure an interface, verify its status by using the show privileged EXEC commands listed in the “Monitoring and Maintaining the Interfaces” section.
Enter the show interfaces privileged EXEC command to see a list of all interfaces on or configured for the switch. A report is provided for each interface that the device supports or for the specified interface.
Configuring a Range of Interfaces
You can use the interface range global configuration command to configure multiple interfaces with the same configuration parameters. When you enter the interface-range configuration mode, all command parameters that you enter are attributed to all interfaces within that range until you exit this mode.
Beginning in privileged EXEC mode, follow these steps to configure a range of interfaces with the same parameters:
|
|
|
|
|---|---|---|
Specify the range of interfaces (VLANs or physical ports) to be configured, and enter interface-range configuration mode.
|
||
Use the normal configuration commands to apply the configuration parameters to all interfaces in the range. Each command is executed as it is entered. |
||
When using the interface range global configuration command, note these guidelines:
–![]() vlan vlan-ID, where the VLAN ID is 1 to 4094
vlan vlan-ID, where the VLAN ID is 1 to 4094

Note Although the command-line interface shows options to set multiple VLANs, these options are not supported on Catalyst 2960 and 2960-S switches.
–![]() , where the module is always 0
, where the module is always 0
–![]() fastethernet module/{first port } - { last port }, where the module is always 0
fastethernet module/{first port } - { last port }, where the module is always 0
–![]() gigabitethernet module/{ first port } - { last port }, where the module is always 0
gigabitethernet module/{ first port } - { last port }, where the module is always 0
–![]() port-channel port-channel-number - port-channel-number, where the port-channel-number is 1 to 6
port-channel port-channel-number - port-channel-number, where the port-channel-number is 1 to 6

Note When you use the interface range command with port channels, the first and last port-channel number must be active port channels.
- You must add a space between the first interface number and the hyphen when using the interface range command.
For example, interface range gigabitethernet 0/1 - 4 is a valid range; interface range gigabit ethernet0/1-4 is not.
- The interface range command only works with VLAN interfaces that have been configured with the interface vlan command. The show running-config privileged EXEC command displays the configured VLAN interfaces. VLAN interfaces not displayed by the show running-config command cannot be used with the interface range command.
- All interfaces defined in a range must be the same type (all Fast Ethernet ports, all Gigabit Ethernet ports, all EtherChannel ports, or all VLANs), but you can enter multiple ranges in a command.
This example shows how to use the interface range global configuration command to set the speed on ports 1 to 2 to 100 Mb/s:
This example shows how to use a comma to add different interface type strings to the range to enable Fast Ethernet ports 1 to 3 and Gigabit Ethernet ports 1 and 2 to receive flow-control pause frames:
If you enter multiple configuration commands while you are in interface-range mode, each command is executed as it is entered. The commands are not batched and executed after you exit interface-range mode. If you exit interface-range configuration mode while the commands are being executed, some commands might not be executed on all interfaces in the range. Wait until the command prompt reappears before exiting interface-range configuration mode.
Configuring and Using Interface Range Macros
You can create an interface range macro to automatically select a range of interfaces for configuration. Before you can use the macro keyword in the interface range macro global configuration command string, you must use the define interface-range global configuration command to define the macro.
Beginning in privileged EXEC mode, follow these steps to define an interface range macro:
Use the no define interface-range macro_name global configuration command to delete a macro.
When using the define interface-range global configuration command, note these guidelines:
–![]() vlan vlan-ID, where the VLAN ID is 1 to 4094
vlan vlan-ID, where the VLAN ID is 1 to 4094

Note Although the command-line interface shows options to set multiple VLANs, these options are not supported on Catalyst 2960 switches.
–![]() fastethernet module/{first port } - { last port }, where the module is always 0
fastethernet module/{first port } - { last port }, where the module is always 0
–![]() gigabitethernet module/{ first port } - { last port }, where the module is always 0
gigabitethernet module/{ first port } - { last port }, where the module is always 0
–![]() port-channel port-channel-number - port-channel-number, where the port-channel-number is 1 to 6
port-channel port-channel-number - port-channel-number, where the port-channel-number is 1 to 6

