- Preface
-
- Getting Started with Security Manager
- Preparing Devices for Management
- Managing the Device Inventory
- Managing Activities
- Managing Policies
- Managing Policy Objects
- Managing FlexConfigs
- Managing Deployment
- Troubleshooting Device Communication and Deployment
- Managing the Security Manager Server
- Configuring Security Manager Administrative Settings
-
- Introduction to Firewall Services
- Managing Identity-Aware Firewall Policies
- Managing TrustSec Firewall Policies
- Managing Firewall AAA Rules
- Managing Firewall Access Rules
- Managing Firewall Inspection Rules
- Managing Firewall Web Filter Rules
- Managing Firewall Botnet Traffic Filter Rules
- Working with ScanSafe Web Security
- Managing Zone-based Firewall Rules
- Managing Traffic Zones
- Managing Transparent Firewall Rules
- Configuring Network Address Translation
-
- Managing Site-to-Site VPNs: The Basics
- Configuring IKE and IPsec Policies
- GRE and DM VPNs
- Easy VPN
- Group Encrypted Transport (GET) VPNs
- Managing Remote Access VPNs: The Basics
- Managing Remote Access VPNs on ASA and PIX 7.0+ Devices
- Managing Dynamic Access Policies for Remote Access VPNs (ASA 8.0+ Devices)
- Managing Remote Access VPNs on IOS and PIX 6.3 Devices
- Configuring Policy Objects for Remote Access VPNs
- Using Map View
-
- Getting Started with IPS Configuration
- Managing IPS Device Interfaces
- Configuring Virtual Sensors
- Defining IPS Signatures
- Configuring Event Action Rules
- Managing IPS Anomaly Detection
- Configuring Global Correlation
- Configuring Attack Response Controller for Blocking and Rate Limiting
- Managing IPS Sensors
- Configuring IOS IPS Routers
-
- Managing Firewall Devices
- Configuring Bridging Policies on Firewall Devices
- Configuring Device Administration Policies on Firewall Devices
- Configuring Device Access Settings on Firewall Devices
- Configuring Failover
- Configuring Hostname, Resources, User Accounts, and SLAs
- Configuring Server Access Settings on Firewall Devices
- Configuring FXOS Server Access Settings on Firepower 2100 Series Devices
- Configuring Logging Policies on Firewall Devices
- Configuring Multicast Policies on Firewall Devices
- Configuring Routing Policies on Firewall Devices
- Configuring Security Policies on Firewall Devices
- Configuring Service Policy Rules on Firewall Devices
- Configuring Security Contexts on Firewall Devices
- User Preferences
- Index
User Guide for Cisco Security Manager 4.15
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- February 12, 2015
Chapter: Configuring Routing Policies
Configuring Routing Policies
This chapter contains the following topics:
- BGP Routing on Cisco IOS Routers
- BGP Routing Policy Page
- EIGRP Routing on Cisco IOS Routers
- EIGRP Routing Policy Page
- OSPF Routing on Cisco IOS Routers
- OSPF Interface Policy Page
- OSPF Process Policy Page
- RIP Routing on Cisco IOS Routers
- RIP Routing Policy Page
- Static Routing on Cisco IOS Routers
- Static Routing Policy Page
BGP Routing on Cisco IOS Routers
BGP is an Exterior Gateway Protocol (EGP) that guarantees the loop-free exchange of routing information between autonomous systems (ASs). The primary function of a BGP system is to exchange information with other BGP systems about the networks it can reach, including AS path information. This information can be used to construct a graph of AS connectivity from which routing loops can be pruned and with which AS-level policy decisions can be enforced.
BGP is the routing protocol used on the Internet and is commonly used between Internet service providers. To achieve scalability at this level, BGP uses several route parameters (attributes) to define routing policies and maintain a stable routing environment. Additionally, BGP uses classless interdomain routing (CIDR) to greatly reduce the size of Internet routing tables.
A BGP route consists of a network number, a list of ASs through which information has passed (called the autonomous system path), and the defined path attributes.
A BGP router exchanges routing information only with those routers that you define as its neighbors. BGP neighbors exchange complete routing information when the TCP connection between them is established. Updates are sent to neighbors only when changes to the routing table are detected. BGP routers do not send regular, periodic updates.
The following topics describe the tasks you perform to create a BGP routing policy:

Note![]() Security Manager supports versions 2, 3 and 4 of BGP, as defined in RFCs 1163, 1267 and 1771.
Security Manager supports versions 2, 3 and 4 of BGP, as defined in RFCs 1163, 1267 and 1771.
- Static Routing on Cisco IOS Routers
- RIP Routing on Cisco IOS Routers
- OSPF Routing on Cisco IOS Routers
- EIGRP Routing on Cisco IOS Routers
Defining BGP Routes
As with all EGPs, when you configure a BGP routing policy, you must define the relationship the router has with its neighbors. BGP supports two kinds of neighbors: internal (located in the same AS) and external (located in a different AS). Typically, external neighbors are adjacent to each other and share a subnet; internal neighbors can be anywhere in the same AS.
In addition, you can select whether to enable the following optional features:
If enabled, auto-summarization injects only the network route when a subnet is redistributed from an Interior Gateway Protocol (IGP) such as OSPF or EIGRP into BGP. Synchronization is useful if your AS acts as an intermediary, passing traffic from one AS to another AS, because it ensures that your AS is consistent about the routes it advertises. For example, if BGP were to advertise a route before all routers in your network had learned about the route through your IGP, your AS might receive traffic that some routers cannot yet route. Neighbor logging enables the router to keep track of messages issued by BGP neighbors when they reset, become unreachable, or restore their connection to the network.
This procedure describes how to define a BGP route. You can define only one BGP route on each router.
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > BGP from the Policy selector, then click the Setup tab in the work area.
- (Policy view) Select Router Platform > Routing > BGP from the Policy Type selector. Select an existing policy or create a new one, and then click the Setup tab.
The BGP Setup is displayed. See Table 67-1 for a description of the fields on this tab.
Step 2![]() On the BGP Setup tab, enter the AS number to which the router belongs.
On the BGP Setup tab, enter the AS number to which the router belongs.
Step 3![]() (Optional) Enter the addresses of the networks that are local to this AS. You can use a combination of addresses and network/host objects, or click Select to select an object from a list or to create a new one. For more information, see Specifying IP Addresses During Policy Definition.
(Optional) Enter the addresses of the networks that are local to this AS. You can use a combination of addresses and network/host objects, or click Select to select an object from a list or to create a new one. For more information, see Specifying IP Addresses During Policy Definition.
Step 4![]() Define external and internal BGP neighbors for the routers:
Define external and internal BGP neighbors for the routers:
a.![]() Click Add under Neighbors to display the BGP Neighbors dialog box. See Table 67-2 for a description of the fields in this dialog box.
Click Add under Neighbors to display the BGP Neighbors dialog box. See Table 67-2 for a description of the fields in this dialog box.
b.![]() Enter an AS number and then click Select to select the hosts that are neighbors within the defined AS. Internal neighbors are located in the same AS as the router; external neighbors are located in a different AS.
Enter an AS number and then click Select to select the hosts that are neighbors within the defined AS. Internal neighbors are located in the same AS as the router; external neighbors are located in a different AS.
c.![]() Click OK to save your definitions and return to the BGP Neighbors dialog box.
Click OK to save your definitions and return to the BGP Neighbors dialog box.
d.![]() (Optional) Repeat b. and c. to define neighbors in additional ASs.
(Optional) Repeat b. and c. to define neighbors in additional ASs.

Note![]() When you define BGP neighbors, the IP addresses cannot belong to an interface on the selected router. In addition, you cannot define the same IP address in more than one AS.
When you define BGP neighbors, the IP addresses cannot belong to an interface on the selected router. In addition, you cannot define the same IP address in more than one AS.
When you finish, click OK in the BGP Neighbors dialog box to return to the BGP Setup tab. Your selections are displayed in the Neighbors field.
Step 5![]() (Optional) Select the Auto-Summary check box to enable automatic summarization. If automatic summarization is enabled, only the network route is injected into the BGP table when a subnet is redistributed from an IGP (such as OSPF or EIGRP) into BGP.
(Optional) Select the Auto-Summary check box to enable automatic summarization. If automatic summarization is enabled, only the network route is injected into the BGP table when a subnet is redistributed from an IGP (such as OSPF or EIGRP) into BGP.
Step 6![]() (Optional) Select the Synchronization check box to synchronize BGP with the IGP. Enabling this feature causes BGP to wait until the IGP propagates routing information across the AS.
(Optional) Select the Synchronization check box to synchronize BGP with the IGP. Enabling this feature causes BGP to wait until the IGP propagates routing information across the AS.
You do not need synchronization if your AS does not pass traffic it receives from one AS to another AS, or if all the routers in your AS run BGP. Disabling synchronization enables BGP to converge more quickly.
Step 7![]() (Optional) Select the Log-Neighbor check box to enable the logging of messages generated when a BGP neighbors resets, comes up, or goes down.
(Optional) Select the Log-Neighbor check box to enable the logging of messages generated when a BGP neighbors resets, comes up, or goes down.
Redistributing Routes into BGP
Redistribution refers to using a routing protocol, such as BGP, to advertise routes that are learned by some other means, such as a different routing protocol, static routes, or directly connected routes. For example, you can redistribute routes from the OSPF routing protocol into your BGP autonomous system (AS). Redistribution is necessary in networks that operate in multiple-protocol environments and can be applied to all IP-based routing protocols.
- Define a BGP AS. See Defining BGP Routes.
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > BGP from the Policy selector, then click the Redistribution tab in the work area.
- (Policy view) Select Router Platform > Routing > BGP from the Policy Type selector. Select an existing policy or create a new one, and then click the Redistribution tab.
The BGP Redistribution tab is displayed. See Table 67-3 for a description of the fields on this tab.
Step 2![]() On the BGP Redistribution tab, select a row from the BGP Redistribution Mappings table, then click Edit, or click Add to create a mapping. The BGP Redistribution Mapping dialog box appears. See Table 67-4 for a description of the fields in this dialog box.
On the BGP Redistribution tab, select a row from the BGP Redistribution Mappings table, then click Edit, or click Add to create a mapping. The BGP Redistribution Mapping dialog box appears. See Table 67-4 for a description of the fields in this dialog box.
Step 3![]() Select the protocol whose routes you want to redistribute into BGP.
Select the protocol whose routes you want to redistribute into BGP.

