Cisco IoT Field Network Director User Guide, Release 4.1.x
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- January 31, 2018
Chapter: Managing Devices
- Overview
- Managing Routers
- Working with Router Views
- Migrating Router Operating Systems
- Creating Work Orders
- Refreshing the Router Mesh Key
- Managing Embedded Access Points on Cisco C819 and Cisco IR829 ISRs
- Using Router Filters
- Displaying Router Configuration Groups
- Displaying Router Firmware Groups
- Displaying Router Tunnel Groups
- Managing Endpoints
- Managing the Cisco Wireless Gateway for LoRaWAN
- Managing Cisco IR510 WPAN Industrial Routers
- Managing Head-End Routers
- Managing External Modules
- Managing Servers
- Tracking Assets
- Common Device Operations
- Selecting Devices
- Customizing Device Views
- Viewing Devices in Map View
- Configuring Map Settings
- Changing the Sorting Order of Devices
- Exporting Device Information
- Pinging Devices
- Tracing Routes to Devices
- Managing Device Labels
- Removing Devices
- Displaying Detailed Device Information
- Using Filters to Control the Display of Devices
- Performing Bulk Import Actions
- Configuring Device Group Settings
- Synchronizing Endpoint Membership
- Editing the ROUTER Configuration Template
- Mesh Security Keys for Dual-PHY Devices
- Configuration Details for WPAN Devices
- Editing the ENDPOINT Configuration Template
- Pushing Configurations to Routers
- Pushing Configurations to Endpoints
- Types of Device Properties
- Device Properties by Category
- Cellular Link Settings
- Cellular Link Metrics for CGRs
- DA Gateway Properties
- Dual PHY WPAN Properties
- Embedded Access Point Credentials
- Embedded AP Properties
- Ethernet Link Metrics
- Guest OS Properties
- Head-End Routers > Netconf Config
- Head-End Routers > Tunnel 1 Config
- Head-End Routers > Tunnel 2 Config
- Inventory
- Mesh Link Config
- Mesh Device Health
- Mesh Link Keys
- Mesh Link Settings
- Mesh Link Metrics
- NAT44 Metrics
- PLC Mesh Info
- Raw Sockets Metrics and Sessions
- Router Battery
- Router Config
- Router Credentials
- Router DHCP Info
- Router DHCP Proxy Config
- Router Health
- Router Tunnel Config
- Router Tunnel 1 Config
- Router Tunnel 2 Config
- SCADA Metrics
- User-defined Properties
- WiFi Interface Config
- WiMAX Config
- WiMAX Link Metrics
- WiMAX Link Settings
Managing Devices
This section describes how to manage devices in IoT FND, and includes the following topics:
■![]() Managing the Cisco Wireless Gateway for LoRaWAN
Managing the Cisco Wireless Gateway for LoRaWAN
■![]() Managing Cisco IR510 WPAN Industrial Routers
Managing Cisco IR510 WPAN Industrial Routers
■![]() Demo and Bandwidth Operation Modes
Demo and Bandwidth Operation Modes
Overview
Use the following IoT FND pages to monitor, add and remove devices, and perform other device management tasks that do not include device configuration:
■![]() To work with Field Devices such as Routers (CGR1000, C800, IR800, SBR (C5921)) and Endpoints (meters and IR500 gateways), and IoT Gateways (such as the LoRaWAN gateway), use the DEVICES > Field Devices page.
To work with Field Devices such as Routers (CGR1000, C800, IR800, SBR (C5921)) and Endpoints (meters and IR500 gateways), and IoT Gateways (such as the LoRaWAN gateway), use the DEVICES > Field Devices page.
–![]() Note: In some textual displays of the IoT FND, routers may display as “FAR” rather than the router model (cgr1000, etc).
Note: In some textual displays of the IoT FND, routers may display as “FAR” rather than the router model (cgr1000, etc).
■![]() To work with Head-end Routers (ASR1000, ISR3900, ISR4000) use the DEVICES > Head-End Routers page.
To work with Head-end Routers (ASR1000, ISR3900, ISR4000) use the DEVICES > Head-End Routers page.
■![]() To work with FND NMS and database servers, use the DEVICES > Servers page.
To work with FND NMS and database servers, use the DEVICES > Servers page.
■![]() To view Assets associated with the Cisco Wireless Gateway for LoRaWAN (IXM-LPWA-900), use the DEVICES > Assets page.
To view Assets associated with the Cisco Wireless Gateway for LoRaWAN (IXM-LPWA-900), use the DEVICES > Assets page.
Note: Refer to the “Managing Managing Firmware UpgradesManaging Firmware UpgradesManaging DevicesFirmware Upgrades” chapter of this book for details on firmware updates for Routers and Gateways mentioned in this chapter.
Managing Routers
You manage routers on the Field Devices page (DEVICES > Field Devices). Initially, the page displays devices in the Default view. This section includes the following topics:
■![]() Refreshing the Router Mesh Key
Refreshing the Router Mesh Key
■![]() Managing Embedded Access Points on Cisco C819 and Cisco IR829 ISRs
Managing Embedded Access Points on Cisco C819 and Cisco IR829 ISRs
■![]() Displaying Router Configuration Groups
Displaying Router Configuration Groups
■![]() Displaying Router Firmware Groups
Displaying Router Firmware Groups
■![]() Displaying Router Tunnel Groups
Displaying Router Tunnel Groups
Working with Router Views
Unless you select the Default to map view option in user preferences (see Setting User Preferences for User Interface Display) the Field Devices page defaults to the List view, which contains basic device properties. Select a router or group of routers in the Browse Devices pane (left pane) to display tabs in the main pane.
The router or routers you select determine which tabs display.
Note: Listed below are all the possible tabs. You can select to view the Map option from the List view.
Each of the tab views above displays different sets of device properties. For example, the Default view displays basic device properties, and the Cellular-GSM view displays device properties particular to the cellular network.
For information on how to customize router views, see Customizing Device Views.
For information about the device properties that display in each view, see Device Properties.
For information about common actions performed in these views (for example, adding labels and changing device properties), see Common Device Operations.
Viewing Routers in Map View
To view routers in Map view, check the Enable map check box in <user> > Preferences (see Setting User Preferences for User Interface Display), and then click the Map tab (see Map View) in the main pane.
Figure 2 Setting User Preferences for User Interface Display


Note: You can view any RPL tree by clicking the device in Map view, and closing the information popup window.
The RPL tree connection displays data traffic flow as blue or orange lines, as follows:
■![]() Orange lines indicate that the link is an uplink: data traffic flows in the up direction on the map.
Orange lines indicate that the link is an uplink: data traffic flows in the up direction on the map.
■![]() Blue lines indicate that the link is a downlink: data traffic flows in the down direction on the map.
Blue lines indicate that the link is a downlink: data traffic flows in the down direction on the map.
Migrating Router Operating Systems
You can migrate CGR operating systems from CG-OS to IOS on the CONFIG > Firmware Update page, using the procedure in Performing CG-OS to Cisco IOS Migrations.
Creating Work Orders
Create work orders in IoT FND to deploy field technicians for device inspections. Field technicians use the IoT-DM client to connect to IoT FND and download the work order.
Note: CGR1000, IR800, and IR500 support work orders. For more details on actions supported by platform and minimum software releases required, refer to the Release Notes for Cisco IoT Device Manager 5.2 and the
Cisco IoT Device Manager Installation and User Guide, Release 5.x for configuration details.
Note: The Work Orders feature works with Release 3.0 or later of Device Manager (IoT-DM) only. See “Accessing Work Authorizations” in the Cisco Connected Grid Device Manager Installation and User Guide, Release 3.1 for integration instructions for CG-OS installations. For Cisco IOS installations, please refer to the Cisco Connected Grid Device Manager Installation and User Guide, Release 4.0 or later.
Note: Before you can create a work order, your user account must have Work Order Management permissions enabled. See Managing Roles and Permissions.
Figure 4 More Actions > Create Work Order

To create work orders for CGRs, select a router or group of routers in the Browse Devices pane, and then in Default view:
1.![]() Check the check box of the faulty CGR.
Check the check box of the faulty CGR.
2.![]() Choose More Actions > Create Work Order.
Choose More Actions > Create Work Order.
The Operations > Work Orders page appears. IoT Field Network Director adds the names of the selected field device to the Field Device Names/EIDs field as a comma-separated list.
3.![]() Follow the steps in Creating Work Orders to create the work order.
Follow the steps in Creating Work Orders to create the work order.
For more information about work orders, see Managing Work Orders.
Refreshing the Router Mesh Key
If you suspect unauthorized access attempts to a router, refresh its mesh key.
Caution: Refreshing the router mesh key can result in mesh endpoints being unable to communicate with the router for a period of time until the mesh endpoints re-register with the router, which happens automatically.
To refresh the router mesh key, select a router or group of routers in the Browse Devices pane, and then in Default view:
1.![]() Check the check boxes of the of the routers to refresh.
Check the check boxes of the of the routers to refresh.
2.![]() Choose More Actions > Refresh Router Mesh Key from the drop-down menu.
Choose More Actions > Refresh Router Mesh Key from the drop-down menu.
Managing Embedded Access Points on Cisco C819 and Cisco IR829 ISRs
IoT Field Network Director allows you to manage the following embedded access point (AP) attributes on C819 and IR829 ISRs:
Note: IoT Field Network Director can only manage APs when operating in Autonomous mode.
■![]() Periodic inventory collection
Periodic inventory collection
■![]() Firmware update of APs when operating in Autonomous Mode
Firmware update of APs when operating in Autonomous Mode
Note: Not all C800 Series and IR800 routers have embedded APs. A C800 ISR features matrix is here. The IR800 ISR features matrix is here.
Using Router Filters
To refine the list of displayed routers, use the built-in router filters under ROUTERS in the Browse Devices pane or saved custom searches in the Quick View pane (left pane). For example, to display all operational routers, click the Up group under ROUTERS in the Browse Devices pane. Click a filter to insert the corresponding search string in the Search Devices field. For example, clicking the Up group under ROUTERS inserts the search string status:up in the Search Devices field.
Displaying Router Configuration Groups
At the DEVICES > Field Devices page, use the Browse Devices pane to display routers that belong to one of the groups (such as CGR1000) listed under ROUTER.
Displaying Router Firmware Groups
1.![]() At the CONFIG > Firmware Update page, select the Groups tab (left pane) and then choose one of the ROUTER Groups (such as Default-c800, Default-cgr1000, Default-lorawan, Default-ir800 or Default-sbr).
At the CONFIG > Firmware Update page, select the Groups tab (left pane) and then choose one of the ROUTER Groups (such as Default-c800, Default-cgr1000, Default-lorawan, Default-ir800 or Default-sbr).
2.![]() The firmware image available for the router displays under the Name field in the right-pane. In the case of the Default-ir800, it includes both the IR809 and IR829, so there are two different firmware images listed.
The firmware image available for the router displays under the Name field in the right-pane. In the case of the Default-ir800, it includes both the IR809 and IR829, so there are two different firmware images listed.

Displaying Router Tunnel Groups
Use the Browse Devices pane to display the router devices that belong to one of the groups listed under ROUTER TUNNEL GROUPS.

Managing Endpoints
To manage endpoints, view the DEVICES > Field Devices page. By default, the page displays the endpoints in List view. This section includes the following topics:
■![]() Viewing Endpoints in Default View
Viewing Endpoints in Default View
■![]() Viewing Mesh Endpoints in Map View
Viewing Mesh Endpoints in Map View
■![]() Displaying Mesh Endpoint Configuration Groups
Displaying Mesh Endpoint Configuration Groups
■![]() Displaying Mesh Endpoint Firmware Groups
Displaying Mesh Endpoint Firmware Groups
Viewing Endpoints in Default View
When you open the DEVICES > Field Devices page in Default view, IoT FND lists All FAN Devices such as Routers, Endpoints (meters, gateways), and IoT Gateway and their basic device properties.
When you select an ENDPOINT device or group in the Browse Devices pane, IoT FND provides tabs to display additional endpoint property views:
Note: Listed below are all the possible tabs. You can select to view the Map option from the List view.
Each one of these views displays different sets of device properties.
For information on how to customize endpoint views, see Customizing Device Views.
For information about the device properties displayed in each view, see Device Properties.
For information about the common actions in these views (for example, adding labels and changing device properties) that also apply to other devices, see Common Device Operations.
Viewing Mesh Endpoints in Map View
To view mesh endpoints in Map view, select Enable map in <user> > Preferences, and click the Map tab.
Blocking Mesh Devices
If you suspect unauthorized access attempts to a mesh device, block it from accessing IoT FND.
Caution: If you block a mesh endpoint, you cannot unblock it using IoT FND. To re-register the mesh endpoints with IoT FND, you must escalate and get your mesh endpoints administrator involved.
To block a mesh endpoint device, in Default view (DEVICES > Field Devices > METER > CG-MESH):
1.![]() Check the check boxes of the mesh devices to refresh.
Check the check boxes of the mesh devices to refresh.
2.![]() Choose More Actions > Block Mesh Device from the drop-down menu.
Choose More Actions > Block Mesh Device from the drop-down menu.

3.![]() Click Yes in the Confirm dialog box.
Click Yes in the Confirm dialog box.
4.![]() Delete the mesh endpoint from the NPS server to prevent the device from rejoining the mesh network.
Delete the mesh endpoint from the NPS server to prevent the device from rejoining the mesh network.
Displaying Mesh Endpoint Configuration Groups
You can view available defined configuration groups for mesh endpoints at the CONFIG > Device Configuration page.
Displaying Mesh Endpoint Firmware Groups
You can use the Browse Devices pane to display the mesh endpoint devices that belong to one of the groups listed under ENDPOINTS.
Managing the Cisco Wireless Gateway for LoRaWAN
You can use the Browse Devices pane to display the Cisco interface module for LoRaWAN devices (IXM-LPWA-800) that belongs to the IoT Gateway group.
The Cisco Wireless Gateway for LoRaWAN can function as:
■![]() a virtual interface of the Cisco 809 and 829 Industrial Integrated Service Routers (IR809, IR829) to provide LoRa radio access with the IR809 and IR829 providing an IP backhaul (Gigabit Ethernet, Fiber, 4G/LTE, and Wi-Fi). In this case, LoRaWAN has an Operating Mode of IOS Interface and displays the Hosting Device ID for the IR800 system to which it connects.
a virtual interface of the Cisco 809 and 829 Industrial Integrated Service Routers (IR809, IR829) to provide LoRa radio access with the IR809 and IR829 providing an IP backhaul (Gigabit Ethernet, Fiber, 4G/LTE, and Wi-Fi). In this case, LoRaWAN has an Operating Mode of IOS Interface and displays the Hosting Device ID for the IR800 system to which it connects.
■![]() a standalone unit using its own built-in Fast Ethernet backhaul to access LAN switches, routers, Wi-Fi AP or other IP interfaces. When functioning as a standalone gateway, LoRaWAN has an Operating Mode of Standalone.
a standalone unit using its own built-in Fast Ethernet backhaul to access LAN switches, routers, Wi-Fi AP or other IP interfaces. When functioning as a standalone gateway, LoRaWAN has an Operating Mode of Standalone.
At the Browse Devices pane, you can view Device details for the LoRaWAN at both the ROUTER > IR800 page and the GATEWAY page.
1.![]() Choose DEVICES > Field Devices.
Choose DEVICES > Field Devices.
2.![]() Select a device under IOT GATEWAY > default-lorawan in the left-pane.
Select a device under IOT GATEWAY > default-lorawan in the left-pane.
3.![]() Click on the desired IXM-LPWA-900 system listed in the Name column to display Device Info, Events, Config Properties, Running Config, and Assets for the gateway.
Click on the desired IXM-LPWA-900 system listed in the Name column to display Device Info, Events, Config Properties, Running Config, and Assets for the gateway.
To perform supported actions for the IOT GATEWAY, use the following buttons:
■![]() Show on Map, Ping, Traceroute, Refresh Metrics and Restart Radio
Show on Map, Ping, Traceroute, Refresh Metrics and Restart Radio
Figure 5 IoT Gateway Device Info Page, 1 of 2

