Understand CWA Flow on a Client
Available Languages
Download Options
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
Contents
Introduction
This document describes the flow for the end client undergoes when connecting to a CWA WLAN.
Prerequisites
Requirements
Cisco recommends you have basic knowledge of:
- Cisco Wireless LAN Controller (WLC) 9800 series
- General understanding of Central Web Authentication (CWA) and its configuration on Identity Services Engine (ISE)
Components Used
The information in this document is based on this software and hardware versions:
- 9800-CL WLC
- Cisco AP 3802
- 9800 WLC Cisco IOS® XE v17.3.6
- Identity Service Engine (ISE) v3.1
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command.
Background Information
CWA is a type of SSID authentication that can be configured on the WLC where the end client attempting to connect is prompted to enter its username and password to a web portal that is presented to them. In short, the flow for the end client goes through when connecting to the WLAN is:
- The end client connects to the SSID that is shown on their device
- The end client is redirected to the web portal to enter its credentials
- The end client is authenticated by ISE with the credentials that were entered
- ISE replies to the WLC saying that the end client has been authenticated. ISE can push some additional attributes the client must comply when accessing the network (such a specific ACLs)
- The end client is re-associated and re-authenticated and finally gains access to the network

Note: It is important to notice that the end client being authenticated twice is transparent for the end client
The underlying process the client must go through is basically divided into two: a connection from the client to the ISE server, and, once authenticated, another connection from the client to the network itself. The controller and ISE always communicate with one another through the RADIUS protocol. Below, an in-depth analysis of a Radioactive (RA) trace and an Embedded Packet Capture (EPC).
CWA Flow - Radioactive (RA) Trace
An RA trace is a set of logs captured for a specific client. It shows the whole process the client is going through while connecting to a WLAN. For more information what they are and how to retrieve RA traces, please visit Understand Wireless Debugs and Log Collection on Catalyst 9800 Wireless LAN Controllers.
First Connection: Client to ISE Server
The WLC does not allow a connection to the network if the client has not been authorized by ISE before.
Association to the WLAN
The WLC detects the client wants to associate to the WLAN “cwa”, which us linked to the policy profile “cwa-policy-profile and is connecting to AP “BC-3802”
[client-orch-sm] [17558]: (note): MAC: 4203.9522.e682 Association received. BSSID dc8c.37d0.83af, WLAN cwa, Slot 1 AP dc8c.37d0.83a0, BC-3802
[client-orch-sm] [17558]: (debug): MAC: 4203.9522.e682 Received Dot11 association request. Processing started,SSID: cwa, Policy profile: cwa-policy-profile, AP Name: BC-3802, Ap Mac Address: dc8c.37d0.83a0 BSSID MAC0000.0000.0000 wlan ID: 1RSSI: -46, SNR: 40
[client-orch-state] [17558]: (note): MAC: 4203.9522.e682 Client state transition: S_CO_INIT -> S_CO_ASSOCIATING
[dot11-validate] [17558]: (info): MAC: 4203.9522.e682 WiFi direct: Dot11 validate P2P IE. P2P IE not present.
MAC Filtering
Test ISE Server Connectivity
Once the WLC has received the association request from the client, the first step is to perform MAC filtering (also known as MAB). MAC filtering is a security method in which the MAC address of the client is checked against a database to validate if they are allowed to join the network or not.
[dot11] [17558]: (info): MAC: 4203.9522.e682 DOT11 state transition: S_DOT11_INIT -> S_DOT11_MAB_PENDING <-- The WLC is waiting for ISE to authenticate the user. It does not send an "Association Response" until the client is accepted by ISE.
[client-orch-state] [17558]: (note): MAC: 4203.9522.e682 Client state transition: S_CO_ASSOCIATING -> S_CO_MACAUTH_IN_PROGRESS
[client-auth] [17558]: (note): MAC: 4203.9522.e682 MAB Authentication initiated. Policy VLAN 0, AAA override = 1, NAC = 1 <-- no VLAN is assigned as ISE can do that
[sanet-shim-translate] [17558]: (ERR): 4203.9522.e682 wlan_profile Not Found : Device information attributes not populated
[auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] Session Start event called from SANET-SHIM with conn_hdl 14, vlan: 0
[auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] Wireless session sequence, create context with method MAB
[auth-mgr-feat_wireless] [17558]: (info): [4203.9522.e682:capwap_90000005] - authc_list: cwa_authz <-- Authentication method list used
[auth-mgr-feat_wireless] [17558]: (info): [4203.9522.e682:capwap_90000005] - authz_list: Not present under wlan configuration
[client-auth] [17558]: (info): MAC: 4203.9522.e682 Client auth-interface state transition: S_AUTHIF_INIT -> S_AUTHIF_AWAIT_MAB_AUTH_START_RESP
[auth-mgr] [17558]: (info): [4203.9522.e682:unknown] auth mgr attr change notification is received for attr (952)
[auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] auth mgr attr change notification is received for attr (1263)
[auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] auth mgr attr change notification is received for attr (220)
[auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] auth mgr attr change notification is received for attr (952)
[auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] Retrieved Client IIF ID 0x530002f1
[auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] Allocated audit session id 0E1E140A0000000C8E2DA642
[auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] Applying policy for WlanId: 1, bssid : dc8c.37d0.83af, slotid: 1 bssid hdl : 12364632849490379189
[auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] Wlan vlan-id from bssid hdl 0
[auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] SM Reauth Plugin: Received valid timeout = 1800
[mab] [17558]: (info): [4203.9522.e682:capwap_90000005] MAB authentication started for 4203.9522.e682
[client-auth] [17558]: (info): MAC: 4203.9522.e682 Client auth-interface state transition: S_AUTHIF_AWAIT_MAB_AUTH_START_RESP -> S_AUTHIF_MAB_AUTH_PENDING
[ewlc-infra-evq] [17558]: (note): Authentication Success. Resolved Policy bitmap:11 for client 4203.9522.e682
[client-auth] [17558]: (info): MAC: 4203.9522.e682 Client auth-interface state transition: S_AUTHIF_MAB_AUTH_PENDING -> S_AUTHIF_MAB_AUTH_PENDING
[mab] [17558]: (info): [4203.9522.e682:capwap_90000005] Received event 'MAB_CONTINUE' on handle 0x8A000002 <-- ISE server connectivity has been tested, the WLC is about to send the MAC address to ISE
[caaa-author] [17558]: (info): [CAAA:AUTHOR:92000002] DEBUG: mlist=cwa_authz for type=1
WLC Sends Request to ISE
The WLC sends a RADIUS Access-Request packet to ISE containing the MAC address of the client that wants to authenticate to the WLAN.
[radius] [17558]: (info): RADIUS: Send Access-Request to <ise-ip-addr>:1812 id 0/28, len 415 <-- The packet is traveling via RADIUS port 1812. The "28" is the session ID and it is unique for every connection attempt
[radius] [17558]: (info): RADIUS: authenticator e7 85 1b 08 31 58 ee 91 - 17 46 82 79 7d 3b c4 30
[radius] [17558]: (info): RADIUS: User-Name [1] 14 "42039522e682" <-- MAC address that is attempting to authenticate
[radius] [17558]: (info): RADIUS: User-Password [2] 18 *
[radius] [17558]: (info): RADIUS: Cisco AVpair [1] 25 "service-type=Call Check" <-- This indicates a MAC filtering process
[radius] [17558]: (info): RADIUS: Framed-MTU [12] 6 1485
[radius] [17558]: (info): RADIUS: Message-Authenticator[80] 18 ...