Note![]() You can create a single mapping for each static route, RIP route, EIGRP AS, and OSPF process.
You can create a single mapping for each static route, RIP route, EIGRP AS, and OSPF process.
Step 4![]() (Optional) Modify the default metric (cost) of the redistributed routes. The metric determines the priority of the routes.
(Optional) Modify the default metric (cost) of the redistributed routes. The metric determines the priority of the routes.
Step 5![]() Click OK to save your definitions locally on the client and close the dialog box. The redistribution mapping appears in the Redistribution Mapping table in the BGP Redistribution tab.
Click OK to save your definitions locally on the client and close the dialog box. The redistribution mapping appears in the Redistribution Mapping table in the BGP Redistribution tab.
BGP Routing Policy Page
Border Gateway Protocol (BGP) is an exterior gateway protocol (EGP) that performs routing between multiple autonomous systems or domains and exchanges routing and reachability information with other BGP systems. BGP is used to exchange routing information on the Internet and is the protocol used between Internet service providers.
You can configure BGP routing policies from the following tabs on the BGP Routing page:
For more information, see BGP Routing on Cisco IOS Routers.
- (Device view) Select Platform > Routing > BGP from the Policy selector.
- (Policy view) Select Router Platform > Routing > BGP from the Policy Type selector. Right-click BGP to create a policy, or select an existing policy from the Shared Policy selector.
BGP Page—Setup Tab
Use the BGP Setup tab to define the number of the autonomous system (AS) in which the selected router is located. You must then define which networks are included in the AS and which networks are the internal and external neighbors of the router. Additionally, you can enable or disable options that govern the interaction between BGP and Interior Gateway Protocols (IGPs), such as OSPF and EIGRP. Use a third option to enable the logging of messages from BGP neighbors.
Go to the BGP Routing Policy Page, then click the Setup tab.
- Defining BGP Routes
- BGP Page—Redistribution Tab
- Specifying IP Addresses During Policy Definition
- Understanding Networks/Hosts Objects
|
|
|
|---|---|
The number of the autonomous system in which the router is located. Valid values range from 1 to 65535. This number enables a BGP routing process. If BGP is already configured on the device, you cannot successfully change and deploy this number. If you need to change the AS number, first unassign the BGP policy, deploy your change (thus removing the BGP configuration from the device), then configure the BGP policy with the new number and redeploy the configuration. |
|
The networks associated with the BGP route. Enter one or more network addresses or network/host objects, or click Select to select the object from a list or to create a new one. Note To remove a network from the route, select it from the Network field, then click Delete. |
|
The internal neighbors (those located in the same AS as the router) and external neighbors (located in different ASs) of the router. See Neighbors Dialog Box. |
|
When selected, automatic summarization is enabled. When a subnet is redistributed from an IGP (such as RIP, OSPF or EIGRP) into BGP, this BGP version 3 feature injects only the network route into the BGP table. Automatic summarization reduces the size and complexity of the routing table that the router must maintain. When deselected, automatic summarization is disabled. This is the default. |
|
When selected, synchronization is enabled. Use this feature to ensure that all routers in your network are consistent about the routes they advertise. Synchronization forces BGP to wait until the IGP propagates routing information across the AS. When deselected, synchronization is disabled. You can disable synchronization if this router does not pass traffic from a different AS to a third AS, or if all the routers in the AS are running BGP. Disabling this feature has the benefit of reducing the number of routes the IGP must carry, which improves convergence times. This is the default. |
|
When selected, enables the logging of messages that are generated when a BGP neighbors resets, connects to the network, or is disconnected. This is the default. |
Neighbors Dialog Box
Use the Neighbors dialog box to define the internal and external neighbors of the selected router.
Go to the BGP Page—Setup Tab, then click the Add or Edit button in the Neighbors field.
- Defining BGP Routes
- Specifying IP Addresses During Policy Definition
- Understanding Networks/Hosts Objects
BGP Page—Redistribution Tab
Use the BGP Redistribution tab to view, create, edit, and delete redistribution settings when performing redistribution into a BGP autonomous system (AS).

Note![]() You must define BGP setup parameters before you can access the BGP Redistribution tab. See BGP Page—Setup Tab.
You must define BGP setup parameters before you can access the BGP Redistribution tab. See BGP Page—Setup Tab.
Go to the BGP Routing Policy Page, then click the Redistribution tab.
- Redistributing Routes into BGP
- BGP Page—Setup Tab
- Table Columns and Column Heading Features
- Filtering Tables
|
|
|
|---|---|
The AS number or process ID of the route being redistributed. |
|
The value that determines the priority of the redistributed route. |
|
When redistributing an OSPF process, indicates the types of OSPF routes that are being redistributed. |
|
When redistributing static routes, indicates the type of static route, IP or OSI. |
|
Opens the BGP Redistribution Mapping Dialog Box. From here you can define BGP redistribution mappings. |
|
Opens the BGP Redistribution Mapping Dialog Box. From here you can edit the selected BGP redistribution mapping. |
|
Deletes the selected BGP redistribution mappings from the table. |
BGP Redistribution Mapping Dialog Box
Use the BGP Redistribution Mapping dialog box to add or edit the properties of a BGP redistribution mapping.
Go to the BGP Page—Redistribution Tab, then click the Add or Edit button beneath the table.
EIGRP Routing on Cisco IOS Routers
Enhanced Interior Gateway Routing Protocol (EIGRP) is an enhanced distance vector protocol developed by Cisco Systems that integrates the capabilities of link-state protocols. EIGRP is suited for many different topologies and media. Key capabilities that distinguish EIGRP from other routing protocols are fast convergence, support for variable-length subnet masks, partial updates, and multiple network-layer protocols.
The metric that the router uses to reach the destination, and to advertise to other routers, is the sum of the best-advertised metrics from all neighbors and the link cost to the best neighbor.
EIGRP uses neighbor tables to store address and interface information about each of the router’s neighbors. Hello packets advertise hold times, which is the length of time a neighbor can be considered reachable and operational. Topology tables contain all destinations advertised by neighboring routers. For each neighbor, the entry records the advertised metric, which the neighbor stores in its routing table.
A router running EIGRP stores all its neighbors’ routing tables so that it can quickly adapt to alternate routes. If no appropriate route exists, EIGRP queries its neighbors to discover an alternate route. These queries propagate until an alternate route is found. EIGRP sends incremental updates when the state of a destination changes, instead of sending the entire contents of the routing table. EIGRP ensures that only those routers needing the information are updated. This feature minimizes the bandwidth required for EIGRP packets.
EIGRP supports both internal and external routes. Internal routes originate within an EIGRP Autonomous System (AS). Therefore, a directly attached network that is configured to run EIGRP is considered an internal route and is propagated with this information throughout the AS. External routes are learned by another routing protocol or reside in the routing table as static routes. These routes are tagged individually with the identity of their origin.
The following topics describe the tasks you perform to create an EIGRP routing policy:
- Static Routing on Cisco IOS Routers
- RIP Routing on Cisco IOS Routers
- OSPF Routing on Cisco IOS Routers
- BGP Routing on Cisco IOS Routers
Defining EIGRP Routes
To configure an EIGRP routing policy, you must assign each autonomous system a number, which identifies the autonomous system to other routers. You then must select the networks to which routes will be created. In addition, you can select which interfaces should be passive. Unlike other routing protocols, passive interfaces in EIGRP neither send nor receive routing updates from their neighbors, resulting in the loss of their neighbor relationship.
When you configure EIGRP routing policies, you can also decide whether to enable auto-summarization, which greatly simplifies routing tables and the exchange of routing information by having many subnets represented by a single network entry.
- Defining EIGRP Interface Properties
- Redistributing Routes into EIGRP
- EIGRP Routing on Cisco IOS Routers
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > EIGRP from the Policy selector, then click the Setup tab in the work area.
- (Policy view) Select Router Platform > Routing > EIGRP from the Policy Type selector. Select an existing policy or create a new one, and then click the Setup tab.
The EIGRP Setup tab is displayed (see EIGRP Page—Setup Tab).
Step 2![]() On the EIGRP Setup tab, select an EIGRP route from the table, then click Edit, or click Add to create a route. The EIGRP Setup dialog box appears. See Table 67-6 for a description of the fields in this dialog box.
On the EIGRP Setup tab, select an EIGRP route from the table, then click Edit, or click Add to create a route. The EIGRP Setup dialog box appears. See Table 67-6 for a description of the fields in this dialog box.
Step 3![]() Enter the autonomous system number for the route. This number identifies the autonomous system to other routers.
Enter the autonomous system number for the route. This number identifies the autonomous system to other routers.
Step 4![]() Enter the addresses of the networks to include in the EIGRP route. You can use a combination of addresses and network/host objects; separate addresses with commas. Click Select to select network/host objects from a list of existing objects, or to create new network/host objects. For more information, see Specifying IP Addresses During Policy Definition.
Enter the addresses of the networks to include in the EIGRP route. You can use a combination of addresses and network/host objects; separate addresses with commas. Click Select to select network/host objects from a list of existing objects, or to create new network/host objects. For more information, see Specifying IP Addresses During Policy Definition.
Step 5![]() Enter the addresses of the passive interfaces, which are interfaces that should not send routing updates to their neighbors, if any. Enter the names of one or more interfaces or interface roles; separate addresses with commas. Click Select to select interface names or roles from a list of existing objects, or to create new interface role objects. For more information, see Specifying Interfaces During Policy Definition.
Enter the addresses of the passive interfaces, which are interfaces that should not send routing updates to their neighbors, if any. Enter the names of one or more interfaces or interface roles; separate addresses with commas. Click Select to select interface names or roles from a list of existing objects, or to create new interface role objects. For more information, see Specifying Interfaces During Policy Definition.
Step 6![]() (Optional) Select Auto-Summary to enable the auto summarization of subnet routes into network-level routes. Summarization reduces the size of routing tables, thereby reducing the complexity of the network.
(Optional) Select Auto-Summary to enable the auto summarization of subnet routes into network-level routes. Summarization reduces the size of routing tables, thereby reducing the complexity of the network.
Step 7![]() Click OK to save your definitions. The EIGRP route appears in the table displayed in the EIGRP Setup tab.
Click OK to save your definitions. The EIGRP route appears in the table displayed in the EIGRP Setup tab.
Defining EIGRP Interface Properties
You can optionally modify the default values of the following two interface properties in a selected EIGRP autonomous system:
The hello interval defines the interval between hello packets. Routing devices periodically send these packets to each other to dynamically learn of other routers on their directly attached networks. This information is used to discover neighbors and to learn when neighbors become unreachable or inoperative. By default, hello packets are sent every 5 seconds. The default interval for low speed (T1 or slower), nonbroadcast multiaccess (NBMA) media is every 60 seconds.
Split horizon is a feature that prevents route information from being sent back in the direction from which that information originated. If you enable split horizon on an interface (this is the default), update and query packets are not sent to destinations for which this interface is the next hop. This helps to prevent routing loops.
For example, as shown in Figure 67-1, if Router One is connected to Routers Two and Three through a single multipoint interface, and Router One learned about Network A from Router Two, Router One does not advertise the route to Network A over that same multipoint interface to Router Three. Router One assumes that Router Three would learn about Network A directly from Router Two.
Figure 67-1 EIGRP Split Horizon Example
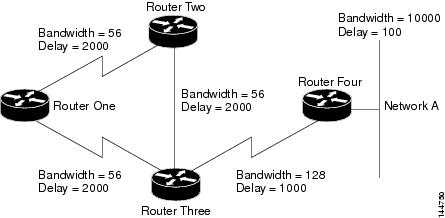
Split horizon is enabled by default on all EIGRP interfaces, because it typically optimizes communications among multiple routing devices. However, in certain cases with nonbroadcast networks (such as Frame Relay and SMDS), you might want to disable split horizon.
If you decide to disable split horizon on an EIGRP interface, keep the following in mind:
- In a hub-and-spoke network, you should disable split horizon only at the hub. This is because disabling split horizon on the spokes greatly increases EIGRP memory consumption on the hub router, as well as the amount of traffic generated on the spoke routers.
- Changing the split horizon setting on an interface resets all adjacencies with the EIGRP neighbors that are reachable over that interface.
- Define at least one EIGRP autonomous system. See Defining EIGRP Routes.
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > EIGRP from the Policy selector, then click the Interfaces tab in the work area.
- (Policy view) Select Router Platform > Routing > EIGRP from the Policy Type selector. Select an existing policy or create a new one, and then click the Interfaces tab.
The EIGRP Interfaces tab is displayed. See Table 67-7 for a description of the fields on this tab.
Step 2![]() On the EIGRP Interfaces tab, select an interface from the table, then click Edit, or click Add to create an interface definition. The EIGRP Interface dialog box appears. See Table 67-8 for a description of the fields in this dialog box.
On the EIGRP Interfaces tab, select an interface from the table, then click Edit, or click Add to create an interface definition. The EIGRP Interface dialog box appears. See Table 67-8 for a description of the fields in this dialog box.
Step 3![]() Select the AS number of the autonomous system whose interface properties you want to modify. See Defining EIGRP Routes for more information about defining an autonomous system.
Select the AS number of the autonomous system whose interface properties you want to modify. See Defining EIGRP Routes for more information about defining an autonomous system.
Step 4![]() Enter the name of the interface or interface role to define, or click Select to select an interface role from a list or to create a new one. For more information, see Specifying Interfaces During Policy Definition.
Enter the name of the interface or interface role to define, or click Select to select an interface role from a list or to create a new one. For more information, see Specifying Interfaces During Policy Definition.
Step 5![]() (Optional) In the Hello Interval field, modify the default interval between hello packets sent over the selected interfaces.
(Optional) In the Hello Interval field, modify the default interval between hello packets sent over the selected interfaces.
The default is 5 seconds for all interfaces, except for low-speed (T1 or less) NBMA media, for which the default interval is 60 seconds.
Step 6![]() (Optional) Deselect the Split Horizon check box to disable the split horizon feature. If you disable this feature, the selected interfaces can advertise a route out of the interface from which they learned the route.
(Optional) Deselect the Split Horizon check box to disable the split horizon feature. If you disable this feature, the selected interfaces can advertise a route out of the interface from which they learned the route.

