Installation and Configuration Guide for Cisco Jabber Guest Server 10.6
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- July 15, 2015
Chapter: Prepare to Install
Prepare to Install
Cisco Jabber Guest can be deployed in combination with Cisco Expressway-E and Cisco Expressway-C or in combination with Cisco VCS-E and VCS-C. To simplify the documentation, we reference only Cisco Expressway-E and Cisco Expressway-C throughout this guide.
The mobile and web clients use the same interfaces when interacting with Cisco Expressway/Cisco TelePresence Video Communication Server (VCS) and Cisco Jabber Guest. To simplify the documentation, we reference only the web client throughout this guide.
- Server Requirements
- License Requirements
- Client Requirements
- Deployment Options
- Network Topology
- Ports and Protocols
- Clustering Options
- Load Balancing Methods Available
Server Requirements
Cisco Product Requirements
Make sure that supporting infrastructure is in place before you begin to deploy and configure Cisco Jabber Guest. Deploy Cisco Jabber Guest with an existing Cisco Unified Communications Manager installation.
-
Cisco Unified Communications Manager 8.6.x or later
Cisco Jabber Guest requires that your Cisco Unified Communications Manager be configured to work with Cisco Expressway.
-
Cisco Jabber Guest Server
-
Cisco Expressway-C X8.2 or later
-
Cisco Expressway-E X8.2 or later
Important: -
Without Cisco Expressway-C and Cisco Expressway-E, you are limited to testing with clients that can directly access the network on which the Cisco Jabber Guest server is homed.
-
You cannot use the same Cisco Expressway-C and Cisco Expressway-E pair or cluster for both Cisco Jabber Guest and Expressway for Mobile and Remote Access.
-
For more information, download the Cisco Expressway Administrator Guide, deployment guides, and release notes or see the online help for complete information on configuring the options available on your Cisco Expressway.
Virtual Machine Requirements
Cisco Jabber Guest is deployed as a virtual server using the Open Virtualization Format (OVF) standard for packaging and distributing virtual appliances that run in a virtual environment. It requires VMware vSphere as the hypervisor. Cisco publishes the distribution as an OVF file with the file extension .OVA, which stands for Open Virtual Appliance. This file contains the OVF template for the application. The OVF template defines the virtual machine’s hardware and is preloaded with required software.
- Hardware and System Requirements
- Supported Storage Models
- Virtual Machine Specifications
- VMware vSphere Feature Support
Hardware and System Requirements
A server platform that meets VMware’s Compatibility Guide for VMware vSphere 5.x or later is required. The Cisco Jabber Guest virtual machine uses a 64-bit distribution of CentOS 6.7. Make sure that the server platform uses CPUs that are capable of 64-bit instructions.
Cisco Jabber Guest Server is supported on any Full UC Performance CPU, beginning with Intel Xeon Processor 5600 with a minimum physical core speed of 2.53 GHz or higher and any Restricted UC Performance CPU, beginning with Intel Xeon Processor E5 2609 v1 with a minimum physical core speed of 2.4 GHz or higher. For more information on Full UC performance CPUs and Restricted UC Performance CPUs, see the Processors/CPUs section in UC Virtualization Supported Hardware.
Cisco Jabber Guest is allowed on server models meeting required specifications, including Cisco Business Edition 6000 (BE6000), Cisco Business Edition 7000 (BE7000), and UC on UCS Tested Reference Configurations with a Full UC Performance CPU. BE6000M (M2) UCS C200 M2 TRC#1 is not supported. For more information, see Virtualization for Cisco Jabber Guest Server. Cisco Jabber Guest Server must follow the application co-residency and virtual-to-physical sizing rules in the Unified Communications Virtualization Sizing Guidelines.
Cisco Jabber Guest supports all virtualization software described in Purchasing/Sourcing Options for Required Virtualization Software.
If Cisco Jabber Guest Server is installed on a Cisco Business Edition 6000 server or Cisco Business Edition 7000 server, it must follow the additional co-residency rules in the Cisco Business Edition 6000 and Cisco Business Edition 7000 Co-residency Policy Requirements.
See the VMware developer documentation for additional configuration and hardware requirements. We highly recommend using the Cisco Unified Computing System (CUCS) to simplify and maximize performance.