[radius] [17558]: (info): RADIUS: EAP-Key-Name [102] 2 *
[radius] [17558]: (info): RADIUS: Cisco AVpair [1] 43 "audit-session-id=0E1E140A0000000C8E2DA642"
[radius] [17558]: (info): RADIUS: Cisco AVpair [1] 12 "method=mab" <-- Controller sends an AVpair with MAB method
[radius] [17558]: (info): RADIUS: Cisco AVpair [1] 26 "client-iif-id=1392509681"
[radius] [17558]: (info): RADIUS: Cisco AVpair [1] 14 "vlan-id=1000"
[radius] [17558]: (info): RADIUS: NAS-IP-Address [4] 6 <wmi-ip-addr> <-- WLC WMI IP address
[radius] [17558]: (info): RADIUS: NAS-Port-Id [87] 17 "capwap_90000005"
[radius] [17558]: (info): RADIUS: NAS-Port-Type [61] 6 802.11 wireless [19]
[radius] [17558]: (info): RADIUS: Cisco AVpair [1] 30 "cisco-wlan-ssid=cwa" <-- SSID and WLAN the client is attempting to connect
[radius] [17558]: (info): RADIUS: Cisco AVpair [1] 32 "wlan-profile-name=cwa"
[radius] [17558]: (info): RADIUS: Called-Station-Id [30] 32 "dc-8c-37-d0-83-a0:cwa"
[radius] [17558]: (info): RADIUS: Calling-Station-Id [31] 19 "42-03-95-22-e6-82"
[radius] [17558]: (info): RADIUS: Airespace-WLAN-ID [1] 6 1
[radius] [17558]: (info): RADIUS: Nas-Identifier [32] 9 "BC-9800"
[radius] [17558]: (info): RADIUS: Started 5 sec timeout

Note: An AV-Pair is "Attribute-Value" used by ISE. It is a Key-Value structure of pre-defined information that can be sent to the WLC. These values are applied on that specific client for that specific session.
Examples of AV-Pairs:
- ACL name
- Redirect URL
- VLAN assignment
- Session timeout timrs
- Re-authentication timers
ISE Responds to the WLC Request
If the MAC address sent by the WLC is accepted by ISE, then ISE sends an Access-Accept RADIUS packet. Depending on the ISE configuration, if it is an unknown MAC address, ISE must accept it and continue with the flow. If you see an Access-Reject, then there is something not correctly configured on ISE that needs to be verified.
[radius] [17558]: (info): RADIUS: Received from id 1812/28 <ise-ip-addr>:0, Access-Accept, len 334 <-- The packet is traveling via RADIUS port 1812 and is has a session ID of 28 (as a response to the above packet)
[radius] [17558]: (info): RADIUS: authenticator 14 0a 6c f7 01 b2 77 6a - 3d ba f0 ed 92 54 9b d6
[radius] [17558]: (info): RADIUS: User-Name [1] 19 "42-03-95-22-E6-82" <-- MAC address of the client that was authorized by ISE
[radius] [17558]: (info): RADIUS: Class [25] 51 ...
[radius] [17558]: (info): RADIUS: Message-Authenticator[80] 18 ...
[radius] [17558]: (info): RADIUS: Cisco AVpair [1] 31 "url-redirect-acl=cwa-acl" <-- ACL to be applied to the client
[radius] [17558]: (info): RADIUS: Cisco AVpair [1] 183 "url-redirect=https://<ise-ip-addr>:8443/portal/[...]" <-- Redirection URL for the client
[radius] [17558]: (info): Valid Response Packet, Free the identifier
[eap-auth] [17558]: (info): SUCCESS for EAP method name: Identity on handle 0xB0000039
[mab] [17558]: (info): [4203.9522.e682:capwap_90000005] MAB received an Access-Accept for 0x8A000002
[mab] [17558]: (info): [4203.9522.e682:capwap_90000005] Received event 'MAB_RESULT' on handle 0x8A000002
[auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] Authc success from MAB, Auth event success
WLC Processes of Information Received from ISE
The WLC processes all the information received from ISE. With it, it applies the user profile it had originally created with that of the data sent by ISE. The WLC assigns a new ACL to the user, for example. If AAA Override is not enabled on the WLAN, this processing by the WLC does not occur.
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< username 0 "42-03-95-22-E6-82">> <-- Processing username received from ISE
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< class 0 43 41 43 53 3a 30 45 31 45 31 34 30 41 30 30 30 30 30 30 30 43 38 45 32 44 41 36 34 32 3a 62 63 2d 69 73 65 2f 34 33 36 37 33 31 34 32 37 2f 33 38 >>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<<Message-Authenticator 0 <hidden>>>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< url-redirect-acl 0 "cwa-acl">> <-- Processing ACL redirection received from ISE
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< url-redirect 0 "https://<ise-ip-addr>:8443/portal/[...]">> <-- Processing URL redirection received from ISE
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< dnis 0 "DC-8C-37-D0-83-A0">>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< formatted-clid 0 "42-03-95-22-E6-82">>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< audit-session-id 0 "0E1E140A0000000C8E2DA642">>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< method 0 2 [mab]>>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< clid-mac-addr 0 42 03 95 22 e6 82 >>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< intf-id 0 2415919109 (0x90000005)>>
{wncd_x_R0-0}{1}: [auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] auth mgr attr change notification is received for attr (450)
{wncd_x_R0-0}{1}: [auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] Received User-Name 42-03-95-22-E6-82 for client 4203.9522.e682
{wncd_x_R0-0}{1}: [auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] User profile is to be applied. Authz mlist is not present, Authc mlist cwa_authz ,session push flag is unset
{wncd_x_R0-0}{1}: [webauth-dev] [17558]: (info): Central Webauth URL Redirect, Received a request to create a CWA session for a mac [42:03:95:22:e6:82]
{wncd_x_R0-0}{1}: [auth-mgr-feat_wireless] [17558]: (info): [0000.0000.0000:unknown] Retrieved zone id 0x0 for bssid 12364632849490379189
{wncd_x_R0-0}{1}: [webauth-dev] [17558]: (info): No parameter map is associated with mac 4203.9522.e682
{wncd_x_R0-0}{1}: [epm-redirect] [17558]: (info): [0000.0000.0000:unknown] URL-Redirect-ACL = cwa-acl
{wncd_x_R0-0}{1}: [epm-redirect] [17558]: (info): [0000.0000.0000:unknown] URL-Redirect = https://<ise-ip-addr>:8443/portal/[...]
{wncd_x_R0-0}{1}: [auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] User Profile applied successfully for 0x92000002 - REPLACE <-- WLC replaces the user profile it had originally created
MAB Authentication Finishes
After the user profile for the client has been successfully modified, the WLC finishes authenticating the MAC address of the client. If the ACL received from ISE does not exist on the WLC, the WLC does not know what to do with that information, and therefore the REPLACE action fails completely causing the MAB authentication to fail as well. The client is not be able to authenticate.
{wncd_x_R0-0}{1}: [mm-client] [17558]: (debug): MAC: 0000.0000.0000 Sending pmk_update of XID (0) to (MobilityD[0])
{wncd_x_R0-0}{1}: [client-auth] [17558]: (note): MAC: 4203.9522.e682 MAB Authentication success.
{wncd_x_R0-0}{1}: [client-auth] [17558]: (info): MAC: 4203.9522.e682 Client auth-interface state transition: S_AUTHIF_MAB_AUTH_PENDING -> S_AUTHIF_MAB_AUTH_DONE
{wncd_x_R0-0}{1}: [client-orch-sm] [17558]: (debug): MAC: 4203.9522.e682 Processing MAB authentication result status: 0, CO_AUTH_STATUS_SUCCESSWLC Sends Association Response to Client
Now that the client has been authenticated by ISE and the correct ACL has been applied, the WLC finally sends an association response to the client. Now, the user is able to continue connecting to the network.