Note When you use the interface range command with port channels, the first and last port-channel number must be active port channels.
- You must add a space between the first interface number and the hyphen when entering an interface-rang.
For example, gigabitethernet 0/1 - 4 is a valid range; gigabit ethernet0/1-4 is not.
- The VLAN interfaces must have been configured with the interface vlan command. The show running-config privileged EXEC command displays the configured VLAN interfaces. VLAN interfaces not displayed by the show running-config command cannot be used as interface-ranges.
- All interfaces defined as in a range must be the same type (all Fast Ethernet ports, all Gigabit Ethernet ports, all EtherChannel ports, or all VLANs), but you can combine multiple interface types in a macro.
This example shows how to define an interface-range named enet_list to include ports 1 and 2 and to verify the macro configuration:
This example shows how to create a multiple-interface macro named macro1 :
This example shows how to enter interface-range configuration mode for the interface-range macro enet_list :
This example shows how to delete the interface-range macro enet_list and to verify that it was deleted.
Using the Ethernet Management Port (Catalyst 2960-S Only)

Note![]() The Ethernet management port is not supported on Catalyst 2960 switches.
The Ethernet management port is not supported on Catalyst 2960 switches.
- Understanding the Ethernet Management Port
- Supported Features on the Ethernet Management Port
- Configuring the Ethernet Management Port
- TFTP and the Ethernet Management Port
Understanding the Ethernet Management Port
The Ethernet management port, also referred to as the Fa0 or fastethernet0 port, is a Layer 3 host port to which you can connect a PC. You can use the Ethernet management port instead of the switch console port for network management. When managing a switch stack, connect the PC to the Ethernet management port on a Catalyst 2960-S stack member.
When connecting a PC to the Ethernet management port, you must assign an IP address.
For a Catalyst 2960-S standalone switch, connect the Ethernet management port to the PC as shown in Figure 1-3.
Figure 1-3 Connecting a Switch to a PC
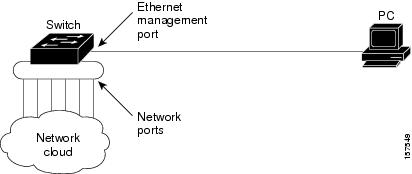
In a Catalyst 2960-S stack, all the Ethernet management ports on the stack members are connected to a hub to which the PC is connected. As shown in Figure 1-4, the active link is from the Ethernet management port on the stack master (switch 2) through the hub, to the PC. If the stack master fails and a new stack master is elected, the active link is now from the Ethernet management port on the new stack master to the PC.
Figure 1-4 Connecting a Switch Stack to a PC

Supported Features on the Ethernet Management Port
The Ethernet management port supports these features:
- Express Setup (only in switch stacks)
- Network Assistant
- Telnet with passwords
- TFTP
- Secure Shell (SSH)
- DHCP-based autoconfiguration
- SMNP (only the ENTITY-MIB and the IF-MIB)
- IP ping
- Interface features
–![]() Speed—10 Mb/s, 100 Mb/s, and autonegotiation
Speed—10 Mb/s, 100 Mb/s, and autonegotiation
–![]() Duplex mode—Full, half, and autonegotiation
Duplex mode—Full, half, and autonegotiation