Supported Storage Models
Virtual Machine Specifications
|
RAM |
CPU |
Storage |
Operating System |
CPU Resource Allocation |
Memory Resource Allocation |
|---|---|---|---|---|---|
|
4 GB |
2 logical CPUs with 1 core each |
100 GB |
CentOS 6.7 64-bit |
Default (not defined) |
Default (not defined) |
VMware vSphere Feature Support
You can restart Cisco Jabber Guest on a different VMware ESXi host and create or revert VMware Snapshots as long as the application was shut down without any issues before moving or taking a snapshot.
Reverse Proxy Server Requirements
Configure the reverse proxy to redirect any HTTP requests to HTTPS.
License Requirements
Cisco Jabber Guest is licensed and obtained through User Connect Licensing (UCL), Cisco Unified Workspace Licensing (CUWL), and other ordering mechanisms. Contact a sales representative from a Cisco partner or from Cisco for ordering details. No license keys are provided or required for the Cisco Jabber Guest software.
The following table describes the license requirements for using Cisco Expressway with Cisco Jabber Guest.
License |
Requirement |
Note |
|---|---|---|
Rich Media Session licenses |
||
TURN relay license |
TURN licensed on Cisco Expressway |
When you order Cisco Expressway, a TURN relay license is included. |
Advanced Networking (AN) license |
If Cisco Jabber Guest is installed in a dual-NIC deployment, an AN license is required on Cisco Expressway. |
When you order Cisco Expressway, an AN license is included. |
The following table describes the license requirements for using Cisco TelePresence Video Communication Server (VCS) with Cisco Jabber Guest.
License |
Requirement |
Note |
|---|---|---|
Traversal call licenses |
||
TURN relay license |
TURN licensed on Cisco VCS |
When you order Cisco VCS, a TURN relay license is included. |
Dual Network Inteface (DI) license |
If Cisco Jabber Guest is installed in a dual-NIC deployment, a DI license is required on Cisco VCS. |
When you order Cisco VCS, a DI license is not included. Specifically select this license. |
Client Requirements
Client Hardware and System Requirements
Callers require a multimedia-capable computer with a camera and microphone that support the following software and hardware requirements:
|
PC Requirements |
Mac Requirements |
|||
|---|---|---|---|---|
|
Operating system |
Microsoft Windows 7 or later |
For Cisco Jabber Guest 10.6 and 10.6(8): Apple Mac OS X 10.7 (Lion) or later For Cisco Jabber Guest 10.6(9) and later: Apple Mac OS X 10.9 (Mavericks) or later |
||
|
Hardware |
GPU capable of OpenGL 1.2 or later Minimum CPU supporting SSE2 (Pentium IV or newer) Encoding at 720p 30 fps requires Intel Core2Duo @ 1.2 GHz or better Encoding at VGA 30 fps can be done on as low-end CPUs as the Intel Atom @ 1.6 GHz |
Apple computer with Intel x86 processor Encoding at 720p 30 fps requires Intel Core2Duo @ 1.2 GHz or better. For optimal experience, Core2Duo @ 2 GHz with 2 MB L2 cache per core is recommended. |
||
|
Browsers |
Mozilla Firefox 10 or later Google Chrome 18 or later
|
For Cisco Jabber Guest 10.6 and 10.6(8): Apple Safari 5 or later For Cisco Jabber Guest 10.6(9) and later: Apple Safari 7 or later Mozilla Firefox 10 or later2 Google Chrome 18 or later |
Cisco Jabber Guest Plug-in Requirement
The Cisco Jabber Guest solution includes a browser plug-in that is downloaded and installed by the caller on the local machine. For Google Chrome, the web page prompts the user to install the Cisco Jabber Guest Add-on and Cisco Jabber Guest Extension. For all other browsers, the Cisco Jabber Guest web page prompts the caller to download and install the plug-in the first time the service is used.
New plug-ins are periodically made available with fixes and new functionality. The caller is prompted to download and install the new plug-in the next time an attempt is made to place a call.
