High Availability Configuration Guide, Cisco IOS Release 12.2SX
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- March 21, 2011
Chapter: Performing an In Service Software Upgrade
- Finding Feature Information
- Prerequisites for Performing an ISSU
- Restrictions for Performing an ISSU
- Information About Performing an ISSU
- ISSU Process Overview
- ISSU Rollback Timer
- Fast Software Upgrade
- Enhanced Fast Software Upgrade
- Versioning Capability in Cisco Software to Support ISSU
- SNMP Support for ISSU
- Virtual Template Manager for ISSU
- Compatibility Verification Using Cisco Feature Navigator
- ISSU-Capable Protocols and Applications
- How to Perform an ISSU
- Displaying ISSU Compatibility Matrix Information
- Loading Cisco IOS Software on the Standby RP
- Switching to the Standby RP
- Stopping the ISSU Rollback Timer
- Verifying the ISSU Software Installation
- Enabling the New Standby RP to Use New Software Version
- Aborting a Software Upgrade Using ISSU
- Configuring the Rollback Timer to Safeguard Against Upgrades
- Configuration Examples for Performing an ISSU
- Additional References
- Feature Information for Performing an ISSU
Performing an In Service Software Upgrade
This module describes how to perform an In Service Software Upgrade (ISSU) process.
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the Feature Information Table at the end of this document.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Prerequisites for Performing an ISSU
- Both the active and standby route processors (RPs) must be available in the system.
- The new and old Cisco software images must be loaded into the file systems of both the active and standby RPs before you begin the ISSU process.
- Stateful switchover (SSO) must be configured and working properly.
- Nonstop forwarding (NSF) must be configured and working properly.
- Before you perform ISSU, the file system for both the active and standby RPs must contain the new ISSU-compatible image. The current version running in the system must also support ISSU. You can issue various commands to determine RP versioning and compatibility, or you can use the ISSU application on Cisco Feature Navigator.
Restrictions for Performing an ISSU
- General Restrictions
- Termination of Virtual Template Manager for ISSU Restrictions
- Cisco 10000 Series Internet Router Platform Restrictions
- Cisco Catalyst 4500 Restrictions
General Restrictions
- Do not make hardware changes while performing an ISSU process.
- Perform upgrades only during a maintenance window. (Recommended)
- Do not enable new features that require configuration changes during the ISSU process.
- If a feature is not available in a downgrade of a Cisco software image, disable that feature before you initiate the ISSU process.
Termination of Virtual Template Manager for ISSU Restrictions
The Virtual Template Manager for ISSU is not supported in Cisco IOS Releases 12.2(31)SB and 12.2(33)SB.
Cisco 10000 Series Internet Router Platform Restrictions
- ISSU is available only in Cisco IOS 12.2(28)SB software released for theand later.
- The following line cards support ISSU:
- 1-port channelized OC-12/STM-4
- 1-port Gigabit Ethernet
- 1-port half-height Gigabit Ethernet
- 1-port OC-12 ATM
- 1-port OC-12 Packet over SONET (PoS)
- l-port OC-48 PoS
- 4-port channelized OC-3/STM-1
- 4-port OC-3 ATM IR
- 4-port OC-3 ATM LR
- 4-port half-height channelized T3
- 6-port channelized T3
- 6-port OC-3 PoS
- 8-port ATM E3/DS3
- 8-port E3/DS3
- 8-port half-height Fast Ethernet
- 24-port channelized E1/T1
- The following interface cards support ISSU:
- SPA Interface Processor (10000-SIP-600)
- 2-port GE SPA
- 5-port GE SPA
- 8-port GE SPA
- 1-port 10GE SPA
Cisco Catalyst 4500 Restrictions
The single-step complete upgrade process cycle is available on the Cisco Catalyst 4500 series switch in Cisco IOS Release 12.2(47)SG.
Information About Performing an ISSU
- ISSU Process Overview
- ISSU Rollback Timer
- Fast Software Upgrade
- Enhanced Fast Software Upgrade
- Versioning Capability in Cisco Software to Support ISSU
- SNMP Support for ISSU
- Virtual Template Manager for ISSU
- Compatibility Verification Using Cisco Feature Navigator
- ISSU-Capable Protocols and Applications
ISSU Process Overview
ISSU allows Cisco software to be upgraded or downgraded, at a router level, while the system continues to forward packets. ISSU takes advantage of the Cisco high availability infrastructure--Cisco NSF with SSO and hardware redundancy--and eliminates downtime associated with software upgrades or version changes by allowing updates while the system remains in service. Cisco high availability features combine to lower the impact that planned maintenance activities have on network service availability, with the results of less downtime and better access to critical systems.
SSO mode supports configuration synchronization. When images on the active and standby RPs are different, this feature allows the two Route Processors (RPs) to remain synchronized although they may support different sets of commands.
An ISSU-capable router consists of two RPs (active and standby) and one or more line cards. Before initiating the ISSU process, you must copy the Cisco IOS software into the file systems of both RPs
After you have copied the Cisco IOS software to both file systems, load the new version of Cisco IOS software onto the standby RP.
After switchover, the standby RP takes over as the new active RP.
