- New and Changed Information
- Preface
- Overview
- Managing User Accounts
- Configuring VSD
- Configuring AAA
- Configuring RADIUS
- Configuring TACACS+
- Configuring SSH
- Configuring Telnet
- Configuring an IP ACL
- Configuring a MAC ACL
- Configuring Port Security
- Configuring DHCP Snooping
- Configuring Dynamic ARP Inspection
- Configuring IP Source Guard
- Security Configuration Limits
- Index
Cisco Nexus 1000V Security Configuration Guide, Release 4.0(4)SV1(2)
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- December 11, 2009
Chapter: Configuring VSD
Configuring VSD
This chapter describes how to configure VSD and includes the following topics:
•![]() Information About Virtual Service Domain
Information About Virtual Service Domain
Information About Virtual Service Domain
A virtual service domain (VSD) allows you to classify and separate traffic for network services, such as firewalls, traffic monitoring, and those in support of compliance goals such as Sarbanes Oxley.
Service Virtual Machine
A service VM (SVM) provides the specialized service like firewall, deep packet inspection (application aware networking), or monitoring. Each Service VM has three virtual interfaces:
There is no source MAC learning on these interfaces. Each SVM creates a secure VSD. Interfaces within the VSD are shielded by the SVM.
Port Profiles
A VSD is the collection of interfaces that are guarded by the SVM providing the security service. Any traffic coming into the VSD or going out of the VSD has to go through the SVM.
Traffic that both originates and terminates within the same VSD need not be routed through the SVM as it is considered to be safe.
A VSD is formed by creating the following port profiles:
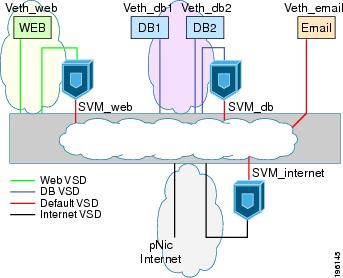
In Figure 3-1, a single VEM takes the place of vswitches; the SVMs define the following VSDs;
Figure 3-1 Virtual Service Domain (VSD) Example
Guidelines and Limitations
Virtual Service Domain has the following configuration guidelines and limitations:
•![]() To prevent traffic latency, VSD should only be used for securing traffic.
To prevent traffic latency, VSD should only be used for securing traffic.
•![]() Up to 6 VSDs can be configured per host and up to 64 on the VSM.
Up to 6 VSDs can be configured per host and up to 64 on the VSM.
•![]() Up to 214 interfaces per VSD are supported on a single host, and 2048 interfaces on the VSM.
Up to 214 interfaces per VSD are supported on a single host, and 2048 interfaces on the VSM.
•![]() Vmotion is not supported for the SVM and should be disabled.
Vmotion is not supported for the SVM and should be disabled.
•![]() To avoid network loops following a VSM reload or a network disruption, control and packet VLANS must be disabled in all port profiles of the Service VMs.
To avoid network loops following a VSM reload or a network disruption, control and packet VLANS must be disabled in all port profiles of the Service VMs.
•![]() If a port profile without a service port is configured on an SVM, it will flood the network with packets.
If a port profile without a service port is configured on an SVM, it will flood the network with packets.
•![]() When configuring a port profile on an SVM, first bring the SVM down, This prevents a port-profile that is mistakenly configured without a service port from flooding the network with packets. The SVM can be returned to service after the configuration is complete and verified.
When configuring a port profile on an SVM, first bring the SVM down, This prevents a port-profile that is mistakenly configured without a service port from flooding the network with packets. The SVM can be returned to service after the configuration is complete and verified.
Configuring VSD
This section includes the following procedures:
•![]() Configuring an Inside or Outside VSD Port Profile
Configuring an Inside or Outside VSD Port Profile
•![]() Configuring a Member VSD Port Profile
Configuring a Member VSD Port Profile
Configuring an Inside or Outside VSD Port Profile
Use this procedure to configure the port-profiles that define the connections going into and out of the SVM.
BEFORE YOU BEGIN
Before beginning this procedure, you must know or do the following:
•![]() You are logged in to the CLI in EXEC mode.
You are logged in to the CLI in EXEC mode.
•![]() You have taken the SVM out of service to prevent any configuration errors from flooding the network. Once the configuration is complete and verified, you can bring the SVM back into service.
You have taken the SVM out of service to prevent any configuration errors from flooding the network. Once the configuration is complete and verified, you can bring the SVM back into service.
•![]() If you do not configure a service-port, the SVM will come up as a regular VM, flooding the network with packets.
If you do not configure a service-port, the SVM will come up as a regular VM, flooding the network with packets.
•![]() Selected VLAN filtering is not supported in this configuration. The default should be used instead, which allows all VLANs on the port.