Supported Mobile Devices
Android Supported Devices
We support Cisco Jabber Guest for Android on audio and video for the following Android devices and operating systems:
|
Make |
Model |
Android OS Required |
|---|---|---|
|
|
Nexus 5 |
4.4.x, 5.0, 5.1 |
|
Nexus 6 |
5.0, 5.1 |
|
|
Nexus 7 2013 version or later |
4.4.x, 5.0, 5.1 |
|
|
Nexus 10 |
4.4.x, 5.0, 5.1 |
|
|
HTC |
One (M7) |
4.4.x |
|
One Max |
4.4.x |
|
|
One (M8) |
4.4.x |
|
|
LG |
G2 |
4.2.2–5.0.x, 5.1 |
|
G3 |
4.4.x–5.0.x, 5.1 |
|
|
G4 |
5.1 |
|
|
Motorola |
Moto G |
4.4.x |
|
Samsung |
Galaxy Note II |
4.2–4.4.x |
|
Galaxy Note 3 |
4.3–4.4.x |
|
|
Galaxy Note 4 |
4.4.x |
|
|
Galaxy Note Pro 12.2 |
4.4.x |
|
|
Galaxy Rugby Pro |
4.2.2–4.4.x |
|
|
Galaxy S II |
4.1.2–4.4.x |
|
|
Galaxy S III |
4.1.2–4.4.x |
|
|
Galaxy S4 |
4.2.2–4.4.x |
|
|
Galaxy S4 mini |
4.2.2–4.4.x |
|
|
Galaxy S5 |
4.4.x |
|
|
Galaxy S5 mini |
4.4.x |
|
|
Galaxy S6 |
5.1.x |
|
|
Galaxy S6 edge |
5.1.x |
|
|
Galaxy S6 edge + |
5.1.x |
|
|
Galaxy Tab 3 8.0 |
4.4.x |
|
|
Galaxy Tab 4 7.0, 8.0, and 10.1 |
4.4.x |
|
|
Galaxy Tab Pro 8.4 and 10.1 |
4.4.x |
|
|
Galaxy Tab S 8.4 and 10.5 |
4.4.x |
|
|
Sony |
Xperia M2 |
4.3 |
|
Xperia Z1 |
4.2–4.4.x |
|
|
Xperia ZR/A |
4.1.2–4.4.x |
|
|
Xperia Z2 |
4.4.x |
|
|
Xperia Z2 tablet |
4.4.x |
|
|
Xperia Z3 |
4.4.x |
|
|
Xperia Z4 |
5.0.x |
We support Cisco Jabber Guest for Android with tested Android devices. Although other devices are not officially supported, you may be able to use Cisco Jabber Guest for Android with other devices.
iOS Supported Devices
Cisco Jabber Guest 10.6 and 10.6(8) is supported on iOS 7.1 or later.
Cisco Jabber Guest 10.6(9), 10.6(10) and 10.6(11) is supported on iOS 8.0 or later.
The following table lists the iOS mobile devices that Cisco Jabber Guest supports:
|
iPad |
iPhone |
|---|---|
|
iPad 2 |
iPhone 4s |
|
iPad 3 |
iPhone 5 |
|
iPad 4 |
iPhone 5c |
|
iPad Air |
iPhone 5s |
|
iPad Air 2 |
iPhone 6 |
|
iPad mini |
iPhone 6 Plus |
|
iPad mini 2 |
iPhone 6s |
|
iPad mini 3 |
iPhone 6s Plus |
|
iPad mini 4 |
|
|
iPad Pro |
Deployment Options
Cisco Expressway-E with a single NIC—SIP traffic goes to the Cisco Expressway-C and media flows over a port range between the Cisco Expressway-E and the Cisco Expressway-C.
Cisco Expressway-E with dual NIC—SIP traffic goes to the Cisco Expressway-E and media flows through the traversal zone between the Cisco Expressway-E and the Cisco Expressway-C.
Only the Cisco Expressway-E with dual NIC deployment supports NAT/PAT between the Cisco Expressway-E and the Cisco Expressway-C.
Lab Deployment
Cisco Jabber Guest can be pointed directly to Cisco Unified Communications Manager for lab deployments only; configure a SIP trunk on Cisco Unified Communications Manager for this deployment. This option is best suited to a lab deployment in which the goal is to familiarize yourself with Cisco Jabber Guest without the additional overhead of configuring Expressway. However, without configuring Expressway, Cisco Jabber Guest is not supported in a production environment.
If you deploy Cisco Jabber Guest directly to Cisco Unified Communications Manager, you may need to enable a client-side firewall rule to allow incoming screen share.
Network Topology
Overview of Cisco Expressway-E with Single NIC Deployment
SIP traffic is sent to the Cisco Expressway-C.
Cisco Expressway-E is single NIC only.
Cisco Expressway-E in static NAT mode is optional and requires additional configuration on the Cisco Jabber Guest server.
Cisco Expressway-E is used for TURN services and reverse proxy, not call control.
Media flows between the Cisco Expressway-E and the Cisco Expressway-C over port range, not a traversal zone.
