Cisco DNS-AS Troubleshooting
Available Languages
Cisco DNS-AS Troubleshooting
First Published: May 11, 2016
Last Updated: May 17, 2016
Contents
Diagnostic Tool: Verify Customization Interval
Diagnostic Tool: Verify that Traffic Interface and DNS-AS Server on Same VRF
Diagnostic Tool: Verify that DNS-AS Server Is Specified on DNS-AS Client Device
Diagnostic Tool: Check Connectivity between DNS-AS Client Device and DNS-AS Server
Diagnostic Tool: DNS Session Simulation
Diagnostic Tool: View DNS Session Using Wireshark
Diagnostic Tool: Check the DNS-AS Client Statistics
Diagnostic Tool: Check for Pending Queries
Diagnostic Tool: Check Trusted Domains Configured on Router
Diagnostic Tool: Display Information Learned from the DNS-AS Server
DNS-AS client auto-custom binding table is empty
DNS-AS custom protocols do not appear in the router’s binding table
Comprehensive Troubleshooting Workflow
Step 2: Verify that the client specifies the DNS-AS server correctly.
Step 3: Verify that DNS-AS server replies to queries
Step 4: Verify that DNS-AS client queries reach DNS-AS server
Step 5: Check for pending queries on the DNS-AS client
Step 6: Verify that router has received information from the DNS-AS server
Step 7: Verify the trusted domains
Step 8: Check the binding table
Step 9: Verify custom protocols
Step 10: On the DNS-AS server, verify the TXT records
Introduction
This guide addresses client-side troubleshooting for Cisco DNS-AS.
About DNS-AS
Working together with Cisco NBAR2, "DNS as Authoritative Source," DNS-AS, provides centralized control of custom application classification information. Classification information (metadata such as application name, ID, traffic class, business relevance, and so on) is used by NBAR2 to recognize the network traffic of specific applications, and to classify the traffic by assigning parameters useful both in reporting and in applying network traffic policy.
DNS-AS feature includes configuration and functionality on:
■ One or more routers (clients) in a network
■ One more DNS-AS servers that communicate with the clients
Verifying Configuration Changes
After making changes to the DNS-AS configuration on client or server, verify the changes using the show commands described in the “Monitoring DNS-AS” section of DNS-AS in the NBAR Configuration Guide. Test DNS-AS functionality by generating traffic for the applications configured with the feature, then use the show commands to confirm that the binding table has been created correctly on the routers operating with DNS-AS.
When Is Troubleshooting Necessary
Any of the following may suggest client-side problems with DNS-AS:
■ If… Custom protocols are not being created by DNS-AS on the client router.
■ If… Network operations, such as traffic reporting, that depend on customized application handling through the DNS-AS feature are not functioning as expected.
How to Use this Guide
This guide provides DNS-AS Troubleshooting Tools that you can use individually, a Comprehensive Troubleshooting Workflow, and specific Problem Scenarios with recommended troubleshooting steps.
DNS-AS Troubleshooting Tools
Use the diagnostic tools described in this section individually or as part of a troubleshooting workflow, such as the Comprehensive Troubleshooting Workflow.
Diagnostic Tool: Verify Customization Interval
The DNS-AS binding table is regenerated on the router every 5 minutes, by default. This is the “customization interval,” the time during which the router collects auto-learn raw data before creating new custom protocols (see Showing the DNS-AS custom-application Data in the NBAR Configuration Guide).
Verify that the traffic has been run on the router. The traffic may not lead to the creation of new custom protocols in the binding table for a period of 5 minutes.
Diagnostic Tool: Verify that Traffic Interface and DNS-AS Server on Same VRF
The DNS query traffic and the DNS-AS server must be on the same VRF.
Figure 1. Verifying that Traffic Interface and DNS-AS Server on the Same VRF

Use show ip vrf to verify that the traffic interface and the interface connected to the DNS-AS server are assigned to the same VRF.
Diagnostic Tool: Verify that DNS-AS Server Is Specified on DNS-AS Client Device
Use show avc dns-as client name-server brief to verify that the correct DNS-AS server IP address is configured on the DNS-AS client device. In this example, the DNS-AS server address is 1.1.1.1.
Diagnostic Tool: Check Connectivity between DNS-AS Client Device and DNS-AS Server
Use ping to check the connectivity from the DNS-AS client device to the DNS-AS server.
ping <vrf> <dns-as-server ip>
In this example, the ping results confirm connectivity.
Diagnostic Tool: DNS Session Simulation
To simulate a DNS session between the DSN-AS client (router) and the DNS-AS server, send DNS queries (A and TXT) from the router to the DNS-AS server and examine the DNS records configured on the server.
