Ejemplo de Configuración de FlexVPN HA Dual Hub
Opciones de descarga
-
ePub (509.4 KB)
Visualice en diferentes aplicaciones en iPhone, iPad, Android, Sony Reader o Windows Phone -
Mobi (Kindle) (562.2 KB)
Visualice en dispositivo Kindle o aplicación Kindle en múltiples dispositivos
Lenguaje no discriminatorio
El conjunto de documentos para este producto aspira al uso de un lenguaje no discriminatorio. A los fines de esta documentación, "no discriminatorio" se refiere al lenguaje que no implica discriminación por motivos de edad, discapacidad, género, identidad de raza, identidad étnica, orientación sexual, nivel socioeconómico e interseccionalidad. Puede haber excepciones en la documentación debido al lenguaje que se encuentra ya en las interfaces de usuario del software del producto, el lenguaje utilizado en función de la documentación de la RFP o el lenguaje utilizado por un producto de terceros al que se hace referencia. Obtenga más información sobre cómo Cisco utiliza el lenguaje inclusivo.
Acerca de esta traducción
Cisco ha traducido este documento combinando la traducción automática y los recursos humanos a fin de ofrecer a nuestros usuarios en todo el mundo contenido en su propio idioma. Tenga en cuenta que incluso la mejor traducción automática podría no ser tan precisa como la proporcionada por un traductor profesional. Cisco Systems, Inc. no asume ninguna responsabilidad por la precisión de estas traducciones y recomienda remitirse siempre al documento original escrito en inglés (insertar vínculo URL).
Contenido
Introducción
Este documento describe cómo configurar un diseño de redundancia completa para oficinas remotas que se conectan a un Data Center a través de una VPN basada en IPSec a través de un medio de red inseguro, como Internet.
Prerequisites
Requirements
No hay requisitos específicos para este documento.
Componentes Utilizados
La información en este documento se basa en estos componentes tecnológicos:
- Protocolo de gateway fronterizo (BGP) como protocolo de routing dentro del Data Center y entre radios y concentradores en la superposición de VPN.
- Detección de reenvío bidireccional (BFD) como mecanismo que detecta los enlaces inactivos (el router está inactivo) que se ejecutan sólo dentro del Data Center (no sobre los túneles superpuestos).
- Cisco IOS® FlexVPN entre los concentradores y los radios, con capacidades de radio a radio habilitadas a través de conmutación corta.
- Tunelización de Generic Routing Encapsulation (GRE) entre dos ejes de conexión para habilitar la comunicación de radio a radio, incluso cuando los radios están conectados a diferentes ejes de conexión.
- Seguimiento de objetos mejorado y rutas estáticas vinculadas a los objetos de seguimiento.
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Antecedentes
Al diseñar soluciones de acceso remoto para el Data Center, la alta disponibilidad (HA) suele ser un requisito clave para las aplicaciones de usuario críticas.
La solución que se presenta en este documento permite una rápida detección y recuperación de situaciones de falla en las que uno de los concentradores de terminación de VPN deja de funcionar debido a problemas de recarga, actualización o energía. Todos los routers de oficinas remotas (spokes) utilizan el otro hub operativo inmediatamente después de detectar tal falla.
Estas son las ventajas de este diseño:
- Recuperación rápida de la red desde un escenario de VPN hub-down
- No hay sincronizaciones complejas con información de estado (como las asociaciones de seguridad IPSec (SA), las SA de protocolo de administración de claves (ISAKMP) y de asociación de seguridad de Internet, y el enrutamiento criptográfico) entre los concentradores de VPN
- No hay problemas de reproducción debido a retrasos en la sincronización del número de secuencia de carga de seguridad de encapsulación (ESP) con HA stateful IPSec
- Los concentradores VPN pueden utilizar diferentes hardware o software basados en Cisco IOS/IOS-XE
- Opciones flexibles de implementación de balanceo de carga con BGP como protocolo de ruteo que se ejecuta en la superposición de VPN
- Routing claro y legible en todos los dispositivos sin mecanismos ocultos que se ejecuten en segundo plano
- Conectividad directa de spoke a spoke
- Todas las ventajas de FlexVPN, para incluir la integración de autenticación, autorización y contabilidad (AAA) y la calidad de servicio (QoS) por túnel
Configurar
Esta sección proporciona escenarios de ejemplo y describe cómo configurar un diseño de redundancia completa para oficinas remotas que se conectan al Data Center a través de VPN basada en IPSec a través de un medio de red inseguro.
Nota: Use la Command Lookup Tool (clientes registrados solamente) para obtener más información sobre los comandos usados en esta sección.