Then, the former active RP, which is now the new standby RP, is loaded with the new software.
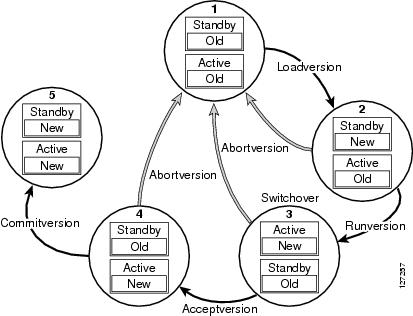
The two RPs in a system can be in one of three different states during ISSU:
- Active--One RP is actively forwarding packets with old software. After the ISSU process is performed, the original active RP becomes the standby RP.
- Standby--Perform ISSU on the standby RP, loading it with new software. After the ISSU process is performed, the original standby RP is the new active RP.
- Hot standby--After the original standby RP becomes the new active RP, load the new software image into the new standby RP. Doing so makes the standby RP a hot standby RP.
The figure below shows the ISSU states during the ISSU process.
ISSU Rollback Timer
Cisco IOS software maintains an ISSU rollback timer. The rollback timer provides a safeguard against an upgrade that may leave the new active RP in a state in which communication with the RP is severed.
Configuring the rollback timer to fewer than 45 minutes (the default) eliminates waiting in case the new software is not committed or the connection to the router is lost while it is in runversion mode. Configure the rollback timer to more than 45 minutes in order to have enough time to verify the operation of the new Cisco IOS software before committing the new image.
Fast Software Upgrade
When Cisco IOS software versions are not compatible and ISSU is not possible, the FSU procedure can be performed within the ISSU command context. Through the use of optional parameters in ISSU commands, the system reverts to RPR mode rather than the SSO mode required for ISSU.
FSU using the ISSU command context works only with ISSU-aware Cisco software versions. If you want to downgrade to a pre-ISSU version, you must use the manual FSU method.
Enhanced Fast Software Upgrade
Enhanced Fast Software Upgrade (eFSU) is an improvement over FSU, reducing the downtime during a Cisco software upgrade.
At the linecard level, an enhanced Fast Software Upgrade (eFSU) process minimizes linecard downtime during upgrades to between 30 and 90 seconds, by pre-loading the new linecard image before the ISSU switchover occurs from the active to the standby Route Processor.
See the Enhanced Fast Software Upgrade on the Cisco 7600 Series Routers for more information.
Versioning Capability in Cisco Software to Support ISSU
Before the introduction of the ISSU capability, the SSO mode of operation required each RP to be running the same versions of Cisco software. The operating mode of the system in a redundant HA configuration is determined by exchanging version strings when the standby RP registers with the active RP.
The system entered SSO mode only if the versions running on both RPs were the same. If not, the redundancy mode was reduced to ensure compatibility. With ISSU capability, the implementation allows two different but compatible release levels of Cisco software images to interoperate in SSO mode and enables software upgrades while packet forwarding continues. Version checking done before ISSU capability was introduced is no longer sufficient to allow the system to determine the operating mode.
ISSU requires additional information to determine compatibility between software versions. Therefore, a compatibility matrix is defined that contains information about other images with respect to the one in question. This compatibility matrix represents the compatibility of two software versions, one running on the active and the other on the standby RP, and to allow the system to determine the highest operating mode it can achieve. Incompatible versions will not be able to progress to SSO operational mode.
The Cisco software infrastructure has been internally modified and redesigned to accommodate subsystem versioning with ISSU. Cisco software subsystems correspond to feature sets and software component groupings. Features or subsystems that maintain state information across RPs are HA-aware or SSO clients. A mechanism called ISSU Framework, or ISSU protocol, allows subsystems within Cisco software to communicate RP to RP and to negotiate the message version for communication between RPs. Internally, all NSF- and SSO-compliant applications or subsystems that are HA-aware must follow this protocol to establish communication with their peer across different versions of software.
Compatibility Matrix
You can perform the ISSU process when the Cisco software on both the active and the standby RP is capable of ISSU and the old and new images are compatible. The compatibility matrix information stores the compatibility among releases as follows:
- Compatible--The base-level system infrastructure and all optional HA-aware subsystems are compatible. An in-service upgrade or downgrade between these versions will succeed with minimal service impact. The matrix entry designates the images to be compatible (C).
- Base-level compatible--One or more of the optional HA-aware subsystems is not compatible. An in-service upgrade or downgrade between these versions will succeed; however, some subsystems will not be able to maintain state during the transition. The matrix entry designates the images to be base-level compatible (B).
- Incompatible--A core set of system infrastructure exists that must be able to interoperate in a stateful manner for SSO to function correctly. If any of these required features or protocols is not interoperable, then the two versions of the Cisco software images are declared to be incompatible. An in-service upgrade or downgrade between these versions is not possible. The matrix entry designates the images to be incompatible (I).
If you attempt to perform ISSU with a peer that does not support ISSU, the system automatically uses Fast Software Upgrade (FSU) instead.