Note![]() In general, we recommend that you not disable split horizon unless you are certain that your application requires the change to properly advertise routes. If you disable split horizon on a serial interface, and that interface is attached to a packet-switched network, you must disable split horizon for all routers and access servers in all relevant multicast groups on that network.
In general, we recommend that you not disable split horizon unless you are certain that your application requires the change to properly advertise routes. If you disable split horizon on a serial interface, and that interface is attached to a packet-switched network, you must disable split horizon for all routers and access servers in all relevant multicast groups on that network.
Step 7![]() Click OK to save your definitions locally on the client and close the dialog box. The interface definition appears in the table on the EIGRP Interfaces tab.
Click OK to save your definitions locally on the client and close the dialog box. The interface definition appears in the table on the EIGRP Interfaces tab.
Redistributing Routes into EIGRP
Redistribution refers to using a routing protocol, such as EIGRP, to advertise routes that are learned by some other means, such as a different routing protocol, static routes, or directly connected routes. For example, you can redistribute routes from the RIP routing protocol into your EIGRP autonomous system (AS). Redistribution is necessary in networks that operate in multiple-protocol environments and can be applied to all IP-based routing protocols.
- Define at least one EIGRP autonomous system. See Defining EIGRP Routes.
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > EIGRP from the Policy selector, then click the Redistribution tab in the work area.
- (Policy view) Select Router Platform > Routing > EIGRP from the Policy Type selector. Select an existing policy or create a new one, and then click the Redistribution tab.
The EIGRP Redistribution tab is displayed. See Table 67-9 for a description of the fields on this tab.
Step 2![]() On the EIGRP Redistribution tab, select a row from the EIGRP Redistribution Mappings table, then click Edit, or click Add to create a mapping. The EIGRP Redistribution Mapping dialog box appears. See Table 67-10 for a description of the fields in this dialog box.
On the EIGRP Redistribution tab, select a row from the EIGRP Redistribution Mappings table, then click Edit, or click Add to create a mapping. The EIGRP Redistribution Mapping dialog box appears. See Table 67-10 for a description of the fields in this dialog box.
Step 3![]() Select an existing EIGRP AS from the displayed list.
Select an existing EIGRP AS from the displayed list.
Step 4![]() Select the protocol whose routes you want to redistribute into the selected EIGRP AS.
Select the protocol whose routes you want to redistribute into the selected EIGRP AS.

Note![]() You can create a single mapping for each static route, RIP route, BGP AS, EIGRP AS, and OSPF process.
You can create a single mapping for each static route, RIP route, BGP AS, EIGRP AS, and OSPF process.
Step 5![]() (Optional) Under Metrics, modify the default metric (cost) of the redistributed routes by entering values in the fields used to calculate the metric. The metric determines the priority of the routes.
(Optional) Under Metrics, modify the default metric (cost) of the redistributed routes by entering values in the fields used to calculate the metric. The metric determines the priority of the routes.

Note![]() Entering a metric is optional, but if you do specify a value, you must enter values for all five parameters. You need not define metric values when redistributing one EIGRP process into another.
Entering a metric is optional, but if you do specify a value, you must enter values for all five parameters. You need not define metric values when redistributing one EIGRP process into another.
Step 6![]() Click OK to save your definitions locally on the client and close the dialog box. The redistribution mapping appears in the Redistribution Mapping table in the EIGRP Redistribution tab.
Click OK to save your definitions locally on the client and close the dialog box. The redistribution mapping appears in the Redistribution Mapping table in the EIGRP Redistribution tab.
EIGRP Routing Policy Page
Enhanced Interior Gateway Routing Protocol (EIGRP) is a scalable interior gateway protocol that provides extremely quick convergence times with minimal network traffic.
You can configure EIGRP routing policies from the following tabs on the EIGRP Routing page:
For more information, see EIGRP Routing on Cisco IOS Routers.
- (Device view) Select Platform > Routing > EIGRP from the Policy selector.
- (Policy view) Select Router Platform > Routing > EIGRP from the Policy Type selector. Right-click EIGRP to create a policy, or select an existing policy from the Shared Policy selector.
EIGRP Page—Setup Tab
Use the EIGRP Setup tab to view, create, edit, and delete EIGRP routes.
Go to the EIGRP Routing Policy Page, then click the Setup tab.
- Defining EIGRP Routes
- EIGRP Page—Interfaces Tab
- EIGRP Page—Redistribution Tab
- Table Columns and Column Heading Features
- Filtering Tables
|
|
|
|---|---|
The autonomous system number that identifies the autonomous system to other routers. |
|
The interfaces that neither send nor receive routing updates from their neighbors. |
|
Indicates whether auto summarization is activated on the selected route. |
|
Opens the EIGRP Setup Dialog Box. From here you can create an EIGRP route. |
|
Opens the EIGRP Setup Dialog Box. From here you can edit the selected EIGRP route. |
|
EIGRP Setup Dialog Box
Use the EIGRP Setup dialog box to add or edit EIGRP routes.
Go to the EIGRP Page—Setup Tab, then click the Add or Edit button beneath the table.
- Defining EIGRP Routes
- Specifying IP Addresses During Policy Definition
- Understanding Networks/Hosts Objects
EIGRP Page—Interfaces Tab
Use the EIGRP Interfaces tab to create, edit, and delete interface properties for selected EIGRP autonomous systems. This includes modifying the default hello interval and disabling split horizon.

Note![]() You can access the EIGRP Interfaces tab only after defining at least one EIGRP autonomous system in the Setup tab. See EIGRP Page—Setup Tab.
You can access the EIGRP Interfaces tab only after defining at least one EIGRP autonomous system in the Setup tab. See EIGRP Page—Setup Tab.
Go to the EIGRP Routing Policy Page, then click the Interfaces tab.
- Defining EIGRP Interface Properties
- EIGRP Page—Setup Tab
- EIGRP Page—Redistribution Tab
- Table Columns and Column Heading Features
- Filtering Tables
|
|
|
|---|---|
The EIGRP autonomous system number for which interface properties are defined. |
|
The interfaces related to the selected EIGRP autonomous system that have specially defined values. |
|
Indicates whether the split horizon feature is enabled or disabled for the selected interface. |
|
The defined interval between hello packets sent to neighboring routers. |
|
Opens the EIGRP Interface Dialog Box. From here you can create an EIGRP interface definition. |
|
Opens the EIGRP Interface Dialog Box. From here you can edit the selected EIGRP interface definition. |
|
Deletes the selected EIGRP interface definitions from the table. |
EIGRP Interface Dialog Box
Use the EIGRP Interface dialog box to add or edit interface definitions for a selected EIGRP autonomous system.
Go to the EIGRP Page—Interfaces Tab, then click the Add or Edit button beneath the table.
- Defining EIGRP Interface Properties
- Basic Interface Settings on Cisco IOS Routers
- Understanding Interface Role Objects
|
|
|
|---|---|
Selects the EIGRP autonomous system number whose interface properties you want to modify. For more information about EIGRP autonomous systems, see EIGRP Setup Dialog Box. |
|
Specifies the EIGRP interface you wish to configure. Enter the name of an interface or interface role, or click Select to select an interface role object from a list or to create a new one. |
|
The default interval between hello packets sent by the router to its neighbors. Routers send hello packets to each other to dynamically learn of other routers on their directly attached networks. Valid values range from 1 to 65535 seconds. The default is 5 seconds. |
|
When selected, the split horizon feature is used to prevent routing loops. When deselected, split horizon is disabled. When split horizon is disabled, the router can advertise a route out of the same interface through which it learned the route. Disabling split horizon is often useful when dealing with nonbroadcast networks, such as Frame Relay and SMDS. Note Changing the split horizon setting on an interface resets all adjacencies with EIGRP neighbors that are reachable over that interface. |
EIGRP Page—Redistribution Tab
Use the EIGRP Redistribution tab to create, edit, and delete EIGRP redistribution mappings.
Go to the EIGRP Routing Policy Page, then click the Redistribution tab.
- Redistributing Routes into EIGRP
- EIGRP Page—Setup Tab
- EIGRP Page—Interfaces Tab
- Table Columns and Column Heading Features
- Filtering Tables
|
|
|
|---|---|
The area ID of the EIGRP route into which other routes are being redistributed. |
|
The AS number or process ID of the route being redistributed. |
|
The minimum bandwidth of the path for the EIGRP route, as defined for the route metric. |
|
The mean latency of the path, as defined for the route metric. |
|
A value representing the estimated reliability of the path, as defined for the route metric. |
|
A value representing the effective load on the link, as defined for the route metric. |
|
The minimum MTU of the path, as defined for the route metric. |
|
When redistributing an OSPF process, indicates the types of OSPF routes that are being redistributed. |
|
Opens the EIGRP Redistribution Mapping Dialog Box. From here you can define EIGRP redistribution mappings. |
|
Opens the EIGRP Redistribution Mapping Dialog Box. From here you can edit the selected EIGRP redistribution mapping. |
|
Deletes the selected EIGRP redistribution mappings from the table. |
EIGRP Redistribution Mapping Dialog Box
Use the EIGRP Redistribution Mapping dialog box to add or edit the properties of an EIGRP redistribution mapping.
Go to the EIGRP Page—Redistribution Tab, then click the Add or Edit button beneath the table.