{wncd_x_R0-0}{1}: [client-orch-state] [17558]: (note): MAC: 4203.9522.e682 Client state transition: S_CO_MACAUTH_IN_PROGRESS -> S_CO_ASSOCIATING
{wncd_x_R0-0}{1}: [dot11] [17558]: (debug): MAC: 4203.9522.e682 dot11 send association response. Sending association response with resp_status_code: 0
{wncd_x_R0-0}{1}: [dot11] [17558]: (debug): MAC: 4203.9522.e682 Dot11 Capability info byte1 1, byte2: 11
{wncd_x_R0-0}{1}: [dot11-frame] [17558]: (info): MAC: 4203.9522.e682 WiFi direct: skip build Assoc Resp with P2P IE: Wifi direct policy disabled
{wncd_x_R0-0}{1}: [dot11] [17558]: (info): MAC: 4203.9522.e682 dot11 send association response. Sending assoc response of length: 137 with resp_status_code: 0, DOT11_STATUS: DOT11_STATUS_SUCCESS
{wncd_x_R0-0}{1}: [dot11] [17558]: (note): MAC: 4203.9522.e682 Association success. AID 1, Roaming = False, WGB = False, 11r = False, 11w = False
{wncd_x_R0-0}{1}: [dot11] [17558]: (info): MAC: 4203.9522.e682 DOT11 state transition: S_DOT11_MAB_PENDING -> S_DOT11_ASSOCIATED
{wncd_x_R0-0}{1}: [client-orch-sm] [17558]: (debug): MAC: 4203.9522.e682 Station Dot11 association is successful. L2 Authentication
As per the process a client must undergo when it associates to an WLAN, L2 authentication "starts". However, in reality, L2 authentication has already been performed due to MAB authentication performed before. The client immediately completes L2 authentication.
{wncd_x_R0-0}{1}: [client-orch-sm] [17558]: (debug): MAC: 4203.9522.e682 Starting L2 authentication. Bssid in state machine:dc8c.37d0.83af Bssid in request is:dc8c.37d0.83af
{wncd_x_R0-0}{1}: [client-orch-state] [17558]: (note): MAC: 4203.9522.e682 Client state transition: S_CO_ASSOCIATING -> S_CO_L2_AUTH_IN_PROGRESS
{wncd_x_R0-0}{1}: [client-auth] [17558]: (note): MAC: 4203.9522.e682 L2 WEBAUTH Authentication Successful
{wncd_x_R0-0}{1}: [client-auth] [17558]: (info): MAC: 4203.9522.e682 Client auth-interface state transition: S_AUTHIF_MAB_AUTH_DONE -> S_AUTHIF_L2_WEBAUTH_DONE
{wncd_x_R0-0}{1}: [client-orch-sm] [17558]: (debug): MAC: 4203.9522.e682 L2 Authentication of station is successful., L3 Authentication : 1Data Plumb
The WLC assigns resources to the connecting client so traffic can flow through the network.
{wncd_x_R0-0}{1}: [client-orch-sm] [17558]: (note): MAC: 4203.9522.e682 Mobility discovery triggered. Client mode: Local
{wncd_x_R0-0}{1}: [client-orch-state] [17558]: (note): MAC: 4203.9522.e682 Client state transition: S_CO_L2_AUTH_IN_PROGRESS -> S_CO_MOBILITY_DISCOVERY_IN_PROGRESS
{wncd_x_R0-0}{1}: [mm-transition] [17558]: (info): MAC: 4203.9522.e682 MMIF FSM transition: S_MA_INIT -> S_MA_MOBILITY_DISCOVERY_PROCESSED_TR on E_MA_MOBILITY_DISCOVERY
{wncd_x_R0-0}{1}: [mm-client] [17558]: (info): MAC: 4203.9522.e682 Invalid transmitter ip in build client context
{wncd_x_R0-0}{1}: [mm-client] [17558]: (debug): MAC: 4203.9522.e682 Sending mobile_announce of XID (0) to (MobilityD[0])
{mobilityd_R0-0}{1}: [mm-client] [18482]: (debug): MAC: 4203.9522.e682 Received mobile_announce, sub type: 0 of XID (0) from (WNCD[0])
{mobilityd_R0-0}{1}: [mm-transition] [18482]: (info): MAC: 4203.9522.e682 MMFSM transition: S_MC_INIT -> S_MC_ANNOUNCE_PROCESSED_NEW_CLIENT_TR on E_MC_ANNOUNCE_RCVD from WNCD[0]
{mobilityd_R0-0}{1}: [mm-client] [18482]: (debug): MAC: 4203.9522.e682 Add MCC by tdl mac: client_ifid 0xa0000001 is assigned to client
{mobilityd_R0-0}{1}: [mm-client] [18482]: (debug): MAC: 4203.9522.e682 Sending capwap_msg_unknown (100) of XID (5) to (WNCD[0])
{mobilityd_R0-0}{1}: [mm-client] [18482]: (debug): MAC: 0000.0000.0000 Sending mobile_announce_nak of XID (5) to (WNCD[0])
{wncd_x_R0-0}{1}: [mm-client] [17558]: (debug): MAC: 4203.9522.e682 Received mobile_announce_nak, sub type: 1 of XID (5) from (MobilityD[0])
{wncd_x_R0-0}{1}: [mm-transition] [17558]: (info): MAC: 4203.9522.e682 MMIF FSM transition: S_MA_INIT_WAIT_ANNOUNCE_RSP -> S_MA_NAK_PROCESSED_TR on E_MA_NAK_RCVD
{wncd_x_R0-0}{1}: [mm-client] [17558]: (info): MAC: 4203.9522.e682 Roam type changed - None -> None
{wncd_x_R0-0}{1}: [mm-client] [17558]: (info): MAC: 4203.9522.e682 Mobility role changed - Unassoc -> Local
{wncd_x_R0-0}{1}: [mm-client] [17558]: (note): MAC: 4203.9522.e682 Mobility Successful. Roam Type None, Sub Roam Type MM_SUB_ROAM_TYPE_NONE, Client IFID: 0xa0000001, Client Role: Local PoA: 0x90000005 PoP: 0x0
{wncd_x_R0-0}{1}: [client-orch-sm] [17558]: (debug): MAC: 4203.9522.e682 Processing mobility response from MMIF. Client ifid: 0xa0000001, roam type: None, client role: Local
{wncd_x_R0-0}{1}: [ewlc-qos-client] [17558]: (info): MAC: 4203.9522.e682 Client QoS add mobile cb
{wncd_x_R0-0}{1}: [ewlc-qos-client] [17558]: (info): MAC: 4203.9522.e682 No QoS PM Name or QoS Level received from SANet for pm_dir:0. Check client is fastlane, otherwise set pm name to none
{wncd_x_R0-0}{1}: [ewlc-qos-client] [17558]: (info): MAC: 4203.9522.e682 No QoS PM Name or QoS Level received from SANet for pm_dir:1. Check client is fastlane, otherwise set pm name to none
{wncd_x_R0-0}{1}: [client-auth] [17558]: (note): MAC: 4203.9522.e682 ADD MOBILE sent. Client state flags: 0x72 BSSID: MAC: dc8c.37d0.83af capwap IFID: 0x90000005
{wncd_x_R0-0}{1}: [client-orch-state] [17558]: (note): MAC: 4203.9522.e682 Client state transition: S_CO_MOBILITY_DISCOVERY_IN_PROGRESS -> S_CO_DPATH_PLUMB_IN_PROGRESS
{wncd_x_R0-0}{1}: [dot11] [17558]: (note): MAC: 4203.9522.e682 Client datapath entry params - ssid:training_cwa,slot_id:1 bssid ifid: 0x0, radio_ifid: 0x90000003, wlan_ifid: 0xf0400001
{wncd_x_R0-0}{1}: [ewlc-qos-client] [17558]: (info): MAC: 4203.9522.e682 Client QoS dpath create params
{wncd_x_R0-0}{1}: [ewlc-qos-client] [17558]: (info): MAC: 4203.9522.e682 No QoS PM Name or QoS Level received from SANet for pm_dir:0. Check client is fastlane, otherwise set pm name to none
{wncd_x_R0-0}{1}: [ewlc-qos-client] [17558]: (info): MAC: 4203.9522.e682 No QoS PM Name or QoS Level received from SANet for pm_dir:1. Check client is fastlane, otherwise set pm name to none
{wncd_x_R0-0}{1}: [avc-afc] [17558]: (debug): AVC enabled for client 4203.9522.e682
{wncd_x_R0-0}{1}: [dpath_svc] [17558]: (note): MAC: 4203.9522.e682 Client datapath entry created for ifid 0xa0000001User is Assigned an IP address
The end user needs an IP address in order to navigate through the network. It undergoes the DHCP process. If the user was connected before and it remembers its IP address, then the DHCP process is skipped. If the user is unable to receive an IP address, the end user is unable to view the web portal. Otherwise, it goes through the next steps:
- A DISCOVER packet is sent from the connecting client as a broadcast to find any DHCP servers available
- If there is a DHCP server available, the DHCP server responds with an OFFER. The offer contains information such as as the IP address to be assigned to the connecting client, lease time, and so on. There can be many OFFERs received from various DHCP servers
- The client accepts an OFFER from one of the servers and responds with a REQUEST for the IP address it selected
- Finally, the DHCP server sends an ACKNOWLEDGMENT packet to the client with its new IP address assigned
The WLC logs the method the client received its IP address.