Configuring the Ethernet Management Port
To specify the Ethernet management port in the CLI, enter fastethernet0.
To disable the port, use the shutdown interface configuration command. To enable the port, use the no shutdown interface configuration command.
To find out the link status to the PC, you can monitor the LED for the Ethernet management port. The LED is green (on) when the link is active, and the LED is off when the link is down. The LED is amber when there is a POST failure.
To display the link status, use the show interfaces fastethernet 0 privileged EXEC command.
TFTP and the Ethernet Management Port
Use the commands in Table 1-2 when using TFTP to download or upload a configuration file to the boot loader.
|
|
|
|---|---|
Displays the currently cached ARP1 table when this command is entered without the ip_address parameter. Enables ARP to associate a MAC address with the specified IP address when this command is entered with the ip_address parameter. |
|
Sends ICMP ECHO_REQUEST packets to the specified network host. |
|
Loads and boots an executable image from the TFTP server and enters the command-line interface. For more details, see the command reference for this release. |
|
copy tftp:/ source-file-url filesystem :/ destination-file-url |
Copies a Cisco IOS image from the TFTP server to the specified location. For more details, see the command reference for this release. |
|
|
Configuring Ethernet Interfaces
These sections contain this configuration information:
- Default Ethernet Interface Configuration
- Setting the Type of a Dual-Purpose Uplink Port
- Setting the Type of a Dual-Purpose Uplink Port
- Configuring Interface Speed and Duplex Mode
- Configuring IEEE 802.3x Flow Control
- Configuring Auto-MDIX on an Interface
- Configuring a Power Management Mode on a PoE Port
- Budgeting Power for Devices Connected to a PoE Port
- Configuring Power Policing
- Adding a Description for an Interface
Default Ethernet Interface Configuration
Table 1-3 shows the Ethernet interface default configuration. For more details on the VLAN parameters listed in the table, see Chapter1, “Configuring VLANs” For details on controlling traffic to the port, see Chapter1, “Configuring Port-Based Traffic Control”
|
|
|
|---|---|
Flow control is set to receive : off. It is always off for sent packets. |
|
Disabled on all Ethernet ports. Chapter1, “Configuring EtherChannels and Link-State Tracking” |
|
Port blocking (unknown multicast and unknown unicast traffic) |
Disabled (not blocked). See the “Configuring Port Blocking” section. |
Disabled. See the “Default Storm Control Configuration” section. |
|
Disabled. See the “Configuring Protected Ports” section. |
|
Disabled. See the “Default Port Security Configuration” section. |
|
Disabled. See the “Default Optional Spanning-Tree Configuration” section. |
|
| Note The switch might not support a pre-standard powered device—such as Cisco IP phones and access points that do not fully support IEEE 802.3af—if that powered device is connected to the switch through a crossover cable. This is regardless of whether auto-MIDX is enabled on the switch port. |
|
Setting the Type of a Dual-Purpose Uplink Port

Note![]() Only Catalyst 2960 switches have dual-purpose uplinks ports.
Only Catalyst 2960 switches have dual-purpose uplinks ports.
Some switches support dual-purpose uplink ports. By default, the switch dynamically selects the interface type that first links up. However, you can use the media-type interface configuration command to manually select the RJ-45 connector or the SFP module connector. For more information, see the “Dual-Purpose Uplink Ports” section.
Beginning in privileged EXEC mode, follow these steps to select which dual-purpose uplink to activate so that you can set the speed and duplex. This procedure is optional.
|
|
|
|
|---|---|---|
Specify the dual-purpose uplink port to be configured, and enter interface configuration mode. |
||
Select the interface and type of a dual-purpose uplink port. The keywords have these meanings:
For information about setting the speed and duplex, see the “Speed and Duplex Configuration Guidelines” section. |
||
To return to the default setting, use the media-type auto interface or the no media-type interface configuration commands.
e switch configures both types to autonegotiate speed and duplex (the default). If you configure auto-select, you cannot configure the speed and duplex interface configuration commands.
When the switch powers on or when you enable a dual-purpose uplink port through the shutdown and the no shutdown interface configuration commands, the switch gives preference to the SFP module interface. In all other situations, the switch selects the active link based on which type first links up.
The switch operates with 100BASE- x (where - x is -BX, -FX-FE, -LX) SFP modules as follows:
- When the 100BASE - x SFP module is inserted into the module slot and there is no link on the RJ-45 side, the switch disables the RJ-45 interface and selects the SFP module interface. This is the behavior even if there is no cable connected and if there is no link on the SFP module side.
- When the 100BASE- x SFP module is inserted and there is a link on the RJ-45 side, the switch continues with that link. If the link goes down, the switch disables the RJ-45 side and selects the SFP module interface.
- When the 100BASE- x SFP module is removed, the switch again dynamically selects the type (auto-select) and re-enables the RJ-45 side.
The switch does not have this behavior with 100BASE-FX-GE SFP modules.
Configuring Interface Speed and Duplex Mode
Depending on the supported port types, Ethernet interfaces on the switch operate at 10, 100, or 1000 Mb/s, or 10,000 Mb/s and in either full- or half-duplex mode. In full-duplex mode, two stations can send and receive traffic at the same time. Normally, 10-Mb/s ports operate in half-duplex mode, which means that stations can either receive or send traffic.
Switch models can include combinations of Fast Ethernet (10/100-Mb/s) ports, Gigabit Ethernet (10/100/1000-Mb/s) ports, 10-Gigabit module ports, and small form-factor pluggable (SFP) module slots supporting SFP modules.
These sections describe how to configure the interface speed and duplex mode:
Speed and Duplex Configuration Guidelines
When configuring an interface speed and duplex mode, note these guidelines:
- Fast Ethernet (10/100-Mb/s) ports support all speed and duplex options.
- Gigabit Ethernet (10/100/1000-Mb/s) ports support all speed options and all duplex options (auto, half, and full). However, Gigabit Ethernet ports operating at 1000 Mb/s do not support half-duplex mode.
- For SFP module ports, the speed and duplex CLI options change depending on the SFP module type:
–![]() The 1000BASE- x (where - x is -BX, -CWDM, -LX, -SX, and -ZX) SFP module ports support the nonegotiate keyword in the speed interface configuration command. Duplex options are not supported.
The 1000BASE- x (where - x is -BX, -CWDM, -LX, -SX, and -ZX) SFP module ports support the nonegotiate keyword in the speed interface configuration command. Duplex options are not supported.
–![]() The 1000BASE-T SFP module ports support the same speed and duplex options as the 10/100/1000-Mb/s ports.
The 1000BASE-T SFP module ports support the same speed and duplex options as the 10/100/1000-Mb/s ports.
–![]() The 100BASE- x (where - x is -BX, -CWDM, -LX, -SX, and -ZX) SFP module ports support only 100 Mb/s. These modules support full- and half- duplex options but do not support autonegotiation.
The 100BASE- x (where - x is -BX, -CWDM, -LX, -SX, and -ZX) SFP module ports support only 100 Mb/s. These modules support full- and half- duplex options but do not support autonegotiation.
For information about which SFP modules are supported on your switch, see the product release notes.
- If both ends of the line support autonegotiation, we highly recommend the default setting of auto negotiation.
- If one interface supports autonegotiation and the other end does not, configure duplex and speed on both interfaces; do not use the auto setting on the supported side.
- When STP is enabled and a port is reconfigured, the switch can take up to 30 seconds to check for loops. The port LED is amber while STP reconfigures.

