Configuración de Syslog de SDWAN Cisco IOS XE TLS en el servidor syslog-ng
Opciones de descarga
Lenguaje no discriminatorio
El conjunto de documentos para este producto aspira al uso de un lenguaje no discriminatorio. A los fines de esta documentación, "no discriminatorio" se refiere al lenguaje que no implica discriminación por motivos de edad, discapacidad, género, identidad de raza, identidad étnica, orientación sexual, nivel socioeconómico e interseccionalidad. Puede haber excepciones en la documentación debido al lenguaje que se encuentra ya en las interfaces de usuario del software del producto, el lenguaje utilizado en función de la documentación de la RFP o el lenguaje utilizado por un producto de terceros al que se hace referencia. Obtenga más información sobre cómo Cisco utiliza el lenguaje inclusivo.
Acerca de esta traducción
Cisco ha traducido este documento combinando la traducción automática y los recursos humanos a fin de ofrecer a nuestros usuarios en todo el mundo contenido en su propio idioma. Tenga en cuenta que incluso la mejor traducción automática podría no ser tan precisa como la proporcionada por un traductor profesional. Cisco Systems, Inc. no asume ninguna responsabilidad por la precisión de estas traducciones y recomienda remitirse siempre al documento original escrito en inglés (insertar vínculo URL).
Contenido
Introducción
Este documento describe una guía completa para configurar un servidor Syslog TLS en dispositivos SD-WAN Cisco IOS® XE.
Prerequisites
Antes de continuar con la configuración de un servidor Syslog TLS en dispositivos SD-WAN Cisco IOS XE, asegúrese de cumplir con los siguientes requisitos:
Requirements
Cisco recomienda que tenga conocimiento sobre estos temas:
-
Controladores SD-WAN: asegúrese de que la red incluye controladores SD-WAN correctamente configurados.
-
Router SD-WAN Cisco IOS XE: router compatible que ejecuta la imagen SD-WAN de Cisco IOS XE.
-
Syslog Server - Un servidor Syslog basado en Ubuntu, como syslog-ng, para recopilar y administrar datos de registro.
Componentes Utilizados
La información que contiene este documento se basa en las siguientes versiones de software y hardware.
-
vManage: Versión 20.9.4
-
SD-WAN de Cisco IOS XE: Versión 17.9.4
-
Ubuntu: Versión 22.04
-
syslog-ng: Versión 3.27
La información que contiene este documento se creó a partir de los dispositivos en un ambiente de laboratorio específico. Todos los dispositivos que se utilizan en este documento se pusieron en funcionamiento con una configuración verificada (predeterminada). Si tiene una red en vivo, asegúrese de entender el posible impacto de cualquier comando.
Configuración
1. Instalación de syslog-ng en la máquina Ubuntu
Para configurar syslog-ng en su servidor Ubuntu, siga estos pasos para garantizar una instalación y configuración adecuadas.
Paso 1. Configuración de los ajustes de la red
Después de instalar el servidor Ubuntu, configure una dirección IP estática y un servidor DNS para asegurarse de que la máquina pueda acceder a Internet. Esto es crucial para descargar paquetes y actualizaciones.
Paso 2. Instalar syslog-ng
Abra un terminal en su máquina Ubuntu y ejecute:
sudo apt-get install syslog-ng sudo apt-get install syslog-ng openssl2. Instale la autoridad certificadora raíz en el servidor Syslog para la autenticación del servidor
Crear directorios y generar claves
cd /etc/syslog-ng mkdir cert.d key.d ca.d cd cert.d openssl genrsa -out ca.key 2048 openssl req -new -x509 -key ca.key -out PROXY-SIGNING-CA.ca -days 730 # Copy key to the key.d folder cp ca.key ../key.dCalcular huella dactilar
Ejecute el comando y copie el resultado:
openssl x509 -in PROXY-SIGNING-CA.ca -fingerprint -noout | awk -F "=" '{print $2}' | sed 's/://g' | tee fingerprint.txt
# Ejemplo de salida: 54F371C8EE2BFB06E2C2D0944245C288FBB07163
3. Configure el archivo de configuración del servidor syslog-ng
Edite el archivo de configuración de syslog-ng:
sudo nano /etc/syslog-ng/syslog-ng.confAgregue la configuración:
source s_src { network( ip(0.0.0.0) port(6514) transport("tls") tls( key-file("/etc/syslog-ng/key.d/ca.key") cert-file("/etc/syslog-ng/cert.d/PROXY-SIGNING-CA.ca") peer-verify(optional-untrusted) ) ); }; destination remote { file("/var/log/syslog"); }; log { source(s_src); destination(remote); };4. Instale la autoridad certificadora raíz en el dispositivo SD-WAN Cisco IOS XE para la autenticación del servidor
Configurar desde CLI
-
Ingrese en el modo de configuración:
config-t-
Configure el punto de confianza:
crypto pki trustpoint PROXY-SIGNING-CA enrollment url bootflash: revocation-check none rsakeypair PROXY-SIGNING-CA 2048 subject-name cn=proxy-signing-cert fqdn none fingerprint 54F371C8EE2BFB06E2C2D0944245C288FBB07163 >> The fingerprint configured was obtained from the fingerprint.txt file above commit-
Copie el PROXY-SIGNING-CA.ca desde el servidor syslog al router bootflash con el mismo nombre.