The compatibility matrix represents the compatibility relationship a Cisco software image has with all of the other Cisco software versions within the designated support window (for example, all of those software versions the image “knows” about) and is populated and released with every image. The matrix stores compatibility information between its own release and prior releases. It is always the newest release that contains the latest information about compatibility with existing releases in the field. The compatibility matrix is available within the Cisco software image and on Cisco.com so that users can determine in advance whether an upgrade can be done using the ISSU process.
SNMP Support for ISSU
ISSU - SNMP for SSO provides a mechanism for synchronizing the Simple Network Management Protocol (SNMP) configurations and the MIBs that support SSO from the active RP to the standby RP, assuming that both RPs are running the same version of Cisco software. This assumption is not valid for ISSU.
ISSU - SNMP provides an SNMP client that can handle ISSU transformations for the MIBs. An SNMP client (SIC) handles ISSU for all MIBs and handles the transmit and receive functions required for ISSU. During SNMP, a MIB is completely synchronized from the active RP to the standby RP only if the versions of the MIB on both Cisco software releases are the same.
Virtual Template Manager for ISSU
The virtual template manager feature for ISSU provides virtual access interfaces for sessions that are not HA-capable and are not synchronized to the standby router. The virtual template manager uses a redundancy facility (RF) client to allow the synchronization of virtual access interfaces as they are created.
The virtual databases have instances of distributed FIB entries on line cards. Line cards require synchronization of content and timing in all interfaces to the standby processor to avoid incorrect forwarding. If the virtual access interface is not created on the standby processor, the interface indexes will be corrupted on the standby router and line cards, which will cause problems with forwarding.
Compatibility Verification Using Cisco Feature Navigator
The ISSU application on Cisco Feature Navigator allows you to:
- Select an ISSU-capable image
- Identify which images are compatible with that image
- Compare two images and understand the compatibility level of the images (that is, compatible, base-level compatible, and incompatible)
- Compare two images and see the client compatibility for each ISSU client
- Provide links to release notes for the image
ISSU-Capable Protocols and Applications
The following protocols and applications support ISSU:
- FHRP - HSRP Group Shutdown--FHRP - HSRP group shutdown is supported in ISSU.
- ISSU - ARP--Address Resolution Protocol (ARP) is supported in ISSU.
- ISSU - ATM--Asynchronous Transfer Mode (ATM) is supported in ISSU. The application requirements for ISSU are as follows:
- Identify the ATM client as nonbase
- Support message versioning of ATM HA event synchronous messages
- Provide capability exchange between peers
- ISSU - Dynamic Host Configuration Protocol (DHCP) on-demand address pool (ODAP) client/server--This feature is supported in ISSU.
- ISSU - DHCP proxy client--The DHCP proxy client feature is supported in ISSU.
- ISSU - DHCP relay on unnumbered interface--The DHCP relay on unnumbered interface feature is supported in ISSU.
- ISSU - DHCP server--The DHCP server feature is supported in ISSU.
- ISSU - DHCP snooping--DHCP snooping is supported in ISSU.
- ISSU - EtherChannel - Port Aggregation Protocol (PagP) and Link Aggregate Control Protocol (LACP) support ISSU.
- ISSU - First Hop Routing Protocol (FHRP) - Gateway Load Balancing Protocol (GLBP) is supported in ISSU.
- ISSU - FHRP/HSRP--The Hot Standby Router Protocol (HSRP) is supported in ISSU.
- ISSU - Frame Relay--The Frame Relay protocol is supported in ISSU.
- ISSU - HDLC--The High-Level Data Link Control (HDLC) protocol is supported in ISSU.
- ISSU - IEEE 802.1x--The IEEE 802.1x protocol is supported in ISSU.
- ISSU - IEEE 802.3af--IEEE 802.3af is supported in ISSU.
- ISSU - Internet Group Management Protocol (IGMP) snooping--IGMP snooping is supported in ISSU.
- ISSU - IP host--The IP host is supported in ISSU.
- ISSU - IPv4 Multicast - IPv4 multicast is supported in ISSU.
- ISSU - IS-IS--The Intermediate System-to-Intermediate System (IS-IS) protocol is supported in ISSU.
- ISSU - MTR--Multitopology routing (MTR) is supported in ISSU.
- ISSU - MPLS L3VPN--Multiprotocol Label Switching (MPLS) is supported in ISSU. For information about upgrading ISSU MPLS-related applications through ISSUt.
- ISSU - Port security--Port security is supported in ISSU.
- ISSU - PPP/MLP--multilink PPP (MLP) support ISSU.
- ISSU - PPP over ATM (PPPoA) and PPP over Ethernet (PPPoE) support ISSU.
- ISSU - QoS support--The quality of service (QoS) feature is supported in ISSU.
- ISSU - RIB/VRF - The RIB/VRF feature is supported in ISSU.
- ISSU - SNMP--SNMP is supported in ISSU.
- ISSU - Spanning-Tree Protocol (STP)--STP is supported in ISSU.