Setting the Interface Speed and Duplex Parameters
Beginning in privileged EXEC mode, follow these steps to set the speed and duplex mode for a physical interface:
|
|
|
|
|---|---|---|
Specify the physical interface to be configured, and enter interface configuration mode. |
||
speed { 10 | 100 | 1000 | auto [ 10 | 100 | 1000 ] | nonegotiate } |
Enter the appropriate speed parameter for the interface:
For more information about speed settings, see the “Speed and Duplex Configuration Guidelines” section. |
|
Enter the duplex parameter for the interface. Enable half-duplex mode (for interfaces operating only at 10 or 100 Mb/s). You cannot configure half-duplex mode for interfaces operating at 1000 Mb/s. For more information about duplex settings, see the “Speed and Duplex Configuration Guidelines” section. |
||
Use the no speed and no duplex interface configuration commands to return the interface to the default speed and duplex settings (autonegotiate). To return all interface settings to the defaults, use the default interface interface-id interface configuration command.
This example shows how to set the interface speed to 10 Mb/s and the duplex mode to half on a 10/100 Mb/s port:
This example shows how to set the interface speed to 100 Mb/s on a 10/100/1000 Mb/s port:
Configuring IEEE 802.3x Flow Control
Flow control enables connected Ethernet ports to control traffic rates during congestion by allowing congested nodes to pause link operation at the other end. If one port experiences congestion and cannot receive any more traffic, it notifies the other port by sending a pause frame to stop sending until the condition clears. Upon receipt of a pause frame, the sending device stops sending any data packets, which prevents any loss of data packets during the congestion period.

Note![]() Ports on the switch can receive, but not send, pause frames.
Ports on the switch can receive, but not send, pause frames.
You use the flowcontrol interface configuration command to set the interface’s ability to receive pause frames to on, off, or desired. The default state is off.
When set to desired, an interface can operate with an attached device that is required to send flow-control packets or with an attached device that is not required to but can send flow-control packets.
These rules apply to flow control settings on the device:
- receive on (or desired): The port cannot send pause frames but can operate with an attached device that is required to or can send pause frames; the port can receive pause frames.
- receive off : Flow control does not operate in either direction. In case of congestion, no indication is given to the link partner, and no pause frames are sent or received by either device.