-
Autenticar el punto de confianza:
crypto pki authenticate PROXY-SIGNING-CA
example:
Router#crypto pki authenticate PROXY-SIGNING-CA
Reading file from bootflash:PROXY-SIGNING-CA.ca
Certificate has the attributes:
Fingerprint MD5: 7A97B30B 2AE458FF D9E7D91F 66488DCF
Fingerprint SHA1: 21E0F09B B67B2E9D 706DBE69 856E5AA3 D39A268A
Trustpoint Fingerprint: 21E0F09B B67B2E9D 706DBE69 856E5AA3 D39A268A
Certificate validated - fingerprints matched.
Trustpoint CA certificate accepted.-
Inscriba el punto de confianza:
crypto pki enroll PROXY-SIGNING-CA
example:
vm32#crypto pki enroll PROXY-SIGNING-CA
Start certificate enrollment ..
The subject name in the certificate will include: cn=proxy-signing-cert
The fully-qualified domain name will not be included in the certificate
Certificate request sent to file system
The 'show crypto pki certificate verbose PROXY-SIGNING-CA' commandwill show the fingerprint.
-
Copie el PROXY-SIGNING-CA.req del router al servidor syslog.
Firmar el certificado en el servidor Syslog
openssl x509 -in PROXY-SIGNING-CA.req -req -CA PROXY-SIGNING-CA.ca -CAkey ca.key -out PROXY-SIGNING-CA.crt -CAcreateserial -extensions ca_extensions-
Copiar el archivo generado (PROXY-SIGNING-CA.crt) al bootflash del router. copy scp: bootflash:
-
Importar el certificado:
crypto pki import PROXY-SIGNING-CA certificate
example:
Router# crypto pki import PROXY-SIGNING-CA certificate
% The fully-qualified domain name will not be included in the certificate
% Request to retrieve Certificate queuedValidar la configuración
show crypto pki trustpoint PROXY-SIGNING-CA status
example:
Router#show crypto pki trustpoint PROXY-SIGNING-CA status
Trustpoint PROXY-SIGNING-CA:
Issuing CA certificate configured:
Subject Name:
o=Internet Widgits Pty Ltd,st=Some-State,c=AU
Fingerprint MD5: 7A97B30B 2AE458FF D9E7D91F 66488DCF
Fingerprint SHA1: 21E0F09B B67B2E9D 706DBE69 856E5AA3 D39A268A
Router General Purpose certificate configured:
Subject Name:
cn=proxy-signing-cert
Fingerprint MD5: 140A1EAB FE945D56 D1A53855 FF361F3F
Fingerprint SHA1: ECA67413 9C102869 69F582A4 73E2B98C 80EFD6D5
Last enrollment status: Granted
State:
Keys generated ............. Yes (General Purpose, non-exportable)
Issuing CA authenticated ....... Yes
Certificate request(s) ..... Yes5. Configure el servidor de registro del sistema TLS en el router SD-WAN Cisco IOS XE
Configure el servidor syslog mediante los comandos:
logging trap syslog-format rfc5424 logging source-interface GigabitEthernet0/0/0 logging tls-profile tls-profile logging host X.X.X.X transport tls profile tls-profile tls-version TLSv1.26. Verificaciones
Comprobación de registros en el router
show logging
Showing last 10 lines
Log Buffer (512000 bytes):
Apr 9 05:59:48.025: %DMI-5-CONFIG_I: R0/0: dmiauthd: Configured from NETCONF/RESTCONF by admin, transaction-id 189410
Apr 9 05:59:48.709: %DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:58393 for netconf over ssh. External groups:
Apr 9 05:59:50.015: %LINK-5-CHANGED: Interface GigabitEthernet0/0/1, changed state to administratively down
Apr 9 05:59:51.016: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0/1, changed state to down
Apr 9 05:59:52.242: %SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Comprobar registros en el servidor Syslog
tail -f /var/log/syslog