Note![]() You must create at least one EIGRP AS before you can access the EIGRP Redistribution dialog box. See EIGRP Page—Setup Tab.
You must create at least one EIGRP AS before you can access the EIGRP Redistribution dialog box. See EIGRP Page—Setup Tab.
|
|
|
|---|---|
The EIGRP AS into which other routes are being redistributed. You must select an ID number from the list of EIGRP autonomous systems defined in the EIGRP Page—Setup Tab. |
|
The routing protocol that is being redistributed:
|
|
– – – – – |
|
The default metric (cost) of the redistributed route. Metric parameters include:
|
OSPF Routing on Cisco IOS Routers
Open Shortest Path First (OSPF) is an interior gateway routing protocol that uses link states instead of distance vectors to distribute routing information within a single autonomous system (AS). OSPF propagates link-state advertisements (LSAs) instead of routing table updates, which allows OSPF networks to converge more quickly than RIP networks. You define areas to limit the number of LSAs that need to be propagated to changes that occur within the area.
A router that has interfaces in multiple OSPF areas is called an Area Border Router (ABR). An ABR uses LSAs to send information about available routes to other OSPF routers. A router that acts as a gateway to redistribute traffic between routers using OSPF and routers using other routing protocols is called an Autonomous System Boundary Router (ASBR). Any router can act as an ABR or ASBR.
The following topics describe the tasks you perform to create an OSPF routing policy:
- Defining OSPF Process Settings
- Defining OSPF Area Settings
- Redistributing Routes into OSPF
- Defining OSPF Interface Settings
- Static Routing on Cisco IOS Routers
- RIP Routing on Cisco IOS Routers
- EIGRP Routing on Cisco IOS Routers
- BGP Routing on Cisco IOS Routers
Defining OSPF Process Settings
You configure OSPF process parameters by specifying a process ID number, which identifies the OSPF process to other routers, and by deciding whether any interfaces should be passive. Passive interfaces do not send routing updates to their neighbors.
- Defining OSPF Area Settings
- Defining OSPF Interface Settings
- Redistributing Routes into OSPF
- OSPF Routing on Cisco IOS Routers
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > OSPF Process from the Policy selector, then click the Setup tab in the work area.
- (Policy view) Select Router Platform > Routing > OSPF Process from the Policy Type selector. Select an existing policy or create a new one, and then click the Setup tab.
The OSPF Process Setup tab is displayed. See Table 67-13 for a description of the fields on this tab.
Step 2![]() On the OSPF Process Setup tab, select an OSPF process from the table, then click Edit, or click Add to create a process. The OSPF Setup dialog box appears. See Table 67-14 for a description of the fields in this dialog box.
On the OSPF Process Setup tab, select an OSPF process from the table, then click Edit, or click Add to create a process. The OSPF Setup dialog box appears. See Table 67-14 for a description of the fields in this dialog box.
Step 3![]() Enter the process ID number in the field provided. The process ID defined here does not need to match the process ID on any other devices.
Enter the process ID number in the field provided. The process ID defined here does not need to match the process ID on any other devices.
Step 4![]() Define which interfaces should not send routing updates to its neighbors:
Define which interfaces should not send routing updates to its neighbors:
a.![]() Click Edit under Passive Interfaces to display the Edit Interfaces dialog box. Use this dialog box to define which interfaces should not send routing updates to its neighbors.
Click Edit under Passive Interfaces to display the Edit Interfaces dialog box. Use this dialog box to define which interfaces should not send routing updates to its neighbors.
b.![]() Enter the names of one or more interfaces or interface roles, or click Select to select an interface role from a list or to create a new one. For more information, see Specifying Interfaces During Policy Definition.
Enter the names of one or more interfaces or interface roles, or click Select to select an interface role from a list or to create a new one. For more information, see Specifying Interfaces During Policy Definition.
c.![]() Click OK to save your changes and return to the OSPF Setup dialog box.
Click OK to save your changes and return to the OSPF Setup dialog box.
Step 5![]() Click OK to save your definitions locally on the client and close the dialog box.
Click OK to save your definitions locally on the client and close the dialog box.
Defining OSPF Area Settings
You configure OSPF area settings by associating an area ID with a particular OSPF process, selecting the networks included in the area, and selecting the type of authentication used by the routers in the area.
Each OSPF process that you define should contain at least one defined area. If you define more than one area, one area must be area 0. This is called the backbone. All other areas must be physically connected to the backbone. This enables other areas to inject routing information into the backbone, which the backbone distributes to the remaining areas.
You must configure at least one OSPF process before defining OSPF area/network settings for that process.
- Defining OSPF Process Settings
- Defining OSPF Interface Settings
- Redistributing Routes into OSPF
- OSPF Routing on Cisco IOS Routers
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > OSPF Process from the Policy selector, then click the Area tab in the work area.
- (Policy view) Select Router Platform > Routing > OSPF Process from the Policy Type selector. Select an existing policy or create a new one, and then click the Area tab.
The OSPF Process Area tab is displayed. See Table 67-15 for a description of the fields on this tab.
Step 2![]() On the OSPF Process Area tab, select an OSPF area from the table, then click Edit, or click Add to create an area. The OSPF Area dialog box appears. See Table 67-16 for a description of the fields in this dialog box.
On the OSPF Process Area tab, select an OSPF area from the table, then click Edit, or click Add to create an area. The OSPF Area dialog box appears. See Table 67-16 for a description of the fields in this dialog box.
Step 3![]() Select a process ID from the displayed list.
Select a process ID from the displayed list.
Step 4![]() Enter an area ID to associate with the selected OSPF process.
Enter an area ID to associate with the selected OSPF process.
Step 5![]() Enter the addresses of the networks to include in the OSPF area. You can enter a combination of addresses and network/host objects, or click Select to select a network/host object from a list or to create a new one. For more information, see Specifying IP Addresses During Policy Definition.
Enter the addresses of the networks to include in the OSPF area. You can enter a combination of addresses and network/host objects, or click Select to select a network/host object from a list or to create a new one. For more information, see Specifying IP Addresses During Policy Definition.
Step 6![]() Select the authentication type to use in the OSPF area: MD5, clear text, or none. We recommend MD5 when security is of concern. Please note the following:
Select the authentication type to use in the OSPF area: MD5, clear text, or none. We recommend MD5 when security is of concern. Please note the following:
- The authentication type must be the same for all routers and access servers in the same area.
- Specifying clear-text authentication for an area sets the authentication to Type 1 (simple password). All routers on a network must use the same clear-text password to communicate with each other using OSPF.
- MD5 passwords need not be the same throughout an area, but they must be the same between neighbors.
- If you use interface authentication (see Defining OSPF Interface Settings), the authentication type used for the area must match the authentication type used for the interface.
Step 7![]() Click OK to save your definitions. The OSPF area appears in the table displayed on the OSPF Area tab.
Click OK to save your definitions. The OSPF area appears in the table displayed on the OSPF Area tab.
Redistributing Routes into OSPF
Redistribution refers to using a routing protocol, such as OSPF, to advertise routes that are learned by some other means, such as a different routing protocol, static routes, or directly connected routes. For example, you can redistribute routes from the RIP routing protocol into your OSPF domain. Redistribution is necessary in networks that operate in multiple-protocol environments and can be applied to all IP-based routing protocols.
Redistributing routes into OSPF from other routing protocols or from static routes causes these routes to become OSPF external routes (Type 1 or Type 2).
Defining OSPF Redistribution Mappings
When you define OSPF redistribution mappings, you must select the protocol to redistribute and the OSPF process into which routes from that protocol are redistributed. Additionally, you can manually define the metric, which determines the priority of the redistributed routes, and the type of external OSPF route to create, Type 1 or Type 2.
You can create multiple mappings to the same OSPF process. For example, you can redistribute both RIP and EIGRP routes into the same OSPF process. You can also redistribute routes from other OSPF processes.

Note![]() Redistribution into an OSPF Not-So-Stubby Area (NSSA) creates a special type of link-state advertisement (LSA) called type 7, which can exist only in an NSSA area. An NSSA autonomous system router (ASBR) generates this LSA, and an NSSA area border router (ABR) translates it into a type 5 LSA, which is propagated into the OSPF domain.
Redistribution into an OSPF Not-So-Stubby Area (NSSA) creates a special type of link-state advertisement (LSA) called type 7, which can exist only in an NSSA area. An NSSA autonomous system router (ASBR) generates this LSA, and an NSSA area border router (ABR) translates it into a type 5 LSA, which is propagated into the OSPF domain.
Type 1 versus Type 2 External Routes
Two types of OSPF external routes exist, Type 1 and Type 2. The difference between the two is related to how the cost (metric) of the route is calculated. The cost of a Type 1 route is the sum of the external cost and the internal cost used to reach that route. The cost of a Type 2 route is based on the external cost only. By default, external routes are defined as Type 2. However, a Type 1 route is always preferred over a Type 2 route to the same destination.
- Define at least one OSPF process. See Defining OSPF Process Settings.
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > OSPF Process from the Policy selector, then click the Redistribution tab in the work area.
- (Policy view) Select Router Platform > Routing > OSPF Process from the Policy Type selector. Select an existing policy or create a new one, and then click the Redistribution tab.
The OSPF Process Redistribution tab is displayed. See Table 67-17 for a description of the fields on this tab.
Step 2![]() On the OSPF Process Redistribution tab, select a row from the OSPF Redistribution Mappings table, then click Edit, or click Add to create a mapping. The OSPF Redistribution Mapping dialog box is displayed. See Table 67-18 for a description of the fields in this dialog box.
On the OSPF Process Redistribution tab, select a row from the OSPF Redistribution Mappings table, then click Edit, or click Add to create a mapping. The OSPF Redistribution Mapping dialog box is displayed. See Table 67-18 for a description of the fields in this dialog box.
Step 3![]() Select an existing OSPF process from the displayed list.
Select an existing OSPF process from the displayed list.
Step 4![]() Select the protocol whose routes you want to redistribute into the selected OSPF process.
Select the protocol whose routes you want to redistribute into the selected OSPF process.