1. Use one of the following options to create DNS query traffic:
— DNS Session Option A: Generate DNS Traffic Using Cisco Router DNS-AS Client
— DNS Session Option B: Generate DNS Traffic Using Windows PC
— DNS Session Option C: Generate DNS Traffic Using Linux PC
2. After generating the DNS requests, view the DNS session information. See Diagnostic Tool: View DNS Session Using Wireshark.
Figure 2. Overview of DNS Session Simulation: Create traffic, then View Session

DNS Session Option A: Generate DNS Traffic Using Cisco Router DNS-AS Client
This procedure specifies a DNS-AS server and generates DNS query traffic to the server.
Figure 3. Generating DNS Traffic Using a Cisco Router

1. On the DNS-AS client (Cisco router), check the address of the configured DNS-AS server. Use one of the following commands:
■ (Not using VRF) ip name-server <server-ip>
■ (Using VRF) ip name-server vrf <vrf-name> <dns-as-server ip>
2. In global configuration mode, execute the service internal troubleshooting command to enable test commands used in the troubleshooting steps in this section.
Note: This command is used in advanced troubleshooting. After completing the troubleshooting, disable the feature using the no service internal command.
3. (Optional) Set the configuration parameters for generating the DNS request.
test ngdns config vrf <vrf-name>
4. Generate a DNS A query.
test ngdns <domain-name>
5. Generate a DNS TXT query.
test ngdns <domain-name> type txt
6. Display the router host table. Use one of the following commands:
■ (Not using VRF) show hosts
■ (Using VRF) show hosts vrf <vrf-name>
Example
In this example:
■ A DNS query for the “aaaa.nbar-dns-as.com” domain is sent to a DNS-AS server.
■ Router is using VRF
■ The server IP address is 1.1.1.1
The initial steps generate the DNS requests.
The final step displays the router’s host table, showing the information provided by DNS-AS in the TXT response, and the address for the requested domain in the A response (shown in bold).
DNS Session Option B: Generate DNS Traffic Using Windows PC
This procedure generates DNS query using a Windows PC in the network.
Figure 4. Generating DNS Traffic Using Windows PC

1. On the Windows PC, open a command line window and use the nslookup command to generate a DNS A session.
nslookup <domain> <dns-server ip>
2. Use nslookup as follows to generate a DNS TXT session.
nslookup –type=txt <domain> <dns-server ip>
Example
In this example, nslookup creates DNS A and TXT queries for aaaa.nbar-dns-as.com.
DNS Session Option C: Generate DNS Traffic Using Linux PC
This procedure generates DNS query using a client Linux PC in the network.
Figure 5. Generating DNS Traffic Using Linux PC
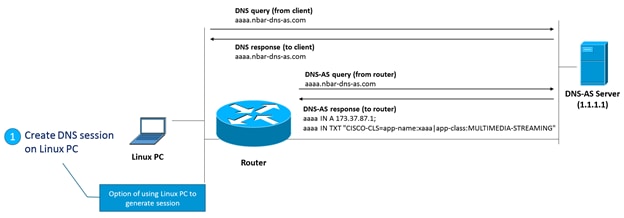
1. On the Linux PC, at a command line interface, use the dig command to generate a DNS query.
dig @<server-ip> <domain> +short
2. Use the dig command as follows to generate a TXT query.
dig txt @<server-ip> <domain> +short
Example
In this example, dig creates DNS A and TXT queries for aaaa.nbar-dns-as.com.
Diagnostic Tool: View DNS Session Using Wireshark
On the DNS-AS server, use a packet analyzer application, such as the popular Wireshark, to view the DNS session data.
Figure 6. Viewing DNS Session Using Wireshark

Diagnostic Tool: Check the DNS-AS Client Statistics
On the DNS-AS client (router), use the show avc dns-as client statistics command to display the DNS-AS client statistics. The command output shows whether the DNS-AS client sent queries to the DNS-AS server, and shows whether the server responded.
In the show avc dns-as client statistics output, check the “TXT Query TX packets” (shown in bold). A value of 0 indicates that the DNS-AS client (router) has not sent any queries to the server.
Example 1: No DNS queries sent, no responses received
This example output shows a value of 0 for “TXT Query TX packets”.
Example 2: DNS queries sent, responses received
This more typical example output shows correct functionality. The router has sent several DNS queries to the server. The query and response packet counts should be equal.
Diagnostic Tool: Check for Pending Queries
The DNS-AS client caches incoming DNS queries for an interval (default: 3 minutes) before sending queries to the DNS-AS server. During this time, they are called “pending” queries.
If the show avc dns-as client statistics output indicates that no DNS queries have been sent to the server, the reason could be that the queries are still pending.
Use the ip nbar classification auto-learn dns-as-client pending-queries command to check for pending queries.