{wncd_x_R0-0}{1}: [client-orch-state] [17558]: (note): MAC: 4203.9522.e682 Client state transition: S_CO_DPATH_PLUMB_IN_PROGRESS -> S_CO_IP_LEARN_IN_PROGRESS
{wncd_x_R0-0}{1}: [client-iplearn] [17558]: (info): MAC: 4203.9522.e682 IP-learn state transition: S_IPLEARN_INIT -> S_IPLEARN_IN_PROGRESS
{wncd_x_R0-0}{1}: [client-auth] [17558]: (info): MAC: 4203.9522.e682 Client auth-interface state transition: S_AUTHIF_L2_WEBAUTH_DONE -> S_AUTHIF_L2_WEBAUTH_DONE
{wncd_x_R0-0}{1}: [auth-mgr-feat_dsensor] [17558]: (info): [4203.9522.e682:capwap_90000005] Skipping DHCP TLVs for further processing. DHCP based classification isn't enabled
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (info): RX: DHCPv4 from interface capwap_90000005 on vlan 1000 Src MAC: 4203.9522.e682 Dst MAC: ffff.ffff.ffff src_ip: 0.0.0.0, dst_ip: 255.255.255.255, BOOTPREQUEST, SISF_DHCPDISCOVER, giaddr: 0.0.0.0, yiaddr: 0.0.0.0, CMAC: 4203.9522.e682
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (info): TX: DHCPv4 from interface capwap_90000005 on vlan 1000 Src MAC: 4203.9522.e682 Dst MAC: ffff.ffff.ffff src_ip: 0.0.0.0, dst_ip: 255.255.255.255, BOOTPREQUEST, SISF_DHCPDISCOVER, giaddr: 0.0.0.0, yiaddr: 0.0.0.0, CMAC: 4203.9522.e682
{wncd_x_R0-0}{1}: [auth-mgr-feat_dsensor] [17558]: (info): [4203.9522.e682:capwap_90000005] Skipping DHCP TLVs for further processing. DHCP based classification isn't enabled
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (info): RX: DHCPv4 from interface capwap_90000005 on vlan 1000 Src MAC: 4203.9522.e682 Dst MAC: ffff.ffff.ffff src_ip: 0.0.0.0, dst_ip: 255.255.255.255, BOOTPREQUEST, SISF_DHCPDISCOVER, giaddr: 0.0.0.0, yiaddr: 0.0.0.0, CMAC: 4203.9522.e682
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (info): TX: DHCPv4 from interface capwap_90000005 on vlan 1000 Src MAC: 4203.9522.e682 Dst MAC: ffff.ffff.ffff src_ip: 0.0.0.0, dst_ip: 255.255.255.255, BOOTPREQUEST, SISF_DHCPDISCOVER, giaddr: 0.0.0.0, yiaddr: 0.0.0.0, CMAC: 4203.9522.e682
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (info): RX: DHCPv4 from interface Tw0/0/0 on vlan 1000 Src MAC: dca6.32d2.e93f Dst MAC: 4203.9522.e682 src_ip: <dhcp-server-ip-addr>, dst_ip: <end-user-ip-addr>, BOOTPREPLY, SISF_DHCPOFFER, giaddr: 0.0.0.0, yiaddr: <end-user-ip-addr>, CMAC: 4203.9522.e682
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (info): TX: DHCPv4 from interface Tw0/0/0 on vlan 1000 Src MAC: dca6.32d2.e93f Dst MAC: 4203.9522.e682 src_ip: <dhcp-server-ip-addr>, dst_ip: <end-user-ip-addr>, BOOTPREPLY, SISF_DHCPOFFER, giaddr: 0.0.0.0, yiaddr: <end-user-ip-addr>, CMAC: 4203.9522.e682
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (info): RX: DHCPv4 from interface Tw0/0/0 on vlan 1000 Src MAC: dca6.32d2.e93f Dst MAC: 4203.9522.e682 src_ip: <dhcp-server-ip-addr>, dst_ip: <end-user-ip-addr>, BOOTPREPLY, SISF_DHCPOFFER, giaddr: 0.0.0.0, yiaddr: <end-user-ip-addr>, CMAC: 4203.9522.e682
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (info): TX: DHCPv4 from interface Tw0/0/0 on vlan 1000 Src MAC: dca6.32d2.e93f Dst MAC: 4203.9522.e682 src_ip: <dhcp-server-ip-addr>, dst_ip: <end-user-ip-addr>, BOOTPREPLY, SISF_DHCPOFFER, giaddr: 0.0.0.0, yiaddr: <end-user-ip-addr>, CMAC: 4203.9522.e682
{wncd_x_R0-0}{1}: [auth-mgr-feat_dsensor] [17558]: (info): [4203.9522.e682:capwap_90000005] Skipping DHCP TLVs for further processing. DHCP based classification isn't enabled
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (info): RX: DHCPv4 from interface capwap_90000005 on vlan 1000 Src MAC: 4203.9522.e682 Dst MAC: ffff.ffff.ffff src_ip: 0.0.0.0, dst_ip: 255.255.255.255, BOOTPREQUEST, SISF_DHCPREQUEST, giaddr: 0.0.0.0, yiaddr: 0.0.0.0, CMAC: 4203.9522.e682
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (info): TX: DHCPv4 from interface capwap_90000005 on vlan 1000 Src MAC: 4203.9522.e682 Dst MAC: ffff.ffff.ffff src_ip: 0.0.0.0, dst_ip: 255.255.255.255, BOOTPREQUEST, SISF_DHCPREQUEST, giaddr: 0.0.0.0, yiaddr: 0.0.0.0, CMAC: 4203.9522.e682
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (info): RX: DHCPv4 from interface Tw0/0/0 on vlan 1000 Src MAC: dca6.32d2.e93f Dst MAC: 4203.9522.e682 src_ip: <dhcp-server-ip-addr>, dst_ip: <end-user-ip-addr>, BOOTPREPLY, SISF_DHCPACK, giaddr: 0.0.0.0, yiaddr: <end-user-ip-addr>, CMAC: 4203.9522.e682
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (info): TX: DHCPv4 from interface Tw0/0/0 on vlan 1000 Src MAC: dca6.32d2.e93f Dst MAC: 4203.9522.e682 src_ip: <dhcp-server-ip-addr>, dst_ip: <end-user-ip-addr>, BOOTPREPLY, SISF_DHCPACK, giaddr: 0.0.0.0, yiaddr: <end-user-ip-addr>, CMAC: 4203.9522.e682
{wncd_x_R0-0}{1}: [client-iplearn] [17558]: (note): MAC: 4203.9522.e682 Client IP learn successful. Method: DHCP IP: <end-user-ip-addr>
{wncd_x_R0-0}{1}: [epm] [17558]: (info): [0000.0000.0000:unknown] HDL = 0x0 vlan 1000 fail count 0 dirty_counter 0 is_dirty 0
{wncd_x_R0-0}{1}: [auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] auth mgr attr change notification is received for attr (8)
{wncd_x_R0-0}{1}: [client-iplearn] [17558]: (info): MAC: 4203.9522.e682 IP-learn state transition: S_IPLEARN_IN_PROGRESS -> S_IPLEARN_COMPLETE
{wncd_x_R0-0}{1}: [client-orch-sm] [17558]: (debug): MAC: 4203.9522.e682 Received ip learn response. method: IPLEARN_METHOD_DHCPL3 Authentication Starts
Now that the end user has received an IP address, L3 authentication starts with CWA detected as the desired method for authentication.