Figure 6 IoT Gateway Device Info Page, 2 of 2

Managing Cisco IR510 WPAN Industrial Routers
Cisco IR510 Industrial Router (formerly known as Cisco 500 Series wireless personal area network (WPAN) industrial routers) provides unlicensed 902-928MHz, ISM-band IEEE 802.15.4g/e/v WPAN communications to diverse Internet of Things (IoT) applications such as smart grid, distribution automation (DA), and supervisory control and data acquisition (SCADA). As the next generation of the DA gateway, IR510 provides higher throughput, distributed intelligence, GPS, and enhanced security. unlicensed 915-MHz industrial, scientific, and medical band WPAN communications.
Note: IR510 is identified and managed as an ENDPOINT in IoT FND.
IoT FND employs Profile-based configuration for IR510s. This allows you to define a specific Profile instance (configuration) that you can assign to multiple IR500 configuration groups.
Table 1 lists the supported Profile types. Note the following about the Profiles:
■![]() Each Profile type has a default profile instance. The default Profile instance cannot be deleted.
Each Profile type has a default profile instance. The default Profile instance cannot be deleted.
■![]() You can create a Profile instance and associate that profile with multiple configuration groups on the IR510.
You can create a Profile instance and associate that profile with multiple configuration groups on the IR510.
■![]() A ‘None’ option is available for all the Profile types that indicates that the configuration does not have any settings for that Profile type.
A ‘None’ option is available for all the Profile types that indicates that the configuration does not have any settings for that Profile type.
■![]() When a configuration push is in progress for a configuration group, all the associated Profiles will be locked (lock icon displays) and Profiles cannot be updated or deleted during that time.
When a configuration push is in progress for a configuration group, all the associated Profiles will be locked (lock icon displays) and Profiles cannot be updated or deleted during that time.
■![]() A lock icon displays for a locked Profile.
A lock icon displays for a locked Profile.
Create, Delete, Rename or Clone any Profile at the Config Profiles Page

1.![]() Choose CONFIG > DEVICE CONFIGURATION > Config Profiles tab
Choose CONFIG > DEVICE CONFIGURATION > Config Profiles tab
2.![]() Click the + (plus icon) at the top of the Configuration Panel to open the Add Profile entry panel.
Click the + (plus icon) at the top of the Configuration Panel to open the Add Profile entry panel.
3.![]() Enter a Name for the new profile and select the Profile type from the drop-down menu.
Enter a Name for the new profile and select the Profile type from the drop-down menu.
4.![]() Click Add button. A new entry for the Profile entry appears in the left pane under the Profile Type sub-heading.
Click Add button. A new entry for the Profile entry appears in the left pane under the Profile Type sub-heading.
1.![]() Choose CONFIG > DEVICE CONFIGURATION > Config Profiles tab.
Choose CONFIG > DEVICE CONFIGURATION > Config Profiles tab.
2.![]() Select the Profile name (excluding Default-Profile) that you want to delete. Click on the trash icon to remove the Profile.
Select the Profile name (excluding Default-Profile) that you want to delete. Click on the trash icon to remove the Profile.
3.![]() In the pop up window that appears, click Yes to confirm deletion.
In the pop up window that appears, click Yes to confirm deletion.
1.![]() Choose CONFIG > DEVICE CONFIGURATION > Config Profiles tab.
Choose CONFIG > DEVICE CONFIGURATION > Config Profiles tab.
2.![]() Select the Profile name (excluding Default-Profile) that you would to rename. Click on the pencil icon to open the Rename Profile pop up window.
Select the Profile name (excluding Default-Profile) that you would to rename. Click on the pencil icon to open the Rename Profile pop up window.
3.![]() Make your edit and click OK. New name appears in the left pane.
Make your edit and click OK. New name appears in the left pane.
1.![]() Choose CONFIG > DEVICE CONFIGURATION > Config Profiles tab.
Choose CONFIG > DEVICE CONFIGURATION > Config Profiles tab.
2.![]() Select the Profile name that you want to clone. Click on the overlapping squares icon to open the Clone Profile pop up window.
Select the Profile name that you want to clone. Click on the overlapping squares icon to open the Clone Profile pop up window.
3.![]() Enter a Name for the new profile and select the Profile type from the drop-down menu.
Enter a Name for the new profile and select the Profile type from the drop-down menu.
4.![]() Click Add button. A new Profile entry appears in the left pane under the Profile Type sub-heading.
Click Add button. A new Profile entry appears in the left pane under the Profile Type sub-heading.
Figure 7 Configuration Template for a Profile

■![]() Set DSCP (QoS) markings for all interfaces - Ethernet, DTE and DCE. Options: Low Priority (0), Normal Priority (10), Medium Priority (18).
Set DSCP (QoS) markings for all interfaces - Ethernet, DTE and DCE. Options: Low Priority (0), Normal Priority (10), Medium Priority (18).
■![]() DSCP is applied on interfaces. Default values for DCE and DTE are Low Priority (0). There are no default values for Ethernet. Traffic will flow unmarked if you do not configure any value on the Configuration Template.
DSCP is applied on interfaces. Default values for DCE and DTE are Low Priority (0). There are no default values for Ethernet. Traffic will flow unmarked if you do not configure any value on the Configuration Template.
■![]() Only one Raw Socket session can flow through DCE and DTE interfaces at a time. The DSCP value will be the same throughout.
Only one Raw Socket session can flow through DCE and DTE interfaces at a time. The DSCP value will be the same throughout.
Configuration Profile for a Group
■![]() You can view Profile details in the Configuration Group Template page (Configuration Template for a Group).
You can view Profile details in the Configuration Group Template page (Configuration Template for a Group).
■![]() You can save configuration templates and push the configuration to all devices in the Configuration Group.
You can save configuration templates and push the configuration to all devices in the Configuration Group.
■![]() Any of the Profile associations within a Configuration Group are optional. For example, a Configuration Group may not require Serial DCE settings, so you may select ‘ None’ for Serial DCE settings.
Any of the Profile associations within a Configuration Group are optional. For example, a Configuration Group may not require Serial DCE settings, so you may select ‘ None’ for Serial DCE settings.
Figure 8 Configuration Template for a Group

Managing Head-End Routers
To manage Head-end routers (HERs), open the Head-End Routers page by choosing Devices > Head-End Routers (Head-End Routers Page). Unless Enable Map is selected in user preferences, by default, the page displays the HERs in List view. When you open the Head-End Routers page in List view, IoT FND displays the Default list view. This view displays basic HER device properties. In addition, IoT FND provides these tabs to display additional HER property views:
Each one of these views displays different sets of device properties. These views display information about the HER tunnels.
Figure 9 Head-End Routers Page

For information on how to customize HER views, see Customizing Device Views.
For information about the device properties displayed in each view, see Device Properties.
For information about the common actions in these views (for example, adding labels and changing device properties) that also apply to other devices, see Common Device Operations.
Managing External Modules
To manage devices that connect to Field Devices such as routers, choose Devices > Field Devices. By default, the page displays all known FAN Devices in List view.
You can manage the following external modules using IoT FND:
Itron CAM Module
You can install an Itron CAM Module within a CGR, after you meet the following requirements:
Guest OS (GOS) must be running on a CGR before you install the Itron CAM module.
1.![]() ACTD driver must be installed and running within the CGR Guest OS before you can use IoT FND to deploy, upgrade or monitor ACTD. This ensures that FND can reach the CGR Guest OS to manage the ACTD driver. This can be done by configuring NAT on the CGR or setup a static route on CGR and HER as follows:
ACTD driver must be installed and running within the CGR Guest OS before you can use IoT FND to deploy, upgrade or monitor ACTD. This ensures that FND can reach the CGR Guest OS to manage the ACTD driver. This can be done by configuring NAT on the CGR or setup a static route on CGR and HER as follows:
A) In the cgms.properties file, you must set the “manage-actd” property to true as follows:
B) Two new device properties are added for the user to specify the Guest OS external reachable IP address and the IOx access port in case port mapping is used.
2.![]() From within IoT FND, do the following to upload the ACTD driver:
From within IoT FND, do the following to upload the ACTD driver:
A) Choose CONFIG > FIRMWARE UPDATE > Images tab.
B) Select CGR-Default profile from under the Groups panel and click the Upload Image button.
C) Click + to open the Upload Image panel and Select Type ACTD-CGR and select the appropriate Image from the drop-down menu such app-actd-ver-x.y.z.tar.
LoRaWAN Gateway Module
■![]() LoRaWAN (IXM-LPWA-800) interface to IR800 router.
LoRaWAN (IXM-LPWA-800) interface to IR800 router.
There are two ways to upload the LRR image for a LoRaWAN module to the IR800 router: during Zero Touch Deployment (ZTD) and by on-demand configuration push.
Note: IoT FND does not support discovery for the LoRaWAN module. Rather, IoT FND recognizes it as an IR800 module and will communicate with it via Cisco IOS.
■![]() To view LoRaWAN modules in a Device List, choose an IR800 router in the Browse Devices list and select the LoRaWAN tab.
To view LoRaWAN modules in a Device List, choose an IR800 router in the Browse Devices list and select the LoRaWAN tab.

■![]() To reboot the modem on the LoRaWAN module:
To reboot the modem on the LoRaWAN module:
a.![]() Click on the relevant IXM-LORA link under the Name column to display the information seen below:
Click on the relevant IXM-LORA link under the Name column to display the information seen below:

b.![]() Click Reboot Modem. When the reboot completes, the date and time display in the Last Reboot Time field in the Device Info pane for the LoRaWAN module. You can only process one modem reboot at a time.
Click Reboot Modem. When the reboot completes, the date and time display in the Last Reboot Time field in the Device Info pane for the LoRaWAN module. You can only process one modem reboot at a time.
The Reboot Modem action generates two events: LoRa Modem Reboot Initiated and LoRa Modem Reboot Success.
■![]() To remove a LoRaWAN module from the IR800 router inventory:
To remove a LoRaWAN module from the IR800 router inventory:
a.![]() In the Browse Devices pane, select the IR800, which has the LoRAWAN module that needs to be disabled and removed from inventory.
In the Browse Devices pane, select the IR800, which has the LoRAWAN module that needs to be disabled and removed from inventory.
b.![]() Select the LoRaWAN tab and check the box next to the LoRaWAN module to be removed.
Select the LoRaWAN tab and check the box next to the LoRaWAN module to be removed.

There are two ways to upload the LRR image for a LoRaWAN module to the IR800 router: during zero touch deployment (ZTD) and by on-demand configuration push.
Note: We do not support discovery for the LoRaWAN module. Rather, IoT FND recognizes it as an IR800 module and will communicate with it via Cisco IOS.
■![]() To view LoRaWAN modules in a Device List, choose an IR800 router in the Browse Devices list and select the LoRaWAN tab.
To view LoRaWAN modules in a Device List, choose an IR800 router in the Browse Devices list and select the LoRaWAN tab.
■![]() To reboot the modem on the LoRaWAN module:
To reboot the modem on the LoRaWAN module:
a.![]() Click on the relevant IXM-LORA link under the Name column to display the information seen below:
Click on the relevant IXM-LORA link under the Name column to display the information seen below:

b.![]() Click Reboot Modem. When the reboot completes, the date and time display in the Last Reboot Time field in the Device Info pane for the LoRaWAN module. You can only process one modem reboot at a time.
Click Reboot Modem. When the reboot completes, the date and time display in the Last Reboot Time field in the Device Info pane for the LoRaWAN module. You can only process one modem reboot at a time.
The Reboot Modem action generates two events: LoRa Modem Reboot Initiated and LoRa Modem Reboot Success.
■![]() To remove a LoRaWAN module from the IR800 router inventory:
To remove a LoRaWAN module from the IR800 router inventory:
a.![]() In the Browse Devices pane, select the IR800, which has the LoRAWAN module that needs to be disabled and removed from inventory.
In the Browse Devices pane, select the IR800, which has the LoRAWAN module that needs to be disabled and removed from inventory.
b.![]() Select the LoRaWAN tab and check the box next to the LoRaWAN module to be removed.
Select the LoRaWAN tab and check the box next to the LoRaWAN module to be removed.