Overview of Cisco Expressway-E with Dual NIC Deployment
SIP traffic is sent to the Cisco Expressway-E.
Cisco Expressway-E is dual NIC only.
Cisco Expressway-E in static NAT mode is optional and requires additional configuration on the Cisco Jabber Guest server.
Cisco Expressway-E is used for TURN services, reverse proxy, and call control.
Media flows between the Cisco Expressway-E and the Cisco Expressway-C through a traversal zone.
In a production environment, Cisco Jabber Guest requires that your Cisco Unified Communications Manager be configured to work with Cisco Expressway.
 Note | If Cisco Expressway-E is used for reverse proxy functionality, the Cisco Jabber Guest URL looks like https://expressway-e.example.com/call where expressway-e.example.com is the FQDN of Cisco Expressway-E. |
Call Control Flow
The following are examples of call control flow for the two supported deployments of Cisco Jabber Guest Server.

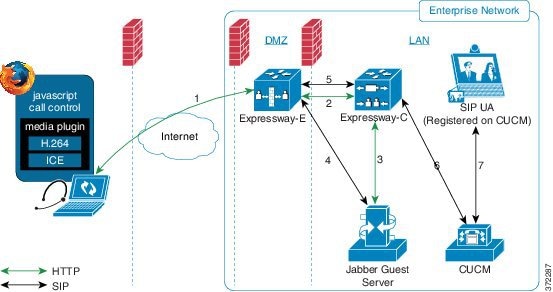
Cisco Expressway-E with Dual NIC Deployment
SIP flows between the Cisco Jabber Guest server and the Cisco Expressway-E. This requires bi-directional TCP traffic between the two servers over 5060 (SIP over TCP) or 5061 (SIP over TLS). The SIP traffic then goes over the traversal zone to the Cisco Expressway-C.
We recommend that you disable SIP and H.323 application-level gateways on routers/firewalls carrying network traffic to or from a Cisco Expressway-E.
Because media hairpins between the two Cisco Expressway-E NICs, the TURN traffic and SIP traffic must reside on the same Cisco Expressway-E server. You must configure the static NAT address, DMZ external address, and DMZ internal address of the Cisco Expressway-E on the Cisco Jabber Guest server.
Media Flow
The web client uses TURN relays allocated on the Cisco Expressway-E to tunnel media into the enterprise. Media is sent and received in STUN encapsulated packets to the TURN server through UDP port 3478.
The Cisco Jabber Guest client allocates a call resource through HTTP to the Cisco Jabber Guest server.
The Cisco Jabber Guest server requests short-term TURN credentials from the Cisco Expressway-C through a secure HTTP request. Administrator credentials are used for authentication. The configured domain must be on the Cisco Expressway-C with Jabber Guest service enabled.
The Cisco Expressway-C creates the TURN credential and passes it to the Cisco Jabber Guest server.
The Cisco Expressway-C propagates the TURN credential to the Cisco Expressway-E through the SSH tunnel (port 2222).
The Cisco Jabber Guest server responds to the Cisco Jabber Guest client with the TURN credential and TURN server (Cisco Expressway-E) address (DNS or IP).
The Cisco Jabber Guestclient uses the TURN credential to allocate the TURN relay on the TURN server.
BFCP Screen Share
The Binary Floor Control Protocol (BFCP) screen share is an RTP media stream that flows in the same path as the audio and video media. The BFCP screen share is a separate stream from the video stream. The maximum bandwidth that the audio, video, and BFCP screen share streams can use is 2000 kbps.
- Media Flow: Cisco Expressway-E with Single NIC Deployment
- Media Flow: Cisco Expressway-E with Dual NIC Deployment
Media Flow: Cisco Expressway-E with Single NIC Deployment
The following diagram is an example of the media flow for a Cisco Expressway-E with single NIC deployment of Cisco Jabber Guest.

Cisco Jabber Guest media does not go through the traversal link between Cisco Expressway-E and Cisco Expressway-C.
If the Cisco Expressway-E is behind a NAT, additional configuration is required on the Cisco Jabber Guest server to avoid the media flowing to the static NAT address. Turn on Static NAT mode and configure the static NAT address and DMZ external address of the Cisco Expressway-E on the Cisco Jabber Guest server. This allows media to be sent to the DMZ external address of the Cisco Expressway-E, avoiding NAT reflection on the outside firewall.