{wncd_x_R0-0}{1}: [client-orch-sm] [17558]: (debug): MAC: 4203.9522.e682 Triggered L3 authentication. status = 0x0, Success
{wncd_x_R0-0}{1}: [client-orch-state] [17558]: (note): MAC: 4203.9522.e682 Client state transition: S_CO_IP_LEARN_IN_PROGRESS -> S_CO_L3_AUTH_IN_PROGRESS
{wncd_x_R0-0}{1}: [client-auth] [17558]: (note): MAC: 4203.9522.e682 L3 Authentication initiated. CWA Sanity IP addresses Tests
In order to move forward with the connection, the client must perform two ARP requests:
1. Validate that no one else has its IP address. If there is an ARP reply for the IP address of the end user, then it is duplicated IP address
2. Validate reachability to the gateway. This is to ensure that the client can leave the network. The ARP reply must be from the gateway
{wncd_x_R0-0}{1}: [client-auth] [17558]: (info): MAC: 4203.9522.e682 Client auth-interface state transition: S_AUTHIF_L2_WEBAUTH_DONE -> S_AUTHIF_WEBAUTH_PENDING
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: 0.0.0.0, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: 4203.9522.e682 ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: 0.0.0.0, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: 0.0.0.0, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: 4203.9522.e682 ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: 0.0.0.0, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: 0.0.0.0, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: 4203.9522.e682 ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: 0.0.0.0, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: 4203.9522.e682 ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: 4203.9522.e682 ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: 4203.9522.e682 ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: <default-gateway-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: <default-gateway-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface Tw0/0/0 on vlan 1000 Source MAC: 64cc.2284.ae10 Dest MAC: 4203.9522.e682 ARP REPLY, ARP sender MAC: 64cc.2284.ae10 ARP target MAC: 4203.9522.e682 ARP sender IP: <default-gateway-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface Tw0/0/0 on vlan 1000 Source MAC: 64cc.2284.ae10 Dest MAC: 4203.9522.e682 ARP REPLY, ARP sender MAC: 64cc.2284.ae10 ARP target MAC: 4203.9522.e682 ARP sender IP: <default-gateway-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: <dhcp-server-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: <dhcp-server-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface Tw0/0/0 on vlan 1000 Source MAC: dca6.32d2.e93f Dest MAC: 4203.9522.e682 ARP REPLY, ARP sender MAC: dca6.32d2.e93f ARP target MAC: 4203.9522.e682 ARP sender IP: <dhcp-server-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface Tw0/0/0 on vlan 1000 Source MAC: dca6.32d2.e93f Dest MAC: 4203.9522.e682 ARP REPLY, ARP sender MAC: dca6.32d2.e93f ARP target MAC: 4203.9522.e682 ARP sender IP: <dhcp-server-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: <default-gateway-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: <default-gateway-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface Tw0/0/0 on vlan 1000 Source MAC: 64cc.2284.ae10 Dest MAC: 4203.9522.e682 ARP REPLY, ARP sender MAC: 64cc.2284.ae10 ARP target MAC: 4203.9522.e682 ARP sender IP: <default-gateway-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface Tw0/0/0 on vlan 1000 Source MAC: 64cc.2284.ae10 Dest MAC: 4203.9522.e682 ARP REPLY, ARP sender MAC: 64cc.2284.ae10 ARP target MAC: 4203.9522.e682 ARP sender IP: <default-gateway-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: 10.20.30.17,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: ffff.ffff.ffff ARP REQUEST, ARP sender MAC: 4203.9522.e682 ARP target MAC: 0000.0000.0000 ARP sender IP: <end-user-ip-addr>, ARP target IP: 10.20.30.17,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface Tw0/0/0 on vlan 1000 Source MAC: 000c.290e.1c37 Dest MAC: 4203.9522.e682 ARP REPLY, ARP sender MAC: 000c.290e.1c37 ARP target MAC: 4203.9522.e682 ARP sender IP: 10.20.30.17, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface Tw0/0/0 on vlan 1000 Source MAC: 000c.290e.1c37 Dest MAC: 4203.9522.e682 ARP REPLY, ARP sender MAC: 000c.290e.1c37 ARP target MAC: 4203.9522.e682 ARP sender IP: 10.20.30.17, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface Tw0/0/0 on vlan 1000 Source MAC: dca6.32d2.e93f Dest MAC: 4203.9522.e682 ARP REQUEST, ARP sender MAC: dca6.32d2.e93f ARP target MAC: 0000.0000.0000 ARP sender IP: <dhcp-server-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface Tw0/0/0 on vlan 1000 Source MAC: dca6.32d2.e93f Dest MAC: 4203.9522.e682 ARP REQUEST, ARP sender MAC: dca6.32d2.e93f ARP target MAC: 0000.0000.0000 ARP sender IP: <dhcp-server-ip-addr>, ARP target IP: <end-user-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): RX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: dca6.32d2.e93f ARP REPLY, ARP sender MAC: 4203.9522.e682 ARP target MAC: dca6.32d2.e93f ARP sender IP: <end-user-ip-addr>, ARP target IP: <dhcp-server-ip-addr>,
{wncd_x_R0-0}{1}: [sisf-packet] [17558]: (debug): TX: ARP from interface capwap_90000005 on vlan 1000 Source MAC: 4203.9522.e682 Dest MAC: dca6.32d2.e93f ARP REPLY, ARP sender MAC: 4203.9522.e682 ARP target MAC: dca6.32d2.e93f ARP sender IP: <end-user-ip-addr>, ARP target IP: <dhcp-server-ip-addr>, Second Connection: Client to Network
At this point, the end user has now been authenticated against ISE through its MAC address, but it has not been fully authorized yet. The WLC must refer to ISE once more to authorize the client to connect to the network. At this point, the portal is presented to the user in which the username must enter its username and password. On the WLC the end user is seen in the "Web Auth Pending" state.
Change of Authorization (CoA)
Here is where "Support for CoA" in the WLC configuration takes effect. Up until this point, the ACL was used. After the end client sees the portal, the ACL is no longer used, as all it did was redirect the client to the portal. At this point, the client enters its credentials for log in to start the CoA process and reauthenticate the client. The WLC prepares the packet to be sent and forwards it to ISE

Tip: CoA uses port 1700. Make sure it is not blocked by the firewall.
{wncd_x_R0-0}{1}: [caaa-ch] [17558]: (info): [CAAA:COMMAND HANDLER:92000002] Processing CoA request under CH-ctx. <-- ISE requests the client to reauthenticate
{wncd_x_R0-0}{1}: [caaa-ch] [17558]: (info): [CAAA:COMMAND HANDLER:92000002] Reauthenticate request (0x55de3f898b88)
{wncd_x_R0-0}{1}: [mab] [17558]: (info): [4203.9522.e682:capwap_90000005] MAB re-authentication started for 2315255810 (4203.9522.e682) <-- ISE requests the WLC to reauthenciate the CoA
{wncd_x_R0-0}{1}: [aaa-coa] [17558]: (info): radius coa proxy relay coa resp(wncd)
{wncd_x_R0-0}{1}: [aaa-coa] [17558]: (info): CoA Response Details
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info): << ssg-command-code 0 32 >>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info): << formatted-clid 0 "4203.9522.e682">>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info): << error-cause 0 1 [Success]>> <-- The WLC responds with a sucess after processing the packet to be sent to ISE
[aaa-coa] [17558]: (info): server:10.20.30.14 cfg_saddr:10.20.30.14 udpport:64016 sport:0, tableid:0iden:30 rad_code:43 msg_auth_rcvd:TRUE coa_resp:ACK
[caaa-ch] [17558]: (info): [CAAA:COMMAND HANDLER] CoA response sent <-- The WLC sends the CoA response to ISE
Second Authentication to ISE
The second authentication does not start from zero. This is the power of CoA. New rules and/or AV paris can be applied to the user. The ACL and the redirection URL received on the first Access-Accept are not pushed to the end user anymore.
