- Index
- Preface
- Overview
- Using the Command-Line Interface
- Assigning the Switch IP Address and Default Gateway
- Clustering Switches
- Administering the Switch
- Configuring SDM Templates
- Configuring Switch-Based Authentication
- Configuring 802.1x Port-Based Authentication
- Configuring Interface Characteristics
- Configuring Smartports Macros
- Configuring VLANs
- Configuring VTP
- Configuring Private VLANs
- Configuring Voice VLAN
- Configuring 802.1Q and Layer 2 Protocol Tunneling
- Configuring STP
- Configuring MSTP
- Configuring Optional Spanning-Tree Features
- Configuring Flex Links
- Configuring DHCP Features and IP Source Guard
- Configuring Dynamic ARP Inspection
- Configuring IGMP Snooping and MVR
- Configuring Port-Based Traffic Control
- Configuring CDP
- Configuring UDLD
- Configuring SPAN and RSPAN
- Configuring RMON
- Configuring System Message Logging
- Configuring SNMP
- Configuring Network Security with ACLs
- Configuring QoS
- Configuring EtherChannels
- Configuring IP Unicast Routing
- Configuring HSRP
- Configuring IP Multicast Routing
- Configuring MSDP
- Configuring Fallback Bridging
- Troubleshooting
- Supported MIBs
- Working with the Cisco IOS File System, Configuration Files, and Software Images
- Unsupported Commands in Cisco IOS Release 12.2(25)SE
- Understanding DHCP Features
- Configuring DHCP Features
- Default DHCP Configuration
- DHCP Snooping Configuration Guidelines
- Configuring the DHCP Server
- Configuring the DHCP Relay Agent
- Specifying the Packet Forwarding Address
- Enabling DHCP Snooping and Option 82
- Enabling DHCP Snooping on Private VLANs
- Enabling the Cisco IOS DHCP Server Database
- Enabling the DHCP Snooping Binding Database Agent
- Displaying DHCP Snooping Information
- Understanding IP Source Guard
- Configuring IP Source Guard
- Displaying IP Source Guard Information
Configuring DHCP Features and IP Source Guard
This chapter describes how to configure DHCP snooping and the option-82 data insertion features on the Catalyst 3560 switch. It also describes how to configure the IP source guard feature.

Note ![]() For complete syntax and usage information for the commands used in this chapter, see the command reference for this release, and see the "DHCP Commands" section in the Cisco IOS IP Command Reference, Volume 1 of 3: Addressing and Services, Release 12.2.
For complete syntax and usage information for the commands used in this chapter, see the command reference for this release, and see the "DHCP Commands" section in the Cisco IOS IP Command Reference, Volume 1 of 3: Addressing and Services, Release 12.2.
This chapter consists of these sections:
•![]() Displaying DHCP Snooping Information
Displaying DHCP Snooping Information
•![]() Understanding IP Source Guard
Understanding IP Source Guard
•![]() Displaying IP Source Guard Information
Displaying IP Source Guard Information
Understanding DHCP Features
DHCP is widely used in LAN environments to dynamically assign host IP addresses from a centralized server, which significantly reduces the overhead of administration of IP addresses. DHCP also helps conserve the limited IP address space because IP addresses no longer need to be permanently assigned to hosts; only those hosts that are connected to the network consume IP addresses.
The switch supports these DHCP features:
•![]() Cisco IOS DHCP Server Database
Cisco IOS DHCP Server Database
•![]() DHCP Snooping Binding Database
DHCP Snooping Binding Database
For information about the DHCP client, see the "Configuring DHCP" section of the "IP Addressing and Services" section of the Cisco IOS IP Configuration Guide, Release 12.2.
DHCP Server
The DHCP server assigns IP addresses from specified address pools on a switch or router to DHCP clients and manages them. If the DHCP server cannot give the DHCP client the requested configuration parameters from its database, it can forward the request to one or more secondary DHCP servers defined by the network administrator.
DHCP Relay Agent
A DHCP relay agent is a Layer 3 device that forwards DHCP packets between clients and servers. Relay agents forward requests and replies between clients and servers when they are not on the same physical subnet. Relay agent forwarding is different from the normal Layer 2 forwarding, in which IP datagrams are switched transparently between networks. Relay agents receive DHCP messages and generate new DHCP messages to send on egress interfaces.