c.![]() At the More Actions drop-down menu, select Remove Devices.
At the More Actions drop-down menu, select Remove Devices.
■![]() To create a user-defined LoRaWAN (IXM) Tunnel, choose CONFIG > Tunnel Provisioning.
To create a user-defined LoRaWAN (IXM) Tunnel, choose CONFIG > Tunnel Provisioning.
a.![]() In the left-pane, under GATEWAY, select the LoRaWAN system for which you want to configure a tunnel.
In the left-pane, under GATEWAY, select the LoRaWAN system for which you want to configure a tunnel.
b.![]() Select the Gateway Tunnel Addition tab.
Select the Gateway Tunnel Addition tab.
c.![]() In the Add Group window that appears, enter a Name for the LoRaWAN (IXM) Tunnel and select Gateway as the Device Category. Click Add. The new tunnel appears under the GATEWAY heading in the left-pane.
In the Add Group window that appears, enter a Name for the LoRaWAN (IXM) Tunnel and select Gateway as the Device Category. Click Add. The new tunnel appears under the GATEWAY heading in the left-pane.
Managing Servers
To manage servers, open the Servers page by choosing Devices > Servers. By default, the page displays the servers in List view. When you open the Servers page in List view, IoT FND displays the Default list view. This view displays basic server device properties. To obtain information about a server, click its name.
To add additional views, see Customizing Device Views.
For more information about the device properties displayed in each view, see Device Properties.
For information about the common actions in this view, see Common Device Operations.
Managing NMS and Database Servers
In the Browse Devices pane, both NMS and Database servers appear under the All Server Devices heading.
In single NMS or Database server deployments, only one server appears under the NMS and/or Database Servers heading. In cluster deployments, multiple NMS servers appear under the NMS Servers heading. To filter the list pane:
■![]() To display all NMS servers, click Devices > Servers in the top-level menu and then select NMS Servers within the Browse Devices pane. In single NMS server deployments, only one server appears under the NMS Servers heading. In cluster deployments, multiple NMS servers appear under the NMS Servers heading.
To display all NMS servers, click Devices > Servers in the top-level menu and then select NMS Servers within the Browse Devices pane. In single NMS server deployments, only one server appears under the NMS Servers heading. In cluster deployments, multiple NMS servers appear under the NMS Servers heading.
■![]() To display all Database servers, click Devices > Servers in the top-level menu and then select Database Servers within the Browse Devices pane. In single-server deployments, only one database server appears under Database Servers. If a secondary database is configured, it also appears under the same entry.
To display all Database servers, click Devices > Servers in the top-level menu and then select Database Servers within the Browse Devices pane. In single-server deployments, only one database server appears under Database Servers. If a secondary database is configured, it also appears under the same entry.
■![]() By default, only those NMS and Database Servers in an Up state display.
By default, only those NMS and Database Servers in an Up state display.
Tracking Assets
Assets represent non-Cisco equipment that is associated with an FND-managed Cisco device.
You can view Assets associated with specific routers (DEVICES > Field Devices) at the Device Detail pages of CGR1000, IR800, C800, and SBR (Cisco 5921).
You can view a summary of all assets being tracked for all devices at the DEVICES > Assets page.
You can perform the following actions on Assets at the DEVICES > Assets page, using Bulk Import:
■![]() Add Assets: Use to upload a CSV file of assets to FND. A history of past file uploads displays at the bottom of the page.
Add Assets: Use to upload a CSV file of assets to FND. A history of past file uploads displays at the bottom of the page.
Example of Asset content in CSV file:
Note: Asset Name and Asset Type are the mandatory fields in the CSV file. All other fields are optional.
■![]() Change Asset Property (CSV file): Use to make changes to existing assets.
Change Asset Property (CSV file): Use to make changes to existing assets.
■![]() Remove Assets (CSV file): Use to remove specific assets.
Remove Assets (CSV file): Use to remove specific assets.
■![]() Add Files to Assets (zip/tar file): Use to append additional information to Asset content.
Add Files to Assets (zip/tar file): Use to append additional information to Asset content.
Guidelines for Adding or Associating an Asset with a Device:
■![]() One or more assets can be mapped to a particular device.
One or more assets can be mapped to a particular device.
■![]() A limit of five assets can be associated to a single device; and there is also a limit of five files per asset.
A limit of five assets can be associated to a single device; and there is also a limit of five files per asset.
■![]() An asset can be mapped to only one device at any point in time.
An asset can be mapped to only one device at any point in time.
■![]() The mapped assets can also be useful when creating Work orders for the device.
The mapped assets can also be useful when creating Work orders for the device.
Common Device Operations
This section describes how to use IoT FND to manage and view information about devices, and includes the following topics:
■![]() Changing the Sorting Order of Devices
Changing the Sorting Order of Devices
■![]() Displaying Detailed Device Information
Displaying Detailed Device Information
■![]() Using Filters to Control the Display of Devices
Using Filters to Control the Display of Devices
■![]() Performing Bulk Import Actions
Performing Bulk Import Actions
Selecting Devices
In List view, IoT FND lets you select devices on a single page and across pages. When you select devices, a yellow bar displays that maintains a count of selected devices and has the Clear Selection and Select All commands. The maximum number of devices you can select is 1000. Perform the following to select devices:
■![]() To select all devices listed on a page, check the check box next to Name.
To select all devices listed on a page, check the check box next to Name.
■![]() To select devices across all pages, click Select All.
To select devices across all pages, click Select All.
■![]() To select a group of devices, check the check boxes of individual devices listed on a page and across pages. The count increments with every device selected, and selections on all pages are retained.
To select a group of devices, check the check boxes of individual devices listed on a page and across pages. The count increments with every device selected, and selections on all pages are retained.
Customizing Device Views
IoT FND lets you customize device views. For List views you can:
■![]() Specify the properties to display in the columns for each view (see Device Properties by Category for available properties)
Specify the properties to display in the columns for each view (see Device Properties by Category for available properties)
Adding Device Views
To add a custom device view tab to a device page in list view:

2.![]() In the Add New View dialog box, enter the name of the new tab.
In the Add New View dialog box, enter the name of the new tab.

3.![]() Add properties to the Active Columns list by selecting them from the Available Columns list, and then clicking the left arrow button, or dragging them into the Active Columns list.
Add properties to the Active Columns list by selecting them from the Available Columns list, and then clicking the left arrow button, or dragging them into the Active Columns list.
Editing Device Views
1.![]() Select a device type under the Browse Devices pane, and click the Default drop-down arrow to open the Edit/Delete View.
Select a device type under the Browse Devices pane, and click the Default drop-down arrow to open the Edit/Delete View.
2.![]() In the Edit/Delete View dialog box:
In the Edit/Delete View dialog box:
a.![]() To remove properties from the Active Columns list, select those properties and click the right-arrow button or drag them out of the Active Columns list.
To remove properties from the Active Columns list, select those properties and click the right-arrow button or drag them out of the Active Columns list.
b.![]() To add properties to the Active Columns list, select those properties from the Available Columns list and click the left-arrow button, or drag them into position in the Active Columns list.
To add properties to the Active Columns list, select those properties from the Available Columns list and click the left-arrow button, or drag them into position in the Active Columns list.
c.![]() To change the sort order of the active columns, use the up- and down-arrow buttons, or drag them to the desired position.
To change the sort order of the active columns, use the up- and down-arrow buttons, or drag them to the desired position.
To close the View without making any changes, select x icon. ==

Deleting a Device View
1.![]() Select a device type under the Browse Devices pane, and click the Default drop-down arrow to open the Edit/Delete View.
Select a device type under the Browse Devices pane, and click the Default drop-down arrow to open the Edit/Delete View.
2.![]() In the Edit/Delete View dialog box, select the desired label in the Active Columns pane.
In the Edit/Delete View dialog box, select the desired label in the Active Columns pane.
Viewing Devices in Map View
IoT FND provides a map view for visualizing device information based on geographic location. In Map view, IoT FND displays a Geographic Information System (GIS) map and uses GIS Map services to show device icons on the map based on the latitude and longitude information of the device. When this information is not defined for a device, IoT FND does not display the device on the map.
1.![]() Choose <user> > Preferences (upper-right hand corner).
Choose <user> > Preferences (upper-right hand corner).
2.![]() Select the Enable map check box, and click Apply.
Select the Enable map check box, and click Apply.

3.![]() Choose DEVICES > Field Devices.
Choose DEVICES > Field Devices.
By default, IoT FND displays all devices registered in its database on the map. Depending on the zoom level of the map and the device count, individual device icons might not display. Instead, IoT FND displays device group icons.

To view individual devices, zoom in until the device icons appear. You can also click on a device to display a popup window that includes the Zoom In link to move the map display to the device level.
IoT FND displays the device count next to each device group or category in the Browse Devices pane (left pane).
| ■ |
| IoT FND changes the map region based on your selection and displays the devices found by the filter. For example, you can use the Routers > Up filter to display all routers that are up and running. You can also use saved custom filters in the Quick View pane (left pane) to filter the device view. For information about creating custom filters, see Creating a Quick View Filter. |
| ■ |

A popup window displays listing basic device or group information.
| ■ |
You can also ping the device, perform a trace route, and create a work order from this window.
5.![]() Close the Device popup window to view the RPL tree associated with the device. See Configuring RPL Tree Polling
Close the Device popup window to view the RPL tree associated with the device. See Configuring RPL Tree Polling
The RPL tree connection displays as blue or orange lines; where blue indicates that the link is down, and orange indicates that the link is up.
Configuring Map Settings
In Map view, IoT FND lets you configure these settings for maps:
■![]() Automatically zoom to devices
Automatically zoom to devices
■![]() Default map location (set to North America by default)
Default map location (set to North America by default)
1.![]() Choose DEVICES > Field Devices.
Choose DEVICES > Field Devices.
Changing the Sorting Order of Devices
To change the sorting order of devices, click the arrowhead icon in the column heading to list the entries in an ascending (upward pointing) or descending manner (downward pointing).
Exporting Device Information
IoT FND lets you export the device properties of the selected devices in List view. IoT FND exports only properties in the current view.
To export device information displayed in the current view, in List view:
1.![]() Select the devices to export by checking their corresponding check boxes.
Select the devices to export by checking their corresponding check boxes.
3.![]() Click Yes in the confirmation dialog box.
Click Yes in the confirmation dialog box.
IoT FND creates a CSV file, export.csv, containing the information that displays in the List view pane. By default, IoT FND saves this file to your default download directory. When a file with the same name exists, IoT FND adds a number to the default filename (for example, export-1.csv and export-2.csv).
The export.csv file consists of one header line defining the exported fields followed by one or more lines, each representing a device. Here is an example of an export of selected devices from the Field Devices page:
Pinging Devices
When troubleshooting device issues, ping registered devices to rule out network connectivity issues. If you can ping a device, it is accessible over the network.
To ping selected devices, in List view:
1.![]() Check the check boxes of the devices to ping.
Check the check boxes of the devices to ping.
Note: If the status of a device is Unheard, a ping gets no response.
2.![]() Click Ping button in heading above List view entries.
Click Ping button in heading above List view entries.
A window displays the ping results. If you check the check box for Auto Refresh, IoT FND pings the device at predefined intervals until you close the window. Click the Refresh button (far right) to ping the device at any time.
Tracing Routes to Devices
The Traceroute command lets you determine the route used to reach a device IP address.
Note: You cannot use the Traceroute command with the Itron OpenWay RIVA CAM module or the Itron OpenWay RIVA Electric devices and Itron OpenWay RIVA G-W (Gas-Water) devices.
To trace routes to selected devices, in List view:
1.![]() Check the check boxes of the devices to trace.
Check the check boxes of the devices to trace.
Note: You can only trace routes to devices registered with IoT FND. If the status of a device is Unheard, you cannot trace the route to it.
A window displays with the route-tracing results.

Expand the Result column to view complete route information.
Click the Refresh button to resend the Traceroute command. Check the Auto Refresh check box to resend the Traceroute command at predefined intervals until you close the window.
Managing Device Labels
You use labels to create logical groups of devices to facilitate locating devices and device management.
Managing Labels
You use the Label Management window to display all custom labels, label properties, and search for custom labels.
To manage labels, in the Browse Device pane on any devices page:
1.![]() Hover your mouse over LABELS and click the edit icon (
Hover your mouse over LABELS and click the edit icon ( ).
).

2.![]() Click Update to accept label property changes or Cancel to retain label properties.
Click Update to accept label property changes or Cancel to retain label properties.
Adding Labels
To add labels to selected devices, in List view:
1.![]() Check the check boxes of the devices to label.
Check the check boxes of the devices to label.

2.![]() Enter the name of the label or choose an existing label from the drop-down menu.
Enter the name of the label or choose an existing label from the drop-down menu.
Tip: You can add multiple labels to one device.
To add labels in bulk, see Adding Labels in Bulk.
Removing Labels
To remove labels from selected devices, in List view:
1.![]() Check the check boxes of the devices from which to remove the label.
Check the check boxes of the devices from which to remove the label.
2.![]() Choose Label > Remove Label.
Choose Label > Remove Label.
To remove labels in bulk, see Removing Labels in Bulk.
Removing Devices
Caution: When you remove routers, IoT FND returns all the leased IP addresses associated with these devices to the Cisco Network Registrar (CNR) server and removes the corresponding tunnels from the head-end routers.
To remove devices, in List view:
1.![]() Check the check boxes of the devices to remove.
Check the check boxes of the devices to remove.

Displaying Detailed Device Information
IoT FND keeps detailed information about every device in the system. To access detailed information about a device, click its name or EID.
■![]() Detailed Device Information Displayed
Detailed Device Information Displayed
■![]() Actions You Can Perform from the Detailed Device Information Page
Actions You Can Perform from the Detailed Device Information Page
Detailed Device Information Displayed
■![]() Head-end Router, Router, and Endpoint Information
Head-end Router, Router, and Endpoint Information
Note: IoT FND automatically refreshes the detailed device information without the need to reload the page.
Server Information
Select DEVICES > Servers and click the Name of the server to open a page to display the following information about the NMS servers.
|
|
|
|---|---|
Total amount of RAM memory (GB) available on the system and Memory Usage graph. |
|
Displays usage information during set and custom-defined intervals. |
|
Head-end Router, Router, and Endpoint Information
Select DEVICES > Field Devices and then select a device type (router, head-end router or endpoint) from the Browse Devices pane. Then, click on the Name of a specific system from the device list to see the available information (such as Device Info, Events, Config Properties, etc.) for that system type as shown in the screen shot below.
A detailed summary for each device is summarized in the table below.

|
|
|
|---|---|
| Displays detailed device information (see Device Properties). For routers and endpoints, IoT FND also displays charts (see Viewing Device Charts). |
|
| Displays information about events associated with the device. |
|
| Config Properties (routers, endpoints: meter-cgmesh, gateway-IR500, meter-cellular) |
Displays the configurable properties of a device (see Device Properties). You can configure these properties by importing a CSV file specifying the properties to configure and their new values, as described in Changing Device Configuration Properties. |
| Mesh Routing Tree (CGR1000, endpoints: gateway-IR500, meter-cgmesh, meter-OW Riva) |
Displays the mesh routing tree. For routers, the Mesh Routing Tree pane displays all the possible routers from the mesh endpoints to the router. For mesh endpoints, the Mesh Routing Tree pane displays the mesh route to the router. |
| Displays the type of mesh link traffic over time in bits per second. |
|
| Lists metrics and session data for the TCP raw sockets (see Table 29) |
|
| Lists inventory (configuration) details and metrics for the attached access point. |
|
| Lists the running configuration file for the attached access point. |
Actions You Can Perform from the Detailed Device Information Page

Depending on device type, the Detailed Device Information page lets you perform the actions summarized in the table below:
|
|
|
|---|---|
| Displays a popup window with a map location of the device. This is the equivalent of entering eid: Device_EID in the search field in Map View. |
|
| Sends a ping to the device to determine its network connectivity. See Pinging Devices |
|
| Traces the route to the device. See Tracing Routes to Devices |
|
| Instructs the device to send metrics to IoT FND. Note: IoT FND assigns historical values for metrics for each device. To access historical metric values, use the GetMetricHistory North Bound API call. |
|
| Synchronizes the configuration membership for this device. See Synchronizing Endpoint Membership |
|
| Click Sync Firmware Membership to synchronize the firmware membership for this device, and then click Yes to complete the process. |
|
| Blocks the mesh endpoint device. Caution: This is a disruptive operation. Note: You cannot use Block Mesh Device with the Itron OpenWay RIVA CAM module or the Itron OpenWay RIVA Electric devices and Itron OpenWay RIVA G-W (Gas-Water) devices. |
|
| Creates a work order. See Creating Work Orders |
Using Filters to Control the Display of Devices
Depending on your deployment, the number of devices managed by IoT FND can be very large (IoT FND supports up to 10 million devices). To facilitate locating and displaying devices in Map View and List view, IoT FND provides filters and lets you add customized filters. Filters are listed in the Browse Devices and Quick View tabs.
Browse Devices Filters
Built-in device filters display in the Browse Devices pane. These filters control the display of devices in List and Map views. For every filter entry, IoT FND provides a device count in parenthesis. IoT FND automatically updates the device count without having to reload the page. In the example in Built-in Filter to Search for Mesh Endpoints, the top-level Endpoints label is selected, which inserts the following built-in filter in the Search Devices field: deviceType:cgmesh firmwareGroup:default-cgmesh.
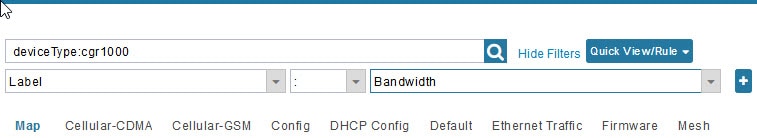
Figure 10 Built-in Filter to Search for Mesh Endpoints