How to Perform an ISSU
- Displaying ISSU Compatibility Matrix Information
- Loading Cisco IOS Software on the Standby RP
- Switching to the Standby RP
- Stopping the ISSU Rollback Timer
- Verifying the ISSU Software Installation
- Enabling the New Standby RP to Use New Software Version
- Aborting a Software Upgrade Using ISSU
- Configuring the Rollback Timer to Safeguard Against Upgrades
Displaying ISSU Compatibility Matrix Information
DETAILED STEPS
Loading Cisco IOS Software on the Standby RP
DETAILED STEPS
Switching to the Standby RP
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | enable Example: Router> enable |
Enables privileged EXEC mode.
|
| Step 2 | issu runversion slot image Example: Router# issu runversion b stby-disk0:c10k2-p11-mz.2.20040830 |
Forces a switchover of the active to the standby processor and causes the newly active processor to run the new image. |
Stopping the ISSU Rollback Timer
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | enable Example: Router> enable |
Enables privileged EXEC mode. |
| Step 2 | show issu rollback-timer Example: Router# show issu rollback-timer |
Displays amount of time left before an automatic rollback will occur. |
| Step 3 | issu acceptversion {active slot-number | active slot-name slot-name} Example: Router# issu acceptversion b disk0:c10k2-p11-mz.2.20040830 |
Halts the rollback timer and ensures the new Cisco IOS software image is not automatically aborted during the ISSU process. |
Verifying the ISSU Software Installation
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | enable Example: Router> enable |
Enables privileged EXEC mode. |
| Step 2 | show issu state [detail] Example: Router# show issu state |
Displays the state of the RPs during the ISSU process. |
| Step 3 | show redundancy [clients | counters | debug-log | handover | history | states | inter-device] Example: Router# show redundancy |
Displays current or historical status, mode, and related redundancy information about the device. |
Enabling the New Standby RP to Use New Software Version
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | enable Example: Router> enable |
Enables privileged EXEC mode.
|
| Step 2 | issu commitversion slot active-image Example: Router# issu commitversion a stby-disk0:c10k2-p11-mz.2.20040830 |
Allows the new Cisco IOS software image to be loaded into the standby RP. |
Aborting a Software Upgrade Using ISSU
If you abort the process after you load a new version on the standby RP and before switching to the standby RP, the standby RP is reset and reloaded with the original software.
If you abort the process after switching to the standby RP or stopping an automatic rollback, a second switchover is performed to the new standby RP that is still running the original software version. The RP that had been running the new software is reset and reloaded with the original software version.
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | enable Example: Router> enable |
Enables privileged EXEC mode.
|
| Step 2 | issu abortversion slot image Example: Router# issu abortversion b disk0:c10k2-p11-mz.2.20040830 |
Aborts the ISSU upgrade or downgrade process in progress and restores the router to its state before the process had started. |
Configuring the Rollback Timer to Safeguard Against Upgrades
The Route Processors (RPs) must be in the init state.
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | enable Example: Router> enable |
Enables privileged EXEC mode.
|
| Step 2 | configure terminal Example: Router# configure terminal |
Enters global configuration mode. |
| Step 3 | configure issu set rollback timer seconds Example: Router(config)# configure issu set rollback timer 3600 |
Configures the rollback timer value. |
| Step 4 | exit Example: Router(config)# exit |
Returns the user to privileged EXEC mode. |
| Step 5 | show issu rollback timer Example: Router# show issu rollback timer |
Displays the current setting of the ISSU rollback timer. |
Configuration Examples for Performing an ISSU
- Example Verifying Redundancy Mode Before Beginning the ISSU Process
- Example Verifying the ISSU State
- Example Performing the ISSU Process
- Example Aborting the ISSU Process
- Example Verifying Rollback Timer Information
Example Verifying Redundancy Mode Before Beginning the ISSU Process
Before you begin the ISSU process, verify the redundancy mode for the system. NSF and SSO must be configured before attempting an ISSU. The following example displays verification that the system is in SSO mode and that slot A--RP A is the active R, and slot B--RP B is the standby RP. Both RPs are running the same Cisco software image.
Router# show redundancy states my state = 13 -ACTIVE peer state = 8 -STANDBY HOT Mode = Duplex Unit = Primary Unit ID = 0 Redundancy Mode (Operational) = SSO Redundancy Mode (Configured) = SSO Split Mode = Disabled Manual Swact = Enabled Communications = Up client count = 31 client_notification_TMR = 30000 milliseconds RF debug mask = 0x0 Router# show redundancy Redundant System Information : ------------------------------ Available system uptime = 9 minutes Switchovers system experienced = 0 Standby failures = 0 Last switchover reason = none Hardware Mode = Duplex Configured Redundancy Mode = SSO Operating Redundancy Mode = SSO Maintenance Mode = Disabled Communications = Up Current Processor Information : ------------------------------- Active Location = slot A Current Software state = ACTIVE Uptime in current state = 9 minutes Image Version = Cisco IOS Software, 10000 Software (C10K2-P11-M), Experimental Version 12.2(20040825:224856) [wgrupp-c10k_bba_122s_work 102] Copyright (c) 1986-2004 by Cisco Systems, Inc. Compiled Mon 30-Aug-04 10:29 by wgrupp BOOT = disk0:c10k2-p11-mz.1.20040830,1; CONFIG_FILE = BOOTLDR = Configuration register = 0x102 Peer Processor Information : ---------------------------- Standby Location = slot B Current Software state = STANDBY HOT Uptime in current state = 8 minutes Image Version = Cisco IOS Software, 10000 Software (C10K2-P11-M), Experimental Version 12.2(20040825:224856) [wgrupp-c10k_bba_122s_work 102] Copyright (c) 1986-2004 by Cisco Systems, Inc. Compiled Mon 30-Aug-04 10:29 by wgrupp BOOT = disk0:c10k2-p11-mz.1.20040830,1; CONFIG_FILE = BOOTLDR = Configuration register = 0x102
Example Verifying the ISSU State
The following sample output displays and verifies the ISSU state:
Router# show issu state detail
Slot = A
RP State = Active
ISSU State = Init
Boot Variable = N/A
Operating Mode = SSO
Primary Version = N/A
Secondary Version = N/A
Current Version = disk0:c10k2-p11-mz.1.20040830
Slot = B
RP State = Standby
ISSU State = Init
Boot Variable = N/A
Operating Mode = SSO
Primary Version = N/A
Secondary Version = N/A
Current Version = disk0:c10k2-p11-mz.1.20040830
The new version of the Cisco IOS software must be present on both of the RPs. The directory information displayed for each of the RPs shows that the new version is present.