DHCP Snooping
DHCP snooping is a DHCP security feature that provides network security by filtering untrusted DHCP messages and by building and maintaining a DHCP snooping binding database, also referred to as a DHCP snooping binding table. For more information about this database, see the "Displaying DHCP Snooping Information" section.
DHCP snooping acts like a firewall between untrusted hosts and DHCP servers. You use DHCP snooping to differentiate between untrusted interfaces connected to the end user and trusted interfaces connected to the DHCP server or another switch.

Note ![]() For DHCP snooping to function properly, all DHCP servers must be connected to the switch through trusted interfaces.
For DHCP snooping to function properly, all DHCP servers must be connected to the switch through trusted interfaces.
An untrusted DHCP message is a message that is received from outside the network or firewall. When you use DHCP snooping in a service-provider environment, an untrusted message is sent from a device that is not in the service-provider network, such as a customer's switch. Messages from unknown devices are untrusted because they can be sources of traffic attacks.
The DHCP snooping binding database has the MAC address, the IP address, the lease time, the binding type, the VLAN number, and the interface information that corresponds to the local untrusted interfaces of a switch. It does not have information regarding hosts interconnected with a trusted interface.
In a service-provider network, a trusted interface is connected to a port on a device in the same network. An untrusted interface is connected to an untrusted interface in the network or to an interface on a device that is not in the network.
When a switch receives a packet on an untrusted interface and the interface belongs to a VLAN in which DHCP snooping is enabled, the switch compares the source MAC address and the DHCP client hardware address. If the addresses match (the default), the switch forwards the packet. If the addresses do not match, the switch drops the packet.
The switch drops a DHCP packet when one of these situations occurs:
•![]() A packet from a DHCP server, such as a DHCPOFFER, DHCPACK, DHCPNAK, or DHCPLEASEQUERY packet, is received from outside the network or firewall.
A packet from a DHCP server, such as a DHCPOFFER, DHCPACK, DHCPNAK, or DHCPLEASEQUERY packet, is received from outside the network or firewall.
•![]() A packet is received on an untrusted interface, and the source MAC address and the DHCP client hardware address do not match.
A packet is received on an untrusted interface, and the source MAC address and the DHCP client hardware address do not match.
•![]() The switch receives a DHCPRELEASE or DHCPDECLINE broadcast message that has a MAC address in the DHCP snooping binding database, but the interface information in the binding database does not match the interface on which the message was received.
The switch receives a DHCPRELEASE or DHCPDECLINE broadcast message that has a MAC address in the DHCP snooping binding database, but the interface information in the binding database does not match the interface on which the message was received.
•![]() A DHCP relay agent forwards a DHCP packet that includes a relay-agent IP address that is not 0.0.0.0, or the relay agent forwards a packet that includes option-82 information to an untrusted port.
A DHCP relay agent forwards a DHCP packet that includes a relay-agent IP address that is not 0.0.0.0, or the relay agent forwards a packet that includes option-82 information to an untrusted port.
Option-82 Data Insertion
In residential, metropolitan Ethernet-access environments, DHCP can centrally manage the IP address assignments for a large number of subscribers. When the DHCP option-82 feature is enabled on the switch, a subscriber device is identified by the switch port through which it connects to the network (in addition to its MAC address). Multiple hosts on the subscriber LAN can be connected to the same port on the access switch and are uniquely identified.

Note ![]() The DHCP option-82 feature is supported only when DHCP snooping is enabled globally and on the VLANs to which subscriber devices using this feature are assigned.
The DHCP option-82 feature is supported only when DHCP snooping is enabled globally and on the VLANs to which subscriber devices using this feature are assigned.
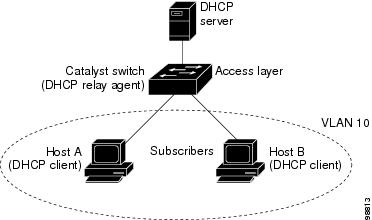
Figure 20-1 is an example of a metropolitan Ethernet network in which a centralized DHCP server assigns IP addresses to subscribers connected to the switch at the access layer. Because the DHCP clients and their associated DHCP server do not reside on the same IP network or subnet, a DHCP relay agent (the Catalyst switch) is configured with a helper address to enable broadcast forwarding and to transfer DHCP messages between the clients and the server.