Creating and Editing Quick View Filters
The Quick View pane displays custom filters. Click a filter in this pane to view the devices that fulfill the search criteria defined in the filter.
Creating a Quick View Filter
To create a Quick View filter:
1.![]() On any device page, click Show Filters and add filters to the Search field.
On any device page, click Show Filters and add filters to the Search field.
For more information about adding filters, see Adding a Filter.
2.![]() From the Quick View/Rule drop-down menu, choose Create Quick View.
From the Quick View/Rule drop-down menu, choose Create Quick View.
3.![]() In the Create Quick View dialog box that opens, enter a Name for the view.
In the Create Quick View dialog box that opens, enter a Name for the view.
4.![]() Click the disk icon to save the view. To close without saving, click the x.
Click the disk icon to save the view. To close without saving, click the x.
Editing a Quick View Filter
To edit or delete a Quick View filter:
1.![]() Click the Quick View tab and select the filter to edit.
Click the Quick View tab and select the filter to edit.
2.![]() From the Quick View/Rule drop-down menu, choose Edit Quick View.
From the Quick View/Rule drop-down menu, choose Edit Quick View.
3.![]() In the Update Quick View dialog box, make the necessary modifications, and then click Save.
In the Update Quick View dialog box, make the necessary modifications, and then click Save.
Adding a Filter
To add a filter to the Search field:
1.![]() If the Add Filter fields are not present under the Search field, click Show Filters.
If the Add Filter fields are not present under the Search field, click Show Filters.
2.![]() From the Label drop-down menu, choose a filter.
From the Label drop-down menu, choose a filter.
The drop-down menu defines filters for all device information categories. For more information about these categories, see Working with Router Views.
3.![]() From the Operator (:) drop-down menu, choose an operator.
From the Operator (:) drop-down menu, choose an operator.
For more information about operators, see Filter Operators. If you choose a numeric metric from the Label menu (for example, Transmit Speed), you can specify a range of values in the filter you are adding. For date/time filters, “between” is the operator. Use the calendar buttons to specify the date range for the filter.
4.![]() In the Value field, enter a value to match or a range of values in the case of numeric metrics or select an available value from the drop-down menu.
In the Value field, enter a value to match or a range of values in the case of numeric metrics or select an available value from the drop-down menu.
5.![]() Click the Add (+) button to add the filter to the existing filter syntax in the Search field.
Click the Add (+) button to add the filter to the existing filter syntax in the Search field.
6.![]() (Optional) Repeat the process to continue adding filters.
(Optional) Repeat the process to continue adding filters.
Filter Operators
Filter Operators describes the operators you can use to create filters.
|
|
|
|---|---|
Search Syntax
IoT FND supports this simple query language syntax:
Filter := fieldname operator value
operator := < | <= | > | >= | <> | = | :
Note the following when creating filters to search fields:
■![]() Each field has a data type (String, Number, Boolean, and Date).
Each field has a data type (String, Number, Boolean, and Date).
■![]() String fields can contain a string, and you can search them using string equality (“:”).
String fields can contain a string, and you can search them using string equality (“:”).
■![]() Numeric fields can contain a decimal number (stored as a double-precision float), and you can search them using the numeric comparison operators (“>”, “>=”, “<“, “<=”, “<>”).
Numeric fields can contain a decimal number (stored as a double-precision float), and you can search them using the numeric comparison operators (“>”, “>=”, “<“, “<=”, “<>”).
■![]() Boolean fields can contain the strings “true” or “false”.
Boolean fields can contain the strings “true” or “false”.
■![]() Date fields can contain a date in this format: yyyy-MM-dd HH:mm:ss:SSS. You can search dates using numeric comparison operators.
Date fields can contain a date in this format: yyyy-MM-dd HH:mm:ss:SSS. You can search dates using numeric comparison operators.
Filter Examples describes filter examples.
|
|
|
|---|---|
|
|
|
|
|
|
|
|
Finds all CGR 1000s in the Nevada group that are up and running. |
Performing Bulk Import Actions
In IoT FND, you can perform these bulk import device actions:
■![]() Adding Routers and Head-end Routers in Bulk
Adding Routers and Head-end Routers in Bulk
Adding Routers and Head-end Routers in Bulk
The Add Devices option in the Bulk Import drop-down menu lets you add routers and head-end routers to IoT Field Network Director in bulk using a CSV file.
1.![]() On any Device page, from the Bulk Import drop-down menu, choose Add Devices.
On any Device page, from the Bulk Import drop-down menu, choose Add Devices.

2.![]() In the Add Devices window, click Browse to locate the CSV file containing the device information to import, and then click Open.
In the Add Devices window, click Browse to locate the CSV file containing the device information to import, and then click Open.
For more information about adding HERs, see Adding HERs to IoT FND.
For more information about adding routers, see Adding Routers to IoT FND.
Note: For routers, you can also use the Notice-of-Shipment XML file provided by your Cisco partner to import routers.
Adding HERs to IoT FND
Configuring HERs Before Adding them to IoT FND
Before you can add an HER to IoT FND, configure the HER to allow management by IoT FND using Netconf over SSH as follows:
Where <her_hostname> is the hostname or IP address of the IoT FND server, and <domain.com> is the name of the domain name where the HER and IoT FND reside. The time-out value of 120 is required for large networks.
After configuring the HER to allow management by IoT FND, ensure that you can:
■![]() Ping the management interface of the HER.
Ping the management interface of the HER.
■![]() Access the management interface of the HER over SSH and vice versa.
Access the management interface of the HER over SSH and vice versa.
To add HERs, create a CSV file like the following example that consists of a header line followed by one or more lines, each representing an HER:
HER Import Fields describes the fields to include in the CSV file.
Note: For device configuration field descriptions, see Device Properties.
When you add an HER, IoT FND displays its status as Unheard. IoT FND changes the status to Up after it polls the HER. IoT FND polls HERs in the background every 15 minutes to collect device metrics, so it should take no more than 15 minutes for the status of HERs to change to Up after you add them to IoT FND. However, you can trigger the polling of HERs by clicking Refresh Metrics ( Refresh Metrics ).
Adding Routers to IoT FND
Typically, when adding routers to IoT FND, you use the Notice-of-Shipment XML file sent to you by your Cisco partner. This file contains an <R> record for every router shipped to you. This is an example of an <R> record for a CGR:
Note: For a list of all Device Properties that you can configure using the XML configuration template go to Device Properties.
Router Import Fields describes the router properties defined in the <R> record used in this example:
Mapping Routers to HERs
After you determine the Router-to-HER mapping, which is essential for tunnel provisioning, you can configure the mapping in IoT FND in one of two ways:
■![]() Adding the mapping information to every router record in the Notice-of-Shipment XML file.
Adding the mapping information to every router record in the Notice-of-Shipment XML file.
■![]() Creating a CSV file specifying the mapping of routers to HERs.
Creating a CSV file specifying the mapping of routers to HERs.
Adding Router-to-HER Mappings to the Notice-of-Shipment XML File
To map a router to an HER, add the tunnelHerEid and ipsecTunnelDestAddr1 HER properties to the router record in the Notice-of-Shipment XML file.
■![]() The tunnelHerEid property specifies the EID of the HER
The tunnelHerEid property specifies the EID of the HER
■![]() The ipsecTunnelDestAddr1 property specifies the tunnel IP address of the HER.
The ipsecTunnelDestAddr1 property specifies the tunnel IP address of the HER.
Adding Router-to-HER Mappings to a CSV File
To map routers to HERs using a CSV file, add a line for every router-to-HER mapping. The line must specify the EID of the router, the EID of the corresponding HER, and the tunnel IP address of the HER, as in this example for a CGR:
Removing Devices in Bulk
You can remove devices in bulk using a CSV file listing the EIDs of the devices to remove.
Caution: When you remove routers, IoT FND returns all the leased IP addresses associated with these devices to CNR and removes the corresponding tunnels from the HERs.
1.![]() Choose Devices > Device Type.
Choose Devices > Device Type.
2.![]() Choose Bulk Import > Remove Devices.
Choose Bulk Import > Remove Devices.

3.![]() Click Browse to locate the CSV file containing the devices to delete, and then click Choose.
Click Browse to locate the CSV file containing the devices to delete, and then click Choose.

This is an example of the CSV format expected. In this case, the CSV file specifies three CGRs and one HER:
The Status section of the Remove Devices window displays the status of the operation. The History section describes additional information about the operation. If there was any failure, click the corresponding link in the Failure# column to get more information about the error.
Changing Device Properties in Bulk
IoT FND lets you configure device properties in bulk using a CSV file. For example, this CSV file changes the latitude and longitude for the specified HER:
To configure device properties in bulk:
1.![]() On any device page, choose Bulk Import > Change Device Properties.
On any device page, choose Bulk Import > Change Device Properties.

2.![]() Click Browse to locate the CSV containing the list of devices and corresponding properties to configure, and then click Open.
Click Browse to locate the CSV containing the list of devices and corresponding properties to configure, and then click Open.
Adding Labels in Bulk
You can group devices logically by assigning them labels. Labels are independent of device type, and devices of any type can belong to any label. A device can also have multiple labels. Unlike configuration groups and firmware groups, there are no policies or metadata associated with labels.
IoT FND lets you add labels in bulk using a CSV file. In the CSV file, specify the list of devices to be labeled.
1.![]() On any device page, choose Bulk Import > Add Label.
On any device page, choose Bulk Import > Add Label.
2.![]() Click Browse to locate the CSV file that contains the list of devices to label, and then click Open.
Click Browse to locate the CSV file that contains the list of devices to label, and then click Open.
This is an example of the expected CSV format:
3.![]() In the Label field, enter the label or choose one from the drop-down menu.
In the Label field, enter the label or choose one from the drop-down menu.
The label appears in the Browse Devices tab (left pane) under LABELS.
Removing Labels in Bulk
IoT FND lets you delete labels in bulk using a CSV file.
1.![]() On any device page, choose Bulk Import > Remove Label.
On any device page, choose Bulk Import > Remove Label.
2.![]() Click Browse to locate the CSV containing the list of devices to remove the label from, and then click Open.
Click Browse to locate the CSV containing the list of devices to remove the label from, and then click Open.
Configuring Rules
A IoT FND rule defines a filter and actions that IoT FND performs after an event or after it receives metrics that match the search criteria defined in the filter. Rules can check for event conditions and metric thresholds.
For example, whenever the status of a router in a configuration group changes to Up, you can add a custom message to the server log (server.log) and add the appropriate labels to the device. This helps you automate the process of adding labels to devices.
When working with rules, you can do the following:
■![]() Add rules with conditions and actions.
Add rules with conditions and actions.
■![]() Define a rule with a condition using a device search query, which matches devices according to properties and metrics.
Define a rule with a condition using a device search query, which matches devices according to properties and metrics.
■![]() Define a rule with an action that adds labels to matching devices or to the devices that sent a matching event.
Define a rule with an action that adds labels to matching devices or to the devices that sent a matching event.
■![]() Define a rule with an action that removes a label from a matching device or the device that sent a matching event.
Define a rule with an action that removes a label from a matching device or the device that sent a matching event.
■![]() Define a rule with an action that places a user alert event into the log, which includes a user-defined message.
Define a rule with an action that places a user alert event into the log, which includes a user-defined message.
Viewing and Editing Rules
IoT FND displays the list of rules stored in its database. Rule Fields describes the fields displayed in the list.
2.![]() To edit a rule, click its name.
To edit a rule, click its name.
For information on how to edit rules, see Creating a Rule.
Creating a Rule
Note: If you enter invalid characters (for example, “=”, “+”, and “~”), IoT FND displays a red alert icon, highlights the field in red, and disables the OK![]() button.
button.
4.![]() To activate the rule, check the Active check box.
To activate the rule, check the Active check box.
5.![]() In the Construct Rule panel, enter the syntax of the rule.
In the Construct Rule panel, enter the syntax of the rule.
Use the same syntax used for creating filters. See Search Syntax.

6.![]() In the Create Rule panel, check the check box of at least one action:
In the Create Rule panel, check the check box of at least one action:
| ■ – – For example, if you enter Red Alert in this field, set the Severity to CRITICAL and enter CHECK ROUTER in the Event Name field, the eventMessage field in the logged entry for the event that matches the rule is set to Red Alert, as shown in this sample entry from the server log (server.log): |
| In IoT FND, the message you define in the Log event with field appears in the Message field of the matching event entries listed on the Events page (Operations > Events), and the new Event Name is a new search filter. |
| ■ |
| ■ |
| ■ |
Activating Rules
IoT FND only applies rules that you activate.
2.![]() Check the check boxes of the rules to activate.
Check the check boxes of the rules to activate.
Deactivating Rules
If you deactivate a rule, IoT FND does not apply it.
2.![]() Check the check boxes of the rules to deactivate.
Check the check boxes of the rules to deactivate.
Deleting Rules
2.![]() Check the check boxes of the rules to delete.
Check the check boxes of the rules to delete.
Configuring Devices
This section describes how to configure devices in IoT FND, including:
■![]() Configuring Device Group Settings
Configuring Device Group Settings
■![]() Editing the ROUTER Configuration Template
Editing the ROUTER Configuration Template
■![]() Editing the ENDPOINT Configuration Template
Editing the ENDPOINT Configuration Template
■![]() Pushing Configurations to Routers
Pushing Configurations to Routers
■![]() Pushing Configurations to Endpoints
Pushing Configurations to Endpoints
Configuring Device Group Settings
IoT FND uses groups to manage devices in bulk. When you add routers to IoT Field Network Director, IoT FND automatically adds them to the appropriate default ROUTER configuration groups, for example, default-cgr1000. When you add MEs (meters and range extenders), IoT FND adds them to the default ENDPOINT configuration group, default-cgmesh.
■![]() Changing Device Configuration Properties
Changing Device Configuration Properties
■![]() Moving Devices to Another Group
Moving Devices to Another Group
■![]() Listing Devices in a Configuration Group
Listing Devices in a Configuration Group
■![]() Configuring Periodic Inventory Notification and Mark-Down Time
Configuring Periodic Inventory Notification and Mark-Down Time
Creating Device Groups
By default, IoT FND defines the following device groups listed on the CONFIG > Device Configuration page left tree as follows:
Each default group defines a default configuration template that you can push to all devices in that group. However, if you need to apply a different template to a group of devices, create a new group and modify its default configuration template as needed.
Note: You cannot delete the default groups, but you can change their names, although we do not recommend it. Also, the default ROUTER and ENDPOINT groups use the same icon, while custom groups use a different icon. See IoT FND Icons for icon definitions.
Creating ROUTER Groups
Note: CGRs, IR800s, C800s and C5921s (SBR) can coexist on a network; however, you must create custom templates that includes all router types.
To create a ROUTER configuration group:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Select the default Configuration Group: Default-cgr1000, Default-ir800., Default-c800 or Default-sbr.
Select the default Configuration Group: Default-cgr1000, Default-ir800., Default-c800 or Default-sbr.
3.![]() With the Groups tab selected (top, left panel of page), click the + icon (under the heading) to open the Add Group entry panel.
With the Groups tab selected (top, left panel of page), click the + icon (under the heading) to open the Add Group entry panel.