Router# directory disk0: Directory of disk0:/ 1 -rw- 16864340 Jul 16 2004 01:59:42 -04:00 c10k2-p11-mz.122-16.BX1.bin 2 -rw- 2530912 Jul 16 2004 02:00:04 -04:00 c10k2-eboot-mz.122-16.BX1.bin 3 -rw- 20172208 Aug 30 2004 16:25:56 -04:00 c10k2-p11-mz.1.20040830 4 -rw- 20171492 Aug 31 2004 12:25:34 -04:00 c10k2-p11-mz.2.20040830 64253952 bytes total (4509696 bytes free) Router# directory stby-disk0: Directory of stby-disk0:/
Example Performing the ISSU Process
The following examples show how to verify the ISSU software installation by entering show commands that provide information on the state of theduring the ISSU process.
Initiating the ISSU Process
To initiate the ISSU process, enter the issu loadversion command as shown in the following example:
Router# issu loadversion a disk0:c10k2-p11-mz.2.20040830 b stby-disk0:c10k2-p11-mz.2.20040830
The following two examples display the ISSU state and redundancy state after ISSU process initiation:
Router# show issu state Slot = A RP State = Active ISSU State = Load Version Boot Variable = disk0:c10k2-p11-mz.1.20040830,1; Slot = B RP State = Standby ISSU State = Load Version Boot Variable = disk0:c10k2-p11-mz.2.20040830,12;disk0:c10k2-p11-mz.1.20040830,1; Router# show redundancy state my state = 13 -ACTIVE peer state = 8 -STANDBY HOT Mode = Duplex Unit = Primary Unit ID = 0 Redundancy Mode (Operational) = SSO Redundancy Mode (Configured) = SSO Split Mode = Disabled Manual Swact = Enabled Communications = Up client count = 31 client_notification_TMR = 30000 milliseconds RF debug mask = 0x0
Forcing a Switchover from the Active RP to the Standby RP
At this point, the system is ready to switch over and run the new version of Cisco software that has been loaded onto the standby RP. When you enter the issu runversion command, an SSO switchover will be performed, and NSF procedures will be invoked if so configured.
Router# issu runversion b stby-disk0:c10k2-p11-mz.2.20040830
Once the ISSU process has been completed, the system will be running the new version of software and the previously active RP will now become the standby RP. The standby will be reset and reloaded, but it will remain on the previous version of software and come back online in STANDBY-HOT status. The following example shows how to connect to the newly active RP and verify these conditions.
Router# show redundancy Redundant System Information : ------------------------------ Available system uptime = 24 minutes Switchovers system experienced = 1 Standby failures = 0 Last switchover reason = user initiated Hardware Mode = Duplex Configured Redundancy Mode = SSO Operating Redundancy Mode = SSO Maintenance Mode = Disabled Communications = Up Current Processor Information : ------------------------------- Active Location = slot B Current Software state = ACTIVE Uptime in current state = 8 minutes Image Version = Cisco IOS Software, 10000 Software (C10K2-P11-M), Experimental Version 12.2(20040825:224856) [wgrupp-c10k_bba_122s_work 103] Copyright (c) 1986-2004 by Cisco Systems, Inc. Compiled Mon 30-Aug-04 11:50 by wgrupp BOOT = disk0:c10k2-p11-mz.2.20040830,12;disk0:c10k2-p11-mz.1.20040830,1; CONFIG_FILE = BOOTLDR = Configuration register = 0x102 Peer Processor Information : ---------------------------- Standby Location = slot A Current Software state = STANDBY HOT Uptime in current state = 6 minutes Image Version = Cisco IOS Software, 10000 Software (C10K2-P11-M), Experimental Version 12.2(20040825:224856) [wgrupp-c10k_bba_122s_work 102] Copyright (c) 1986-2004 by Cisco Systems, Inc. Compiled Mon 30-Aug-04 10:29 by wgrupp BOOT = disk0:c10k2-p11-mz.1.20040830,1; CONFIG_FILE = BOOTLDR = Configuration register = 0x102 Router# show issu state Slot = B RP State = Active ISSU State = Run Version Boot Variable = disk0:c10k2-p11-mz.2.20040830,12;disk0:c10k2-p11-mz.1.20040830,1; Slot = A RP State = Standby ISSU State = Run Version Boot Variable = disk0:c10k2-p11-mz.1.20040830,1; Router# show issu state detail Slot = B RP State = Active ISSU State = Run Version Boot Variable = disk0:c10k2-p11-mz.2.20040830,12;disk0:c10k2-p11-mz.1.20040830,1; Operating Mode = SSO Primary Version = disk0:c10k2-p11-mz.2.20040830 Secondary Version = disk0:c10k2-p11-mz.1.20040830 Current Version = disk0:c10k2-p11-mz.2.20040830 Slot = A RP State = Standby ISSU State = Run Version Boot Variable = disk0:c10k2-p11-mz.1.20040830,1; Operating Mode = SSO Primary Version = disk0:c10k2-p11-mz.2.20040830 Secondary Version = disk0:c10k2-p11-mz.1.20040830 Current Version = disk0:c10k2-p11-mz.1.20040830
The new active RP is now running the new version of software, and the standby RP is running the old version of software and is in the STANDBY-HOT state.
