The following are
restrictions for Flexible NetFlow:
-
Flexible Netflow Version 5 Export Protocol and Autonomous System Number feature is not supported on the C9500-12Q, C9500-16X,
C9500-24Q, C9500-40X models of the Cisco Catalyst 9500 Series Switches.
-
Flexible NetFlow is not supported on the Layer 2 port-channel interface, but is supported on the Layer 2 port-channel member
ports.
-
Flexible NetFlow is supported on the Layer 3 port-channel interfaces and member ports but not on both at the same time for
the same traffic type and direction.
-
Traditional NetFlow accounting is not supported.
-
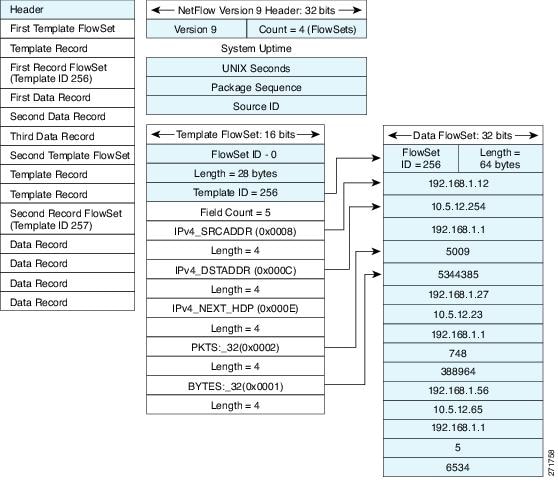
Flexible NetFlow Version 9 and Version 10 export formats are supported. However, if you have not configured the export protocol,
Version 9 export format is applied by default.
-
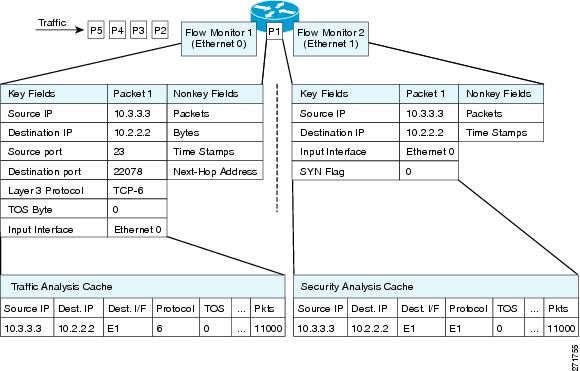
For wired Application Visibility and Control (AVC) traffic, only one flow monitor can be configured on one or more Layer 2
or Layer 3 physical interfaces on the system.
-
Flexible NetFlow and NBAR cannot be configured together at the same time on the same interface.
-
Layer 2, IPv4, and IPv6 traffic types are supported. Multiple flow monitors of different traffic types can be applied for
a given interface and direction. Multiple flow monitors of same traffic type cannot be applied for a given interface and direction.
-
The device does not support tunnels and SVI interfaces; however Layer 2 and Layer 3 physical interfaces and VLAN configuration
mode are supported.
-
The following NetFlow table sizes are supported:
|
Trim Level
|
Ingress NetFlow Table
|
Egress NetFlow Table
|
|
Network Essentials
|
32 K
|
32 K
|
|
Network Advantage
|
32 K
|
32 K
|
-
Depending on the switch type, a switch will have one or two forwarding ASICs. The capacities listed in the above table are
on a per-Core/per-ASIC basis.
-
The switch can support upto four ASICs. Each ASIC has two cores. Each core has 32K ingress and 32K egress entries, whereas
each TCAM can handle up to 1024 ingress and 2048 egress entries.
-
The NetFlow tables are on separate compartments and cannot be combined. Depending on which core processed the packet, the
flows will be created in the table in the corresponding core.
-
NetFlow hardware implementation supports four hardware samplers. You can select a sampler rate from 1 out of 2 to 1 out of
1024. Both — random and deterministic — sampling modes are supported.
-
NetFlow hardware uses hash tables internally. Hash collisions can occur in the hardware. Therefore, in spite of the internal
overflow Content Addressable Memory (CAM), the actual NetFlow table utilization could be about 80 percent.
-
Depending on the fields that are used for the flow, a single flow could take two consecutive entries. IPv6 and datalink flows
also take two entries. In these situations, the effective usage of NetFlow entries is half the table size, which is separate
from the above hash collision limitation.
-
The device supports up to 15 flow monitors.
-
The NetFlow software implementation supports distributed NetFlow export, so the flows are exported from the same device in
which the flow was created.
-
Ingress flows are present in the ASIC that first received the packets for the flow. Egress flows are present in the ASIC from
which the packets actually left the device set up.
-
The reported value for the bytes count field (called “bytes long”) is Layer-2-packet-size—18 bytes. For classic Ethernet traffic
(802.3), this will be accurate. For all other Ethernet types, this field will not be accurate. Use the "bytes layer2” field,
which always reports the accurate Layer 2 packet size. For information about supported Flexible NetFlow fields, see 'Supported
Flexible NetFlow Fields' topic.
-
Configuration of IPFIX exporter on an AVC flow monitor is not supported.
-
Flexible NetFlow export is not supported on the Ethernet management port, GigabitEthernet 0/0.
-
When a flow record has only Source Group Tag (SGT) and Destination Group Tag (DGT) fields (or only either of the two) and
if both the values are not applicable, then a flow will still be created with zero values for SGT and DGT. The flow records
are expected to include source and destination IP addresses, along with SGT and DGT fields.
-
On non-Cisco TrustSec interfaces, an SGT value of zero implies that there is no command header. On Cisco TrustSec interfaces,
an SGT value of zero implies an unknown tag.
-
For an IPv6 flow monitor, Source Group Tag (SGT) and Destination Group Tag (DGT) fields cannot co-exist with MAC address fields.
-
When a quality of service (QoS) marked packet is received on an interface which has NetFlow configured in the ingress direction,
the QoS value of the packet is captured by the NetFlow collector. However, when the packet is received on an interface which
has NetFlow configured in the egress direction and the QoS value has been rewritten on ingress by the switch, the new QoS
value of the packet is not captured by the collector.
-
NetFlow records do not support MultiProtocol Label Switching-enabled (MPLS-enabled) interfaces.
-
Data capture based on MPLS label inside the MPLS network is not supported. Capture of IP header fields of an MPLS tagged packet
is not supported.
-
Egress flow monitors do not capture flows that are egressing out in EoMPLS mode or in L3VPN Per-Prefix mode.
-
A flow monitor cannot be shared across Layer 3 physical interfaces and logical interfaces (such as, Layer 3 port-channel interface,
Layer 3 port-channel member, and switch virtual interface [SVI]), but a flow monitor can be shared across logical interfaces
or Layer 3 physical interfaces.


 Feedback
Feedback