4.![]() Enter the name of the group. The Device Category auto-fills router by default.
Enter the name of the group. The Device Category auto-fills router by default.
Note: If you enter invalid characters (for example, “=”, “+”, and “~”), IoT FND displays a red alert icon, highlights the field in red, and disables the Add![]() button.
button.
The new group entry appears in the ROUTER list (left pane).
■![]() To change the name of a group, see Renaming a Device Configuration Group.
To change the name of a group, see Renaming a Device Configuration Group.
■![]() To remove a group, see Deleting Device Groups.
To remove a group, see Deleting Device Groups.
Creating Endpoint Groups
To create an Endpoint configuration group:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Select the default group (Default-act, Default-bact, Default-cam, Default-cgmesh, Default-ir500)
Select the default group (Default-act, Default-bact, Default-cam, Default-cgmesh, Default-ir500)
3.![]() With the Groups tab selected (top, left panel of page), click the + icon (under the heading) to open the Add Group entry panel. Note : The device category (such as endpoint or router) auto-populates.
With the Groups tab selected (top, left panel of page), click the + icon (under the heading) to open the Add Group entry panel. Note : The device category (such as endpoint or router) auto-populates.
4.![]() Enter a name for the group. The device category (endpoint, gateway or router) auto-populates.
Enter a name for the group. The device category (endpoint, gateway or router) auto-populates.

Note: If you enter invalid characters (for example, “=”, “+”, and “~”), IoT FND displays a red alert icon, highlights the field in red, and disables the OK![]() button.
button.
The new group entry appears in the appropriate device category list (left pane).
■![]() To change the name of a group, see Renaming a Device Configuration Group.
To change the name of a group, see Renaming a Device Configuration Group.
■![]() To remove a group, see Deleting Device Groups.
To remove a group, see Deleting Device Groups.
Changing Device Configuration Properties
You can change the configurable properties of devices by uploading a Device Properties CSV file with modified values for the devices.
To change device configuration properties:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Click Change Device Properties.
Click Change Device Properties.

3.![]() Click Browse and select the Device Properties CSV or XML file to upload.
Click Browse and select the Device Properties CSV or XML file to upload.
■![]() For a list of configurable device properties in IoT FND, see Device Properties.
For a list of configurable device properties in IoT FND, see Device Properties.
Moving Devices to Another Group
There are two ways to move devices from one configuration group to another:
Moving Devices to Another Configuration Group Manually
To move devices to another configuration group:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Select a group from the list of configuration groups (left pane).
Select a group from the list of configuration groups (left pane).
3.![]() Select the check box of the devices to move.
Select the check box of the devices to move.
4.![]() Click Change Configuration Group.
Click Change Configuration Group.

5.![]() From the drop-down menu in the dialog box, choose the target group for the devices.
From the drop-down menu in the dialog box, choose the target group for the devices.
Moving Devices to Another Configuration Group in Bulk
To move a large number of devices from one group to another, you can import a CSV file containing the list of the devices to move.
For example, this CSV file specifies the EIDs of three CGRs to move:
To move devices to another configuration group in bulk:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Click Assign Devices to Group.
Click Assign Devices to Group.

3.![]() Click Browse to locate the CSV or XML file containing the list of devices to move, and then click Open.
Click Browse to locate the CSV or XML file containing the list of devices to move, and then click Open.
4.![]() From the Group drop-down menu, choose the target group for the devices.
From the Group drop-down menu, choose the target group for the devices.
Listing Devices in a Configuration Group
To list the devices in a configuration group:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Select a group from the list of configuration groups (left pane).
Select a group from the list of configuration groups (left pane).
3.![]() To get more information about a device in the list, click its EID (for example: CGR1240/K9+JAF1723AHGD).
To get more information about a device in the list, click its EID (for example: CGR1240/K9+JAF1723AHGD).
Configuring Periodic Inventory Notification and Mark-Down Time
You can change the periodic inventory notification interval for a configuration group of routers without affecting the logic that IoT FND uses to mark those routers as Down. However, for this to happen, you must enable the periodic configuration notification frequency for the router group so that it is less than the mark-down timer.
You can configure the mark-down timer by clicking the Group Properties tab for the group and modifying the value of the Mark Routers Down After field.
Configuring Periodic Inventory Notification
To configure the periodic inventory notification interval for a ROUTER configuration group:
1.![]() Click CONFIG > Device Configuration.
Click CONFIG > Device Configuration.
2.![]() Select a ROUTER configuration group.
Select a ROUTER configuration group.
3.![]() Click Edit Configuration Template.
Click Edit Configuration Template.
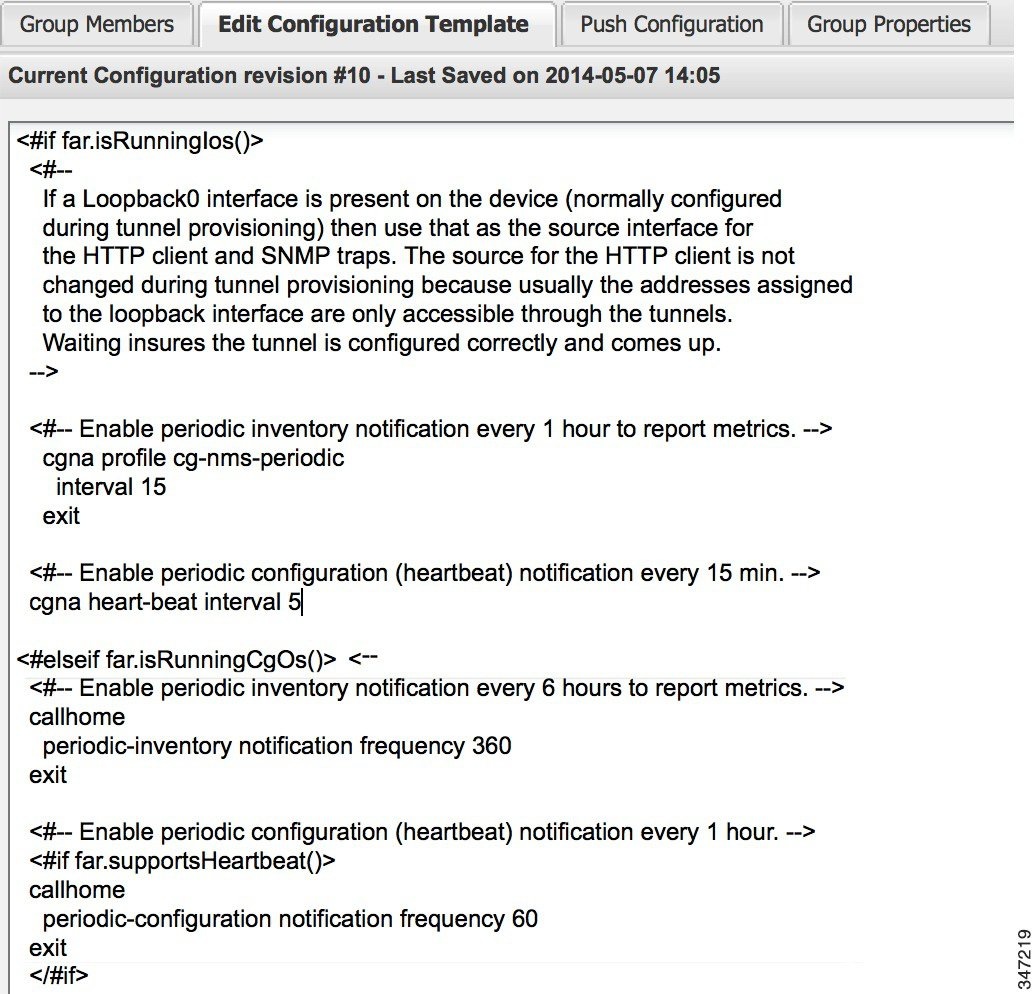
Configuring the Mark-Down Timer
To configure the mark-down timer for a ROUTER configuration group:
1.![]() Click CONFIG > Device Configuration.
Click CONFIG > Device Configuration.
2.![]() Select a ROUTER configuration group.
Select a ROUTER configuration group.

4.![]() In the Mark Routers Down After field, enter the number of seconds after which IoT FND marks the routers as down if they do not send periodic configuration notifications (heartbeats) to IoT FND during that time.
In the Mark Routers Down After field, enter the number of seconds after which IoT FND marks the routers as down if they do not send periodic configuration notifications (heartbeats) to IoT FND during that time.
Note: We recommend a 1:3 ratio of heartbeat interval to mark-down timer.
5.![]() Click the disk icon to save changes.
Click the disk icon to save changes.
6.![]() Ensure that the periodic-configuration notification frequency in the configuration template is less than the value you entered the Mark Routers Down After field:
Ensure that the periodic-configuration notification frequency in the configuration template is less than the value you entered the Mark Routers Down After field:
a.![]() Click Edit Configuration Template.
Click Edit Configuration Template.
b.![]() Ensure that the value of the periodic-configuration notification frequency parameter is less than the Mark Routers Down After value.
Ensure that the value of the periodic-configuration notification frequency parameter is less than the Mark Routers Down After value.
Use a notification value that is at most one-third of the mark-down value. For example, if you choose a mark-down value of 3600 seconds (60 minutes), set the periodic-configuration notification frequency parameter to 20 minutes:
Note: The ability to control the periodic inventory notification interval and the periodic-configuration notification frequency applies to CGR image version 3.2.
Renaming a Device Configuration Group
To rename a device configuration group:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Select a group from the list of configuration groups (left pane).
Select a group from the list of configuration groups (left pane).
3.![]() Hover over the name of the group in the list. A pencil icon appears.
Hover over the name of the group in the list. A pencil icon appears.
4.![]() Click on the pencil icon to open the Edit Group panel.
Click on the pencil icon to open the Edit Group panel.