Example 1: No Pending Queries
This output example shows no pending queries.
Example 2: Pending Queries
This output example shows pending queries.
Diagnostic Tool: Check Trusted Domains Configured on Router
Check the configured trusted domains on the router. The router sends a DNS request to the DNS-AS server only for applications specified as trusted domains. Use show run command, piped to the sec command to display the configured trusted domains.
show run | sec trusted-domains
Example: Trusted domains
Diagnostic Tool: Display Information Learned from the DNS-AS Server
The show ip nbar classification auto-learn dns-as-client 100 detailed command displays the application information that a router has received from the DNS-AS server, arranged by domain.
Example: Application data learned from DNS-AS server
In this example, the router has information for 10 applications.
Problem Scenarios
DNS-AS client auto-custom binding table is empty
Symptoms
The show avc dns-as client binding-table command displays the auto-custom bind table. The following example shows and empty binding table, indicated by “No data available yet” (bold added).
Troubleshooting Steps
Use the Comprehensive Troubleshooting Workflow.
DNS-AS custom protocols do not appear in the router’s binding table
Symptoms
The results of the show ip nbar protocol-discovery stats packet-count command do not show the custom protocols generated by DNS-AS.
Troubleshooting Steps
Use the Comprehensive Troubleshooting Workflow.
Comprehensive Troubleshooting Workflow
The comprehensive client-side troubleshooting workflow addresses the following common issues affecting DNS-AS function:
| Category |
Potential Problem |
Description |
| Connectivity |
Network connectivity |
Connectivity problems between the DNS-AS client (router) and the DNS-AS server. ■ Step 1: Verify connectivity |
| Server specification |
Wrong DNS-AS server specified on the client device. ■ Step 2: Verify that the client specifies the DNS-AS server correctly |
|
| DNS session |
DNS query/response not successful. ■ Step 3: Verify that DNS-AS server replies to queries ■ Step 4: Verify that DNS-AS client queries reach DNS-AS server ■ Step 5: Check for pending queries on the DNS-AS client ■ Step 6: Verify that router has received information from the DNS-AS server |
|
| Client (router) |
Trusted domain configuration |
Wrong DNS-AS trusted-domain configuration on the DNS-AS client device. The trusted domain configuration specifies the applications that are handled by the DNS-AS feature. ■ Step 7: Verify the trusted domains |
| Custom protocol creation |
Problem with completing the process of custom protocol creation. ■ Step 8: Check the binding table ■ Step 9: Verify custom protocols |
|
| DNS-AS server |
Server configuration |
Incorrect DNS-AS record configuration on the DNS-AS server. ■ Step 10: On the DNS-AS server, verify the TXT records |
Step 1: Verify connectivity
Check connectivity between the DNS-AS client (router) and the DNS-AS server.
Procedure
Use the ping <dns-as-server ip> command.
See Diagnostic Tool: Check Connectivity between DNS-AS Client Device and DNS-AS Server.
Results
If the server does not respond to the ping, there is a basic connectivity problem between the client and server.
Step 2: Verify that the client specifies the DNS-AS server correctly
Verify that the client (router) is configured correctly to connect to the DNS-AS server.
Procedure
Use the show avc dns-as client name-server brief command to display the configured DNS-AS server(s).
Results
Expected result: One or more correct DNS-AS servers are configured. The server(s) must be accessible, as tested in Step 1: Verify connectivity.
Step 3: Verify that DNS-AS server replies to queries
Verify that the DNS-AS server replies to DNS A and TXT queries from the client (router).
Procedure
1. Use one of the following options to create DNS query traffic:
— DNS Session Option A: Generate DNS Traffic Using Cisco Router DNS-AS Client
— DNS Session Option B: Generate DNS Traffic Using Windows PC
— DNS Session Option C: Generate DNS Traffic Using Linux PC
2. After generating the DNS requests, view the DNS session information. See Diagnostic Tool: View DNS Session Using Wireshark.
Figure 7. Viewing DNS Session Information

Results
Expected result: DNS requests appear in the DNS session information.
Step 4: Verify that DNS-AS client queries reach DNS-AS server
Verify that the DNS-AS client (router) has sent DNS requests to the DNS-AS server, including:
■ A (for IPv4 address) or AAAA (for IPv6 address) queries
■ TXT queries
Procedure
Use the show avc dns-as client statistics command, described in Diagnostic Tool: Check the DNS-AS Client Statistics.
Results
Expected result: show avc dns-as client statistics output indicates queries sent and responses received. If none are displayed, the reason could be that the router has pending queries that have not yet been sent to the DNS-AS server. See Step 5: Check for pending queries on the DNS-AS client.