Selected VLAN filtering is not supported in this configuration. The default should be used instead, which allows all VLANs on the port.
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() port-profile name
port-profile name
3. ![]() switchport mode trunk
switchport mode trunk
4. ![]() switchport trunk allowed vlan vlanID
switchport trunk allowed vlan vlanID
5. ![]() virtual-service-domain name
virtual-service-domain name
6. ![]() no shut
no shut
7. ![]() vmware port-group pg-name
vmware port-group pg-name
8. ![]() service-port {inside | outside} [default-action {drop | forward}]
service-port {inside | outside} [default-action {drop | forward}]
9. ![]() state enabled
state enabled
10. ![]() show virtual-service-domain name
show virtual-service-domain name
11. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Configuring a Member VSD Port Profile
Use this procedure to configure the VSD port profile where individual members reside.
BEFORE YOU BEGIN
Before beginning this procedure, you must know or do the following:
•![]() You are logged in to the CLI in EXEC mode.
You are logged in to the CLI in EXEC mode.
•![]() Do not configure a member VSD port profile on an SVM.
Do not configure a member VSD port profile on an SVM.
A member VSD port profile does not have a service port, and will flood the network with packets if configured on an SVM.
SUMMARY STEPS
1. ![]() config t
config t
2. ![]() port-profile name
port-profile name
3. ![]() switchport access vlan vlanID
switchport access vlan vlanID
4. ![]() switchport trunk allowed vlan vlanID
switchport trunk allowed vlan vlanID
5. ![]() virtual-service-domain name
virtual-service-domain name
6. ![]() no shut
no shut
7. ![]() state enabled
state enabled
8. ![]() show virtual-service-domain name
show virtual-service-domain name
9. ![]() copy running-config startup-config
copy running-config startup-config
DETAILED STEPS
Verifying the Configuration
To display the VSD configuration, use the following commands:
For detailed information about command output for these commands, see the Cisco Nexus 1000V Command Reference, Release 4.0(4)SV1(2).
Example 3-1 show vsd
n1000v# module vem 3 execute vemcmd show vsd
ID Def_Act ILTL OLTL NMLTL State Member LTLs
1 DROP 48 49 4 ENA 54,52,55,53
2 FRWD 50 51 0 ENA
vsim-cp# module vem 3 execute vemcmd show vsd ports
LTL IfIndex VSD_ID VSD_PORT_TYPE
48 1b020000 1 INSIDE
49 1b020010 1 OUTSIDE
50 1b020020 2 INSIDE
51 1b020030 2 OUTSIDE
52 1b020040 1 REGULAR
53 1b020050 1 REGULAR
54 1b020060 1 REGULAR
55 1b020070 1 REGULAR
n1000v#
Example 3-2 show virtual-service-domain brief
n1000v# show virtual-service-domain brief
Name default action in-ports out-ports mem-ports
vsd1 drop 1 1 4
vsd2 forward 1 1 0
vsim-cp# sho virtual-service-domain interface
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
Name Interface Type Status
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
vsd1 Vethernet1 Member Active
vsd1 Vethernet2 Member Active
vsd1 Vethernet3 Member Active
vsd1 Vethernet6 Member Active
vsd1 Vethernet7 Inside Active
vsd1 Vethernet8 Outside Active
vsd2 Vethernet9 Inside Active
vsd2 Vethernet10 Outside Active
vsim-cp# show virtual-service-domain name vsd1
Default Action: drop
___________________________
Interface Type
___________________________
Vethernet1 Member
Vethernet2 Member
Vethernet3 Member
Vethernet6 Member
Vethernet7 Inside
Vethernet8 Outside
n1000v#
Configuration Example
The following example shows how to configure VSD.
port-profile vsd1_member
vmware port-group
switchport access vlan 315
virtual-service-domain vsd1
no shutdown
state enabled
port-profile svm_vsd1_in
vmware port-group
switchport mode trunk
switchport trunk allowed vlan 310-319
virtual-service-domain vsd1
service-port inside default-action drop
no shutdown
state enabled
port-profile svm_vsd1_out
vmware port-group
switchport mode trunk
switchport trunk allowed vlan 310-319
virtual-service-domain vsd1
service-port outside default-action drop
no shutdown
Default Setting
The following table lists the default setting for Telnet.
|
|
|
|---|---|
service-port default-action |
Forward. |
switchport trunk allowed vlan |
All |
Additional References
For additional information related to VSD configuration, see the following:
Related Documents
Standards
|
|
|
|---|---|
No new or modified standards are supported by this feature, and support for existing standards has not been modified by this feature. |
— |
Feature History
This section provides the VSD release history.
|
|
|
|
|---|---|---|
VSD |
4.0(4)SV1(2) |
This feature was introduced. |

 Feedback
Feedback