5.![]() Enter the new name in the Rename Group dialog box, and then click OK.
Enter the new name in the Rename Group dialog box, and then click OK.
Note: If you enter invalid characters (for example, “=”, “+”, and “~”), IoT FND displays a red alert icon, highlights the field in red, and disables the OK![]() button.
button.
Deleting Device Groups
Note: Before deleting a group, move all devices in that group to another group. You cannot delete a non-empty group.
To delete a configuration group:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Select a group from the list of configuration groups (left pane).
Select a group from the list of configuration groups (left pane).
3.![]() Ensure that the group is empty.
Ensure that the group is empty.
The Delete icon displays as a red minus sign when you hover over the name of the group in the list.
Synchronizing Endpoint Membership
Endpoints maintain information about the IoT FND group to which they belong. If the group information changes, the endpoint becomes out of sync. For example, if you rename an endpoint group, the members of the group might not be modified immediately (for example, due to a packet loss). If a device is out of sync, any operation you perform on the group through IoT FND does not reach the device. To ensure that the endpoints remain in sync, use the Sync Membership button to push the group information to group members.
Note: Devices sync for the first time after they register with IoT FND.
To send group information to endpoints:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Select an ENDPOINT group (left pane).
Select an ENDPOINT group (left pane).
3.![]() In the Group Members pane, click on the name of an endpoint.
In the Group Members pane, click on the name of an endpoint.
4.![]() Click Sync Config Membership button on the page that appears.
Click Sync Config Membership button on the page that appears.
Editing the ROUTER Configuration Template
IoT FND lets you configure routers in bulk using a configuration template. When a router registers with IoT FND, IoT Field Network Director pushes the configuration defined in the default template to the device and commits the changes to the router startup configuration. IoT FND then retrieves the running configuration from the router before changing the device status to Up.
To edit a ROUTER group configuration template:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Under CONFIGURATION GROUPS (left pane), select the group with the template to edit.
Under CONFIGURATION GROUPS (left pane), select the group with the template to edit.
3.![]() Click Edit Configuration Template.
Click Edit Configuration Template.
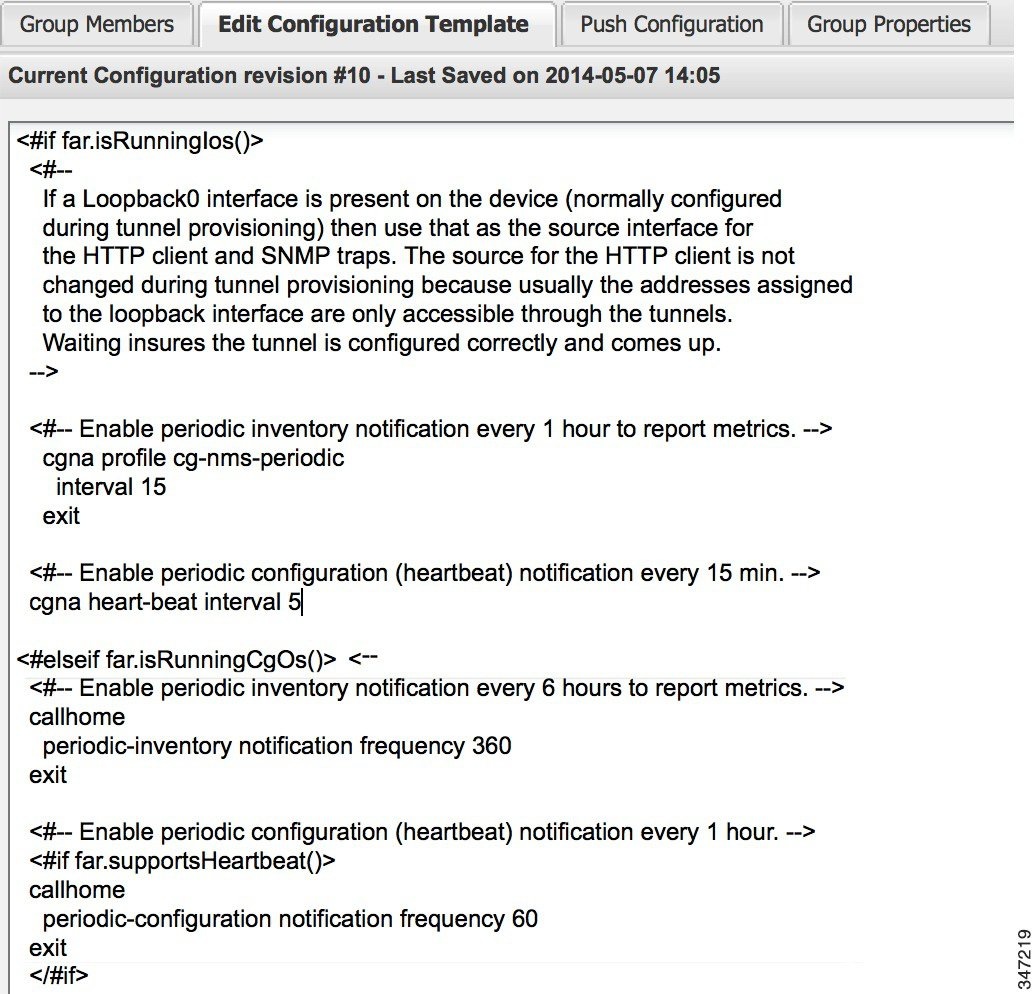
The template is expressed in FreeMarker syntax.
Note: The router configuration template does not validate the configuration data entered. Verify the configuration before saving.
IoT FND commits the changes to the database and increases the template version number.
Editing the AP Configuration Template
IoT FND lets you configure APs in bulk using a configuration template. When the AP registers with IoT FND, it pushes the configuration defined in the default template to devices and commits the changes to the startup configuration. IoT FND then retrieves the running configuration from the AP before changing the device status to Up.
To edit a AP group configuration template:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Under CONFIGURATION GROUPS (left pane), select the C800 device group with embedded AP devices with the template to edit.
Under CONFIGURATION GROUPS (left pane), select the C800 device group with embedded AP devices with the template to edit.
3.![]() Click Edit AP Configuration Template.
Click Edit AP Configuration Template.
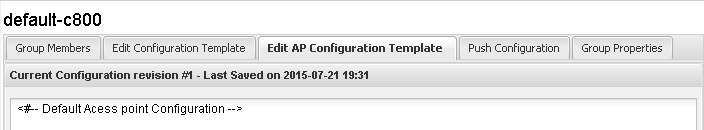
The template is expressed in FreeMarker syntax. For more information about FreeMarker.
Note: The AP configuration template does not validate the configuration data entered. Verify the configuration before saving.
IoT FND commits the changes to the database and increases the template revision number.
Enabling Dual PHY Support on IoT FND
You can configure CGR master and slave interfaces. For more information about configuring a dual-PHY WPAN interface, refer to Cisco Connected Grid WPAN Module for CGR 1000 Series Installation and CG-Mesh Configuration Guide (Cisco IOS).
Configuring IoT FND for Dual-PHY
For Dual-PHY CGRs, you must configure all Dual-PHY WPAN modules–master and slaves–by setting the Dual-PHY WPAN Properties (see Mesh Link Config Fields). The parameters to set in the appropriate device addition file are masterWpanInterface and slaveWpanInterface. For slave Dual-PHY WPAN devices, you must also set the slave-mode parameter.
The following is a typical template for configuring the master/slave interface on CGR WPAN modules:
Mesh Security Keys for Dual-PHY Devices
Note: Do not configure mesh security keys on slave WPAN devices.
With master/slave mode configured correctly in IoT FND, IoT FND automatically detects the master WPAN and sets its the mesh security keys. When configuring an existing CGR and adding another WPAN interface, remove all mesh security keys from both interfaces, and then configure master/slave mode through IoT FND. If CGRs are connected, all meters go through re-authentication.
You can remove mesh keys using the command:
Configuration Details for WPAN Devices
The following examples retrieve the current Dual-PHY WPAN device RPL slot tree, RPL slot table, RPL IP route info table, and configuration information for slots 4/1 and 3/1.
// SY RF nodes
NODE_IPADDR RANK VERSION NEXTHOP_IP ETX_P ETX_LRSSIR RSSIF HOPS PARENTS SSLOT
2001:RTE:RTE:64:207:8108:3C:1800 835 1 2001:RTE:RTE:64::4 0 762 -67 -71 1 1 3
// SY RF nodes
2001:RTE:RTE:64:207:8108:3C:1801 692 2 2001:RTE:RTE:64::4 0 547 -68 -67 1 1 3
2001:RTE:RTE:64:207:8108:3C:1802 776 2 2001:RTE:RTE:64::4 0 711 -82 -83 1 1 3
2001:RTE:RTE:64:207:8108:3C:1803 968 2 2001:RTE:RTE:64::4 0 968 -72 -63 1 1 3
2001:RTE:RTE:64:207:8108:3C:1804 699 1 2001:RTE:RTE:64::4 0 643 -71 -66 1 1 3
2001:RTE:RTE:64:207:8108:3C:1805 681 1 2001:RTE:RTE:64::4 0 627 -70 -64 1 1 3
2001:RTE:RTE:64:207:8108:3C:1806 744 1 2001:RTE:RTE:64::4 0 683 -69 -68 1 1 3
2001:RTE:RTE:64:207:8108:3C:1807 705 1 2001:RTE:RTE:64::4 0 648 -76 -63 1 1 3
2001:RTE:RTE:64:207:8108:3C:1808 811 2 2001:RTE:RTE:64::4 0 811 -68 -69 1 2 3
2001:RTE:RTE:64:207:8108:3C:1809 730 1 2001:RTE:RTE:64::4 0 692 -68 -70 1 1 3
2001:RTE:RTE:64:207:8108:3C:180A 926 1 2001:RTE:RTE:64::4 0 926 -66 -68 1 1 3
2001:RTE:RTE:64:207:8108:3C:180B 602 2 2001:RTE:RTE:64::4 0 314 -74 -69 1 1 3
2001:RTE:RTE:64:207:8108:3C:1A00 948 1 2001:RTE:RTE:64:207:8108:3C:1801 692 256 -73 -75 2 1 3
2001:RTE:RTE:64:207:8108:3C:1A01 646 2 2001:RTE:RTE:64:207:8108:3C:180B 323 256 -73 -75 2 3 3
2001:RTE:RTE:64:207:8108:3C:1A02 948 1 2001:RTE:RTE:64:207:8108:3C:180B 602 256 -73 -75 2 2 3
2001:RTE:RTE:64:207:8108:3C:1A03 803 2 2001:RTE:RTE:64:207:8108:3C:1805 503 256 -68 -78 2 3 3
2001:RTE:RTE:64:207:8108:3C:1A04 858 1 2001:RTE:RTE:64:207:8108:3C:180B 602 256 -65 -69 2 1 3
2001:RTE:RTE:64:207:8108:3C:1A05 646 2 2001:RTE:RTE:64:207:8108:3C:180B 323 256 -71 -69 2 2 3
2001:RTE:RTE:64:207:8108:3C:1A06 858 1 2001:RTE:RTE:64:207:8108:3C:180B 602 256 -73 -75 2 2 3
2001:RTE:RTE:64:207:8108:3C:1A07 979 1 2001:RTE:RTE:64:207:8108:3C:1805 627 352 -71 -73 2 1 3
2001:RTE:RTE:64:207:8108:3C:1A08 646 2 2001:RTE:RTE:64:207:8108:3C:180B 390 256 -75 -70 2 3 3
2001:RTE:RTE:64:207:8108:3C:1A09 948 1 2001:RTE:RTE:64:207:8108:3C:180B 602 256 -70 -69 2 3 3
2001:RTE:RTE:64:207:8108:3C:1A0A 646 2 2001:RTE:RTE:64:207:8108:3C:180B 390 256 -75 -71 2 2 3
2001:RTE:RTE:64:207:8108:3C:1A0B 858 1 2001:RTE:RTE:64:207:8108:3C:180B 602 256 -68 -68 2 2 3
2001:RTE:RTE:64:207:8108:3C:1C00 902 2 2001:RTE:RTE:64:207:8108:3C:1A0A 646 256 -70 -74 3 1 3
2001:RTE:RTE:64:207:8108:3C:1C01 902 2 2001:RTE:RTE:64:207:8108:3C:1A0A 646 256 -71 -72 3 1 3
2001:RTE:RTE:64:207:8108:3C:1C02 1114 1 2001:RTE:RTE:64:207:8108:3C:1A06 858 256 -74 -73 3 1 3
2001:RTE:RTE:64:207:8108:3C:1C03 1114 1 2001:RTE:RTE:64:207:8108:3C:1A05 858 256 -76 -77 3 1 3
2001:RTE:RTE:64:207:8108:3C:1C04 902 2 2001:RTE:RTE:64:207:8108:3C:1A06 646 256 -75 -68 3 2 3
2001:RTE:RTE:64:207:8108:3C:1C05 1114 1 2001:RTE:RTE:64:207:8108:3C:1A01 858 256 -66 -74 3 1 3
2001:RTE:RTE:64:207:8108:3C:1C06 1114 1 2001:RTE:RTE:64:207:8108:3C:1A01 858 256 -74 -72 3 1 3
2001:RTE:RTE:64:207:8108:3C:1C07 1114 1 2001:RTE:RTE:64:207:8108:3C:1A01 858 256 -70 -75 3 1 3
2001:RTE:RTE:64:207:8108:3C:1C08 1114 1 2001:RTE:RTE:64:207:8108:3C:1A05 858 256 -74 -70 3 1 3
2001:RTE:RTE:64:207:8108:3C:1C09 1114 1 2001:RTE:RTE:64:207:8108:3C:1A05 858 256 -70 -74 3 1 3
2001:RTE:RTE:64:207:8108:3C:1C0A 1114 1 2001:RTE:RTE:64:207:8108:3C:1A05 858 256 -70 -69 3 1 3
2001:RTE:RTE:64:207:8108:3C:1C0B 902 2 2001:RTE:RTE:64:207:8108:3C:1A0A 646 256 -76 -74 3 1 3
2001:RTE:RTE:64:217:3BCD:26:4E00 616 2 2001:RTE:RTE:64::4 0 616 118 118 1 1 4 // CY PLC nodes
2001:RTE:RTE:64:217:3BCD:26:4E01 702 1 2001:RTE:RTE:64::4 0 646 118 118 1 1 4
2001:RTE:RTE:64:217:3BCD:26:4E02 557 2 2001:RTE:RTE:64::4 0 557 118 118 1 1 4
2001:RTE:RTE:64:217:3BCD:26:4E03 626 1 2001:RTE:RTE:64::4 0 579 118 118 1 1 4
2001:RTE:RTE:64:217:3BCD:26:4E04 609 2 2001:RTE:RTE:64::4 0 609 118 118 1 1 4
2001:RTE:RTE:64:217:3BCD:26:4E05 602 2 2001:RTE:RTE:64::4 0 602 118 118 1 1 4
2001:RTE:RTE:64:217:3BCD:26:4E06 594 2 2001:RTE:RTE:64::4 0 594 118 118 1 1 4
2001:RTE:RTE:64:217:3BCD:26:4E07 584 2 2001:RTE:RTE:64::4 0 584 118 118 1 1 4
Enabling Router GPS Tracking
You can enable GPS traps to trigger an event if the router moves a distance threshold, after a time threshold, or both. For example, you can configure stationary, pole-top CGR monitoring for a distance threshold, to detect movement from theft or pole incident; for mobile routers, set both thresholds to determine distance over time. The recommended distance threshold is 100 feet (30 m).
To enable GPS traps, uncomment these lines in the default configuration template.
Tip: Because GPS traps only generate Informational logs, we recommend that you create a rule-based event with high severity (such as CRITICAL) to inform the administrator of router movement. An example of this type of rule definition is: configGroup:name eventName:deviceLocChanged (see Creating a Rule).
Configuring SNMP v3 Informational Events
For Cisco IOS routers you configure SNMP v3 Informational Events to replace the default SNMP v3 traps. In CG-OS by default, SNMP v3 traps are configured for any IoT FND event-related changes that generate a trap on the router. IoT FND maps these traps to the corresponding event. For Cisco IOS routers, converting these SNMP v3 traps to SNMP v3 Informational Events sends an acknowledgment to the router for every event received from the router. The router then verifies that the trap was received by IoT FND. To enable SNMP v3 Informational Events, uncomment the following lines in the default configuration file and push the new configuration file to all router(s) in the group:
Editing the ENDPOINT Configuration Template
To edit an ENDPOINT configuration template:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Under CONFIGURATION GROUPS (left pane), select the ENDPOINT group with the template to edit.
Under CONFIGURATION GROUPS (left pane), select the ENDPOINT group with the template to edit.
3.![]() Click Edit Configuration Template.
Click Edit Configuration Template.
For example, in the Report Interval field, you can enter the number of seconds between data updates. By default, mesh endpoints send a new set of metrics every 28,800 seconds (8 hours).
You can change the following values on the Edit Configuration Template tab:
IoT FND commits the changes to the database and increases the version number.
Pushing Configurations to Routers
Note: CGRs, C800s, IR800s, and ISR 800s can coexist on a network; however, you must create custom configuration templates that includes both router types.
To push the configuration to routers:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Select the group or subset of a group to push the configuration to in the CONFIGURATION GROUPS pane.
Select the group or subset of a group to push the configuration to in the CONFIGURATION GROUPS pane.
3.![]() Click the Push Configuration tab to display that window.
Click the Push Configuration tab to display that window.
4.![]() In the Select Operation drop-down menu, choose Push Router Configuration.
In the Select Operation drop-down menu, choose Push Router Configuration.
For C800 and IR800 groups with embedded AP devices, choose Push AP Configuration to push the AP configuration template.
5.![]() In the Select Operation drop-down menu, choose Push Endpoint Configuration. Click Start.
In the Select Operation drop-down menu, choose Push Endpoint Configuration. Click Start.
The Push Configuration page displays the status of the push operation for every device in the group. If an error occurs while pushing configuration to a device, the error and its details display in the relevant columns.
In the Status column, one of these values appear:
Tip: To refresh the status information, click the Refresh button.
Enabling CGR SD Card Password Protection
Password protection for the SD card in the CGR helps prevent unauthorized access and prevents transference of the CGR SD card to another system with a different password.
Note: This does not apply to C800s or IR800s.
The Device Info pane displays CGR SD card password protection status in the Inventory section. The Config Properties tab displays the SD card password in the Router Credentials section.
To enable CGR SD card password protection:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Select the CGR group or CGRs to push the configuration to in the Configuration Groups pane.
Select the CGR group or CGRs to push the configuration to in the Configuration Groups pane.
3.![]() Select the Push Configuration tab.
Select the Push Configuration tab.

4.![]() In the Select Operation drop-down menu, choose Push SD Card Password.
In the Select Operation drop-down menu, choose Push SD Card Password.
5.![]() Click Start. Click Yes to confirm action or No to stop action.
Click Start. Click Yes to confirm action or No to stop action.
6.![]() Select SD Card protection > Enable.
Select SD Card protection > Enable.

7.![]() Select the desired protection method:
Select the desired protection method:
| ■ |
Pushing Configurations to Endpoints
To push configuration to mesh endpoints:
1.![]() Choose CONFIG > Device Configuration.
Choose CONFIG > Device Configuration.
2.![]() Select the group or subset of a group to push the configuration to in the ENDPOINT list.
Select the group or subset of a group to push the configuration to in the ENDPOINT list.
3.![]() Click the Push Configuration tab.
Click the Push Configuration tab.
Note: The Push Configuration tab supports a subnet view for cgmesh Endpoints that summarizes:
4.![]() In the Select Operation drop-down menu, choose Push Endpoint Configuration.
In the Select Operation drop-down menu, choose Push Endpoint Configuration.
5.![]() Click Start. Confirm action by clicking Yes button or stop the action by clicking the No button.
Click Start. Confirm action by clicking Yes button or stop the action by clicking the No button.
The Push Configuration page displays the status of the push operation for every device in the group. If an error occurs while pushing configuration to a device, the error and its details display in the relevant columns.
In the Status column, one of these values appear:
To refresh the status information, click the Refresh button.
Monitoring a Guest OS
Cisco IOS CGR1000s and IR800s support a virtual machine to run applications on a Guest OS (GOS) instance running beside the Cisco IOS virtual machine. The GOS is Linux. Applications running on the GOS typically collect statistics from the field for monitoring and accounting purposes. The Cisco IOS firmware bundle installs a reference GOS on the VM instance on the CGR or IR800s. IoT FND supports the following role-based features on the GOS:
■![]() Upgrading the reference GOS in the Cisco IOS firmware bundle
Upgrading the reference GOS in the Cisco IOS firmware bundle
Note: IoT FND only supports the reference GOS provided by Cisco.
You monitor a GOS on the DEVICES > Field Devices on the CGR1000 or IR829 configuration page.
Installing a GOS
Depending on CGR factory configuration, a GOS may be present in the VM instance. The GOS installs with the Cisco IOS firmware bundle (see Router Firmware Updates). The GOS, Hypervisor, and Cisco IOS all upgrade when you perform a Cisco IOS image bundle installation or update.
After any Cisco IOS install or upgrade, when IoT FND discovers a GOS, it checks if the initial communications setup is complete before it performs the required setup. The CGR must have a DHCP pool and Gigabit Ethernet 0/1 interface configured to provide an IP address and act as the gateway for the Guest OS. See the Cisco 1000 Series Connected Grid Routers Configuration Guides web portal for information on configuring the CGR.
Note: if the router is configured with Guest-OS CLI during the router’s registration with FND, FND detects that Guest-OS is running and will populate a new Guest OS tab on the Device Info page for that particular router.
Restarting a GOS
From that page, we could also trigger a Guest-OS restart by selecting the Restart GOS button and selecting Yes to confirm restart. Once the Guest-OS is restarted a pop-up with the status of the operation would be seen on the UI and messages would be logged in the server.log file.
Figure 11 DEVICES > Field Devices Information Page Showing Guest OS tab and Restart GOS Button