Note![]() You can create a single mapping for each static route, RIP route, BGP AS, EIGRP AS, and OSPF process.
You can create a single mapping for each static route, RIP route, BGP AS, EIGRP AS, and OSPF process.
Step 5![]() (Optional) Modify the default metric (cost) of the redistributed routes. The metric determines the priority of the routes.
(Optional) Modify the default metric (cost) of the redistributed routes. The metric determines the priority of the routes.
Step 6![]() Select the Metric Type of external route to create, Type 1 or Type 2. The default is Type 2.
Select the Metric Type of external route to create, Type 1 or Type 2. The default is Type 2.
Step 7![]() (Optional) Select the Limit to Subnets check box to redistribute only subnetted routes. By default, this option is not selected.
(Optional) Select the Limit to Subnets check box to redistribute only subnetted routes. By default, this option is not selected.
Step 8![]() Click OK to save your definitions. The redistribution mapping appears in the Redistribution Mapping table on the OSPF Process Redistribution tab.
Click OK to save your definitions. The redistribution mapping appears in the Redistribution Mapping table on the OSPF Process Redistribution tab.
Defining OSPF Maximum Prefix Values
You can define a maximum number of prefixes (routes) that may be redistributed from other protocols or OSPF processes into a selected OSPF process. Setting a limit helps prevent the router from being flooded by too many redistributed routes. For example, without a defined maximum, flooding can occur when BGP is redistributed into OSPF.
When you define a maximum prefix value, you can decide whether to prevent additional routes from being redistributed once this maximum is reached, or whether to only issue a warning.
The redistribution limit applies to all IP redistributed prefixes, including summarized ones. The limit does not apply to default routes or prefixes that are generated as a result of type 7 to type 5 translations.
- Define at least one OSPF process. Define at least one OSPF process. See Defining OSPF Process Settings.
- Define at least one OSPF redistribution mapping. See Defining OSPF Redistribution Mappings.
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > OSPF Process from the Policy selector, then click the Redistribution tab in the work area.
- (Policy view) Select Router Platform > Routing > OSPF Process from the Policy Type selector. Select an existing policy or create a new one, and then click the Redistribution tab.
The OSPF Process Redistribution tab is displayed. See Table 67-17 for a description of the fields on this tab.
Step 2![]() On the OSPF Process Redistribution tab, select a row from the Max Prefix Mapping table, then click Edit, or click Add to create a definition. The Max Prefix Mapping dialog box appears. See Table 67-19 for a description of the fields in this dialog box.
On the OSPF Process Redistribution tab, select a row from the Max Prefix Mapping table, then click Edit, or click Add to create a definition. The Max Prefix Mapping dialog box appears. See Table 67-19 for a description of the fields in this dialog box.
Step 3![]() Select an existing OSPF process from the displayed list.
Select an existing OSPF process from the displayed list.
Step 4![]() In the Max Prefix field, enter the maximum number of routes that can be redistributed into the selected OSPF process.
In the Max Prefix field, enter the maximum number of routes that can be redistributed into the selected OSPF process.
Step 5![]() (Optional) Modify the default threshold percentage. When the number of redistributed routes reaches this threshold, a warning is issued. By default, the threshold value is 75% of the defined maximum prefix value.
(Optional) Modify the default threshold percentage. When the number of redistributed routes reaches this threshold, a warning is issued. By default, the threshold value is 75% of the defined maximum prefix value.
Step 6![]() (Optional) Select what should happen when the maximum prefix value is reached:
(Optional) Select what should happen when the maximum prefix value is reached:
- Enforce Maximum Route—Prevents additional routes from being redistributed to the selected process.
- Warning Only—Issues an additional warning, but allows route redistribution to continue even after the maximum prefix value is reached.

Note![]() Flooding can result if you allow route redistribution to continue after exceeding the maximum prefix value.
Flooding can result if you allow route redistribution to continue after exceeding the maximum prefix value.
Step 7![]() Click OK to save your definitions. The maximum prefix definition appears in the Maximum Prefix table on the OSPF Process Redistribution tab.
Click OK to save your definitions. The maximum prefix definition appears in the Maximum Prefix table on the OSPF Process Redistribution tab.
Defining OSPF Interface Settings
You can modify a variety of interface-specific OSPF parameters. This procedure describes how to define these parameters. For more information about a particular parameter, see the following topics:
- Understanding Interface Cost
- Understanding Interface Priority
- Disabling MTU Mismatch Detection
- Understanding OSPF Timer Settings
- Blocking LSA Flooding
- Understanding the OSPF Network Type
- Understanding OSPF Interface Authentication
- Defining OSPF Process Settings
- Defining OSPF Area Settings
- Redistributing Routes into OSPF
- OSPF Routing on Cisco IOS Routers
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > OSPF Interface from the Policy selector.
- (Policy view) Select Router Platform > Routing > OSPF Interface from the Policy Type selector. Select an existing policy or create a new one.
The OSPF Interface page is displayed. See Table 67-11 for a description of the fields on this page.
Step 2![]() On the OSPF Interface page, select an interface definition from the table, then click Edit, or click Add to create a definition. The OSPF Interface dialog box appears. See Table 67-12 for a description of the fields in this dialog box.
On the OSPF Interface page, select an interface definition from the table, then click Edit, or click Add to create a definition. The OSPF Interface dialog box appears. See Table 67-12 for a description of the fields in this dialog box.
Step 3![]() Enter the name of the interface or interface role to define, or click Select to select an interface role from a list or to create a new one. For more information, see Specifying Interfaces During Policy Definition.
Enter the name of the interface or interface role to define, or click Select to select an interface role from a list or to create a new one. For more information, see Specifying Interfaces During Policy Definition.
Step 4![]() Define interface authentication. The authentication type you select for the interface must match the authentication type you select for the area (see Defining OSPF Area Settings).
Define interface authentication. The authentication type you select for the interface must match the authentication type you select for the area (see Defining OSPF Area Settings).
All neighboring routers on the same network must have the same password to be able to exchange OSPF information. For more information, see Understanding OSPF Interface Authentication.
The key ID number can be associated with multiple passwords. This is an easy and secure way to migrate passwords. For example, to migrate from one password to another, configure a password under a different key ID, then remove the first key.

Tip The key ID number can be associated with multiple passwords. This is an easy and secure way to migrate passwords. For example, to migrate from one password to another, configure a password under a different key ID, then remove the first key.

Note![]() Do not use clear text authentication in OSPF packets for security purposes, because the unencrypted authentication key is sent in every packet. Use clear text authentication only when security is not an issue, for example, to ensure that misconfigured hosts do not participate in routing.
Do not use clear text authentication in OSPF packets for security purposes, because the unencrypted authentication key is sent in every packet. Use clear text authentication only when security is not an issue, for example, to ensure that misconfigured hosts do not participate in routing.
Step 5![]() (Optional) Under Properties, configure interface parameters as required. See Table 67-12 for information about each parameter.
(Optional) Under Properties, configure interface parameters as required. See Table 67-12 for information about each parameter.
Step 6![]() Click OK to save your definitions. The defined interfaces appear on the OSPF Interface page.
Click OK to save your definitions. The defined interfaces appear on the OSPF Interface page.
Step 7![]() Repeat the process to define interface-specific parameters on additional OSPF interfaces.
Repeat the process to define interface-specific parameters on additional OSPF interfaces.
Understanding Interface Cost
The cost of an OSPF interface is a metric representing the cost of sending a packet over that interface. By default, this cost is calculated using this formula:
10 8 / bandwidth [bits per second]
For example, if the bandwidth of a Fast Ethernet interface is 10 Mbps (equal to 10 7), the cost of sending packets over that interface is calculated as 10 8 /10 7 or 10. This formula establishes an inverse relationship between the bandwidth of an interface and its cost; the greater the bandwidth, the lower the cost.
Although cost is a calculated value, you can manually enter the cost of a selected interface.
Understanding Interface Priority
Routers that share a common segment are elected through the Hello protocol to be neighbors on that segment. Election occurs as soon as the routers see themselves listed in their neighbor’s hello packet. Adjacency is the next step. Adjacent routers are routers that proceed beyond the simple Hello exchange to a database exchange.
On each multiaccess (as opposed to point-to-point) segment, OSPF elects one router as the designated router (DR) for that segment. The DR acts as a central point of contact to minimize information exchange. Each router in the segment sends updates to the DR, which in turn relays the information to the other routers. A second router is elected as the backup designated router (BDR) in case the DR goes down.
DR and BDR election is performed via the Hello protocol. The router with the highest OSPF priority becomes the DR for that segment. The same process is then repeated for the BDR. In the case of a tie, the router with the higher router ID (RID) is elected. By default, each interface is given a priority of 1, but you can assign a higher priority to selected interfaces, as required.

Note![]() The priority setting does not apply to point-to-point, nonbroadcast interfaces.
The priority setting does not apply to point-to-point, nonbroadcast interfaces.
Disabling MTU Mismatch Detection
The MTU is the largest packet size that a particular interface can handle. If one router sends a DBD packet that is larger than the MTU setting on a neighboring router, the neighboring router ignores the packet. In many cases, an MTU mismatch causes the two routers to become stuck in exstart/exchange state, which prevents OSPF adjacency from being established. This is why it is important that all neighboring routers share the same MTU setting and that MTU mismatch detection be enabled.
You can, however, disable MTU mismatch detection. This is useful in cases where mismatch detection is preventing adjacency from taking place in an otherwise valid setup between two devices with different MTUs.
Blocking LSA Flooding
By default, OSPF floods new LSAs over all interfaces in the same area, except the interface on which the LSA arrives. Although some redundancy is desirable, too much redundancy can waste bandwidth. In certain topologies, such as full mesh, LSA flooding can destabilize the network because of excessive link and CPU usage. Therefore, you can block LSA flooding to selected interfaces on broadcast, nonbroadcast, and point-to-point networks.
Understanding OSPF Timer Settings
OSPF uses a series of timers during operation:
- Hello Interval—Determines how often an interface sends hello packets, which are used to acquire neighbors and act as indicators that the router is still functioning. The smaller the interval, the faster topological changes on the network are detected. However, a smaller interval also results in more traffic being sent over the interface. The hello interval must be the same on all routers and access servers on a specific network.
- Transmit Delay—Determines the delay before an LSA is flooded over the link. The transmit delay setting should take into account the transmission and propagation delays for the interface. These factors are particularly important when configuring low-speed and on-demand links.
- Retransmit Interval—Determines how long to wait before retransmitting an unacknowledged database description (DBD) packet to its neighbors. The retransmit interval setting should be low enough to prevent excessive retransmissions.