Figure 20-1 DHCP Relay Agent in a Metropolitan Ethernet Network
When you enable the DHCP snooping information option 82 on the switch, this sequence of events occurs:
•![]() The host (DHCP client) generates a DHCP request and broadcasts it on the network.
The host (DHCP client) generates a DHCP request and broadcasts it on the network.
•![]() When the switch receives the DHCP request, it adds the option-82 information in the packet. The option-82 information is the switch MAC address (the remote ID suboption) and the port identifier, vlan-mod-port, from which the packet is received (the circuit ID suboption).
When the switch receives the DHCP request, it adds the option-82 information in the packet. The option-82 information is the switch MAC address (the remote ID suboption) and the port identifier, vlan-mod-port, from which the packet is received (the circuit ID suboption).
•![]() If the IP address of the relay agent is configured, the switch adds this IP address in the DHCP packet.
If the IP address of the relay agent is configured, the switch adds this IP address in the DHCP packet.
•![]() The switch forwards the DHCP request that includes the option-82 field to the DHCP server.
The switch forwards the DHCP request that includes the option-82 field to the DHCP server.
•![]() The DHCP server receives the packet. If the server is option-82-capable, it can use the remote ID, the circuit ID, or both to assign IP addresses and implement policies, such as restricting the number of IP addresses that can be assigned to a single remote ID or circuit ID. Then the DHCP server echoes the option-82 field in the DHCP reply.
The DHCP server receives the packet. If the server is option-82-capable, it can use the remote ID, the circuit ID, or both to assign IP addresses and implement policies, such as restricting the number of IP addresses that can be assigned to a single remote ID or circuit ID. Then the DHCP server echoes the option-82 field in the DHCP reply.
•![]() The DHCP server unicasts the reply to the switch if the request was relayed to the server by the switch. The switch verifies that it originally inserted the option-82 data by inspecting the remote ID and possibly the circuit ID fields. The switch removes the option-82 field and forwards the packet to the switch port that connects to the DHCP client that sent the DHCP request.
The DHCP server unicasts the reply to the switch if the request was relayed to the server by the switch. The switch verifies that it originally inserted the option-82 data by inspecting the remote ID and possibly the circuit ID fields. The switch removes the option-82 field and forwards the packet to the switch port that connects to the DHCP client that sent the DHCP request.
When the previously described sequence of events occurs, the values in these fields in Figure 20-2 do not change:
•![]() Circuit ID suboption fields
Circuit ID suboption fields
–![]() Suboption type
Suboption type
–![]() Length of the suboption type
Length of the suboption type
–![]() Circuit ID type
Circuit ID type
–![]() Length of the circuit ID type
Length of the circuit ID type
•![]() Remote ID suboption fields
Remote ID suboption fields
–![]() Suboption type
Suboption type
–![]() Length of the suboption type
Length of the suboption type
–![]() Remote ID type
Remote ID type
–![]() Length of the circuit ID type
Length of the circuit ID type
In the port field of the circuit ID suboption, the port numbers start at 3. For example, on a Catalyst 3560-24PS switch, port 3 is the Fast Ethernet 0/1 port, port 4 is the Fast Ethernet 0/2 port, port 5 is the Fast Ethernet 0/3 port, and so on. Port 27 is the small form-factor pluggable (SFP) module slot 0/1, and port 28 is the SFP module slot 0/2.
Figure 20-2 shows the packet formats for the remote ID suboption and the circuit ID suboption. For the circuit ID suboption, the module number corresponds to the switch number in the stack. The switch uses the packet formats when DHCP snooping is globally enabled and when the ip dhcp snooping information option global configuration command is entered.
Figure 20-2 Suboption Packet Formats

Cisco IOS DHCP Server Database
During the DHCP-based autoconfiguration process, the designated DHCP server uses the Cisco IOS DHCP server database. It has IP addresses, address bindings, and configuration parameters, such as the boot file.
An address binding is a mapping between an IP address and a MAC address of a host in the Cisco IOS DHCP server database. You can manually assign the client IP address, or the DHCP server can allocate an IP address from a DHCP address pool. For more information about manual and automatic address bindings, see the "Configuring DHCP" chapter of the Cisco IOS IP Configuration Guide,
Release 12.2.
DHCP Snooping Binding Database
When DHCP snooping is enabled, the switch uses the DHCP snooping binding database to store information about untrusted interfaces. The database can have up to 512 bindings.
Each database entry (binding) has an IP address, an associated MAC address, the lease time (in hexadecimal format), the interface to which the binding applies, and the VLAN to which the interface belongs. A checksum value, the end of each entry, is the number of bytes from the start of the file to end of the entry. Each entry is 72 bytes, followed by a space and then the checksum value.
To keep the bindings when the switch reloads, you must use the DHCP snooping database agent. If the agent is disabled, the switch loses its DHCP snooping bindings and its connectivity when it reloads. The switch also loses connectivity.
The database agent stores the bindings in a file at a configured location. When reloading, the switch reads the binding file to build the DHCP snooping binding database. The switch keeps the file current by updating it when the database changes.
When a switch learns of new bindings or when it loses bindings, the switch updates the entries in the database and in the binding file. The frequency at which database and file are updated is based on a configurable delay, and the updates are batched. If the database and file are not updated in a specified time (set by the write-delay and abort-timeout values), the update stops.
This is the format of the file that has the bindings:
<initial-checksum>
TYPE DHCP-SNOOPING
VERSION 1
BEGIN
<entry-1> <checksum-1>
<entry-2> <checksum-1-2>
...
...
<entry-n> <checksum-1-2-..-n>
END
Each entry in the file is tagged with a checksum value that the switch uses to verify the entries when it reads the file. The initial-checksum entry on the first line distinguishes entries associated with the latest file update from entries associated with a previous file update.
This is an example of a binding file:
3ebe1518
TYPE DHCP-SNOOPING
VERSION 1
BEGIN
1.1.1.1 512 0001.0001.0005 3EBE2881 Gi0/1 e5e1e733
1.1.1.1 512 0001.0001.0002 3EBE2881 Gi0/1 4b3486ec
1.1.1.1 1536 0001.0001.0004 3EBE2881 Gi0/1 f0e02872
1.1.1.1 1024 0001.0001.0003 3EBE2881 Gi/1 ac41adf9
1.1.1.1 1 0001.0001.0001 3EBE2881 Gi0/1 34b3273e
END
When the switch starts and the calculated checksum value equals the stored checksum value, the switch reads entries from the binding file and adds the bindings to its DHCP snooping binding database. The switch ignores an entry when one of these situations occurs:
•![]() The switch reads the entry and the calculated checksum value does not equal the stored checksum value. The entry and the ones following it are ignored.
The switch reads the entry and the calculated checksum value does not equal the stored checksum value. The entry and the ones following it are ignored.
•![]() An entry has an expired lease time (the switch might not remove a binding entry when the lease time expires).
An entry has an expired lease time (the switch might not remove a binding entry when the lease time expires).
•![]() The interface in the entry no longer exists on the system.
The interface in the entry no longer exists on the system.
•![]() The interface is a routed interface or a DHCP snooping-trusted interface.
The interface is a routed interface or a DHCP snooping-trusted interface.
Configuring DHCP Features
These sections describe how to configure the DHCP server, the DHCP relay agent, DHCP snooping, option 82, the Cisco IOS DHCP server binding database, and the DHCP snooping binding database on your switch:
•![]() DHCP Snooping Configuration Guidelines
DHCP Snooping Configuration Guidelines
•![]() Configuring the DHCP Relay Agent
Configuring the DHCP Relay Agent
•![]() Specifying the Packet Forwarding Address
Specifying the Packet Forwarding Address
•![]() Enabling DHCP Snooping and Option 82
Enabling DHCP Snooping and Option 82
•![]() Enabling DHCP Snooping on Private VLANs
Enabling DHCP Snooping on Private VLANs
•![]() Enabling the Cisco IOS DHCP Server Database
Enabling the Cisco IOS DHCP Server Database
•![]() Enabling the DHCP Snooping Binding Database Agent
Enabling the DHCP Snooping Binding Database Agent
Default DHCP Configuration
Table 20-1 shows the default DHCP configuration.
|
|
|
|---|---|
DHCP server |
Enabled1 |
DHCP relay agent |
Enabled2 |
DHCP packet forwarding address |
None configured |
Checking the relay agent information |
Enabled (invalid messages are dropped)2 |
DHCP relay agent forwarding policy |
Replace the existing relay agent information2 |
Cisco IOS DHCP server binding database3 |
Enabled4 |
DHCP snooping enabled globally |
Disabled |
DHCP snooping information option |
Enabled |
DHCP snooping limit rate |
None configured |
DHCP snooping trust |
Untrusted |
DHCP snooping VLAN |
Disabled |
DHCP snooping MAC address verification |
Enabled |
DHCP snooping binding database agent3 |
Enabled |
1 The switch responds to DHCP requests only if it is configured as a DHCP server. 2 The switch relays DHCP packets only if the IP address of the DHCP server is configured on the SVI of the DHCP client. 3 This feature is supported only when your switch is running the enhanced multilayer image (EMI). 4 The switch gets network addresses and configuration parameters only from a device configured as DHCP server. |
DHCP Snooping Configuration Guidelines
These are the configuration guidelines for DHCP snooping.
•![]() You must globally enable DHCP snooping on the switch.
You must globally enable DHCP snooping on the switch.
•![]() DHCP snooping is not active until DHCP snooping is enabled on a VLAN.
DHCP snooping is not active until DHCP snooping is enabled on a VLAN.
•![]() Before globally enabling DHCP snooping on the switch, make sure that the devices acting as the DHCP server and the DHCP relay agent are configured and enabled.
Before globally enabling DHCP snooping on the switch, make sure that the devices acting as the DHCP server and the DHCP relay agent are configured and enabled.
•![]() When you globally enable DHCP snooping on the switch, these Cisco IOS commands are not available until snooping is disabled. If you enter these commands, the switch returns an error message, and the configuration is not applied.
When you globally enable DHCP snooping on the switch, these Cisco IOS commands are not available until snooping is disabled. If you enter these commands, the switch returns an error message, and the configuration is not applied.
–![]() ip dhcp relay information check global configuration command
ip dhcp relay information check global configuration command
–![]() ip dhcp relay information policy global configuration command
ip dhcp relay information policy global configuration command
–![]() ip dhcp relay information trust-all global configuration command
ip dhcp relay information trust-all global configuration command
–![]() ip dhcp relay information trusted interface configuration command
ip dhcp relay information trusted interface configuration command
•![]() Before configuring the DHCP snooping information option on your switch, be sure to configure the device that is acting as the DHCP server. For example, you must specify the IP addresses that the DHCP server can assign or exclude, or you must configure DHCP options for these devices.
Before configuring the DHCP snooping information option on your switch, be sure to configure the device that is acting as the DHCP server. For example, you must specify the IP addresses that the DHCP server can assign or exclude, or you must configure DHCP options for these devices.
•![]() Before configuring the DHCP relay agent on your switch, make sure to configure the device that is acting as the DHCP server. For example, you must specify the IP addresses that the DHCP server can assign or exclude, configure DHCP options for devices, or set up the DHCP database agent.
Before configuring the DHCP relay agent on your switch, make sure to configure the device that is acting as the DHCP server. For example, you must specify the IP addresses that the DHCP server can assign or exclude, configure DHCP options for devices, or set up the DHCP database agent.
•![]() If the DHCP relay agent is enabled but DHCP snooping is disabled, the DHCP option-82 data insertion feature is not supported.
If the DHCP relay agent is enabled but DHCP snooping is disabled, the DHCP option-82 data insertion feature is not supported.
•![]() If a switch port is connected to a DHCP server, configure a port as trusted by entering the ip dhcp snooping trust interface configuration command.
If a switch port is connected to a DHCP server, configure a port as trusted by entering the ip dhcp snooping trust interface configuration command.
•![]() If a switch port is connected to a DHCP client, configure a port as untrusted by entering the no ip dhcp snooping trust interface configuration command.
If a switch port is connected to a DHCP client, configure a port as untrusted by entering the no ip dhcp snooping trust interface configuration command.
•![]() Follow these guidelines when configuring the DHCP snooping binding database:
Follow these guidelines when configuring the DHCP snooping binding database:
–![]() Because both NVRAM and the flash memory have limited storage capacity, we recommend that you store the binding file on a TFTP server.
Because both NVRAM and the flash memory have limited storage capacity, we recommend that you store the binding file on a TFTP server.
–![]() You must create an empty file at the configured URL on network-based URLs (such as TFTP and FTP) before the switch can initially write bindings to the binding file at that URL for the first time.
You must create an empty file at the configured URL on network-based URLs (such as TFTP and FTP) before the switch can initially write bindings to the binding file at that URL for the first time.
–![]() To ensure that the lease time in the database is accurate, we recommend that NTP is enabled and configured. For more information, see the "Configuring NTP" section.
To ensure that the lease time in the database is accurate, we recommend that NTP is enabled and configured. For more information, see the "Configuring NTP" section.
–![]() If NTP is not configured, the switch writes binding changes to the binding file only when the switch system clock is synchronized with NTP.
If NTP is not configured, the switch writes binding changes to the binding file only when the switch system clock is synchronized with NTP.
Configuring the DHCP Server
The switch can act as a DHCP server. By default, the Cisco IOS DHCP server and relay agent features are enabled on your switch but are not configured. These features are not operational.
For procedures to configure the switch as a DHCP server, see the "Configuring DHCP" section of the "IP addressing and Services" section of the Cisco IOS IP Configuration Guide, Release 12.2.
Configuring the DHCP Relay Agent
Beginning in privileged EXEC mode, follow these steps to enable the DHCP relay agent on the switch:
To disable the DHCP server and relay agent, use the no service dhcp global configuration command.
See the "Configuring DHCP" section of the "IP Addressing and Services" section of the Cisco IOS IP Configuration Guide, Release 12.2 for these procedures:
•![]() Checking (validating) the relay agent information
Checking (validating) the relay agent information
•![]() Configuring the relay agent forwarding policy
Configuring the relay agent forwarding policy
Specifying the Packet Forwarding Address
If the DHCP server and the DHCP clients are on different networks or subnets, you must configure the switch with the ip helper-address address interface configuration command. The general rule is to configure the command on the Layer 3 interface closest to the client. The address used in the ip helper-address command can be a specific DHCP server IP address, or it can be the network address if other DHCP servers are on the destination network segment. Using the network address enables any DHCP server to respond to requests.
Beginning in privileged EXEC mode, follow these steps to specify the packet forwarding address:
To remove the DHCP packet forwarding address, use the no ip helper-address address interface configuration command.
Enabling DHCP Snooping and Option 82
Beginning in privileged EXEC mode, follow these steps to enable DHCP snooping on the switch.
To disable DHCP snooping, use the no ip dhcp snooping global configuration command. To disable DHCP snooping on a VLAN or range of VLANs, use the no ip dhcp snooping vlan vlan-range global configuration command. To disable the insertion and removal of the option-82 field, use the no ip dhcp snooping information option global configuration command.
This example shows how to enable DHCP snooping globally and on VLAN 10 and to configure a rate limit of 100 packets per second on a port:
Switch(config)# ip dhcp snooping
Switch(config)# ip dhcp snooping vlan 10
Switch(config)# ip dhcp snooping information option
Switch(config)# interface gigabitethernet0/1
Switch(config-if)# ip dhcp snooping limit rate 100
Enabling DHCP Snooping on Private VLANs
You can enable DHCP snooping on private VLANs. If DHCP snooping is enabled, the configuration is propagated to both a primary VLAN and its associated secondary VLANs. If DHCP snooping is enabled on the primary VLAN, it is also configured on the secondary VLANs.
If DHCP snooping is already configured on the primary VLAN and you configure DHCP snooping with different settings on a secondary VLAN, the configuration for the secondary VLAN does not take effect. If DHCP snooping is not configured on the primary VLAN and you configure DHCP snooping on a secondary VLAN, the configuration takes affect only on the secondary VLAN.
When you manually configure DHCP snooping on a secondary VLAN, this message appears:
DHCP Snooping configuration may not take effect on secondary vlan XXX.
The show ip dhcp snooping privileged EXEC command output shows all VLANs, including primary and secondary private VLANs, on which DHCP snooping is enabled.
Enabling the Cisco IOS DHCP Server Database
For procedures to enable and configure the Cisco IOS DHCP server database, see the "DHCP Configuration Task List" section in the "Configuring DHCP" chapter of the Cisco IOS IP Configuration Guide, Release 12.2.
Enabling the DHCP Snooping Binding Database Agent
Beginning in privileged EXEC mode, follow these steps to enable and configure the DHCP snooping binding database agent on the switch.
To delete the database agent or binding file, use the no ip dhcp snooping database interface configuration command. To reset the timeout or delay values, use the ip dhcp snooping database timeout seconds or the ip dhcp snooping database write-delay seconds interface configuration command.
To clear the statistics of the DHCP snooping binding database agent, use the clear ip dhcp snooping database statistics privileged EXEC command. To renew the database, use the renew ip dhcp snooping database privileged EXEC command.
To delete binding entries from the DHCP snooping binding database, use the no ip dhcp snooping binding mac-address vlan vlan-id ip-address interface interface-id expiry seconds privileged EXEC command. Enter this command for each entry that you delete.
This example shows how to enable the DHCP snooping binding database agent, configure the database agent, and add binding entries to the binding database:
Switch(config)# ip dhcp snooping database flash:/database1
Switch(config)# ip dhcp snooping database timeout 30
Switch(config)# ip dhcp snooping database write-delay 30
Switch# ip dhcp snooping binding 0001.0200.0004 vlan 100 172.16.22.44 interface gigabitethernet0/1 expiry 5000
Switch# ip dhcp snooping binding 0022.0300.0008 vlan 100 172.16.24.44 interface gigabitethernet0/1 expiry 5000
Switch(config)# ip dhcp snooping binding 0004.0070.0012 vlan 100 172.16.26.44 interface gigabitethernet0/1 expiry 5000
Displaying DHCP Snooping Information
To display the DHCP snooping information, use one or more of the privileged EXEC commands in Table 20-2:
|
|
|
|---|---|
show ip dhcp snooping |
Displays the DHCP snooping configuration for a switch |
show ip dhcp snooping binding |
Displays only the dynamically configured bindings in the DHCP snooping binding database, also referred to as a binding table.1 |
show ip dhcp snooping database |
Displays the DHCP snooping binding database status and statistics. |
show up source binding |
Display the dynamically and statically configured bindings. |
1 If DHCP snooping is enabled and an interface changes to the down state, the switch does not delete the manually configured bindings. |

Note ![]() If DHCP snooping is enabled and an interface changes to the down state, the switch does not delete the statically configured bindings.
If DHCP snooping is enabled and an interface changes to the down state, the switch does not delete the statically configured bindings.
Understanding IP Source Guard
IP source guard is a security feature that restricts IP traffic on nonrouted, Layer 2 interfaces by filtering traffic based on the DHCP snooping binding database and on manually configured IP source bindings. You can use IP source guard to prevent traffic attacks caused when a host tries to use the IP address of its neighbor.
You can enable IP source guard when DHCP snooping is enabled on an untrusted interface. After IP source guard is enabled on an interface, the switch blocks all IP traffic received on the interface, except for DHCP packets allowed by DHCP snooping. A port access control list (ACL) is applied to the interface. The port ACL allows only IP traffic with s a source IP address in the IP source binding table and denies all other traffic.
The IP source binding table has bindings that are learned by DHCP snooping or are manually configured (static IP source bindings). An entry in this table has an IP address, its associated MAC address, and its associated VLAN number. The switch uses the IP source binding table only when IP source guard is enabled.
IP source guard is supported only on Layer 2 ports, including access and trunk ports.You can configure IP source guard with source IP address filtering or with source IP and MAC address filtering.
To use this feature, you must have the enhanced multilayer image (EMI) installed on your switch.
Source IP Address Filtering
When IP source guard is enabled with this option, IP traffic is filtered based on the source IP address. The switch forwards IP traffic when the source IP address matches an entry in the DHCP snooping binding database or a binding in the IP source binding table.
When a DHCP snooping binding or static IP source binding is added, changed, or deleted on an interface, the switch modifies the port ACL with the IP source binding changes and re-applies the port ACL to the interface.
If you enable IP source guard on an interface on which IP source bindings (dynamically learned by DHCP snooping or manually configured) are not configured, the switch creates and applies a port ACL that denies all IP traffic on the interface. If you disable IP source guard, the switch removes the port ACL from the interface.
Source IP and MAC Address Filtering
When IP source guard is enabled with this option, IP traffic is filtered based on the source IP and MAC addresses. The switch forwards traffic only when the source IP and MAC addresses match an entry in the IP source binding table.
When IP source guard with source IP and MAC address filtering is enabled, the switch filters IP and non-IP traffic. If the source MAC address of an IP or non-IP packet matches a valid IP source binding, the switch forwards the packet. The switch drops all other types of packets except DHCP packets.
The switch uses port security to filter source MAC addresses. The interface can shut down when a port-security violation occurs.
Configuring IP Source Guard
This section describes how to configure IP source guard on your switch.
•![]() Default IP Source Guard Configuration
Default IP Source Guard Configuration
•![]() IP Source Guard Configuration Guidelines
IP Source Guard Configuration Guidelines
•![]() Displaying IP Source Guard Information
Displaying IP Source Guard Information
Default IP Source Guard Configuration
By default, IP source guard is disabled.
IP Source Guard Configuration Guidelines
These are the configuration guides for IP source guard:
•![]() You can configure static IP bindings only on nonrouted ports. If you enter the ip source binding mac-address vlan vlan-id ip-address interface interface-id global configuration command on a routed interface, this error message appears:
You can configure static IP bindings only on nonrouted ports. If you enter the ip source binding mac-address vlan vlan-id ip-address interface interface-id global configuration command on a routed interface, this error message appears:
Static IP source binding can only be configured on switch port.
•![]() When IP source guard with source IP filtering is enabled on a VLAN, DHCP snooping must be enabled on the access VLAN to which the interface belongs.
When IP source guard with source IP filtering is enabled on a VLAN, DHCP snooping must be enabled on the access VLAN to which the interface belongs.
•![]() If you are enabling IP source guard on a trunk interface with multiple VLANs and DHCP snooping is enabled on all the VLANs, the source IP address filter is applied on all the VLANs.
If you are enabling IP source guard on a trunk interface with multiple VLANs and DHCP snooping is enabled on all the VLANs, the source IP address filter is applied on all the VLANs.

Note ![]() If IP source guard is enabled and you enable or disable DHCP snooping on a VLAN on the trunk interface, the switch might not properly filter traffic.
If IP source guard is enabled and you enable or disable DHCP snooping on a VLAN on the trunk interface, the switch might not properly filter traffic.
•![]() When IP source guard with source IP and MAC address filtering is enabled, DHCP snooping and port security must be enabled on the interface.
When IP source guard with source IP and MAC address filtering is enabled, DHCP snooping and port security must be enabled on the interface.
•![]() When configuring IP source guard on interfaces on which a private VLAN is configured, port security is not supported.
When configuring IP source guard on interfaces on which a private VLAN is configured, port security is not supported.
•![]() IP source guard is not supported on EtherChannels.
IP source guard is not supported on EtherChannels.
•![]() You can enable this feature when 802.1x port-based authentication is enabled.
You can enable this feature when 802.1x port-based authentication is enabled.
•![]() If the number of ternary content addressable memory (TCAM) entries exceeds the maximum available, the CPU usage increases.
If the number of ternary content addressable memory (TCAM) entries exceeds the maximum available, the CPU usage increases.
Enabling IP Source Guard
Beginning in privileged EXEC mode, follow these steps to enable and configure IP source guard on an interface.
To disable IP source guard with source IP address filtering, use the no ip verify source interface configuration command.
To delete a static IP source binding entry, use the no ip source binding ip-address mac-address vlan vlan-id inteface interface-id interface configuration command.
This example shows how to enable IP source guard with source IP and MAC filtering on VLANs 10
and 11:
Switch# configure terminal
Enter configuration commands, one per line. End with CNTL/Z.
Switch(config)# interface gigabitethernet0/1
Switch(config-if)# ip verify source port-security
Switch(config-if)# exit
Switch(config)# ip source binding 0100.0022.0010 vlan 10 10.0.0.2 interface gigabitethernet0/2
Switch(config)# ip source binding 0100.0230.0002 vlan 11 10.0.0.4 interface gigabitethernet0/2
Switch(config)# end
Displaying IP Source Guard Information
To display the IP source guard information, use one or more of the privileged EXEC commands in Table 20-3:
 Feedback
Feedback