Installing a GOS
Depending on CGR factory configuration, a GOS may be present in the VM instance. The GOS installs with the Cisco IOS firmware bundle. The GOS, Hypervisor, and Cisco IOS all upgrade when you perform a Cisco IOS image bundle installation or update.
Note: Refer to the Router Firmware Updates section in the “Managing Firmwares Upgrades” chapter of this configuration guide.
After any Cisco IOS install or upgrade, when IoT FND discovers a GOS, it checks if the initial communications setup is complete before it performs the required setup. The CGR must have a DHCP pool and Gigabit Ethernet 0/1 interface configured to provide an IP address and act as the gateway for the Guest OS. See the Cisco 1000 Series Connected Grid Routers Configuration Guides web portal for information on configuring the CGR.
if the router is configured with Guest-OS CLI during the router’s registration with FND, FND would detect that Guest-OS is running and will populate a new Guest OS tab on the Device Info page for that particular router)DEVICES. From that page, we could also trigger a Guest-OS restart. Once the Guest-OS is restarted a pop-up with the status of the operation would be seen on the UI and messages would be logged in the server.log file.
Pushing GOS Configurations
You can push the GOS configuration to the CGR using the IoT FND config template. This is the only way to configure the DHCP pool.
Managing Files
Use the CONFIG > Device File Management page to transfer and execute dual backhaul and Embedded Event Manager (EEM) scripts on the router. The Template module performs file validation. This section includes the following topics:
Note: File management is role-dependent and may not be available to all users. See Managing Roles and Permissions.
File Types and Attributes
Two types of EEM scripts are used on the router: an embedded applet, and Tool Command Language (TCL) scripts that execute on the router individually. You can upload and run new EEM TCL scripts on the router without doing a firmware upgrade. EEM files upload to the eem directory in router flash memory. These scripts display in the Import File page File Type column as eem script. You must edit the configuration template file to activate the EEM TCL scripts (see Editing the ROUTER Configuration Template). This feature works with all router OS versions currently supported by IoT FND.
You can also transfer other file types to the router for better file management capability. You must first import the files to IoT FND to upload files to the router. IoT FND processes the file and stores it in the IoT FND database with the following attributes:
Adding a File to IoT FND
1.![]() On the CONFIG > Device File Management page, click Import Files or Upload (Actions tab) to open a selected file from List dialog box (far-left panel).
On the CONFIG > Device File Management page, click Import Files or Upload (Actions tab) to open a selected file from List dialog box (far-left panel).

2.![]() Click Add File and browse to the file location.
Click Add File and browse to the file location.
Note: The maximum import file size is 200 MB.
3.![]() (Optional) Type a description for the file.
(Optional) Type a description for the file.
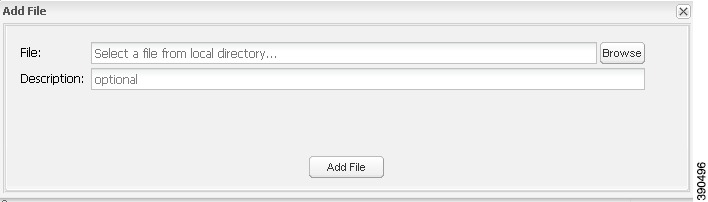
When the upload completes, the file name displays in the Select File From List dialog box.
5.![]() Repeat steps 2 through 4 to add another file, or see Transferring Files to upload the file to the selected device or group, or close the Select File From List dialog box.
Repeat steps 2 through 4 to add another file, or see Transferring Files to upload the file to the selected device or group, or close the Select File From List dialog box.
Note: At the Select File from List![]() dialog box, you can also delete imported files from the IoT FND database if the file is not in an active file transfer. This action only removes the file from the IoT FND database, not from any routers that contain the file. Click the Name hyperlink to view uploaded text files (file size must be less than 100KB).
dialog box, you can also delete imported files from the IoT FND database if the file is not in an active file transfer. This action only removes the file from the IoT FND database, not from any routers that contain the file. Click the Name hyperlink to view uploaded text files (file size must be less than 100KB).
Deleting a File from IoT FND
You can also delete imported files from the IoT FND database if the file is not in an active file transfer. This action only removes the file from the IoT FND database, not from any routers that contain the file. Click the Name hyperlink to view uploaded text files (file size must be less than 100KB).
1.![]() On the CONFIG > Device File Management page, select a file from List dialog box (far-left panel).
On the CONFIG > Device File Management page, select a file from List dialog box (far-left panel).
2.![]() At the Actions tab, click Delete button.
At the Actions tab, click Delete button.
3.![]() At the Delete from List panel, select a file and click Delete File.
At the Delete from List panel, select a file and click Delete File.
Transferring Files
You can transfer files from the NMS database to any firmware, configuration or tunnel provisioning group, or to individual routers. The maximum import file size is 200 MB.
1.![]() On the CONFIG > Device File Management page, select the group to transfer the file to from the Browse Devices left pane.
On the CONFIG > Device File Management page, select the group to transfer the file to from the Browse Devices left pane.
2.![]() Click Import Files or Upload on the Actions tab. The Select File from List dialog box displays.
Click Import Files or Upload on the Actions tab. The Select File from List dialog box displays.
3.![]() Select the file to transfer to the routers in the selected group.
Select the file to transfer to the routers in the selected group.
The Upload File to Routers dialog box displays.
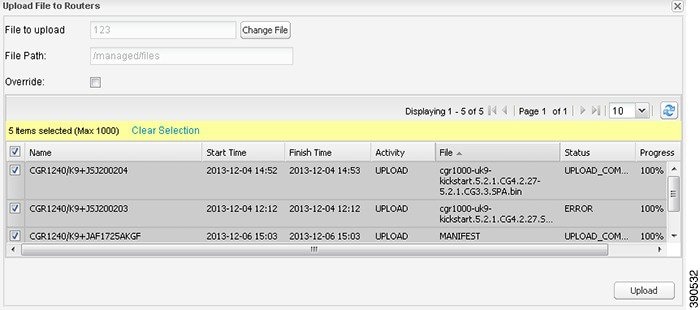
5.![]() Check the check boxes of the routers to which you want to transfer the file.
Check the check boxes of the routers to which you want to transfer the file.
If there is no file transfer or deletion, configuration push, firmware upload, or install or reprovision operations in progress for the group, the upload starts.
You can choose to transfer files to all routers in the selected group or select only a subset of the routers in the group. You can also select another group and file to perform a separate file transfer or deletion simultaneously.
All files transferred from IoT FND reside on the router in flash:/managed/files/ for Cisco IOS CGRs, and bootflash:/managed/files/ for CG-OS CGRs.
The status of the last file transfer is saved with the group, as well as the operation (firmware update, configuration push, and so on) and status of the group.
Viewing Files
To view imported text file content:
1.![]() Select CONFIG > Device File Management.
Select CONFIG > Device File Management.
2.![]() Click the EID link (such as CGR1240/K9+JAF1626BLDK) listed under the Name column to display the Device Info pane.
Click the EID link (such as CGR1240/K9+JAF1626BLDK) listed under the Name column to display the Device Info pane.
3.![]() Click the Router Files tab.
Click the Router Files tab.
4.![]() Click the file name link to view the content in a new window.
Click the file name link to view the content in a new window.
Note: IoT FND only displays files saved as plain text that are under 100 KB are viewable. You cannot view larger text files or binary files of any size. Those file types do not have a hyperlink.
Monitoring Files
On the CONFIG > Device File Management page, click the Managed Files tab to view a list of routers and the files uploaded to their.../managed/files/ directories. Devices listed in the main pane are members of the selected group.
The following information is included in this list:
■![]() EID link (Name) to the Device Info page
EID link (Name) to the Device Info page
■![]() Number of files (#Files) stored on the device
Number of files (#Files) stored on the device
You can use the Filter By File Name drop-down menu to only view devices that contain a particular file. Select All from the menu to include all devices in the group. Click the refresh button to update the list during file transfer or deletion processes.
Monitoring Actions
On the CONFIG > Device File Management page, click the Actions tab to view the status of the last file transfer or last file deleted for routers in the selected group. You can click the Cancel button to terminate any active file operation.
The Actions tab lists the following attributes:
■![]() Start Time and Finish time of the last transfer
Start Time and Finish time of the last transfer
■![]() Status of the process: UNKNOWN, AWAITING_DELETE, DELETE_IN_PROGRESS, DELETE_COMPLETE, CANCELLED, FINISHED, NONE, NOTSTARTED, UPLOAD_IN_PROGRESS, UPLOAD_COMPLETE, STOPPING, STOPPED
Status of the process: UNKNOWN, AWAITING_DELETE, DELETE_IN_PROGRESS, DELETE_COMPLETE, CANCELLED, FINISHED, NONE, NOTSTARTED, UPLOAD_IN_PROGRESS, UPLOAD_COMPLETE, STOPPING, STOPPED
■![]() Completed Devices: Displays the following total number of (upload complete/total number of target devices)
Completed Devices: Displays the following total number of (upload complete/total number of target devices)
■![]() Error/Devices: Number of errors and errored device count
Error/Devices: Number of errors and errored device count
■![]() Status: Icon displays: ?, X or check mark
Status: Icon displays: ?, X or check mark
■![]() Name: EID link to Device Info page
Name: EID link to Device Info page
■![]() Activity: UPLOAD, DELETE, NONE
Activity: UPLOAD, DELETE, NONE
■![]() Status: Text description of status)
Status: Text description of status)
■![]() Message: Describes any issues discovered during the process
Message: Describes any issues discovered during the process
Deleting Files
1.![]() On the CONFIG > Device File Management page, select the group to transfer the file to in the Browse Devices pane.
On the CONFIG > Device File Management page, select the group to transfer the file to in the Browse Devices pane.
2.![]() On the Actions tab, click Delete.
On the Actions tab, click Delete.
3.![]() In the Delete file from List dialog, select a file to delete.
In the Delete file from List dialog, select a file to delete.
You can delete the file from all routers in the selected group or any subset of routers in the group.
The Delete File from Routers dialog box displays.
5.![]() Check the check boxes of the routers from which you want to delete the file.
Check the check boxes of the routers from which you want to delete the file.
| ■ |
| ■ |
If there are no file transfer or deletion, configuration push, firmware upload, or install or reprovision operations in progress for the group, the delete operation begins. IoT FND searches the.../managed/files/ directory on the devices for the specified file name.
Note: On deletion, all file content is purged from the selected devices, but not from the IoT FND database. File clean-up status displays for the selected group.
You can select another group and file to perform a separate file deletion while file transfer or deletion processes are in progress for this group. When you cancel file deletion process before it completes, the currently running file deletion process completes and all waiting file deletion processes are cancelled.
Managing Work Orders
■![]() Creating User Accounts for Device Manager (IoT-DM) Users
Creating User Accounts for Device Manager (IoT-DM) Users
Note: The CGR1000, IR800, and IR500 routers support work orders. For more details on actions supported by platform and minimum software releases required, refer to the Release Notes for Cisco IoT Device Manager 5.2 and the
Cisco IoT Device Manager Installation and User Guide, Release 5.x for configuration details.
Note: The Work Orders feature works with IoT-DM Release 3.0 or later. For integration instructions, see “Accessing Work Authorizations” in the Cisco Connected Grid Device Manager Installation and User Guide, Release 3.1, or “Managing Work Orders” in the Cisco Connected Grid Device Manager Installation and User Guide (Cisco IOS), Release 4.0 and 4.1 or Cisco IoT Device Manager Installation and User Guide (Cisco IOS), Release 5.0.
Note: If you are using CGDM Release 3.1 and later, you must enable SSLv3 for IoT-DM–IoT FND connection authentication:
2.![]() For IoT-DM Release 3.x and later, in the following files, replace protocol="TLSv1" attribute:
For IoT-DM Release 3.x and later, in the following files, replace protocol="TLSv1" attribute:
Viewing Work Orders
To view work orders in IoT FND, choose OPERATIONS > Work Orders.
Work Orders Page Fields lists the fields that display on the Work Orders page.
Creating User Accounts for Device Manager (IoT-DM) Users
Before creating work orders, you must create user accounts for the field technicians who use IoT-DM to download work orders from IoT FND.
To create a Device Manager user account:
1.![]() If not defined, create a Device Manager User role:
If not defined, create a Device Manager User role:
a.![]() Choose ADMIN > Access Management > Roles.
Choose ADMIN > Access Management > Roles.
c.![]() (CG-OS only) In the Role Name field, enter a name for the role.
(CG-OS only) In the Role Name field, enter a name for the role.
d.![]() Check the check box for Device Manager User, and click the disk icon to save the changes.
Check the check box for Device Manager User, and click the disk icon to save the changes.
a.![]() Choose ADMIN > Access Management > Users, and then click + to add a user.
Choose ADMIN > Access Management > Users, and then click + to add a user.
b.![]() Enter the user name, new password, confirm password and time zone information.
Enter the user name, new password, confirm password and time zone information.
d.![]() Click Assign Domain. In the panel that appears, check the check boxes for Monitor Only and the Device Manager User role you created in Step 1.
Click Assign Domain. In the panel that appears, check the check boxes for Monitor Only and the Device Manager User role you created in Step 1.
Creating Work Orders
If you need a technician to inspect a deployed router (CGR 1120 or CGR 1240) or DA Gateway (IR509) in the field, create a work order. A work order includes the WiFi credentials required for the technician to connect to the router.
■![]() Your user account must have the Work Order Management permissions enabled.
Your user account must have the Work Order Management permissions enabled.
■![]() To provide a signed work order to IoT-DM on request, you must import IoT-DM certificates to cgms_keystore using the alias cgms.
To provide a signed work order to IoT-DM on request, you must import IoT-DM certificates to cgms_keystore using the alias cgms.
■![]() Create the user account for the field technician. (See Creating User Accounts for Device Manager (IoT-DM) Users)
Create the user account for the field technician. (See Creating User Accounts for Device Manager (IoT-DM) Users)
Note: You can only create work orders for CGRs and IR509 devices.
Figure 12 Creating a Work Order