WLC Sends Request to ISE
The WLC sends a new RADIUSAccess-Requestpacket to ISE with the entered username/password combination. This triggers a new MAB authentication, and since ISE already knows the client, a new policy set is to be applied (for example, Access Granted).
{wncd_x_R0-0}{1}: [mab] [17558]: (info): [4203.9522.e682:capwap_90000005] Received event 'MAB_REAUTHENTICATE' on handle 0x8A000002
{wncd_x_R0-0}{1}: [caaa-author] [17558]: (info): [CAAA:AUTHOR:92000002] DEBUG: mlist=cwa_authz for type=1
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Send Access-Request to <ise-ip-addr>:1812 id 0/29, len 421 <-- The packet is traveling via RADIUS port 1812. The "29" is the session ID and it is unique for every connection attempt
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: authenticator c6 ae ab d5 55 c9 65 e2 - 4d 28 01 75 65 54 df 4d
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: User-Name [1] 14 "42039522e682" <-- MAC address that is attempting to authenticate
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: User-Password [2] 18 *
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Cisco AVpair [1] 25 "service-type=Call Check" <-- This indicates a MAC filtering process
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Framed-MTU [12] 6 1485
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Message-Authenticator[80] 18 ...
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: EAP-Key-Name [102] 2 *
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Cisco AVpair [1] 43 "audit-session-id=0E1E140A0000000C8E2DA642"
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Cisco AVpair [1] 12 "method=mab" <-- Controller sends an AVpair with MAB method
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Cisco AVpair [1] 26 "client-iif-id=1392509681"
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Cisco AVpair [1] 14 "vlan-id=200"
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: NAS-IP-Address [4] 6 <wmi-ip-addr> <-- WLC WMI IP address
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: NAS-Port-Id [87] 17 "capwap_90000005"
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: NAS-Port-Type [61] 6 802.11 wireless [19]
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Cisco AVpair [1] 30 "cisco-wlan-ssid=cwa" <-- SSID and WLAN the client is attempting to connect
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Cisco AVpair [1] 32 "wlan-profile-name=cwa"
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Called-Station-Id [30] 32 "dc-8c-37-d0-83-a0:cwa"
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Calling-Station-Id [31] 19 "42-03-95-22-e6-82"
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Airespace-WLAN-ID [1] 6 1
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Nas-Identifier [32] 9 "BC-9800"
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Started 5 sec timeoutISE Responds to the WLC Request
ISE performs a lookup of its policy, and if the username received matches the policy profile, then ISE reponds to the WLC once more, accepting the client connection to the WLAN. It returns the username of the end user. If configured on ISE, additional rules and/or AV pairs can be applied to the user and they are seen on the Access-Accept.
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Received from id 1812/29 <ise-ip-addr>:0, Access-Accept, len 131 <-- The packet is traveling via RADIUS port 1812 and is has a session ID of 29 (as a response to the above packet)
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: authenticator a3 b0 45 d6 e5 1e 38 4a - be 15 fa 6b f4 67 62 8a
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: User-Name [1] 14 "cwa-username" <-- Username entered by the end client on the portal that was shown
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Class [25] 51 ...
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Message-Authenticator[80] 18 ...
{wncd_x_R0-0}{1}: [radius] [17558]: (info): RADIUS: Cisco AVpair [1] 22 "profile-name=Unknown"
{wncd_x_R0-0}{1}: [radius] [17558]: (info): Valid Response Packet, Free the identifier
{wncd_x_R0-0}{1}: [eap-auth] [17558]: (info): SUCCESS for EAP method name: Identity on handle 0xEE00003B
{wncd_x_R0-0}{1}: [mab] [17558]: (info): [4203.9522.e682:capwap_90000005] MAB received an Access-Accept for 0x8A000002
{wncd_x_R0-0}{1}: [mab] [17558]: (info): [4203.9522.e682:capwap_90000005] Received event 'MAB_RESULT' on handle 0x8A000002
{wncd_x_R0-0}{1}: [auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] Authc success from MAB, Auth event successWLC Processes of Information Received from ISE
Once more, the WLC processes the information received by ISE. It performs another REPLACE action on the user with the new values received from ISE.
[aaa-attr-inf] [17558]: (info):
<< username 0 "cwa-username">> <-- Processing username received from ISE
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< class 0 43 41 43 53 3a 30 45 31 45 31 34 30 41 30 30 30 30 30 30 30 43 38 45 32 44 41 36 34 32 3a 62 63 2d 69 73 65 2f 34 33 36 37 33 31 34 32 37 2f 34 30 >>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<<Message-Authenticator 0 <hidden>>>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< dnis 0 "DC-8C-37-D0-83-A0">>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< formatted-clid 0 "42-03-95-22-E6-82">>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< audit-session-id 0 "0E1E140A0000000C8E2DA642">>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< method 0 2 [mab]>>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< clid-mac-addr 0 42 03 95 22 e6 82 >>
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info):
<< intf-id 0 2415919109 (0x90000005)>>
{wncd_x_R0-0}{1}: [auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] auth mgr attr change notification is received for attr (450)
{wncd_x_R0-0}{1}: [auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] auth mgr attr change notification is received for attr (450)
{wncd_x_R0-0}{1}: [auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] Received User-Name cwa-username for client 4203.9522.e682
{wncd_x_R0-0}{1}: [auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] User profile is to be applied. Authz mlist is not present, Authc mlist cwa_authz ,session push flag is unset
{wncd_x_R0-0}{1}: [auth-mgr] [17558]: (info): [4203.9522.e682:capwap_90000005] User Profile applied successfully for 0x92000002 - REPLACE <-- WLC replaces the user profile it had originally created
L3 Authentication Finishes
The end user has now been authenticated with the given data. L3 authentication (web authentication) is finished.
{wncd_x_R0-0}{1}: [client-auth] [17558]: (note): MAC: 4203.9522.e682 L3 Authentication Successful. ACL:[]
{wncd_x_R0-0}{1}: [client-auth] [17558]: (info): MAC: 4203.9522.e682 Client auth-interface state transition: S_AUTHIF_WEBAUTH_PENDING -> S_AUTHIF_WEBAUTH_DONE
{wncd_x_R0-0}{1}: [ewlc-qos-client] [17558]: (info): MAC: 4203.9522.e682 Client QoS add mobile cb
{wncd_x_R0-0}{1}: [ewlc-qos-client] [17558]: (info): MAC: 4203.9522.e682 No QoS PM Name or QoS Level received from SANet for pm_dir:0. Check client is fastlane, otherwise set pm name to none
{wncd_x_R0-0}{1}: [ewlc-qos-client] [17558]: (info): MAC: 4203.9522.e682 No QoS PM Name or QoS Level received from SANet for pm_dir:1. Check client is fastlane, otherwise set pm name to none
{wncd_x_R0-0}{1}: [client-auth] [17558]: (note): MAC: 4203.9522.e682 ADD MOBILE sent. Client state flags: 0x78 BSSID: MAC: dc8c.37d0.83af capwap IFID: 0x90000005
{wncd_x_R0-0}{1}: [errmsg] [17558]: (info): %CLIENT_ORCH_LOG-6-CLIENT_ADDED_TO_RUN_STATE: Username entry (cwa-username) joined with ssid (cwa) for device with MAC: 4203.9522.e682 <-- End user "cwa-username" has joined the WLAN "cwa"
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info): [ Applied attribute : username 0 "cwa-username" ]
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info): [ Applied attribute : class 0 43 41 43 53 3a 30 45 31 45 31 34 30 41 30 30 30 30 30 30 30 43 38 45 32 44 41 36 34 32 3a 62 63 2d 69 73 65 2f 34 33 36 37 33 31 34 32 37 2f 34 30 ]
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info): [ Applied attribute :bsn-vlan-interface-name 0 "MGMT" ]
{wncd_x_R0-0}{1}: [aaa-attr-inf] [17558]: (info): [ Applied attribute : timeout 0 1800 (0x708) ]
{wncd_x_R0-0}{1}: [ewlc-qos-client] [17558]: (info): MAC: 4203.9522.e682 Client QoS run state handlerEnd User Reaches RUN State on the WLC
Finally, the user is authenticated and associated to the WLAN.