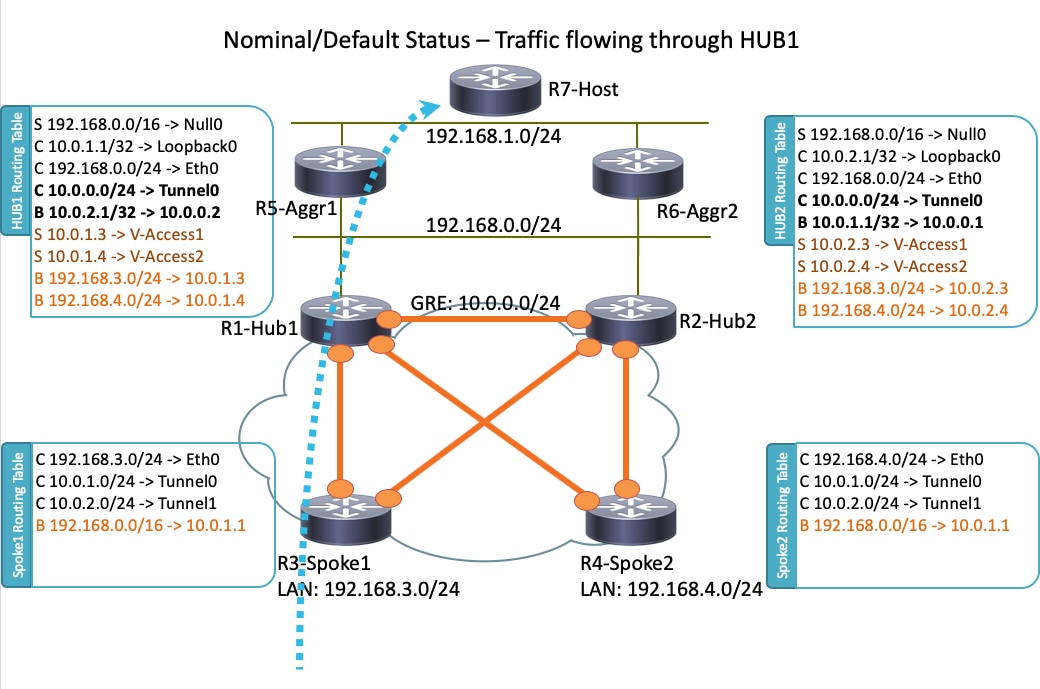
Diagrama de la red
Esta es la topología de red que se utiliza en este documento:
Nota: Todos los routers que se utilizan en esta topología ejecutan Cisco IOS versión 15.2(4)M1, y Internet Cloud utiliza un esquema de direcciones de 172.16.0.0/24.
Escenario operativo normal
En un escenario operativo normal, cuando todos los routers están activos y en funcionamiento, todos los routers radiales enrutan todo el tráfico a través del hub predeterminado (R1-HUB1). Esta preferencia de ruteo se logra cuando la preferencia local predeterminada de BGP se establece en 200 (consulte las secciones que siguen para obtener detalles). Esto se puede ajustar en función de los requisitos de implementación, como el equilibrio de carga del tráfico.
Spoke-to-Spoke (acceso directo)
Si R3-Spoke1 inicia una conexión a R4-Spoke2, se crea un túnel dinámico spoke-to-spoke con la configuración de conmutación corta.
Consejo: Para obtener más detalles, consulte la guía de configuración Configuración de FlexVPN Spoke to Spoke.
Si R3-Spoke1 está conectado sólo a R1-HUB1 y R4-Spoke2 está conectado sólo a R2-HUB2, todavía se puede lograr una conexión directa de radio a radio con el túnel GRE punto a punto que se ejecuta entre los concentradores. En este caso, la trayectoria de tráfico inicial entre R3-Spoke1 y R4-Spoke2 parece similar a esta:

Dado que R1-Hub1 recibe el paquete en la interfaz de acceso virtual, que tiene el mismo ID de red de protocolo de resolución de salto siguiente (NHRP) que en el túnel GRE, la indicación de tráfico se envía hacia el R3-Spoke1. Esto desencadena la creación del túnel dinámico spoke-to-spoke:

Tablas de routing y salidas para situaciones operativas regulares
Esta es la tabla de ruteo R1-HUB1 en un escenario operativo normal:
R1-HUB1# show ip route
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP
a - application route
+ - replicated route, % - next hop override
Gateway of last resort is not set
10.0.0.0/8 is variably subnetted, 11 subnets, 3 masks
S 10.0.0.0/8 is directly connected, Null0
C 10.0.0.0/24 is directly connected, Tunnel0
L 10.0.0.1/32 is directly connected, Tunnel0
C 10.0.1.1/32 is directly connected, Loopback0
S 10.0.1.2/32 is directly connected, Virtual-Access1
S 10.0.1.3/32 is directly connected, Virtual-Access2
B 10.0.2.1/32 [200/0] via 10.0.0.2, 00:05:40
B 10.0.2.3/32 [200/0] via 10.0.0.2, 00:05:40
B 10.0.2.4/32 [200/0] via 10.0.0.2, 00:05:40
B 10.0.5.1/32 [200/0] via 192.168.0.5, 00:05:40
B 10.0.6.1/32 [200/0] via 192.168.0.6, 00:05:40
172.16.0.0/16 is variably subnetted, 2 subnets, 2 masks
C 172.16.0.0/24 is directly connected, Ethernet0/0
L 172.16.0.1/32 is directly connected, Ethernet0/0
S 192.168.0.0/16 is directly connected, Null0
192.168.0.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.0.0/24 is directly connected, Ethernet0/2
L 192.168.0.1/32 is directly connected, Ethernet0/2
B 192.168.1.0/24 [200/0] via 192.168.0.5, 00:05:40
B 192.168.3.0/24 [200/0] via 10.0.1.4, 00:05:24
B 192.168.4.0/24 [200/0] via 10.0.1.5, 00:05:33
Esta es la tabla de ruteo R3-SPOKE1 en un escenario de funcionamiento normal después de crear el túnel de radio a radio con R4-SPOKE2:
R3-SPOKE1# show ip route
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP
a - application route
+ - replicated route, % - next hop override
Gateway of last resort is not set
10.0.0.0/8 is variably subnetted, 8 subnets, 2 masks
B 10.0.0.0/8 [200/0] via 10.0.1.1, 00:06:27
H 10.0.0.1/32 is directly connected, 00:06:38, Tunnel1
S % 10.0.1.1/32 is directly connected, Tunnel0
C 10.0.1.3/32 is directly connected, Tunnel0
H 10.0.1.4/32 is directly connected, 00:01:30, Virtual-Access1
S 10.0.2.1/32 is directly connected, Tunnel1
C 10.0.2.3/32 is directly connected, Tunnel1
H 10.0.2.4/32 [250/1] via 10.0.2.3, 00:01:30, Virtual-Access1
172.16.0.0/16 is variably subnetted, 2 subnets, 2 masks
C 172.16.0.0/24 is directly connected, Ethernet0/0
L 172.16.0.3/32 is directly connected, Ethernet0/0
B 192.168.0.0/16 [200/0] via 10.0.1.1, 00:06:27
192.168.3.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.3.0/24 is directly connected, Ethernet0/1
L 192.168.3.3/32 is directly connected, Ethernet0/1
192.168.4.0/32 is subnetted, 1 subnets
H 192.168.4.4 [250/1] via 10.0.1.3, 00:01:30, Virtual-Access1
En R3-Spoke1, la tabla BGP tiene dos entradas para la red 192.168.0.0/16 con diferentes preferencias locales (se prefiere R1-Hub1):
R3-SPOKE1#show ip bgp 192.168.0.0/16
BGP routing table entry for 192.168.0.0/16, version 8
Paths: (2 available, best #2, table default)
Not advertised to any peer
Refresh Epoch 1
Local
10.0.2.1 from 10.0.2.1 (10.0.2.1)
Origin incomplete, metric 0, localpref 100, valid, internal
rx pathid: 0, tx pathid: 0
Refresh Epoch 1
Local
10.0.1.1 from 10.0.1.1 (10.0.1.1)
Origin incomplete, metric 0, localpref 200, valid, internal, best
rx pathid: 0, tx pathid: 0x0
Esta es la tabla de ruteo R5-AGGR1 en un escenario operativo normal:
R5-LAN1#show ip route
10.0.0.0/8 is variably subnetted, 10 subnets, 3 masks
B 10.0.0.0/8 [200/0] via 192.168.0.1, 00:07:22
B 10.0.0.0/24 [200/0] via 192.168.0.1, 00:07:22
B 10.0.1.1/32 [200/0] via 192.168.0.1, 00:07:22
B 10.0.1.3/32 [200/0] via 192.168.0.1, 00:07:17
B 10.0.1.4/32 [200/0] via 192.168.0.1, 00:07:16
B 10.0.2.1/32 [200/0] via 192.168.0.2, 15:44:13
B 10.0.2.3/32 [200/0] via 192.168.0.2, 15:44:13
B 10.0.2.4/32 [200/0] via 192.168.0.2, 15:44:13
C 10.0.5.1/32 is directly connected, Loopback0
B 10.0.6.1/32 [200/0] via 192.168.0.6, 00:07:22
172.16.0.0/24 is subnetted, 1 subnets
B 172.16.0.0 [200/0] via 192.168.0.1, 00:07:22
B 192.168.0.0/16 [200/0] via 192.168.0.1, 00:07:22
192.168.0.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.0.0/24 is directly connected, Ethernet0/0
L 192.168.0.5/32 is directly connected, Ethernet0/0
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.1.0/24 is directly connected, Ethernet0/1
L 192.168.1.5/32 is directly connected, Ethernet0/1
B 192.168.3.0/24 [200/0] via 10.0.1.3, 00:07:06
B 192.168.4.0/24 [200/0] via 10.0.1.4, 00:07:15
Esta es la tabla de ruteo R7-HOST en un escenario operativo normal:
R7-HOST#show ip route
S* 0.0.0.0/0 [1/0] via 192.168.1.254
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.1.0/24 is directly connected, Ethernet0/0
L 192.168.1.7/32 is directly connected, Ethernet0/0
Escenario de falla HUB1
Este es un escenario de inactividad R1-HUB1 (debido a acciones como cortes de energía o una actualización):
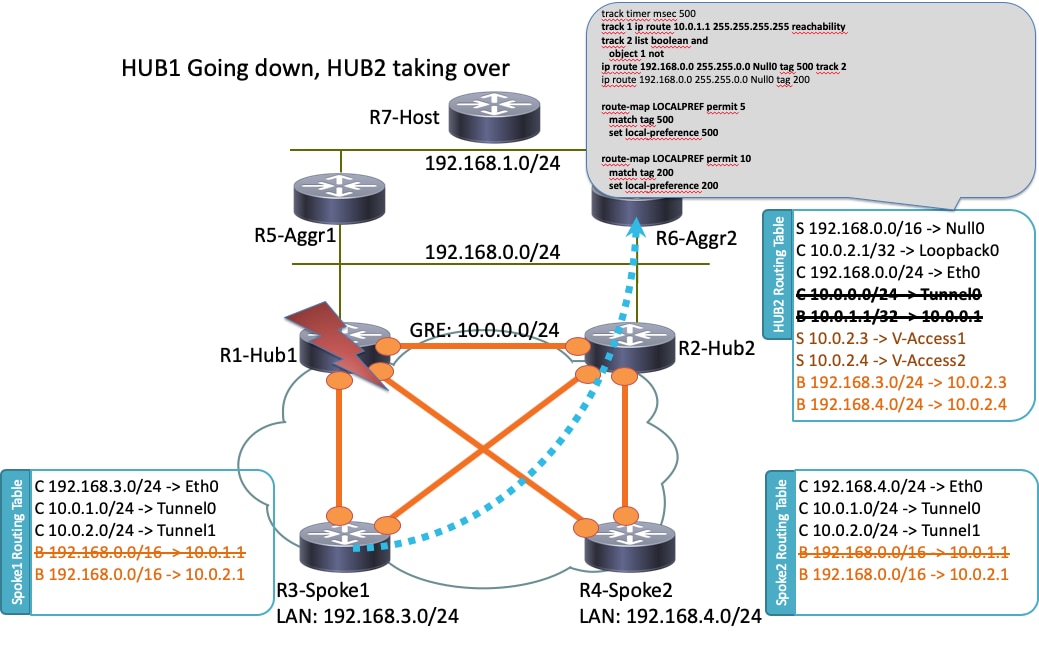
En este escenario, se produce esta secuencia de eventos:
- El BFD en R2-HUB2 y en los routers de agregación LAN R5-AGGR1 y R6-AGGR2 detecta el estado de inactividad de R1-HUB1. Como resultado, la vecindad BGP se desactiva inmediatamente.
- La detección del objeto de pista para R2-HUB2 que detecta la presencia del loopback R1-HUB1 se desactiva (Track 1 en la configuración de ejemplo).
- Este objeto de seguimiento descartado activa otra pista para subir (Logical NOT). En este ejemplo, el Track 2 aumenta cada vez que el Track 1 se desactiva.