To create a work order for Router (CGR1000) or Endpoint (IR509):
1.![]() Choose OPERATIONS > Work Orders.
Choose OPERATIONS > Work Orders.
3.![]() In the Work Order Name field, enter the name of the work order.
In the Work Order Name field, enter the name of the work order.
4.![]() In the Field Device Names/EIDs field, enter a comma-separated list of router names or EIDs.
In the Field Device Names/EIDs field, enter a comma-separated list of router names or EIDs.
For every router in the list, IoT FND creates a separate work order.
5.![]() Device Type (Router or Endpoint) and CGR OS version (CG-OS or IOS) auto-populate.
Device Type (Router or Endpoint) and CGR OS version (CG-OS or IOS) auto-populate.
6.![]() Enter the IoT-DM system name in the Device Username field.
Enter the IoT-DM system name in the Device Username field.
Select the Technician User Name for the IoT-DM from the drop-down menu.This menu only lists users with IoT-DM User permissions enabled.
7.![]() From the Status drop-down menu, choose the status of the work order (New, Assigned, In Service, Completed, or InComplete). The New option auto-populates.
From the Status drop-down menu, choose the status of the work order (New, Assigned, In Service, Completed, or InComplete). The New option auto-populates.
Note: For a IoT-DM user to retrieve a work order, the work order must be in the Assigned state in IoT FND for that user. If the work order is in any other state, IoT-DM cannot retrieve the signed work order.
Note: After the work order has been successfully requested by the IoT-DM user, the state of work order changes to In Service.
8.![]() In the Start Date and End Date fields, specify the starting and ending dates for which the work order is valid.
In the Start Date and End Date fields, specify the starting and ending dates for which the work order is valid.
If the work order is not valid, the technician cannot access the router.
9.![]() In the Device Time Zone field, choose the time zone of the device from the drop-down menu.
In the Device Time Zone field, choose the time zone of the device from the drop-down menu.
10.![]() To save your entries, click the disk icon. (To cancel your entries, click x)
To save your entries, click the disk icon. (To cancel your entries, click x)
You can also create work orders on the Field Devices page (DEVICES > Field Devices > More Actions menu), as described in Creating Work Orders, and on the Device Info page.
Downloading Work Orders
To download the work orders created by IoT FND, a field technician uses Cisco IoT-DM, which is a Windows-based application used to manage a single Cisco CGR 1000 router. The technician can download all work orders in the Assigned state.
Field technicians use IoT-DM to update work order status, which is sent to IoT FND.
Note: Certificates are not included in the work order and are preinstalled on the IoT-DM field laptop prior to downloading work orders from IoT FND.
For more information about IoT-DM, see the 2 Cisco IoT Device Manager User Guide for Release 5.2.
Editing Work Orders
1.![]() Choose OPERATIONS > Work Orders.
Choose OPERATIONS > Work Orders.
2.![]() Click the box next to the work order you want to edit. Click Edit Work Order.
Click the box next to the work order you want to edit. Click Edit Work Order.
Alternatively, click the work order number to open the page displaying the work order details.
Deleting Work Orders
1.![]() Choose OPERATIONS > Work Orders.
Choose OPERATIONS > Work Orders.
Demo and Bandwidth Operation Modes
The Demo and Bandwidth Operation Modes allow you define the application protocol (HTTP or HTTPS) to use for communication between FND and the router to minimize setup and bandwidth requirements, respectively. The two modes do not affect or change the way that FND communicates with meters or other endpoints. Secure communication between FND and endpoints devices will continue to be secured by using a hardware secure module (HSM) or software secure module (SSM).
■![]() Demo Mode: Allows users to quickly set up a small network with FND for demos by minimizing the setup requirements. It eliminates the need for router certificates or the need to setup SSL.
Demo Mode: Allows users to quickly set up a small network with FND for demos by minimizing the setup requirements. It eliminates the need for router certificates or the need to setup SSL.
■![]() Bandwidth optimization mode: Reduces network bandwidth requirements for a network by using HTTP to send periodic metrics between routers and FND while preserving security for other operations. All other router communications will employ HTTPS.
Bandwidth optimization mode: Reduces network bandwidth requirements for a network by using HTTP to send periodic metrics between routers and FND while preserving security for other operations. All other router communications will employ HTTPS.
Demo Mode Configuration
FND Configuration Changes
In order to change FND router Management mode to Demo mode, you must:
1.![]() Add the following to the cgms.properties file:
Add the following to the cgms.properties file:
2.![]() Add the following to the tpsproxy.properties file:
Add the following to the tpsproxy.properties file:
3.![]() For the AP registration process, you must add the following two properties to the cgms.properties file:
For the AP registration process, you must add the following two properties to the cgms.properties file:
Router Configuration Changes
In order to manage routers in Demo mode:
1.![]() Manually change the URL for all the profiles to use HTTP protocol:
Manually change the URL for all the profiles to use HTTP protocol:
2.![]() Update WSMA profile URL to use HTTP protocol (Only Required in Demo Mode
Update WSMA profile URL to use HTTP protocol (Only Required in Demo Mode
3.![]() Update URL of iot-fnd-register, iot-fnd-metric and iot-fnd-tunnel profiles to use HTTP protocol on Cisco Wireless Gateway for LoRaWAN (IXM-LPWA)
Update URL of iot-fnd-register, iot-fnd-metric and iot-fnd-tunnel profiles to use HTTP protocol on Cisco Wireless Gateway for LoRaWAN (IXM-LPWA)
Bandwidth Optimization Mode Configuration
Only periodic metrics will go over HTTP protocol in the Bandwidth Organization Mode. So, you have to manually change the metric profile URL as follows:
Manually change the URL of metrics profiles to use HTTP protocol, by entering:
Note: When operating In Bandwidth Optimization Mode, all WSMA requests must go over HTTPS. Therefore, you must ensure that the WSMA profile listener is set to HTTPS at the config and exec command modes.
Configuring Demo Mode in User Interface
Note: By default, all communications between FND and the router will be over HTTPS.
To setup Demo Mode for FND and router communications:
1.![]() Choose ADMIN > SYSTEM MANAGEMENT > Provisioning Settings.
Choose ADMIN > SYSTEM MANAGEMENT > Provisioning Settings.
2.![]() In the Provisioning Process panel, enter the IoT-FND URL in the following format: http:// <ip address:9121> in both the IoT-FND URL and Periodic Metrics URL fields.
In the Provisioning Process panel, enter the IoT-FND URL in the following format: http:// <ip address:9121> in both the IoT-FND URL and Periodic Metrics URL fields.
Note: The FAR uses the IoT FND URL to communicate with IoT-FND after the tunnel is configured and uses the Periodic Metrics URL to report periodic metrics and notifications with IoT-FND.
Configuring Bandwidth Optimization Mode in User Interface
Note: By default, all communications between FND and the router will be over HTTPS.
To setup Bandwidth Optimization Mode for FND and router communications:
1.![]() Choose ADMIN > SYSTEM MANAGEMENT > Provisioning Settings.
Choose ADMIN > SYSTEM MANAGEMENT > Provisioning Settings.
2.![]() In the Provisioning Process panel:
In the Provisioning Process panel:
–![]() Enter your IoT-FND URL in the following format: “https:// FND IP/HostName:9121" in the IoT-FND URL field. FAR uses this URL to communicate with IoT-FND after the tunnel is configured.
Enter your IoT-FND URL in the following format: “https:// FND IP/HostName:9121" in the IoT-FND URL field. FAR uses this URL to communicate with IoT-FND after the tunnel is configured.
–![]() Enter the following URL in the Periodic Metrics URL field: http:// <ip address:9124>
Enter the following URL in the Periodic Metrics URL field: http:// <ip address:9124>
FAR uses this URL to report periodic metrics and notifications with IoT-FND.

Device Properties
This section describes the device properties that you can view in IoT FND. Some of these properties are configurable; others are not.
■![]() Device Properties by Category
Device Properties by Category
Types of Device Properties
IoT FND stores two types of device properties in its database:
■![]() Actual device properties—These are the properties defined by the device, such as IP Address, Transmit Speed, and SSID.
Actual device properties—These are the properties defined by the device, such as IP Address, Transmit Speed, and SSID.
■![]() IoT FND device properties—These are properties defined by IoT FND for devices, such Latitude and Longitude properties, which IoT FND uses to display device locations on its GIS map.
IoT FND device properties—These are properties defined by IoT FND for devices, such Latitude and Longitude properties, which IoT FND uses to display device locations on its GIS map.
Note: The Key column provides the version of the property name in the IoT FND database that you can use in filters. For example, to search for the device with an IP address of 10.33.0.30, enter ip:10.33.0.30 in the Search Devices field.
Device Properties by Category
This section presents IoT FND device properties by category:
■![]() Cellular Link Metrics for CGRs
Cellular Link Metrics for CGRs
■![]() Embedded Access Point Credentials
Embedded Access Point Credentials
■![]() Head-End Routers > Netconf Config
Head-End Routers > Netconf Config
■![]() Head-End Routers > Tunnel 1 Config
Head-End Routers > Tunnel 1 Config
■![]() Head-End Routers > Tunnel 2 Config
Head-End Routers > Tunnel 2 Config
■![]() Raw Sockets Metrics and Sessions
Raw Sockets Metrics and Sessions
Every device in IoT FND presents a list of fields, which are used for device searches. The available fields for a device are defined in the Device Type field. Fields are either configurable or discovered. Configurable fields are set using XML and CSV files; the device EID is the lookup key. Discovered fields are presented from the device. Fields are also accessible in the device configuration templates for routers.
Cellular Link Settings
Cellular Link Settings Fields lists the fields in the Cellular Link area of the Device Detail page for all Cellular interfaces.
Note: Beginning with IoT FND 3.2, Cisco routers IR829, CGR1240, CGR1120 and Cisco 819 4G LTE ISRs (C819) support a new dual-active radio module that support dual modems and 2 physical interfaces (interfaces 0 and 1, interfaces 2 and 3) per modem. See SKUs below:
■![]() CGM-LTE-LA for CGR 1000 routers
CGM-LTE-LA for CGR 1000 routers
Cellular properties supported on the dual modems and their two physical interfaces (and four logical interfaces 0, 1, 2 and 3), display as follows:
Additionally, the 4G LTE dual-active radio module does not support or display all fields summarized in Cellular Link Settings Fields
Cellular Link Metrics for CGRs
Cellular Link Metrics Area Fields describes the fields in the Cellular Link Metrics area of the Device Info view.
DA Gateway Properties
DA Gateway Metrics Area Fields describe the fields in the DA Gateway area of the Device Info view.
Dual PHY WPAN Properties
Dual PHY Metrics Area Fields describes the fields in the Dual PHY area of the Device Info view.
Embedded Access Point Credentials
Embedded Access Point Credentials Fields describes the fields in the Embedded Access Point Credentials area of the Device Info view.
|
|
|
|
|
|---|---|---|---|
Embedded AP Properties
Embedded AP Properties describes the fields on the Embedded AP tab of the C800 or IR800 Device Info view.
Ethernet Link Metrics
Ethernet Link Metrics Area Fields describes the fields in the Ethernet link traffic area of the Device Info view.
Guest OS Properties
Guest OS Properties Fields describes the fields in the Guest OS Properties area of the Config Properties page.
|
|
|
|
|---|---|---|
Head-End Routers > Netconf Config
Head-End Routers > Netconf Config Client Fields describes the fields in the Netconf Client area of the Head-End Routers > Config Properties page.
Head-End Routers > Tunnel 1 Config
Head-End Routers > Tunnel 1 Config Fields describes the fields in the Tunnel 1 Config area of the Head-End Routers > Config Properties page.
Head-End Routers > Tunnel 2 Config
Head-End Routers > Tunnel 2 Config Device Fields describes the fields in the Tunnel 2 Config area of the Head-End Routers > Config Properties page.
Inventory
Inventory Fields describes the fields in the Inventory area of the Device Info page.
EXAMPLE PATH to Device Info page which summarizes the Inventory details: DEVICES> Field Devices > ROUTERS > CGR1000 > EID Name
Mesh Link Config
Mesh Link Config Fields describes the fields in the Mesh Link Config area of the Routers > Config Properties page.
|
|
|
|
|
|---|---|---|---|
(Dual-PHY CGRs only) The interface on which the device is master. |
|||
(Dual-PHY CGRs only) The interface on which the device is slave. |
Mesh Device Health
Mesh Device Health Fields describes the fields in the Mesh Device Health area of the Device Info view.
|
|
|
|
|---|---|---|
The amount of time in days, hours, minutes and seconds, that the device has been running since the last boot. Unknown appears when the system is not connected to the network. |
Mesh Link Keys
Mesh Link Keys Fields describes the fields in the Mesh Link Keys area of the Device Info view.
|
|
|
|
|
|---|---|---|---|
Mesh Link Settings
Mesh Link Settings Fields describes the fields in the Mesh Link Settings area of the Device Info view.
Mesh Link Metrics
Mesh Link Metrics Fields describes the fields in the Mesh Link Metrics area of the Device Info page.
NAT44 Metrics
NAT44 Metrics Fields describes the fields in the NAT44 area of the Device Info page.
|
|
|
|
|---|---|---|
PLC Mesh Info
PLC Mesh Info Fields describes the fields in the PLC Mesh Info area of the Device Info view.
Raw Sockets Metrics and Sessions
Raw Sockets Metrics and Sessions View describes the fields in the TCP Raw Sockets area of the Field Devices > Config Properties page.
Router Battery
Router Battery Device View describes the fields in the Router Battery area of the Device Info page.
Router Config
Router Config Device View describes the fields in the Router Config area of the Field Devices > Config Properties page.
|
|
|
|
|
|---|---|---|---|
The internal GPS module provides the router location (longitude and latitude). |
Router Credentials
Router Credentials Fields describes the fields in the Router Credentials area of the Field Devices > Config Properties page.
|
|
|
|
|
|---|---|---|---|
Router DHCP Info
Router DHCP Fields describes the fields in the DHCP Info area of the Device Info page.
|
|
|
|
|---|---|---|
Router DHCP Proxy Config
DHCP Proxy Config Fields describes the fields in the DHCP Proxy Config area of the Field Devices > Config Properties page.
Router Health
Router Health Device View describes the Router Health fields in the Device Info view.
Router Tunnel Config
Router Tunnel Config Device View describes the fields in the Router Tunnel Config area of the Field Devices > Config Properties page.
|
|
|
|
|
|---|---|---|---|
Displays the EID number of the HER that the router connects with through secure tunnels. |
|||
Displays the Non-Broadcast Multiple Access (NBMA) IPv4 address. |
|||
Router Tunnel 1 Config
Router Tunnel 1 Config Device View describes the fields in the Router Tunnel 1 Config area of the Field Devices > Config Properties page.
Router Tunnel 2 Config
Router Tunnel 2 Config Device View describes the fields in the Router Tunnel 2 Config area of the Field Devices > Config Properties page.
SCADA Metrics
SCADA Metrics View describes the fields on the SCADA tab of the Device Info page.
User-defined Properties
The User-defined Properties area of the Routers > Config Properties page displays any customer defined properties.
WiFi Interface Config
WiFi Interface Config Fields describes the fields in the WiFi Interface Config area of the Field Devices > Config Properties page.
|
|
|
|
|
|---|---|---|---|
The service set identifier (SSID) assigned to the WiFi interface on the router. |
|||
The key used to encrypt other pre-shared keys stored on the router. |
WiMAX Config
WiMAX Config Fields describes the fields in the WiMAX Config area of the Device Info page. Use these properties to set up a username and password for the Pairwise Key Management (PKM) of a CGR 1000.
Note: The WiMAX module must be installed and running. CGR1000s that ship with a pre-installed WiMAX module that has a pre-installed WiMAX configuration.
|
|
|
|
|---|---|---|
WiMAX Link Metrics
WiMAX Link Health Fields describes the fields in the WiMAX Link Health area of the Device Info page.
WiMAX Link Settings
WiMAX Link Settings Fields describes the fields in the WiMAX Link Settings area of the Device Info page.
|
|
|
|
|---|---|---|
 ) to update the Map view.
) to update the Map view.  ).
). Feedback
Feedback