{wncd_x_R0-0}{1}: [rog-proxy-capwap] [17558]: (debug): Managed client RUN state notification: 4203.9522.e682
{wncd_x_R0-0}{1}: [client-orch-state] [17558]: (note): MAC: 4203.9522.e682 Client state transition: S_CO_L3_AUTH_IN_PROGRESS -> S_CO_RUN
CWA Flow - Embedded Packet Capture (EPC)
An EPC is a packet capture that can be retrieved directly from the WLC showing all the packets that are either passing through the WLC or are being sourced from it. For more information on what they are and how to retrieve them, please visit Understand Wireless Debugs and Log Collection on Catalyst 9800 Wireless LAN Controllers.
First Connection: Client to ISE Server

Warning: The IP addresses on the images of the packet capture have been deleted. They are shown as and
Association to the WLAN and Request Sent to ISE Server
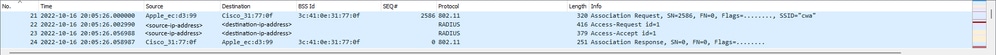 First Packets
First Packets
Association Request From the WLC to the Client
Looking at the first packet "Association Request" you can see the MAC addresses of the devices that are involved in this process.
 Association Request
Association Request
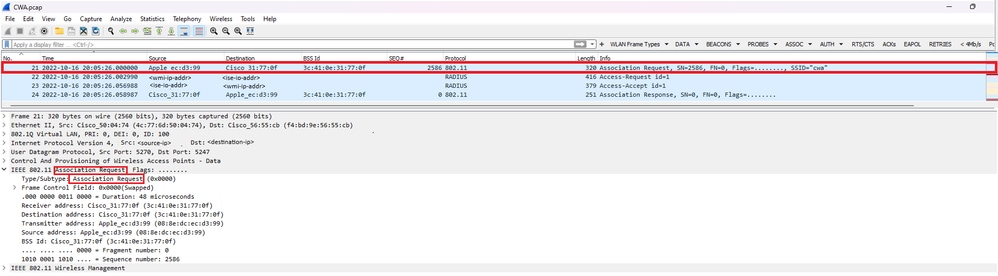
Access-Request Packet Sent From the WLC to ISE
Once the association request has been processed by the WLC, the WLC sends an Access-Request packet to the ISE server.
 Analysis of Access-Request Packet
Analysis of Access-Request Packet
- Name of the packet.
- The MAC address that is attempting to authenticate.
- This indicates a MAC filtering.
- The AV pair sent by the controller to ISE to indicate a MAC filtering process.
- The WMI IP address of the WLC.
- The SSID the client is attempting to connect.
- The name of the WLAN the client is attempting to connect.
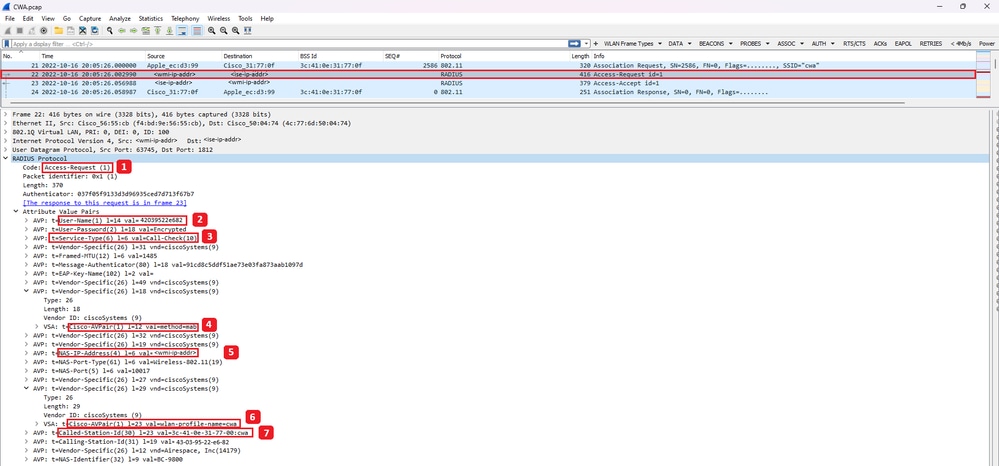
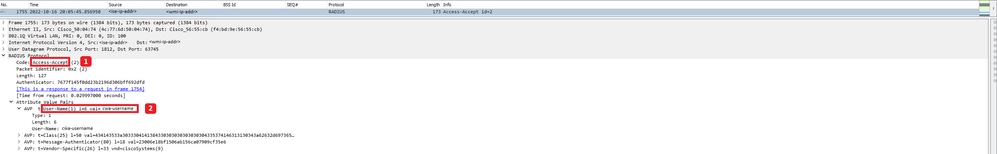
Access-Accept Packet Sent From the WLC to ISE
Once ISE has processed the Access-Accept packet, it responds with an Access-Accept if successful or with an Access-Reject if not.
 Analysis of Access-Accept Packet
Analysis of Access-Accept Packet
- Name of the packet.
- The MAC address authenticated.
- The ACL to be applied.
- The URL to redirect the user to.
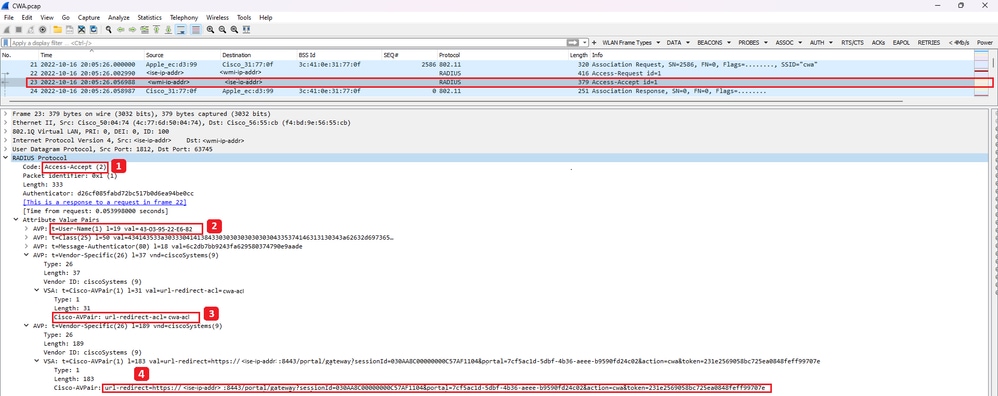
Association Response From the WLC to the Client
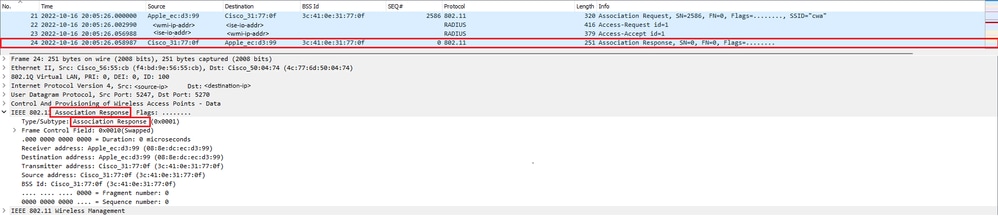 Association Response
Association Response
DHCP Process
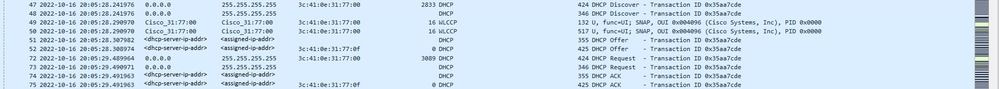 DHCP Process
DHCP Process

Note: From now on, packets are seen duplicated, but that is only because one is CAPWAP encapsulated and the other one is not
ARP
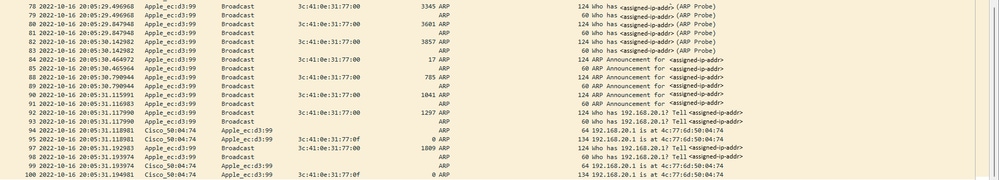 Client ARPing for its own IP Address and for the Gateway
Client ARPing for its own IP Address and for the Gateway
Connectivity Test
Once the ARP process has finished, the device that is attempting to connect does performs a check to validate if a portal is triggered, this is also known as probing. If the device says there is no Internet connection, then it means the ARP process failed (for example, the gateway never answered) or the device was unable to do the probing.