Media Flow: Cisco Expressway-E with Dual NIC Deployment
The following diagram is an example of the media flow for a Cisco Expressway-E with dual NIC deployment of Cisco Jabber Guest.

Media flows through the traversal zone between the Cisco Expressway-C and the internal NIC of the Cisco Expressway-E. It hairpins on the Cisco Expressway-E to the external NIC of the Cisco Expressway-E, and then is STUN/TURN wrapped before being sent to the client browser.
If the Cisco Expressway-E is behind a NAT, additional configuration is required on the Cisco Jabber Guest server to avoid the media flowing to the static NAT address. Turn on Static NAT mode and configure the static NAT address, DMZ external address, and DMZ internal address of the Cisco Expressway-E on the Cisco Jabber Guest server. This allows media to be sent to the DMZ external address of the Cisco Expressway-E, avoiding NAT reflection on the outside firewall.
Ports and Protocols
HTTP and HTTPS traffic from Cisco Jabber Guest clients in the Internet is sent to ports 80 and 443 TCP respectively. Therefore the firewall between the Cisco Expressway-E and the public Internet must translate destination port 80 to 9980 and destination port 443 to 9443 for all TCP traffic that targets the Cisco Expressway-E address.
The Cisco Expressway-E redirects HTTP requests on port 9980 to HTTPS on 9443.
80/443 TCP are the standard HTTP/S administration interfaces on the Expressway. If the Cisco Expressway-E is administered from systems located in the Internet, then the firewall translation must also distinguish by source address and must not translate the destination port of traffic arriving from those management systems.
You also need to ensure that appropriate DNS records exist so that the Cisco Jabber Guest client can reach the Cisco Expressway-E. The FQDN of the Cisco Expressway-E in DNS must include the Cisco Jabber Guest domain. The Cisco Jabber Guest domain is the domain that is configured on the Cisco Expressway-C.
- Ports and Protocols: Cisco Expressway-E with Single NIC Deployment
- Ports and Protocols: Cisco Expressway-E with Dual NIC Deployment
Ports and Protocols: Cisco Expressway-E with Single NIC Deployment
|
Purpose |
Protocol |
Internet Endpoint (Source) |
Cisco Expressway-E (Listening) |
|---|---|---|---|
|
HTTP |
TCP |
TCP source port |
9980 (read the following Important note) |
|
HTTPS proxy |
TLS |
TCP source port |
9443 (read the following Important note) |
|
TURN Server (control and media relays) |
UDP |
UDP source port |
3478–3483 4 |
-
The Cisco Expressway-E administrator currently uses port 80 and therefore, incoming requests from the Cisco Jabber Guest client to Cisco Expressway-E on port 80 must be remapped to port 9980 using a firewall (or similar) in front of Cisco Expressway-E. For the mobile client, using 9980 in call links is not supported; you must use port remapping on your firewall to remap port 80 to port 9980.
- The Cisco Expressway-E administrator currently uses port 443 and therefore, incoming requests from the Cisco Jabber Guest client to Cisco Expressway-E on port 443 must be remapped to port 9443 using a firewall (or similar) in front of Cisco Expressway-E. For mobile clients (10.6(9) and later releases), that do not use a firewall during deployment, include port 9443 in call links.
|
Purpose |
Protocol |
Cisco Expressway-C (Source) |
Cisco Expressway-E (Destination) |
|---|---|---|---|
|
SSH (HTTP/S tunnels) |
TCP |
Ephemeral port |
2222 (not configurable) |
|
Traversal zone SIP signaling |
TLS |
25000–29999 |
7001 |
|
Media5 |
UDP |
36000–59999 |
24000–29999 |
|
Purpose |
Protocol |
Cisco Expressway-E (Source) |
Cisco Expressway-C (Destination) |
|---|---|---|---|
|
Media |
UDP |
24000–29999 |
36000–59999 |
-
Inbound firewall rules are required to allow media to flow from the Cisco Expressway-E to Cisco Expressway-C.