Stopping the Rollback Process
In the following example, the “Automatic Rollback Time” information indicates the amount of time left before an automatic rollback will occur. Enter the issu acceptversion command within the time period specified by the rollback timer to acknowledge that the RP has achieved connectivity to the outside world; otherwise, the ISSU process is terminated, and the system reverts to the previous version of Cisco software by switching to the standby RP.
Router# show issu rollback-timer
Rollback Process State = In progress
Configured Rollback Time = 45:00
Automatic Rollback Time = 29:03
Entering the issu acceptversion command stops the rollback timer:
Router# issu acceptversion b disk0:c10k2-p11-mz.2.20040830
Committing the New Software to the Standby RP
The following example shows how to commit the new Cisco software image in the file system of the standby RP and ensure that both the active and the standby RPs are in the run version (RV) state. The standby RP is reset and reloaded with the new Cisco software and returned to STANDBY-HOT status.
Router# issu commitversion a stby-disk0:c10k2-p11-mz.2.20040830 Router# show redundancy states my state = 13 -ACTIVE peer state = 8 -STANDBY HOT Mode = Duplex Unit = Secondary Unit ID = 1 Redundancy Mode (Operational) = SSO Redundancy Mode (Configured) = SSO Split Mode = Disabled Manual Swact = Enabled Communications = Up client count = 31 client_notification_TMR = 30000 milliseconds RF debug mask = 0x0 Router# show redundancy Redundant System Information : ------------------------------ Available system uptime = 35 minutes Switchovers system experienced = 1 Standby failures = 1 Last switchover reason = user initiated Hardware Mode = Duplex Configured Redundancy Mode = SSO Operating Redundancy Mode = SSO Maintenance Mode = Disabled Communications = Up Current Processor Information : ------------------------------- Active Location = slot B Current Software state = ACTIVE Uptime in current state = 18 minutes Image Version = Cisco IOS Software, 10000 Software (C10K2-P11-M), Experimental Version 12.2(20040825:224856) [wgrupp-c10k_bba_122s_work 103] Copyright (c) 1986-2004 by Cisco Systems, Inc. Compiled Mon 30-Aug-04 11:50 by wgrupp BOOT = disk0:c10k2-p11-mz.2.20040830,12;disk0:c10k2-p11-mz.1.20040830,1; CONFIG_FILE = BOOTLDR = Configuration register = 0x102 Peer Processor Information : ---------------------------- Standby Location = slot A Current Software state = STANDBY HOT Uptime in current state = 4 minutes Image Version = Cisco IOS Software, 10000 Software (C10K2-P11-M), Experimental Version 12.2(20040825:224856) [wgrupp-c10k_bba_122s_work 103] Copyright (c) 1986-2004 by Cisco Systems, Inc. Compiled Mon 30-Aug-04 11:50 by wgrupp BOOT = disk0:c10k2-p11-mz.2.20040830,12;disk0:c10k2-p11-mz.1.20040830,1; CONFIG_FILE = BOOTLDR = Configuration register = 0x102 Router# show issu state Slot = B RP State = Active ISSU State = Init Boot Variable = disk0:c10k2-p11-mz.2.20040830,12;disk0:c10k2-p11-mz.1.20040830,1; Slot = A RP State = Standby ISSU State = Init Boot Variable = disk0:c10k2-p11-mz.2.20040830,12;disk0:c10k2-p11-mz.1.20040830,1; Router# show issu state detail Slot = B RP State = Active ISSU State = Init Boot Variable = disk0:c10k2-p11-mz.2.20040830,12;disk0:c10k2-p11-mz.1.20040830,1; Operating Mode = SSO Primary Version = N/A Secondary Version = N/A Current Version = disk0:c10k2-p11-mz.2.20040830 Slot = A RP State = Standby ISSU State = Init Boot Variable = disk0:c10k2-p11-mz.2.20040830,12;disk0:c10k2-p11-mz.1.20040830,1; Operating Mode = SSO Primary Version = N/A Secondary Version = N/A Current Version = disk0:c10k2-p11-mz.2.20040830
The ISSU process has been completed. At this stage, any further Cisco software version upgrades or downgrades will require that a new ISSU process be invoked.