This probing is something that is not seen on the RA traces, only the EPC is able to provide this information. The probing query depends on the device that is attempting a connection, in this example the testing device was an Apple device, so the probing was made directly towards the captive portal of Apple.
As the probing is made using an URL, DNS is required to solve this URL. Therefore, if the DNS server is unable to respond to the queries of the client, then the client continues to query for the URL and the portal is never seen. At this point, if the IP address of the ISE server is entered on the end device web browser, the portal must be visible. If so, then there is an issue with the DNS server.
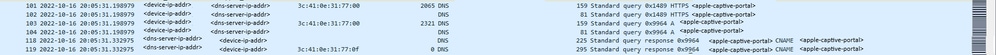 Connectivity Test from Client - DNS Query and Answer
Connectivity Test from Client - DNS Query and Answer
DNS Resolved IP Address
Upon inspecting the DNS query response, you can see the the IP address that was resolved by the DNS server.
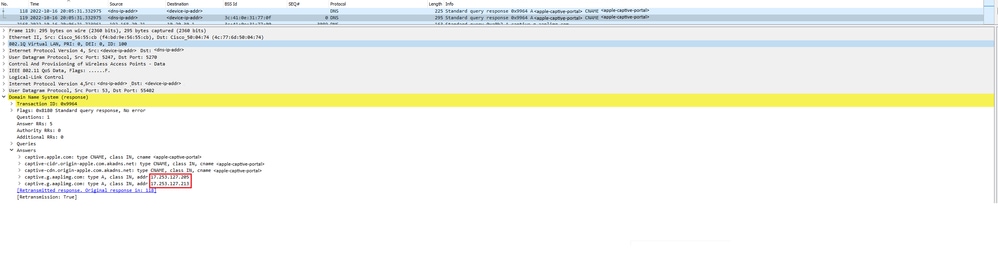 IP Address Resolved by DNS Server
IP Address Resolved by DNS Server
Establish 3-Way Handshake
Now that the DNS IP address has been resolved, a TCP 3-Way handshake is established between the portal and the client. The IP address used is any one of the IP addresses resolved.
 3-Way Handshake Establishment
3-Way Handshake Establishment
GET Hotspot
Once the TCP session has been established, the client does a probing and attempt to access the portal.
 GET Hotspot
GET Hotspot
OK Packet
The OK packet contains the portal of ISE to which the client must be redirected to.
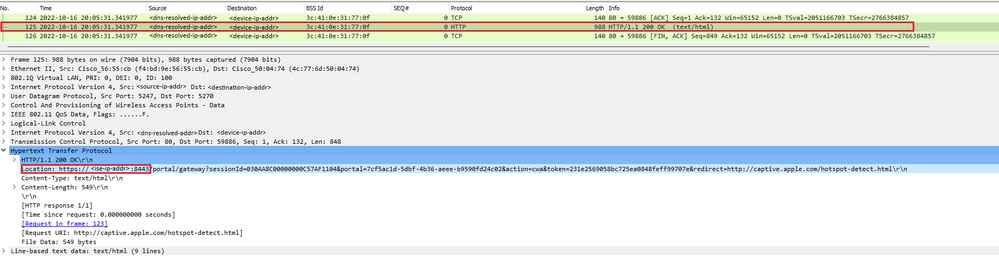 OK Packet
OK Packet

Note: Most people have another URL returned in the OK packet. Therefore, another DNS query needs to be made to obtain the final IP address.
New TCP Session Established
Now that the IP address of the portal has been discovered, many packets are exchanged, but in the end a packet with the destination IP that was returned in the OK packet (or resolved by DNS) which corresponds to the IP address of ISE, shows a new TCP session being established to the portal.
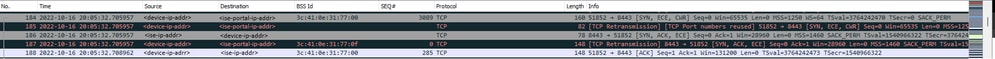 Second Connection and New TCP Session to ISE Portal
Second Connection and New TCP Session to ISE Portal
Portal is Displayed to the User
At this point, the portal of ISE is finally displayed on the browser of the client browser. As before, many packets are exchanged between ISE and the device; things like a client hello and a server hello, and so on. Here is where ISE asks the client for the username and password, accept terms and conditions or whatever it is that was configured over on the ISE server.
CoA Request / CoA Acknowledgement
Once the user has entered all the requested data, ISE sends a CoA request to the controller to change the authorization of the user. If everything on the WLC is configured as expected, such as having the NAC state, support for CoA, and so on, the WLC sends a CoA Acknowledgement (CoA ACK). Otherwise, the WLC can send a CoA Non-Acknowledgement (CoA NACK) or simply it does not even send the CoA ACK.
 CoA Request and Acknowledgement
CoA Request and Acknowledgement
Second Connection: Client to Network
New Access-Request
The WLC sends a new Access-Request packet to ISE.
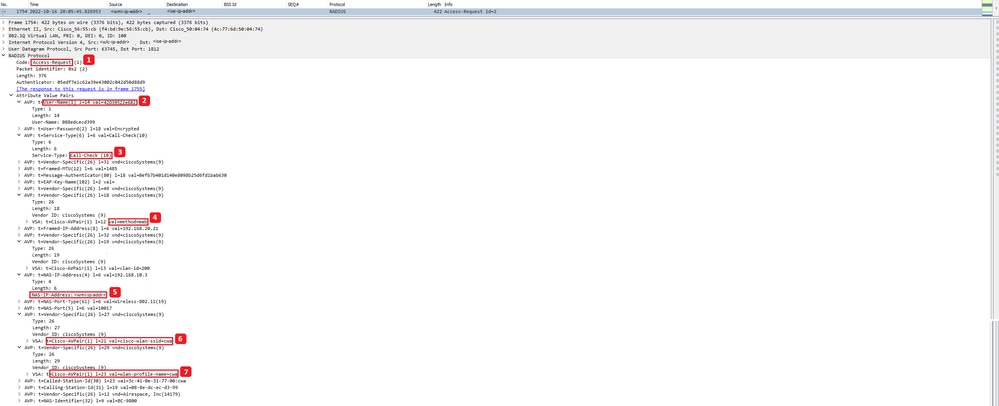 Analysis of New Access-Request Packet
Analysis of New Access-Request Packet
- Name of the packet.
- The MAC address that is attempting to authenticate.
- This indicates a MAC filtering.
- The AV pair sent by the controller to ISE to indicate a MAC filtering process.
- The WMI IP address of the WLC.
- The SSID the client is attempting to connect.
- The name of the WLAN the client is attempting to connect.
New Access-Accept
The WLC sends a new Access-Request packet to ISE.
 Analysis of New Access-Accept Packet
Analysis of New Access-Accept Packet
- Name of the packet.
- The username entered by the end client on the portal that was shown.
Again, a new probing connectivity test is made from the client. Once the client has confirmed it has Internet connectivity, the portal can now be closed (it can be automatically closed, depending on the device used). The client is now connected to the network.
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
06-Oct-2023 |
Initial Release |
Contributed by Cisco Engineers
- Daniela Vignau LeonCisco Technical Consulting Engineer
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback