- New and Changed Information
- Preface
- Overview
- Tools
- Installation
- Licenses
- Upgrade
- High Availability
- VSM and VEM Modules
- L3Sec
- Ports
- Port Profiles
- Port Channels and Trunking
- Layer 2 Switching
- VLANs
- Private VLANs
- NetFlow
- ACLs
- Quality of Service
- SPAN
- Multicast IGMP
- DHCP, DAI, and IPSG
- Storm Control
- System
- Before Contacting Technical Support
- Network Segmentation Manager
- VXLANs
- VDP
- Cisco TrustSec
- vCenter Plug-in
- Ethanalyzer
- 802.1X
Cisco Nexus 1000V Troubleshooting Guide, Release 5.2(1)SV3(4.1)
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- May 25, 2018
Chapter: Layer 2 Switching
Layer 2 Switching
This chapter describes how to identify and resolve problems that relate to Layer 2 switching and includes the following sections:
Information About Layer 2 Ethernet Switching
The Cisco Nexus1000V is a distributed Layer 2 virtual switch that extends across many virtualized hosts.
It consists of two components:
- The Virtual Supervisor Module (VSM), which is also known as the control plane (CP). The VSM acts as the supervisor and contains the Cisco CLI, configuration, and high-level features.
- The Virtual Ethernet Module (VEM), which is also known as the data plane (DP). The VEM acts as a line card and runs in each virtualized server to handle packet forwarding and other localized functions.
Port Model
This section includes the following topics:
Viewing Ports from the VEM
The Cisco Nexus1000V differentiates between virtual and physical ports on each of the VEMs. Figure 12-1 shows how ports on the Cisco Nexus1000V switch are bound to physical and virtual VMware ports within a VEM.
On the virtual side of the switch, three layers of ports are mapped together:
- Virtual NICs—Three types of Virtual NICs are in VMware. The virtual NIC (vnic) is part of the VM and represents the physical port of the host that is plugged into the switch. The virtual kernel NIC (VTEP) is used by the hypervisor for management, VMotion, iSCSI, network file system (NFS), and other network access needed by the kernel. This interface carries the IP address of the hypervisor itself and is also bound to a virtual Ethernet port. The vswif (not shown) appears only in CoS-based systems and is used as the VMware management port. Each type maps to a virtual Ethernet port within the Cisco Nexus1000V.
- Virtual Ethernet Ports (VEth)—A vEth port is a port on the Cisco Nexus 1000V. The Cisco Nexus 1000V has a flat space of vEth ports 0..N. The virtual cable plugs into these vEth ports that are moved to the host running the VM.
Virtual Ethernet ports are assigned to port groups.
- Local Virtual Ethernet Ports (lveth)—Each host has a number of local vEth ports. These ports are dynamically selected for vEth ports that are needed on the host.
These local ports do not move and are addressable by the module/port number method.
On the physical side of the switch, from bottom to top, is the following:
- Each physical NIC in VMware is represented by an interface called a vmnic. The vmnic number is allocated during VMware installation, or when a new physical NIC is installed, and remains the same for the life of the host.
- Each uplink port on the host represents a physical interface. It acts like an lveth port, but because physical ports do not move between hosts, the mapping is 1:1 between an uplink port and a vmnic.
- Each physical port added to the Cisco Nexus1000V switch appears as a physical Ethernet port, just as it would on a hardware-based switch.
The uplink port concept is handled entirely by VMware and is used to associate port configuration with vmnics. There is no fixed relationship between the uplink number and vmnic number. These can be different on different hosts and can change throughout the life of the host. On the VSM, the Ethernet interface number, such as ethernet 2/4, is derived from the vmnic number, not the uplink number.
Viewing Ports from the VSM
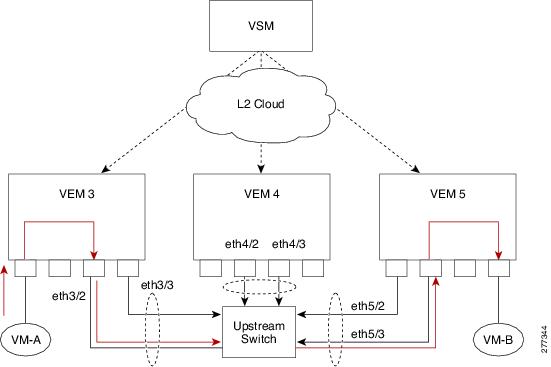
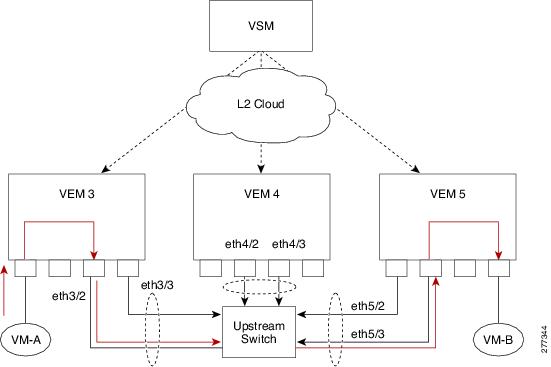
Figure 12-2 shows the VSM view ports.
Port Types
The following types of ports are available:
–![]() VNICs of a Virtual Machine on the ESX host.
VNICs of a Virtual Machine on the ESX host.
- Eths (physical Ethernet interfaces)—Correspond to the Physical NICs on the ESX host.
- Po (port channel interfaces)—The physical NICs of an ESX Host can be bundled into a logical interface. This logical bundle is referred to as a port channel interface.
For more information about Layer 2 switching, see the Cisco Nexus 1000V Layer 2 Switching Configuration Guide.
Layer 2 Switching Problems
This section describes how to troubleshoot Layer 2 problems and lists troubleshooting commands. This section includes the following topics:
- Verifying a Connection Between VEM Ports
- Verifying a Connection Between VEMs
- Isolating Traffic Interruptions
Verifying a Connection Between VEM Ports
You can verify a connection between two vEth ports on a VEM.
Step 1![]() View the state of the VLANs associated with the port. If the VLAN associated with a port is not active, the port may be down. In this case, you must create the VLAN and activate it.
View the state of the VLANs associated with the port. If the VLAN associated with a port is not active, the port may be down. In this case, you must create the VLAN and activate it.
Step 2![]() View the state of the ports on the VSM.
View the state of the ports on the VSM.
Step 3![]() Display the ports that are present on the VEM, their local interface indices, VLAN, type (physical or virtual), port mode and port name.
Display the ports that are present on the VEM, their local interface indices, VLAN, type (physical or virtual), port mode and port name.
switch# module vem module-number execute vemcmd show port
The key things to look for in the output are as follows:
- State of the port.
- CBL.
- Mode.
- Attached device name.
- The LTL of the port that you are trying to troubleshoot. It will help you to identify the interface quickly in other VEM commands where the interface name is not displayed.
- Make sure that the state of the port is up. If not, verify the configuration of the port on the VSM.
Step 4![]() View the VLANs and port lists on a particular VEM.
View the VLANs and port lists on a particular VEM.
switch# module vem module-number execute vemcmd show bd
If you are trying to verify that a port belongs to a particular VLAN, make sure that you see the port name or LTL in the port list of that VLAN.
Verifying a Connection Between VEMs
You can verify a connection between vEth ports on two separate VEMs.
Step 1![]() Check if the VLAN associated with the port is created on the VSM.
Check if the VLAN associated with the port is created on the VSM.
Step 2![]() Check if the ports are up in the VSM.
Check if the ports are up in the VSM.
Step 3![]() On the VEM, check if the CBL state of the two ports is set to the value of 1 for forwarding (active).
On the VEM, check if the CBL state of the two ports is set to the value of 1 for forwarding (active).
switch# module vem 3 execute vemcmd show port
Step 4![]() On the VEM, check if the two vEth ports are listed in the flood list of the VLAN with which they are trying to communicate.
On the VEM, check if the two vEth ports are listed in the flood list of the VLAN with which they are trying to communicate.
switch# module vem 3 execute vemcmd show bd
Step 5![]() Verify that the uplink switch to which the VEMs are connected is carrying the VLAN to which the ports belong.
Verify that the uplink switch to which the VEMs are connected is carrying the VLAN to which the ports belong.
Step 6![]() Find out the port on the upstream switch to which the PNIC (that is supposed to be carrying the VLAN) on the VEM is connected to.
Find out the port on the upstream switch to which the PNIC (that is supposed to be carrying the VLAN) on the VEM is connected to.
The PNIC (Eth 5/2) is connected to swordfish-6k-2 on port Gig1/38.
Step 7![]() Log in to the upstream switch and make sure that the port is configured to allow the VLAN that you are looking for.
Log in to the upstream switch and make sure that the port is configured to allow the VLAN that you are looking for.
switch# show running-config interface gigabitEthernet 1/38
As this output shows, VLANs 1,60-69, 231-233 are allowed on the port. If a particular VLAN is not in the allowed VLAN list, make sure to add it to the allowed VLAN list of the port.
Isolating Traffic Interruptions
You can isolate the cause for no traffic passing across VMs on different VEMs.
Step 1![]() In the output of the show port-profile name command, verify the following information:
In the output of the show port-profile name command, verify the following information:
- The control and packet VLANs that you configured are present (in the example, these are 3002 and 3003).
- If the physical NIC in your configuration carries the VLAN for the VM, that VLAN is also present in the allowed VLAN list.
Step 2![]() Inside the VM, verify that the Ethernet interface is up.
Inside the VM, verify that the Ethernet interface is up.
If not, delete that NIC from the VM, and add another NIC.
Step 3![]() Using any sniffer tool, verify that ARP requests and responses are received on the VM interface.
Using any sniffer tool, verify that ARP requests and responses are received on the VM interface.
Step 4![]() On the upstream switch, look for the association between the IP and MAC address:
On the upstream switch, look for the association between the IP and MAC address:
Step 5![]() You have completed this procedure.
You have completed this procedure.
Layer 2 Switching Troubleshooting Commands
You can use the commands in this section to troubleshoot problems related to the Layer 2 MAC address configuration.
|
|
|
|---|---|
Displays the MAC address table to verify all MAC addresses on all VEMs controlled by the VSM. |
|
Displays the interface on which the MAC address specified is learned or configured. |
|
Displays the static MAC address of vEthernet interfaces in case a VEM physical port learns a dynamic MAC addrress and the packet source is in another VEM on the same VSM. |
|
show vlan [ all-ports | brief | id vlan-id | name name | dot1q tag native ] |
Displays VLAN information as specified. See Example 12-4 on page 12-9 . |
Displays a table of interface states. |
|
On the VEM, displays the port state on a particular VEM. |
|
For the specified VEM, displays its VLANs and their port lists. |
|
For the specified VEM, displays the VLAN state on a trunk port. |
|
For the specified VEM, displays the VLAN forwarding table for a specified VLAN. |
|
Displays the MAC addresses and the burn-in MAC address for an interface. |
Example 12-1 show mac address-table Command

Note![]() The Cisco Nexus 1000V MAC address table does not display multicast MAC addresses.
The Cisco Nexus 1000V MAC address table does not display multicast MAC addresses.

Tip The “Module” indicates the VEM on which this MAC address is seen.
The “N1KV Internal Port” refers to an internal port created on the VEM. This port is used for control and management of the VEM and is not used for forwarding packets.
Example 12-2 show mac address-table address Command

Tip This command shows all interfaces on which a MAC is learned dynamically.
In this example, the same MAC appears on Eth3/3 and Eth4/3.
Total MAC Addresses: 1
Example 12-3 show mac address-table static | inc veth Command
Example 12-4 show vlan Command

Tip This command shows the state of each VLAN created on the VSM.
Example 12-5 show interface brief Command
Example 12-6 module vem module- number execute vemcmd show port Command

Tip Look for the state of the port.
Example 12-7 module vem module-numbe r execute vemcmd show bd Command

Tip If a port belongs to a particular VLAN, the port name or LTL should be in the port list for the VLAN.
BD 1, vdc 1, vlan 1, 2 ports
Portlist:
16 vmnic1
17 vmnic2
Portlist:
BD 110, vdc 1, vlan 110, 1 ports
Portlist:
16 vmnic1
Portlist:
16 vmnic1
Portlist:
16 vmnic1
Portlist:
16 vmnic1
Portlist:
16 vmnic1
Portlist:
10 l22
16 vmnic1
Example 12-8 module vem module-number execute vemcmd show trunk Command

Tip If a VLAN is active on a port, its CBL state should be 1.
If a VLAN is blocked, its CBL state is 0.
Example 12-9 module vem module-number execute vemcmd show l2 Command
Dynamic MAC 00:50:56:bb:49:d9 LTL 16 timeout 0
Dynamic MAC 00:02:3d:42:e3:03 LTL 10 timeout 0
Troubleshooting Microsoft NLB Unicast Mode
Microsoft Network Load Balancing (MS-NLB) is a clustering technology offered by Microsoft as part of the Windows server operating systems. Clustering enables a group of independent servers to be managed as a single system for higher availability, easier manageability, and greater scalability.
For more information about Microsoft Network Load Balancing, see this URL:
http://technet.microsoft.com/en-us/library/bb742455.aspx

Note![]() Access to third-party websites identified in this document is provided solely as a courtesy to customers and others. Cisco Systems, Inc. and its affiliates are not in any way responsible or liable for the functioning of any third-party website, or the download, performance, quality, functioning, or support of any software program or other item accessed through the website, or any damages, repairs, corrections, or costs arising out of any use of the website or any software program or other item accessed through the website. Cisco's End User License Agreement does not apply to the terms and conditions of use of a third-party website or any software program or other item accessed through the website.
Access to third-party websites identified in this document is provided solely as a courtesy to customers and others. Cisco Systems, Inc. and its affiliates are not in any way responsible or liable for the functioning of any third-party website, or the download, performance, quality, functioning, or support of any software program or other item accessed through the website, or any damages, repairs, corrections, or costs arising out of any use of the website or any software program or other item accessed through the website. Cisco's End User License Agreement does not apply to the terms and conditions of use of a third-party website or any software program or other item accessed through the website.
Limitations and Restrictions
A syslog is generated if one of the following configurations exists when you try to disable automatic static MAC learning for MS-NLB because they do not support this feature:
Disabling Automatic Static MAC Learning on a vEthernet Interface
You must disable automatic static MAC learning before you can successfully configure NLB on a vEthernet (vEth) interface.
In interface configuration mode enter the following commands:
In port profile configuration mode enter the following commands:
Checking Status on a VSM
If the NLB unicast mode configuration does not function, check the status of the Virtual Supervisor Module (VSM).
Confirm that the no mac auto-static-learn command is listed in the vEth and/or port profile configurations.
Step 1![]() In interface configuration mode, generate the VSM status.
In interface configuration mode, generate the VSM status.
Step 2![]() In port profile configuration mode, generate the VSM status.
In port profile configuration mode, generate the VSM status.
Checking the Status on a VEM
If the NLB unicast mode configuration does not function, check the status of the Virtual Ethernet Module (VEM). Check the following:
- Confirm that the MS-NLB vEths are disabled.
- Confirm that the MS-NLB shared-MAC (starting with 02:BF) is not listed in the Layer 2 (L2) MAC table.
Step 1![]() Generate the VEM status.
Generate the VEM status.
Step 2![]() Generate the Layer 2 MAC address table for VLAN 59.
Generate the Layer 2 MAC address table for VLAN 59.
Bridge domain 15 brtmax 4096, brtcnt 6, timeout 300
Flags: P - PVLAN S - Secure D - Drop
Configuring MS NLB for Multiple VM NICs in the Same Subnet
When MS NLB VMs have more than one port on the same subnet, a request is flooded, which causes both ports to receive it. The server cannot manage this situation.
As a workaround for this situation, enable Unknown Unicast Flood Blocking (UUFB).
Enabling UUFB
To enable UUFB, enter these configuration commands, one on each line. At the end, press Cntl-Z.
This configuration conceals the requests from the non-NLB ports and allows the system to function as it expected.
Disabling UUFB for VMs That Use Dynamic MAC Addresses
Issues might occur for VMs that use dynamic MAC addresses, other than those MAC addresses assigned by VMware. For ports that host these types of VMs, disable UUFB. To disable UUFB, enter the following commands:
Troubleshooting BPDU Guard
BPDU Guard is one of the Spanning Tree Protocol (STP) enhancements. This feature enhances switch network reliability, manageability, and security. It prevent loops and broadcast radiation. We recommend that you enable BPDU guard on access ports so that any end user devices on these ports that have BPDU guard enabled cannot influence the topology. Any malfunctioning device connected to a virtual Ethernet port can flood the Layer 2 network with unwanted BPDUs and causes STP to break down. When you enable BPDU guard on the access-ports, it shuts down the port in the event that it receives a BPDU. To bring up a port disabled by BDPU guard, you must remove the device from the network and then restart the port by entering the shut/no shut command.
BPDU Guard Troubleshooting Commands
You can use the commands in this section to troubleshoot problems related to the Layer 2 MAC address configuration.
|
|
|
|---|---|
Displays the license edition. You must have the ADVANCED 3.0 license for BPDU guard to be enabled in DAOX. |
|
Example 12-10 show switch edition Command
Dynamic 00:00:5e:00:01:0a 51 0
Example 12-11 show spanning-tree bpduguard info Command
Example 12-12 show run interface name Command
Example 12-13 show interface virtual spanning-tree bpduguard status Command
Example 12-14 show system internal cdm info port-profile name Command
Example 12-15 show system internal cdm info interface name Command
Example 12-16 vemcmd show card Command
Example 12-17 vemcmd show port bpdugard Command
 Feedback
Feedback