Note![]() You should increase the retransmit interval for serial lines and virtual links.
You should increase the retransmit interval for serial lines and virtual links.
- Dead Interval—Determines how long an interface should wait before declaring its neighbor to be down. This declaration is caused by an absence of hello packets from the neighbor during this interval. The dead interval setting must be the same for all routers and access servers on a specific network. By default, this interval is four times the hello interval.
Understanding the OSPF Network Type
You can manually configure the OSPF network type on an interface as either broadcast or nonbroadcast multiaccess (NBMA), regardless of the default media type. For example, you can use this feature to configure broadcast networks (such as Ethernet, Token Ring, and FDDI) as NBMA when your network contains routers that do not support multicast addressing. You can also configure NBMA networks (such as X.25, Frame Relay, and SMDS) as broadcast networks, which eliminates the need to configure neighbors.
Configuring NBMA networks as either broadcast or nonbroadcast assumes the existence of virtual circuits (VCs) from every router to every router (fully meshed network). If VCs do not exist between each router, due to cost constraints or the existence of an only partially meshed network, you can configure the OSPF network type as point-to-multipoint. An OSPF point-to-multipoint interface is defined as a numbered point-to-point interface having one or more neighbors. It creates multiple host routes.
If you use the point-to-multipoint network type, routing between two routers that are not directly connected go through a third router that has VCs to both routers. You do not need to configure neighbors when using this feature. OSPF point-to-multipoint networks have the following benefits compared to NBMA and point-to-point networks:
- Point-to-multipoint is easier to configure because it consumes only one IP subnet and does not require neighbor configuration or designated router election.
- It costs less because it does not require a fully meshed topology.
- It is more reliable because it maintains connectivity in the event of VC failure.

Note![]() For point-to-multipoint, broadcast networks, you can optionally define neighbors, in which case you should specify the cost to each neighbor. For point-to-multipoint, nonbroadcast networks, you must identify neighbors, but specifying a cost to each neighbor is optional. In both cases, you define neighbors using FlexConfig. See Chapter 7, “Managing FlexConfigs” for more information.
For point-to-multipoint, broadcast networks, you can optionally define neighbors, in which case you should specify the cost to each neighbor. For point-to-multipoint, nonbroadcast networks, you must identify neighbors, but specifying a cost to each neighbor is optional. In both cases, you define neighbors using FlexConfig. See Chapter 7, “Managing FlexConfigs” for more information.
Understanding OSPF Interface Authentication
You define neighbor authentication settings for OSPF interfaces by selecting the interfaces and selecting an authentication type, either MD5 or clear text.
When you use MD5 authentication, neighboring routers must share the same password. When you use clear-text authentication, all routers on the network using OSPF must share the same password.
Whenever you configure an interface with a new key, the router sends multiple copies of the same packet, each authenticated by different keys. The router stops sending duplicate packets when it detects that all of its neighbors have adopted the new key.

Note![]() You should use authentication with all routing protocols when possible, because attackers can use route redistribution between OSPF and other protocols (such as RIP) to subvert routing information.
You should use authentication with all routing protocols when possible, because attackers can use route redistribution between OSPF and other protocols (such as RIP) to subvert routing information.
OSPF Interface Policy Page
Use the OSPF Interface page to view, create, edit, and delete interface-specific OSPF settings. For more information, see Defining OSPF Interface Settings.
- (Device view) Select Platform > Routing > OSPF Interface from the Policy selector.
- (Policy view) Select Router Platform > Routing > OSPF Interface from the Policy Type selector. Right-click OSPF Interface to create a policy, or select an existing policy from the Shared Policy selector.
|
|
|
|---|---|
The name of an interface (as defined by an interface role) on which OSPF is enabled. |
|
The type of OSPF neighbor authentication enabled for the selected interface. |
|
The identification number of the authentication key used for MD5 authentication. |
|
The cost of sending packets over the selected interface, if this value is different from the cost as normally calculated. |
|
Indicates whether Maximum Transmission Rate (MTU) detection is disabled on the selected interface. |
|
Indicates whether link-state advertisement (LSA) flooding is disabled on the selected interface. |
|
The interval between hello packets (in seconds) sent over this interface. |
|
The amount of time OSPF waits (in seconds) before flooding an LSA over the link. |
|
The interval between LSA retransmissions (in seconds) over the selected interface. |
|
The interval OSPF waits (in seconds) before declaring a neighboring router dead because of an absence of hello packets. |
|
The network type configured for the selected interface, if it differs from the default medium. |
|
Opens the OSPF Interface Dialog Box. From here you can define the properties of an OSPF interface. |
|
Opens the OSPF Interface Dialog Box. From here you can edit the properties of the selected OSPF interface. |
|
Deletes the selected OSPF interface definitions from the table. |
OSPF Interface Dialog Box
Use the OSPF Interface dialog box to add or edit the properties of OSPF interfaces.
Go to the OSPF Interface Policy Page, then click the Add or Edit button beneath the table.
- Defining OSPF Interface Settings
- OSPF Routing on Cisco IOS Routers
- Basic Interface Settings on Cisco IOS Routers
- Understanding Interface Role Objects
|
|
|
|---|---|
The OSPF interface to configure. Enter the name of an interface or interface role, or click Select to select the object from a list or to create a new one. |
|
Type—The authentication type used by the selected interface:
Note The authentication type used on an interface must match the authentication type defined for the area. Note Use plain text authentication only when security is not an issue, for example, to ensure that misconfigured hosts do not participate in routing. The identification number of the authentication key. This number must be shared with all other devices sending updates to, and receiving updates from, the selected device. Valid values range from 1 to 255.
When using clear text, the key can include any continuous string of characters that can be entered from the keyboard (up to 8 bytes). When using MD5, the key can include alphanumeric characters only (up to 16 bytes). |
|
The cost of sending packets over this interface. A value entered here overrides the default calculated cost (10 8 /bandwidth in bits per second). |
|
The default priority of the interface. The priority is used to determine which routers become the designated router (DR) and backup designated router (BDR) for that segment. The higher the number, the higher the priority. The default priority is 1. Valid values range from 0 to 255. Note To exclude the interface from election as DR or BDR, assign a priority of 0. Configure router priority only for interfaces to multiaccess networks, not point-to-point networks. |
|
When selected, ignores MTU mismatches between neighboring routers. When deselected, MTU mismatch detection is enabled. Note Typically, this option is not used, because it can cause routers to become stuck in exstart/exchange state, which prevents OSPF adjacency from being established. |
|
When selected, blocks link-state advertisement (LSA) flooding to the selected interface. When deselected, LSA flooding is permitted. Note We recommend that you enable this option on fully-meshed networks. This option is not available for point-to-multipoint networks. |
|
The default interval (in seconds) between hello packets sent over the selected interface. These packets are used by neighboring routers to confirm the router sending the packets is still operating. Valid values range 1 to 65535 seconds. Note The hello interval must be the same for all routers and access servers in the network. |
|
The amount of time OSPF waits (in seconds) before flooding an LSA over the link. The default is 1 second. Valid values range from 1 to 65535 seconds. Note When you configure slow links or on-demand links that queue traffic before sending it in bursts, we recommend that you take these link delays into account when defining this value. |
|
The interval between LSA retransmissions (in seconds) over the selected interface. The default is 5 seconds. Valid values range from 1 to 65535 seconds. Note We recommend that you increase this value for serial lines and virtual links. |
|
The interval (in seconds) after which an interface declares its neighbor dead if no hello packets are received. Valid values range from 1 to 655335 seconds. Note The value of the dead interval is typically the hello interval value multiplied by 4. The dead interval must be the same for all routers and access servers in the network. |
|
When selected, enables you to select a network type that differs from the default medium used by the interface. When deselected, the network type is equivalent to the default medium used by the interface. For nonbroadcast multiaccess (NBMA) networks (such as ATM and Frame Relay), options are:
Note Another option for NBMA networks is to configure neighbors manually using FlexConfigs. See Understanding FlexConfig Policies and Policy Objects. For broadcast networks (such as Ethernet, Token Ring, and FDDI), you can select:
|
OSPF Process Policy Page
OSPF is an interior gateway routing protocol that uses link states instead of distance vectors for path selection. OSPF propagates link-state advertisements (LSAs) instead of routing table updates, which enables OSPF networks to converge quickly.
You can configure OSPF process policies from the following tabs on the OSPF Process page:
For more information, see OSPF Routing on Cisco IOS Routers.

Note![]() For more information about OSPF interface policies, see OSPF Interface Policy Page.
For more information about OSPF interface policies, see OSPF Interface Policy Page.
- (Device view) Select Platform > Routing > OSPF Process from the Policy selector.
- (Policy view) Select Router Platform > Routing > OSPF Process from the Policy Type selector. Right-click OSPF Process to create a policy, or select an existing policy from the Shared Policy selector.
OSPF Process Page—Setup Tab
Use the OSPF Process Setup tab to create, edit, and delete OSPF processes. This includes selecting those interfaces that will remain passive, which means that they will not send routing updates to their neighbors. You can create as many processes for each router as required.
Go to the OSPF Process Policy Page, then click the Setup tab.
- Defining OSPF Process Settings
- OSPF Process Page—Area Tab
- OSPF Process Page—Redistribution Tab
- OSPF Interface Policy Page
- Table Columns and Column Heading Features
- Filtering Tables
|
|
|
|---|---|
The process ID that identifies the OSPF routing process to other routers. |
|
Opens the OSPF Setup Dialog Box. From here you can define an OSPF process. |
|
Opens the OSPF Setup Dialog Box. From here you can edit the selected OSPF process. |
|
OSPF Setup Dialog Box
Use the OSPF Setup dialog box to add or edit an OSPF process.
Go to the OSPF Process Page—Setup Tab, then click the Add or Edit button beneath the table.
|
|
|
|---|---|
The process ID number for the OSPF process. This number identifies the OSPF process to other routers. It does not need to match the process ID on other devices. Valid values are from 1 to 65535. |
|
The interfaces that do not send updates to their routing neighbors. Click Edit to display the Edit Interfaces Dialog Box—OSPF Passive Interfaces. From here you can define these interfaces. Note When you make an interface passive, OSPF suppresses the sending of hello packets to neighboring routers. The interface will continue to receive routing updates, however. |
Edit Interfaces Dialog Box—OSPF Passive Interfaces
When you configure an OSPF routing policy on a Cisco IOS router, use the Edit Interfaces dialog box to specify which interfaces will not send updates to their routing neighbors. Separate multiple names or roles with commas. Click Select to select interface names or roles from a list of existing objects, or to create new interface role objects.
Go to the OSPF Setup Dialog Box, then click the Edit button in the Passive Interfaces field.
OSPF Process Page—Area Tab
Use the OSPF Area tab to create, edit, and delete the areas and networks contained in each OSPF process. This includes selecting the type of authentication used by each area.
Go to the OSPF Process Policy Page, then click the Area tab.
- Defining OSPF Area Settings
- OSPF Process Page—Setup Tab
- OSPF Process Page—Redistribution Tab
- OSPF Interface Policy Page
- Table Columns and Column Heading Features
- Filtering Tables
|
|
|
|---|---|
The process ID that identifies the OSPF routing process to other routers. |
|
The authentication type used by the area—MD5, clear text, or none. |
|
Open the OSPF Area Dialog Box. From here you can define an OSPF area. |
|
Opens the OSPF Area Dialog Box. From here you can edit the selected OSPF area. |
|
OSPF Area Dialog Box
Use the OSPF Area dialog box to add or edit the properties of an OSPF area. You should define at least one area for each OSPF process (see OSPF Setup Dialog Box), but deployment will not fail if you do not.
Go to the OSPF Process Page—Area Tab, then click the Add or Edit button beneath the table.
- Defining OSPF Area Settings
- Specifying IP Addresses During Policy Definition
- Understanding Networks/Hosts Objects
|
|
|
|---|---|
The process ID associated with the OSPF area. The list contains the OSPF processes defined in the OSPF Process Page—Setup Tab. |
|
The area ID number associated with the selected process. Valid values range from 0 to 4294967295. |
|
The networks to add to the OSPF area. Enter one or more network addresses or network/host objects, or click Select to select the object from a list or to create a new one. |
|
The type of authentication used for the area:
Note The authentication type must be the same for all routers and access servers in an area. |
OSPF Process Page—Redistribution Tab
Use the OSPF Process Redistribution tab to create, edit, and delete OSPF redistribution mappings. This includes defining the maximum number of routes that can be redistributed into OSPF from other protocols or other OSPF processes.
Go to the OSPF Process Policy Page, then click the Redistribution tab.
- Redistributing Routes into OSPF
- OSPF Process Page—Setup Tab
- OSPF Process Page—Area Tab
- OSPF Interface Policy Page
- Table Columns and Column Heading Features
- Filtering Tables
|
|
|
|---|---|
The ID of the OSPF routing domain into which other routes are being redistributed. |
|
The AS number or process ID of the route that is being redistributed. |
|
When redistributing an OSPF process, indicates the types of OSPF routes that are being redistributed. |
|
The value that determines the priority of the redistributed route. |
|
The external link type associated with the default route advertised into the OSPF routing domain. |
|
Indicates whether routes that are subnetted are also being redistributed. |
|
Opens the OSPF Redistribution Mapping Dialog Box. From here you can define OSPF redistribution mappings. |
|
Opens the OSPF Redistribution Mapping Dialog Box. From here you can edit the selected OSPF redistribution mapping. |
|
Deletes the selected redistribution mappings from the table. |
|
The ID of the OSPF routing domain for which a maximum prefix values has been defined. |
|
The maximum number of prefixes (routes) that may be redistributed to the selected OSPF process. |
|
The percentage of the maximum prefix value that acts as a threshold for triggering a warning message. |
|
Indicates whether redistribution to this OSPF process will stop when the maximum is reached, or whether only a warning is displayed. |
|
Opens the OSPF Max Prefix Mapping Dialog Box. From here you can define maximum prefix values for OSPF processes. |
|
Opens the OSPF Max Prefix Mapping Dialog Box. From here you can edit the maximum prefix value defined for the selected OSPF process. |
|
OSPF Redistribution Mapping Dialog Box
Use the OSPF Redistribution Mapping dialog box to add or edit the properties of an OSPF redistribution mapping.
Go to the OSPF Process Page—Redistribution Tab, then click the Add or Edit button beneath the Redistribution Mapping table.

Note![]() You must create at least one OSPF process before you can access the OSPF Redistribution dialog box. See OSPF Process Page—Setup Tab.
You must create at least one OSPF process before you can access the OSPF Redistribution dialog box. See OSPF Process Page—Setup Tab.
|
|
|
|---|---|
The OSPF process into which other routes are being redistributed. You must select a process ID number from the list of OSPF processes defined in the OSPF Process Page—Setup Tab. |
|
The routing protocol that is being redistributed:
|
|
– – – – – |
|
The external link type that is associated with the route being redistributed into the OSPF routing domain: |
|
OSPF Max Prefix Mapping Dialog Box
Use the OSPF Max Prefix Mapping dialog box to add or edit the maximum number of routes that can be redistributed into an OSPF process.
Go to the OSPF Process Page—Redistribution Tab, then click the Add or Edit button beneath the Prefix Mapping table.
|
|
|
|---|---|
The OSPF process into which other routes are being redistributed. The list contains the OSPF processes defined in the OSPF Process Page—Setup Tab. |
|
The maximum number of prefixes (routes) that can be redistributed into the selected OSPF process. Limiting the number of redistributed routes helps prevent the router from being flooded by an excessive number of routes. |
|
The percentage of the maximum prefix value that acts as a threshold for triggering warning messages. The default is 75%. Note This warning is triggered whether or not the Warning-Only check box is selected. |
|
The action to take when the maximum number of redistributed routes is reached: |
RIP Routing on Cisco IOS Routers
Routing Information Protocol (RIP) is an Interior Gateway Protocol (IGP) that was created for use in small, homogeneous networks. RIP is a distance-vector protocol that sends routing-update messages at regular intervals (in a process called advertising) and whenever the network topology changes. When a router receives a routing update that includes changes to an entry, it updates its routing table to reflect the new route. If a router does not receive an update from another router for 180 seconds or more, it marks the routes served by the non-updating router as being unusable. If there is still no update after 240 seconds, the router removes all routing table entries for the non-updating router. Routing information is exchanged using UDP packets.
RIP evaluates routes by measuring the number of hops (the number of routers traversed) from the source to the destination. A directly connected network has a metric of zero. The maximum hop count allowed by RIP is 15. Any route with a hop count greater than 15 is considered unreachable.
Security Manager supports RIP version 2 only, which is described in RFC 1723. RIP 2 improves on the original RIP by enabling RIP messages to carry more information, which permits the use of a simple authentication mechanism (clear text or MD5) to secure table updates. RIP 2 also supports subnet masks, a critical feature that was not available in the original version of RIP.
The following topics describe the tasks you perform to create a RIP routing policy:
- Defining RIP Setup Parameters
- Defining RIP Interface Authentication Settings
- Redistributing Routes into RIP
- Static Routing on Cisco IOS Routers
- OSPF Routing on Cisco IOS Routers
- EIGRP Routing on Cisco IOS Routers
- BGP Routing on Cisco IOS Routers
Defining RIP Setup Parameters
You configure RIP setup parameters by selecting the networks to include in the route and deciding whether any interfaces should be passive. These interfaces do not send routing updates to their neighbors. Additionally, you can enable auto-summarization, which reduces the size and complexity of the routing tables the router must maintain.
- Defining RIP Interface Authentication Settings
- Redistributing Routes into RIP
- RIP Routing on Cisco IOS Routers
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > RIP from the Policy selector, then click the Setup tab in the work area.
- (Policy view) Select Router Platform > Routing > RIP from the Policy Type selector. Select an existing policy or create a new one, and then click the Setup tab.
The RIP Setup tab is displayed (see RIP Page—Setup Tab).
Step 2![]() Enter the addresses of the directly connected networks whose interfaces are to receive RIP updates. You can use a combination of addresses and network/host objects; separate addresses with commas. Click Select to select network/host objects from a list of existing objects, or to create new network/host objects. For more information, see Specifying IP Addresses During Policy Definition.
Enter the addresses of the directly connected networks whose interfaces are to receive RIP updates. You can use a combination of addresses and network/host objects; separate addresses with commas. Click Select to select network/host objects from a list of existing objects, or to create new network/host objects. For more information, see Specifying IP Addresses During Policy Definition.
Step 3![]() Enter the addresses of the passive interfaces, which are interfaces that should not send routing updates to their neighbors, if any. These interfaces continue to receive RIP routing broadcasts, which they use to populate their routing tables. Enter the names of one or more interfaces or interface roles; separate addresses with commas. Click Select to select interface names or roles from a list of existing objects, or to create new interface role objects. For more information, see Specifying Interfaces During Policy Definition.
Enter the addresses of the passive interfaces, which are interfaces that should not send routing updates to their neighbors, if any. These interfaces continue to receive RIP routing broadcasts, which they use to populate their routing tables. Enter the names of one or more interfaces or interface roles; separate addresses with commas. Click Select to select interface names or roles from a list of existing objects, or to create new interface role objects. For more information, see Specifying Interfaces During Policy Definition.
Step 4![]() (Optional) Select the Auto Summary check box to enable the automatic summarization of subnet routes into network-level routes. Summarization reduces the size of routing tables, thereby reducing the complexity of the network.
(Optional) Select the Auto Summary check box to enable the automatic summarization of subnet routes into network-level routes. Summarization reduces the size of routing tables, thereby reducing the complexity of the network.
Disable automatic summarization when you perform routing between disconnected subnets. When automatic summarization is turned off, subnets are advertised.
Defining RIP Interface Authentication Settings
You define neighbor authentication settings for RIP interfaces by selecting the interfaces and then selecting an authentication type, either MD5 or clear text.
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > RIP from the Policy selector, then click the Authentication tab in the work area.
- (Policy view) Select Router Platform > Routing > RIP from the Policy Type selector. Select an existing policy or create a new one, and then click the Authentication tab.
The RIP Authentication tab is displayed. See Table 67-21 for a description of the fields on this tab.
Step 2![]() On the RIP Authentication tab, select an interface definition from the table, then click Edit, or click Add to create a definition. The RIP Authentication dialog box appears. See Table 67-22 for a description of the fields in this dialog box.
On the RIP Authentication tab, select an interface definition from the table, then click Edit, or click Add to create a definition. The RIP Authentication dialog box appears. See Table 67-22 for a description of the fields in this dialog box.
Step 3![]() Enter the name of the interface or interface role for which authentication is defined, or click Select to select an interface role from a list or to create a new one. For more information, see Specifying Interfaces During Policy Definition.
Enter the name of the interface or interface role for which authentication is defined, or click Select to select an interface role from a list or to create a new one. For more information, see Specifying Interfaces During Policy Definition.
Step 4![]() Define interface authentication (MD5 or clear text).
Define interface authentication (MD5 or clear text).

Note![]() We do not recommend that you use clear text authentication in RIP packets, because the unencrypted authentication key is sent in every packet. Use plain text authentication only when security is not an issue, for example, to ensure that misconfigured hosts do not participate in routing.
We do not recommend that you use clear text authentication in RIP packets, because the unencrypted authentication key is sent in every packet. Use plain text authentication only when security is not an issue, for example, to ensure that misconfigured hosts do not participate in routing.
Step 5![]() Click OK to save your definitions locally on the client and close the dialog box. The defined interface appears on the RIP Authentication tab.
Click OK to save your definitions locally on the client and close the dialog box. The defined interface appears on the RIP Authentication tab.
Redistributing Routes into RIP
Redistribution refers to using a routing protocol, such as RIP, to advertise routes that are learned by some other means, such as a different routing protocol, static routes, or directly connected routes. For example, you can redistribute routes from the OSPF routing protocol into your RIP route. Redistribution is necessary in networks that operate in multiple-protocol environments and can be applied to all IP-based routing protocols.
When you redistribute into RIP, you can maintain the original metric of the route by redistributing it transparently.
- Define at least one RIP route. See Defining RIP Setup Parameters.
- Defining RIP Setup Parameters
- Defining RIP Interface Authentication Settings
- RIP Routing on Cisco IOS Routers
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > RIP from the Policy selector, then click the Redistribution tab in the work area.
- (Policy view) Select Router Platform > Routing > RIP from the Policy Type selector. Select an existing policy or create a new one, and then click the Redistribution tab.
The RIP Redistribution tab is displayed. See Table 67-23 for a description of the fields on this tab.
Step 2![]() On the RIP Redistribution tab, select a row from the RIP Redistribution Mappings table, then click Edit, or click Add to create a mapping. The RIP Redistribution Mapping dialog box appears. See Table 67-24 for a description of the fields in this dialog box.
On the RIP Redistribution tab, select a row from the RIP Redistribution Mappings table, then click Edit, or click Add to create a mapping. The RIP Redistribution Mapping dialog box appears. See Table 67-24 for a description of the fields in this dialog box.
Step 3![]() Select the protocol whose routes you want to redistribute into RIP.
Select the protocol whose routes you want to redistribute into RIP.