root@server1:/etc/syslog-ng# tail -f /var/log/syslog
Apr 9 15:51:14 10.66.91.94 188 <189>1 2024-04-09T05:51:51.037Z - - - - - BOM%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:38032 for netconf over ssh. External groups:
Apr 9 15:59:10 10.66.91.94 177 <189>1 2024-04-09T05:59:47.463Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Apr 9 15:59:10 10.66.91.94 177 <189>1 2024-04-09T05:59:47.463Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Apr 9 15:59:10 10.66.91.94 143 <189>1 2024-04-09T05:59:47.463Z - - - - - BOM%DMI-5-CONFIG_I: R0/0: dmiauthd: Configured from NETCONF/RESTCONF by admin, transaction-id 189410
Apr 9 15:59:11 10.66.91.94 188 <189>1 2024-04-09T05:59:48.711Z - - - - - BOM%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:58393 for netconf over ssh. External groups:
Apr 9 15:59:13 10.66.91.94 133 <189>1 2024-04-09T05:59:50.016Z - - - - - BOM%LINK-5-CHANGED: Interface GigabitEthernet0/0/1, changed state to administratively down
Apr 9 15:59:13 10.66.91.94 137 <189>1 2024-04-09T05:59:50.016Z - - - - - BOM%LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0/1, changed state to down
Apr 9 15:59:15 10.66.91.94 177 <189>1 2024-04-09T05:59:52.242Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Apr 9 15:59:15 10.66.91.94 177 <189>1 2024-04-09T05:59:52.242Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Apr 9 15:59:18 10.66.91.94 188 <189>1 2024-04-09T05:59:55.286Z - - - - - BOM%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:34575 for netconf over ssh. External groups:
Apr 9 15:59:21 10.66.91.94 113 <187>1 2024-04-09T05:59:58.882Z - - - - - BOM%LINK-3-UPDOWN: Interface GigabitEthernet0/0/1, changed state to up
Apr 9 15:59:21 10.66.91.94 135 <189>1 2024-04-09T05:59:59.882Z - - - - - BOM%LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0/1, changed state to up
Apr 9 15:59:28 10.66.91.94 177 <189>1 2024-04-09T06:00:05.536Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
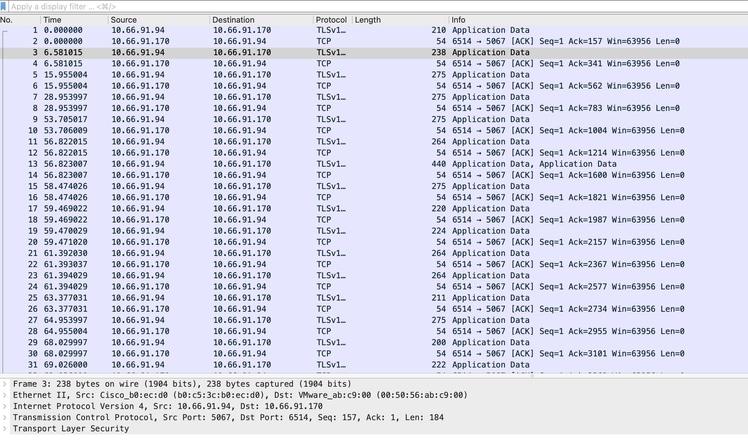
Apr 9 15:59:43 10.66.91.94 188 <189>1 2024-04-09T06:00:20.537Z - - - - - BOM%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:43530 for netconf over ssh. External groups:Captura de pantalla de captura de paquetes y puede ver cómo se producen las comunicaciones cifradas:
ISR4331-branch-NEW_Branch#show logging
Trap logging: level informational, 6284 message lines logged
Logging to 10.66.91.170 (tls port 6514, audit disabled,
link up),
131 message lines logged,
0 message lines rate-limited,
0 message lines dropped-by-MD,
xml disabled, sequence number disabled
filtering disabled
tls-profile: tls-proile
Logging Source-Interface: VRF Name:
GigabitEthernet0/0/0
TLS Profiles:
Profile Name: tls-proile
Ciphersuites: Default
Trustpoint: Default
TLS version: TLSv1.2Verificación
Actualmente, no hay un procedimiento de verificación disponible para esta configuración.
Troubleshoot
Actualmente, no hay información específica de troubleshooting disponible para esta configuración.
Historial de revisiones
| Revisión | Fecha de publicación | Comentarios |
|---|---|---|
1.0 |
18-Dec-2024 |
Versión inicial |
Con la colaboración de ingenieros de Cisco
- Md Aamir SadiqueLíder técnico de Cisco TAC
Contacte a Cisco
- Abrir un caso de soporte

- (Requiere un Cisco Service Contract)
 Comentarios
Comentarios