Step 5: Check for pending queries on the DNS-AS client
Check for pending queries on the DNS-AS client (router).
The DNS-AS client caches incoming DNS queries for an interval (default: 3 minutes) before sending queries to the DNS-AS server. During this time, they are called “pending” queries.
If the show avc dns-as client statistics output indicates that no DNS queries have been sent to the server, the reason could be that the queries are still pending.
Procedure
Use the ip nbar classification auto-learn dns-as-client pending-queries command to check for pending queries. See .Diagnostic Tool: Check for Pending Queries.
Results
Expected result: Counters increase after each inject interval (3 minutes). If the results do not show this, determine why no DNS requests are being made.
Step 6: Verify that router has received information from the DNS-AS server
Verify that the DNS-AS client (router) has received and stored information from the DNS-AS server.
Procedure
Use the show ip nbar classification auto-learn dns-as-client 100 detailed command to display the application information that a router has received from the DNS-AS server, arranged by domain.
See Diagnostic Tool: Display Information Learned from the DNS-AS Server.
Results
Expected result: The table has entries that match the information provided by the DNS-AS server.
Step 7: Verify the trusted domains
Check the configured trusted domains on the router. The router sends a DNS request to the DNS-AS server only for applications specified as trusted domains.
Procedure
See Diagnostic Tool: Check Trusted Domains Configured on Router.
Results
Expected result: The show run | sec trusted-domains output shows the configured regular expressions that are used by DNS packet snooping to identify the applications being configured with the DNS-AS feature.
Step 8: Check the binding table
The DNS-AS binding table is regenerated on the router every 5 minutes, by default. This is the “customization interval,” the time during which the router collects auto-learn raw data before creating new custom protocols.
Verify that the auto-custom protocol table reflects the information received from the DNS-AS server.
Procedure
Use the show avc dns-as client binding-table command to display the auto-learn table.
Results
Expected results:
■ The table has entries
■ The entries match the info displayed in Step 6: Verify that router has received information from the DNS-AS server.
Step 9: Verify custom protocols
Verify that DNS-AS is generating custom protocols for the applications configured to operate with DNS-AS. Also verify that the traffic for those applications is directed to the IP addresses specified by the DNS-AS server.
Procedure
Use the show ip nbar protocol-discovery stats packet-count command to display the packet count for all NBAR protocols, including the custom protocols generated by DNS-AS.
Results
Expected result: Output displays the custom protocols and shows an increasing packet count.
Step 10: On the DNS-AS server, verify the TXT records
On the DNS-AS server, verify that the TXT records have been configured correctly, according to the rules for specifying NBAR DNS‑AS records. If the TXT record is not configured correctly, the router will not learn the classification information specified in the TXT records.
Procedure
The procedure will vary, according to the OS and DNS software operating on the DNS-AS server. In general terms, inspect the TXT records specified on the server.
■ The CISCO-CLS is case-sensitive. Verify that it is capitalized.
■ Verify the syntax.
Example: For a DNS server using BIND as the DNS server software, a valid entry for an application called staffonly might appear as follows:
Legal Information
THE SPECIFICATIONS AND INFORMATION REGARDING THE PRODUCTS IN THIS MANUAL ARE SUBJECT TO CHANGE WITHOUT NOTICE. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL RESPONSIBILITY FOR THEIR APPLICATION OF ANY PRODUCTS.
THE SOFTWARE LICENSE AND LIMITED WARRANTY FOR THE ACCOMPANYING PRODUCT ARE SET FORTH IN THE INFORMATION PACKET THAT SHIPPED WITH THE PRODUCT AND ARE INCORPORATED HEREIN BY THIS REFERENCE. IF YOU ARE UNABLE TO LOCATE THE SOFTWARE LICENSE OR LIMITED WARRANTY, CONTACT YOUR CISCO REPRESENTATIVE FOR A COPY.
The Cisco implementation of TCP header compression is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB’s public domain version of the UNIX operating system. All rights reserved. Copyright © 1981, Regents of the University of California.
NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ARE PROVIDED “AS IS” WITH ALL FAULTS. CISCO AND THE ABOVE-NAMED SUPPLIERS DISCLAIM ALL WARRANTIES, EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, THOSE OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE PRACTICE.
IN NO EVENT SHALL CISCO OR ITS SUPPLIERS BE LIABLE FOR ANY INDIRECT, SPECIAL, CONSEQUENTIAL, OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental.
All printed copies and duplicate soft copies are considered un-Controlled copies and the original on-line version should be referred to for latest version.
Cisco has more than 200 offices worldwide. Addresses, phone numbers, and fax numbers are listed on the Cisco website at www.cisco.com/go/offices.
Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R)
© 2016 Cisco Systems, Inc. All rights reserved.
 Feedback
Feedback