Example Aborting the ISSU Process
The following example shows how to abort the ISSU process manually:
Router# issu abortversion b disk0:c10k2-p11-mz.2.20040830
If you abort the process after you have entered the issu loadversion command, the standby RP is reset and is reloaded with the original software version.
Example Verifying Rollback Timer Information
To display rollback timer information, enter the show issu rollback-timercommand:
Router# show issu rollback-timer
Rollback Process State = In progress
Configured Rollback Time = 45:00
Automatic Rollback Time = 29:03
Additional References
Related Documents
| Related Topic |
Document Title |
|---|---|
| Cisco IOS master command list |
Cisco IOS Master Command List , All Releases |
| Cisco IOS High Availability commands |
Cisco IOS High Availability Command Reference |
| DHCP ODAP client/server |
ISSU - DHCP ODAP Client and Server module in the Cisco IOS IP Addressing Services Configuration Guide |
| DHCP proxy client |
ISSU - DHCP Proxy Client module in the Cisco IOS IP Addressing Services Configuration Guide |
| DHCP relay on unnumbered interface |
ISSU - DHCP Relay on Unnumbered Interface module in the Cisco IOS IP Addressing Services Configuration Guide |
| DHCP server |
ISSU - DHCP Server module in the Cisco IOS IP Addressing Services Configuration Guide |
| Enhanced Fast Software Upgrade (eFSU) |
Enhanced Fast Software Upgrade on the Cisco 7600 Series Router |
| FHRP and HSRP group shutdown |
FHRP - HSRP Group Shutdown module in the Cisco IOS IP Application Services Configuration Guide |
| ISSU - 802.3ah OAM |
Using Ethernet Operations, Administration, and Maintenance module in the Cisco IOS Carrier Ethernet Configuration Guide |
| ISSU - AToM ATM Attachment Circuit |
Any Transport over MPLS and AToM Graceful Restart module in the Cisco IOS Multiprotocol Label Switching Configuration Guide |
| ISSU and eFSU on Cisco 7600 series routers |
ISSU and eFSU on Cisco 7600 Series Routers module in the Cisco 7600 Series Cisco IOS Software Configuration Guide |
| ISSU- E-LMI Support |
Configuring Ethernet Local Management Interface at a Provider Edge module in the Cisco IOS Carrier Ethernet Configuration Guide |
| ISSU - IPv4 multicast |
Monitoring and Maintaining Multicast HA Operations (NSF/SSO and ISSU) module in the Cisco IOS IP Multicast Configuration Guide |
| ISSU - PPoE |
Cisco IOS Broadband High Availability In Service Software Upgrade module in the Cisco IOS Broadband Access Aggregation and DSL Configuration Guide |
| ISSU - VRRP |
Configuring VRRP module in the Cisco IOS IP Application Services Configuration Guide |
| MPLS clients |
ISSU MPLS Clients module in the Cisco IOS Multiprotocol Label Switching Configuration Guide |
| MTR |
Cisco IOS Multi-Topology Routing Configuration Guide |
| Virtual Private LAN Services |
NSF/SSO/ISSU Support for VPLS module in the Cisco IOS Multiprotocol Label Switching Configuration Guide |
Standards
| Standard |
Title |
|---|---|
| No new or modified standards are supported, and support for existing standards has not been modified. |
-- |
MIBs
| MIB |
MIBs Link |
|---|---|
| No new or modified MIBs are supported, and support for existing MIBs has not been modified. |
To locate and download MIBs for selected platforms, Cisco IOS releases, and feature sets, use Cisco MIB Locator found at the following URL: |
RFCs
| RFC |
Title |
|---|---|
| No new or modified RFCs are supported, and support for existing RFCs has not been modified. |
-- |
Technical Assistance
| Description |
Link |
|---|---|
| The Cisco Support and Documentation website provides online resources to download documentation, software, and tools. Use these resources to install and configure the software and to troubleshoot and resolve technical issues with Cisco products and technologies. Access to most tools on the Cisco Support and Documentation website requires a Cisco.com user ID and password. |
Feature Information for Performing an ISSU
The following table provides release information about the feature or features described in this module. This table lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
| Feature Name |
Releases |
Feature Information |
|---|---|---|
| ISSU |
12.2(28)SB 12.2(31)SB2 12.2(31)SGA 12.2(33)SB 12.2(33)SRB1 12.2(33)SRC 12.2(33)SRE 12.3(11)T Cisco IOS XE 3.1.0SG |