Note![]() For details on the command settings and the resulting flow control resolution on local and remote ports, see the flowcontrol interface configuration command in the command reference for this release.
For details on the command settings and the resulting flow control resolution on local and remote ports, see the flowcontrol interface configuration command in the command reference for this release.
Beginning in privileged EXEC mode, follow these steps to configure flow control on an interface:
|
|
|
|
|---|---|---|
Specify the physical interface to be configured, and enter interface configuration mode. |
||
To disable flow control, use the flowcontrol receive off interface configuration command.
This example shows how to turn on flow control on a port:
Configuring Auto-MDIX on an Interface
When automatic medium-dependent interface crossover (auto-MDIX) is enabled on an interface, the interface automatically detects the required cable connection type (straight through or crossover) and configures the connection appropriately. When connecting switches without the auto-MDIX feature, you must use straight-through cables to connect to devices such as servers, workstations, or routers and crossover cables to connect to other switches or repeaters. With auto-MDIX enabled, you can use either type of cable to connect to other devices, and the interface automatically corrects for any incorrect cabling. For more information about cabling requirements, see the hardware installation guide.
Auto-MDIX is enabled by default. When you enable auto-MDIX, you must also set the interface speed and duplex to auto so that the feature operates correctly.
Auto-MDIX is supported on all 10/100 and 10/100/1000-Mb/s interfaces. It is not supported on 1000BASE-SX or -LX SFP module interfaces.
Table 1-4 shows the link states that result from auto-MDIX settings and correct and incorrect cabling.
|
|
|
|
|
|---|---|---|---|
Beginning in privileged EXEC mode, follow these steps to configure auto-MDIX on an interface:
To disable auto-MDIX, use the no mdix auto interface configuration command.
This example shows how to enable auto-MDIX on a port:
Configuring a Power Management Mode on a PoE Port

Note![]() PoE commands are supported only when the switch is running the LAN base image. Power over Ethernet Plus (PoE+) is supported only on Catalyst 2960-S switches.
PoE commands are supported only when the switch is running the LAN base image. Power over Ethernet Plus (PoE+) is supported only on Catalyst 2960-S switches.
For most situations, the default configuration (auto mode) works well, providing plug-and-play operation. No further configuration is required. However, use the following procedure to give a PoE port higher priority, to make it data only, or to specify a maximum wattage to disallow high-power powered devices on a port.

Note![]() When you make PoE configuration changes, the port being configured drops power. Depending on the new configuration, the state of the other PoE ports, and the state of the power budget, the port might not be powered up again. For example, port 1 is in the auto and on state, and you configure it for static mode. The switch removes power from port 1, detects the powered device, and repowers the port. If port 1 is in the auto and on state and you configure it with a maximum wattage of 10 W, the switch removes power from the port and then redetects the powered device. The switch repowers the port only if the powered device is a Class 1, Class 2, or a Cisco-only powered device.
When you make PoE configuration changes, the port being configured drops power. Depending on the new configuration, the state of the other PoE ports, and the state of the power budget, the port might not be powered up again. For example, port 1 is in the auto and on state, and you configure it for static mode. The switch removes power from port 1, detects the powered device, and repowers the port. If port 1 is in the auto and on state and you configure it with a maximum wattage of 10 W, the switch removes power from the port and then redetects the powered device. The switch repowers the port only if the powered device is a Class 1, Class 2, or a Cisco-only powered device.
Beginning in privileged EXEC mode, follow these steps to configure a power management mode on a PoE-capable port:
For information about the output of the show power inline user EXEC command, see the command reference for this release. For more information about PoE-related commands, see the “Troubleshooting Power over Ethernet Switch Ports” section. For information about configuring voice VLAN, see Chapter1, “Configuring Voice VLAN”
Budgeting Power for Devices Connected to a PoE Port
When Cisco powered devices are connected to PoE ports, the switch uses Cisco Discovery Protocol (CDP) to determine the actual power consumption of the devices, and the switch adjusts the power budget accordingly. The CDP protocol works with Cisco powered devices and does not apply to IEEE third-party powered devices. For these devices, when the switch grants a power request, the switch adjusts the power budget according to the powered-device IEEE classification. If the powered device is a Class 0 (class status unknown) or a Class 3, the switch budgets 15,400 milliwatts for the device, regardless of the actual amount of power needed. If the powered device reports a higher class than its actual consumption or does not support power classification (defaults to Class 0), the switch can power fewer devices because it uses the IEEE class information to track the global power budget.
By using the power inline consumption wattage configuration command, you can override the default power requirement specified by the IEEE classification. The difference between what is mandated by the IEEE classification and what is actually needed by the device is reclaimed into the global power budget for use by additional devices. You can then extend the switch power budget and use it more effectively.
For example, if the switch budgets 15,400 milliwatts on each PoE port, you can connect only 24 Class 0 powered devices. If your Class 0 device power requirement is actually 5000 milliwatts, you can set the consumption wattage to 5000 milliwatts and connect up to 48 devices. The total PoE output power available on a 24-port or 48-port switch is 370,000 milliwatts.


Note![]() When you manually configure the power budget, you must also consider the power loss over the cable between the switch and the powered device.
When you manually configure the power budget, you must also consider the power loss over the cable between the switch and the powered device.
When you enter the power inline consumption default wattage or the no power inline consumption default global configuration command, or the power inline consumption wattage or the no power inline consumption interface configuration command this caution message appears:
If the power supply is over-subscribed to by up to 20 percent, the switch continues to operate but its reliability is reduced. If the power supply is subscribed to by more than 20 percent, the short-circuit protection circuitry triggers and shuts the switch down.
For more information about the IEEE power classifications, see the “Power over Ethernet Ports” section.
Beginning in privileged EXEC mode, follow these steps to configure the amount of power budgeted to a powered device connected to each PoE port on a switch:
To return to the default setting, use the no power inline consumption default global configuration command.
Beginning in privileged EXEC mode, follow these steps to configure amount of power budgeted to a powered device connected to a specific PoE port:
To return to the default setting, use the no power inline consumption interface configuration command.
For information about the output of the show power inline consumption privileged EXEC command, see the command reference for this release.
Configuring Power Policing
By default, the switch monitors the real-time power consumption of connected powered devices. You can configure the switch to police the power usage. By default, policing is disabled.
For more information about the cutoff power value, the power consumption values that the switch uses, and the actual power consumption value of the connected device, see the “Power Monitoring and Power Policing” section.
Beginning in privileged EXEC mode, follow these steps to enable policing of the real-time power consumption of a powered device connected to a PoE port:
To disable policing of the real-time power consumption, use the no power inline police interface configuration command. To disable error recovery for PoE error-disabled cause, use the no errdisable recovery cause inline-power global configuration command.
For information about the output from the show power inline police privileged EXEC command, see the command reference for this release.
Adding a Description for an Interface
You can add a description about an interface to help you remember its function. The description appears in the output of these privileged EXEC commands: show configuration , show running-config , and show interfaces .
Beginning in privileged EXEC mode, follow these steps to add a description for an interface:
|
|
|
|
|---|---|---|
Specify the interface for which you are adding a description, and enter interface configuration mode. |
||
Use the no description interface configuration command to delete the description.
This example shows how to add a description on a port and how to verify the description:
Configuring Layer 3 SVIs

Note![]() Only switches running the LAN base image support Layer 3 SVIs for static routing.
Only switches running the LAN base image support Layer 3 SVIs for static routing.
You should configure SVIs for any VLANs for which you want to route traffic. SVIs are created when you enter a VLAN ID following the interface vlan global configuration command. To delete an SVI, use the no interface vlan global configuration command. You cannot delete VLAN 1.

Note![]() When you create an SVI, it does not become active until you associate it with a physical port. For information about assigning Layer 2 ports to VLANs, see Chapter1, “Configuring VLANs”
When you create an SVI, it does not become active until you associate it with a physical port. For information about assigning Layer 2 ports to VLANs, see Chapter1, “Configuring VLANs”
A Layer 3 switch can have an IP address assigned to each SVI, but the switch supports static routing on 16 SVIs. All Layer 3 interfaces require an IP address to route traffic. This procedure shows how to configure an interface as a Layer 3 interface and how to assign an IP address to an interface.
Beginning in privileged EXEC mode, follow these steps to configure a Layer 3 SVI:
|
|
|
|
|---|---|---|
Specify the VLAN to be configured as a Layer 3 SVI, and enter interface configuration mode. |
||
show interfaces [ interface-id ] |
||
To remove an IP address from an SVI, use the no ip address interface configuration command.
This example shows how to configure a Layer 3 SVI and to assign it an IP address:
Configuring the System MTU
The default maximum transmission unit (MTU) size for frames received and transmitted on all interfaces is 1500 bytes. You can increase the MTU size for all interfaces operating at 10 or 100 Mb/s by using the system mtu global configuration command. You can increase the MTU size to support jumbo frames on all Gigabit Ethernet interfaces by using the system mtu jumbo global configuration command.
Gigabit Ethernet ports are not affected by the system mtu command; 10/100 ports are not affected by the system mtu jumbo command. If you do not configure the system mtu jumbo command, the setting of the system mtu command applies to all Gigabit Ethernet interfaces.
You cannot set the MTU size for an individual interface; you set it for all 10/100 or all Gigabit Ethernet interfaces. When you change the system or jumbo MTU size, you must reset the switch before the new configuration takes effect.
Frames sizes that can be received by the switch CPU are limited to 1998 bytes, no matter what value was entered with the system mtu or system mtu jumbo commands. Although frames that are forwarded are typically not received by the CPU, in some cases, packets are sent to the CPU, such as traffic sent to control traffic, SNMP, or Telnet.

Note![]() If Layer 2 Gigabit Ethernet interfaces are configured to accept frames greater than the 10/100 interfaces, jumbo frames received on a Layer 2 Gigabit Ethernet interface and sent on a Layer 2 10/100 interface are dropped.
If Layer 2 Gigabit Ethernet interfaces are configured to accept frames greater than the 10/100 interfaces, jumbo frames received on a Layer 2 Gigabit Ethernet interface and sent on a Layer 2 10/100 interface are dropped.
Beginning in privileged EXEC mode, follow these steps to change MTU size for all 10/100 or Gigabit Ethernet interfaces:
|
|
|
|
|---|---|---|
(Optional) Change the MTU size for all interfaces on the switch that are operating at 10 or 100 Mb/s. |
||
(Optional) Change the MTU size for all Gigabit Ethernet interfaces on the switch. |
||
If you enter a value that is outside the allowed range for the specific type of interface, the value is not accepted.
Once the switch reloads, you can verify your settings by entering the show system mtu privileged EXEC command.
This example shows how to set the maximum packet size for a Gigabit Ethernet port to 1800 bytes:
This example shows the response when you try to set Gigabit Ethernet interfaces to an out-of-range number:
Monitoring and Maintaining the Interfaces
These sections contain interface monitoring and maintenance information:
- Monitoring Interface Status
- Clearing and Resetting Interfaces and Counters
- Shutting Down and Restarting the Interface
- Setting the Type of a Dual-Purpose Uplink Port
Monitoring Interface Status
Commands entered at the privileged EXEC prompt display information about the interface, including the versions of the software and the hardware, the configuration, and statistics about the interfaces. Table 1-5 lists some of these interface monitoring commands. (You can display the full list of show commands by using the show ? command at the privileged EXEC prompt.) These commands are fully described in the Cisco IOS Interface Command Reference, Release 12.2 from the Cisco.com page under Documentation > Cisco IOS Software > 12.2 Mainline > Command References.
Clearing and Resetting Interfaces and Counters
Table 1-6 lists the privileged EXEC mode clear commands that you can use to clear counters and reset interfaces.
|
|
|
|---|---|
To clear the interface counters shown by the show interfaces privileged EXEC command, use the clear counters privileged EXEC command. The clear counters command clears all current interface counters from the interface unless you specify optional arguments that clear only a specific interface type from a specific interface number.

Note![]() The clear counters privileged EXEC command does not clear counters retrieved by using Simple Network Management Protocol (SNMP), but only those seen with the show interface privileged EXEC command.
The clear counters privileged EXEC command does not clear counters retrieved by using Simple Network Management Protocol (SNMP), but only those seen with the show interface privileged EXEC command.
Shutting Down and Restarting the Interface
Shutting down an interface disables all functions on the specified interface and marks the interface as unavailable on all monitoring command displays. This information is communicated to other network servers through all dynamic routing protocols. The interface is not mentioned in any routing updates.
Beginning in privileged EXEC mode, follow these steps to shut down an interface:
|
|
|
|
|---|---|---|
interface { vlan vlan-id } | {{ fastethernet | gigabitethernet } interface-id } | { port-channel port-channel-number } |
||
 Feedback
Feedback