Note![]() You can create a single mapping for each static route, BGP AS, EIGRP AS, and OSPF process.
You can create a single mapping for each static route, BGP AS, EIGRP AS, and OSPF process.
Step 4![]() Define the metric (cost) of the redistributed routes by doing one of the following:
Define the metric (cost) of the redistributed routes by doing one of the following:
- Select the Default Metric check box, then enter the default metric of the redistributed routes. The metric determines the priority of the routes.
- Select the Transparent check box to maintain the original metric of the routes being redistributed into RIP.
Step 5![]() Click OK to save your definitions locally on the client and close the dialog box. The redistribution mapping appears in the Redistribution Mapping table on the RIP Redistribution tab.
Click OK to save your definitions locally on the client and close the dialog box. The redistribution mapping appears in the Redistribution Mapping table on the RIP Redistribution tab.
RIP Routing Policy Page
RIP is a distance-vector routing protocol that uses hop count as the metric for path selection. Security Manager supports RIP version 2 only, which includes support for neighbor authentication when routing updates are exchanged.
You can configure RIP routing policies from the following tabs on the RIP Routing page:
For more information, see RIP Routing on Cisco IOS Routers.
- (Device view) Select Platform > Routing > RIP from the Policy selector.
- (Policy view) Select Router Platform > Routing > RIP from the Policy Type selector. Right-click RIP to create a policy, or select an existing policy from the Shared Policy selector.
RIP Page—Setup Tab
Use the RIP Setup tab to create, edit, and delete RIP routes.
Go to the RIP Routing Policy Page, then click the Setup tab.
- Defining RIP Setup Parameters
- RIP Page—Authentication Tab
- RIP Page—Redistribution Tab
- Specifying IP Addresses During Policy Definition
- Understanding Networks/Hosts Objects
RIP Page—Authentication Tab
Use the RIP Authentication tab to view, create, edit, and delete the neighbor authentication settings of RIP interfaces.
Go to the RIP Routing Policy Page, then click the Authentication tab.
- Defining RIP Interface Authentication Settings
- RIP Page—Setup Tab
- RIP Page—Redistribution Tab
- RIP Routing Policy Page
- Table Columns and Column Heading Features
- Filtering Tables
|
|
|
|---|---|
The name of an interface (as defined by an interface role) on which RIP is enabled. |
|
The type of RIP neighbor authentication that is enabled for the selected interface role—clear text or MD5. |
|
The identification number of the authentication key used for MD5 authentication. |
|
Opens the RIP Authentication Dialog Box. From here you can define authentication for an additional RIP interface. |
|
Opens the RIP Authentication Dialog Box. From here you can edit the authentication properties of the selected RIP interface. |
|
Deletes the selected authentication definitions from the table. |
RIP Authentication Dialog Box
Use the RIP Authentication dialog box to add or edit the neighbor authentication properties of RIP interfaces.
Go to the RIP Page—Authentication Tab, then click the Add or Edit button beneath the table.
RIP Page—Redistribution Tab
Use the RIP Redistribution tab to view, create, edit, and delete redistribution settings when performing redistribution into an RIP routing domain.

Note![]() You must define RIP setup parameters before you can access the RIP Redistribution tab. See RIP Page—Setup Tab.
You must define RIP setup parameters before you can access the RIP Redistribution tab. See RIP Page—Setup Tab.
Go to the RIP Routing Policy Page, then click the Redistribution tab.
|
|
|
|---|---|
The autonomous system (AS) number or process ID of the route being redistributed. |
|
The value that determines the priority of the redistributed route. |
|
When redistributing an OSPF process, indicates which types of OSPF routes are being redistributed. |
|
Opens the RIP Redistribution Mapping Dialog Box. From here you can define a RIP redistribution mapping. |
|
Opens the RIP Redistribution Mapping Dialog Box. From here you can edit the selected RIP redistribution mapping. |
|
Deletes the selected redistribution mappings from the table. |
RIP Redistribution Mapping Dialog Box
Use the RIP Redistribution Mapping dialog box to add or edit the properties of an RIP redistribution mapping.
Go to the RIP Page—Redistribution Tab, then click the Add or Edit button beneath the table.
|
|
|
|---|---|
The routing protocol that is being redistributed:
|
|
– – – – – |
|
Establishes a default value for the redistributed route. Valid values range from 0 to 16. |
|
When selected, maintains the original metric of the route being redistributed. When deselected, the value specified in the Metric field is used. |
Static Routing on Cisco IOS Routers
You can configure static routing policies to ensure that the router correctly forwards packets to their destination when a route cannot be built dynamically. By default, static routes have a default administrative distance of 1 (implying a directly connected network), which causes them to override any dynamic routes discovered for the same host or network. You can, however, define a larger administrative distance to a static route so that it does not take precedence over a corresponding dynamic route.
For example, EIGRP routes have a default administrative distance of 5. To have a static route that can be overridden by an EIGRP route, you must specify an administrative distance greater than 5. This feature is useful when you define the static route as a “floating” route, which is inserted into the routing table only when the preferred route is unavailable.

Tip![]() When you use the static route as a backup, “floating” route, specify the interface through which the next hop IP address can be reached instead of entering a specific IP address. Otherwise, the “floating” route is not inserted in the routing table if the primary link fails. For more information, see Specifying a Next Hop IP Address for Static Routes on Cisco.com at this URL: http://www.cisco.com/en/US/tech/tk365/technologies_tech_note09186a00800ef7b2.shtml
When you use the static route as a backup, “floating” route, specify the interface through which the next hop IP address can be reached instead of entering a specific IP address. Otherwise, the “floating” route is not inserted in the routing table if the primary link fails. For more information, see Specifying a Next Hop IP Address for Static Routes on Cisco.com at this URL: http://www.cisco.com/en/US/tech/tk365/technologies_tech_note09186a00800ef7b2.shtml
Defining Static Routes
To define a static route, you must define the IP address (and optionally, the metric) of the hop gateway to which the router forwards packets destined to the selected host or network. You can define as many static routes as required.
- Static Routing on Cisco IOS Routers
- RIP Routing on Cisco IOS Routers
- OSPF Routing on Cisco IOS Routers
- EIGRP Routing on Cisco IOS Routers
- BGP Routing on Cisco IOS Routers
Step 1![]() Do one of the following:
Do one of the following:
- (Device view) Select Platform > Routing > Static Routing from the Policy selector.
- (Policy view) Select Router Platform > Routing > Static Routing from the Policy Type selector. Select an existing policy or create a new one.
The Static Routing page is displayed. See Table 67-25 for a description of the fields on this page.
Step 2![]() On the Static Routing page, select a static route from the table, then click Edit, or click Add to create a route. The Static Routing dialog box appears. See Table 67-26 for a description of the fields in this dialog box.
On the Static Routing page, select a static route from the table, then click Edit, or click Add to create a route. The Static Routing dialog box appears. See Table 67-26 for a description of the fields in this dialog box.
Step 3![]() (Optional) Select the Use as Default Route check box to make this route the default route for all unknown outbound packets.
(Optional) Select the Use as Default Route check box to make this route the default route for all unknown outbound packets.
Step 4![]() In the Prefix field, enter the address for the destination network, or click Select to select a network/host object from a list or to create a new one. For more information, see Specifying IP Addresses During Policy Definition.
In the Prefix field, enter the address for the destination network, or click Select to select a network/host object from a list or to create a new one. For more information, see Specifying IP Addresses During Policy Definition.
Step 5![]() Select a forwarding option:
Select a forwarding option:
- To define the router interface that forwards packets to the remote network, select Forwarding Interface and enter the name of an interface or interface role. You can click Select to select an interface role from a list or to create a new one. See Understanding Interface Role Objects and Selecting Objects for Policies.
- To specify the next hop router that receives and forwards packets to the remote network, select Forwarding IP, then enter the address in the field provided, or click Select to select a network/host object from a list or to create a new one. For more information, see Specifying IP Addresses During Policy Definition.
Step 6![]() (Optional) In the Distance Metric field, enter the number of hops to the next hop address for this router. This metric identifies the priority of the static route. If two routing entries specify the same network, the route with the lower metric value (that is, the lower cost) is given a higher priority and is selected.
(Optional) In the Distance Metric field, enter the number of hops to the next hop address for this router. This metric identifies the priority of the static route. If two routing entries specify the same network, the route with the lower metric value (that is, the lower cost) is given a higher priority and is selected.
If no value is specified, the default is 1, which implies a directly connected network.
Step 7![]() (Optional) Select the Permanent route check box to prevent this static route entry from being deleted, even in cases in which the interface is shut down or the router cannot communicate with the next router.
(Optional) Select the Permanent route check box to prevent this static route entry from being deleted, even in cases in which the interface is shut down or the router cannot communicate with the next router.
Step 8![]() Click OK to save your definitions locally on the client and close the dialog box. The static route appears in the table on the Static Routing page.
Click OK to save your definitions locally on the client and close the dialog box. The static route appears in the table on the Static Routing page.
Static Routing Policy Page
Use the Static Routing page to create, edit, and delete static routes. For more information, see Defining Static Routes.
- (Device view) Select Platform > Routing > Static Routing from the Policy selector.
- (Policy view) Select Router Platform > Routing > Static Routing from the Policy Type selector. Right-click Static Routing to create a policy, or select an existing policy from the Shared Policy selector.
|
|
|
|---|---|
Indicates whether the static route is the default route for unknown packets being forwarded by this router. |
|
The IP address or the interface name associated with the gateway router that is the next hop address for this router. |
|
The number of hops from the gateway IP to the destination. The metric determines the priority of this route. The fewer the hops, the higher the priority assigned to the route, based on lower costs. When two routing entries specify the same network, the entry with the lower metric (that is, the higher priority) is selected. |
|
Indicates whether the static route is defined as a permanent route, which means that it will not be removed even if the interface is shut down or if the router is unable to communicate with the next router. |
|
Opens the Static Routing Dialog Box. From here you can create a static route. |
|
Opens the Static Routing Dialog Box. From here you can edit the selected static route. |
|
Static Routing Dialog Box
Use the Static Routing dialog box to add or edit static routes.
Go to the Static Routing Policy Page, then click the Add or Edit button beneath the table.
 Feedback
Feedback