In Service Software Upgrade (ISSU) allows Cisco IOS software to be updated or otherwise modified while packet forwarding continues, increasing network availability and reducing downtime caused by planned software upgrades. In 12.2(31)SGA, ISSU was introduced on the Cisco 7200 router. In 12.2(31)SGA, support for ISSU was introduced on the Cisco Catalyst 4500 series switch. In 12.2(33)SB, support for the following interface cards was added. |
| ARP |
12.2(33)SRB1 12.2(33)SXI |
This feature is supported. |
| ATM |
12.2(33)SRB1 12.2(33)SRE 15.0(1)S |
This feature is supported. |
| Circuit Emulation Services (CES) for TDM pseudowires |
12.2(33)SRC |
This feature is supported. |
| DHCP ODAP client/server |
12.2(31)SB2 12.2(33)SRC 15.0(1)S |
This feature is supported. |
| DHCP proxy client |
12.2(31)SB2 12.2(33)SRC 15.0(1)S |
This feature is supported. |
| DHCP relay on unnumbered interface |
12.2(31)SB2 12.2(33)SRC 15.0(1)S |
This feature is supported. |
| DHCP server |
12.2(31)SB2 12.2(33)SRC 15.0(1)S |
This feature is supported. |
| DHCP snooping |
12.2(31)SGA |
This feature was introduced on the Cisco 7200 router and support for ISSU was introduced on the Cisco Catalyst 4500 series switch. |
| EtherChannel - PagP and LACP |
12.2(31)SGA |
This feature was introduced on the Cisco 7200 router and support for ISSU was introduced on the Cisco Catalyst 4500 series switch. |
| FHRP - HSRP group shutdown |
12.2(33)SRC |
This feature is supported. |
| Frame Relay |
12.2(33)SRB1 15.0(1)S |
This feature is supported. |
| GLBP |
12.2(31)SB2 12.2(33)SRB1 |
This feature is supported. |
| HDLC |
12.2(33)SRB1 |
This feature is supported. |
| HSRP |
12.2(30)S 12.2(31)SGA 12.2(33)SRB1 |
This feature is supported. In 12.2(31)SGA, this feature was introduced on the Cisco 7200 router. Support for ISSU was introduced on the Cisco Catalyst 4500 series switch. |
| IEEE 802.1x protocol |
12.2(33)SRB1 12.2(31)SGA |
This feature is supported. In 12.2(31)SGA, this feature was introduced on the Cisco 7200 router. Support for ISSU was introduced on the Cisco Catalyst 4500 series switch. |
| IEEE 802.3af |
12.2(31)SGA |
This feature was introduced on the Cisco 7200 router and support for ISSU was introduced on the Cisco Catalyst 4500 series switch. |
| IGMP snooping |
12.2(31)SGA |
This feature was introduced on the Cisco 7200 router and support for ISSU was introduced on the Cisco Catalyst 4500 series switch. |
| IP host |
12.2(31)SGA |
This feature is supported. |
| IPv4 Multicast |
12.2(33)SRE 15.0(1)S |
This feature is supported. |
| IS-IS |
12.2(31)SB2 12.2(31)SGA 12.2(33)SRB1 15.0(1)S Cisco IOS XE 3.1.0SG |
This feature is supported. In 12.2(31)SGA,this feature was introduced on the Cisco 7200 router. Support for ISSU was introduced on the Cisco Catalyst 4500 series switch. |
| MPLS Clients |
12.2(28)SB 12.2(33)SRB1 |
MPLS applications can be upgrading using the In Service Software Upgrade (ISSU) process and the enhanced Fast Software Upgrade (eFSU) process. Thus, MPLS applications are considered ISSU's MPLS clients. The ISSU process allows Cisco IOS software at the router level to be updated or otherwise modified while packet forwarding continues. At the line-card level, the eFSU process minimizes line-card downtime during such upgrades to between 30 and 90 seconds, by loading the new line-card image before the ISSU switchover occurs from the active to the standby Route Processor (RP). In 12.2(28)SB, the ISSU feature was introduced. In 12.2(33)SRB-1, the LSPV Push and TE clients and the eFSU functionality were added. |
| MPLS VPN 6VPE and 6PE ISSU support |
12.2(33)SRE 12.2(33)XNE |
This feature is supported. |
| MTR |
12.2(33)SRB1 |
This feature is supported. |
| NSF/SSO/ISSU - Virtual Private LAN Services |
12.2(33)SXI4 15.0(1)S |
This feature is supported. |
| Port security |
12.2(31)SGA |
This feature was introduced on the Cisco 7200 router and support for ISSU was introduced on the Cisco Catalyst 4500 series switch. |
| PPP/MLP |
12.2(33)SRB1 |
This feature is supported. |
| PPPoA |
12.2(31)SB2 |
This feature is supported. |
| PPPoE |
12.2(31)SB2 15.0(1)S |
This feature is supported. |
| QoS |
12.2(31)SB2 12.2(33)SRB1 |
This feature is supported. |
| RIB/VRF |
12.2(33)SRB1 12.2(33)SRE |
This feature is supported. |
| SNMP |
12.2(33)SB 12.2(33)SRB1 |
This feature is supported. |
| STP |
12.2(31)SGA 12.2(33)SRB1 |
This feature was introduced on the Cisco 7200 router and support for ISSU was introduced on the Cisco Catalyst 4500 series switch. |
| Virtual template manager |
12.2(33)SRC |
This feature is supported. |
| VRRP |
15.0(1)S |
This feature is supported. |
Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1005R)
Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental.
 Feedback
Feedback