-
You may find that two-way media can still be established even if the inbound from Cisco Expressway-E (DMZ) to Cisco Expressway-C (private) firewall rules are not applied. This is because the outbound media creates a pinhole in the firewall; however, these rules are required to support uni-directional media (that is, only from outside to inside).
|
Purpose |
Protocol |
Cisco Expressway-C (Source) |
Cisco Jabber Guest (Destination) |
|---|---|---|---|
|
HTTP |
TCP |
Ephemeral port |
80 |
|
HTTPS |
TLS |
Ephemeral port |
443 |
|
SIP |
TCP/TLS |
Ephemeral port |
5060 (SIP over TCP) 5061 (SIP over TLS) |
|
Purpose |
Protocol |
Cisco Jabber Guest (Source) |
Cisco Expressway-C (Destination) |
|---|---|---|---|
|
HTTPS |
TLS |
Ephemeral port |
443 |
|
SIP |
TCP/TLS |
Ephemeral port |
5060 (SIP over TCP) 5061 (SIP over TLS) |
Ports and Protocols: Cisco Expressway-E with Dual NIC Deployment
|
Purpose |
Protocol |
Internet Endpoint (Source) |
Cisco Expressway-E (Listening) |
|---|---|---|---|
|
HTTP |
TCP |
TCP source port |
9980 (read the following Important note) |
|
HTTPS proxy |
TLS |
TCP source port |
9443 (read the following Important note) |
|
TURN Server (control and media relays) |
UDP |
UDP source port |
3478–3483 7 |
-
The Cisco Expressway-E administrator currently uses port 80 and therefore, incoming requests from the Cisco Jabber Guest client to Cisco Expressway-E on port 80 must be remapped to port 9980 using a firewall (or similar) in front of Cisco Expressway-E. For the mobile client, using 9980 in call links is not supported; you must use port remapping on your firewall to remap port 80 to port 9980.
-
The Cisco Expressway-E administrator currently uses port 443 and therefore, incoming requests from the Cisco Jabber Guest client to Cisco Expressway-E on port 443 must be remapped to port 9443 using a firewall (or similar) in front of Cisco Expressway-E. For mobile clients (10.6(9) and later releases), that do not use a firewall during deployment, include port 9443 in call links.
|
Purpose |
Protocol |
Cisco Expressway-C (Source) |
Cisco Expressway-E (Destination) |
||
|---|---|---|---|---|---|
|
SSH (HTTP/S tunnels) |
TCP |
Ephemeral port |
2222 (not configurable) |
||
|
Traversal zone SIP signaling |
TLS |
25000–29999 |
7001 |
||
|
Media
|
UDP |
36002–59999 |
36000–360018 36000–360119 |
|
Purpose |
Protocol |
Cisco Jabber Guest (Source) |
Cisco Expressway-E (Destination) |
|---|---|---|---|
|
SIP |
TCP/TLS |
Ephemeral port |
5060 (SIP over TCP) 5061 (SIP over TLS) |
|
Purpose |
Protocol |
Cisco Expressway-E (Source) |
Cisco Jabber Guest (Destination) |
|---|---|---|---|
|
SIP |
TCP/TLS |
Ephemeral port |
5060 (SIP over TCP) 5061 (SIP over TLS) |
|
Purpose |
Protocol |
Cisco Expressway-C (Source) |
Cisco Jabber Guest (Destination) |
|---|---|---|---|
|
HTTP |
TCP |
Ephemeral port |
80 |
|
HTTPS |
TLS |
Ephemeral port |
443 |
|
Purpose |
Protocol |
Cisco Jabber Guest (Source) |
Cisco Expressway-C (Destination) |
|---|---|---|---|
|
HTTPS |
TLS |
Ephemeral port |
443 |
Clustering Options
Cisco Jabber Guest only supports a three-server cluster. Three operational servers are required for full redundancy.
Recommended Deployment
Configure the reverse proxy to send requests to only one server in the cluster at a time. You set the order in which requests are sent on Cisco Expressway-C, from the Priority field in . Give each Cisco Jabber Guest server a different priority. Requests are sent to a different server only if a server becomes unresponsive.
Cisco Jabber Guest can be administered from any server in the cluster. To simplify troubleshooting, we recommend that you use one server in the cluster for administration purposes.
Data Replication
|
Data That Replicates |
Data That Does Not Replicate |
|---|---|
|
Users |
Settings > Local SSL Certificate |
|
Links |
Settings > Call Control and Media (Local) |
|
Services > Passwords |
Logs |
|
Settings > Links |
|
|
Settings > Mobile |
|
|
Settings > Secure SIP Trust Certificate |
|
|
Settings > Call Control and Media |
Cluster Latency
The upper latency limit is 15 milliseconds.
Load Balancing Methods Available
You can balance the load on your Cisco Expressway-C, Cisco Expressway-E, and Cisco Jabber Guest server clusters.
The following table describes the methods of load balancing that are available to distribute different types of traffic across the network.
 Feedback
Feedback