- Esto activa una entrada de ruteo IP estática que se agregará a la tabla de ruteo debido a un valor que es inferior a la distancia administrativa predeterminada. Esta es la configuración relevante:
! Routes added when second HUB is down
ip route 10.0.0.0 255.0.0.0 Null0 tag 500 track 2
ip route 192.168.0.0 255.255.0.0 Null0 tag 500 track 2
! Default static routes are with Tag 200 and admin distance of 150
ip route 10.0.0.0 255.0.0.0 Null0 150 tag 200
ip route 192.168.0.0 255.255.0.0 Null0 150 tag 200 - R2-HUB2 redistribuye estas rutas estáticas con una preferencia local BGP que es mayor que el valor configurado para R1-HUB1. En este ejemplo, se utiliza una preferencia local de 500 en el escenario de falla, en lugar de 200 que se establece por R1-HUB1:
route-map LOCALPREF permit 5
match tag 500
set local-preference 500
!
route-map LOCALPREF permit 10
match tag 200
set local-preference 200
!
En R3-Spoke1, puede ver esto en los resultados de BGP. Tenga en cuenta que la entrada a R1 aún existe, pero no se utiliza:
R3-SPOKE1#show ip bgp 192.168.0.0/16
BGP routing table entry for 192.168.0.0/16, version 10
Paths: (2 available, best #1, table default)
Not advertised to any peer
Refresh Epoch 1
Local
10.0.2.1 from 10.0.2.1 (10.0.2.1)
Origin incomplete, metric 0, localpref 500, valid, internal, best
rx pathid: 0, tx pathid: 0x0
Refresh Epoch 1
Local
10.0.1.1 from 10.0.1.1 (10.0.1.1)
Origin incomplete, metric 0, localpref 200, valid, internal
rx pathid: 0, tx pathid: 0 - En este punto, ambos radios (R3-Spoke1 y R4-Spoke2) comienzan a enviar tráfico a R2-HUB2. Todos estos pasos deben darse en un segundo. Esta es la tabla de ruteo en el Spoke 3:
R3-SPOKE1#show ip route
10.0.0.0/8 is variably subnetted, 5 subnets, 2 masks
B 10.0.0.0/8 [200/0] via 10.0.2.1, 00:00:01
S 10.0.1.1/32 is directly connected, Tunnel0
C 10.0.1.3/32 is directly connected, Tunnel0
S 10.0.2.1/32 is directly connected, Tunnel1
C 10.0.2.3/32 is directly connected, Tunnel1
172.16.0.0/16 is variably subnetted, 2 subnets, 2 masks
C 172.16.0.0/24 is directly connected, Ethernet0/0
L 172.16.0.3/32 is directly connected, Ethernet0/0
B 192.168.0.0/16 [200/0] via 10.0.2.1, 00:00:01
192.168.3.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.3.0/24 is directly connected, Ethernet0/1
L 192.168.3.3/32 is directly connected, Ethernet0/1 - Las sesiones BGP posteriores entre los radios y R1-HUB1 se desactivan y la Detección de Peer Muerto (DPD) elimina los túneles IPSec que se terminan en R1-HUB1. Sin embargo, esto no afecta al reenvío de tráfico, ya que R2-HUB2 ya se utiliza como gateway de terminación de túnel principal:
R3-SPOKE1#show ip bgp 192.168.0.0/16
BGP routing table entry for 192.168.0.0/16, version 10
Paths: (1 available, best #1, table default)
Not advertised to any peer
Refresh Epoch 1
Local
10.0.2.1 from 10.0.2.1 (10.0.2.1)
Origin incomplete, metric 0, localpref 500, valid, internal, best
rx pathid: 0, tx pathid: 0x0
Configuraciones
Esta sección proporciona configuraciones de ejemplo para los hubs y radios que se utilizan en esta topología.
Configuración R1-HUB
version 15.4
!
hostname R1-HUB1
!
aaa new-model
!
aaa authorization network default local
!
aaa session-id common
!
! setting track timers to the lowest possible (the lower this value is
! the faster router will react
track timer ip route msec 500
!
! Monitoring of HUB2's loopback present in routing table
! If it is present it will mean that HUB2 is alive
track 1 ip route 10.0.2.1 255.255.255.255 reachability
!
! Monitoring of loopback of R5-AGGR-1
track 3 ip route 10.0.5.1 255.255.255.255 reachability
!
! Monitoring of loopback of R6-AGGR-2
track 4 ip route 10.0.6.1 255.255.255.255 reachability
!
! Track 2 should be UP only when HUB2 is not available and both AGGRE routers are up
!
track 2 list boolean and
object 1 not
object 3
object 4
!
! IKEv2 Config Exchange configuration (IP addresses for spokes are assigned from pool)
crypto ikev2 authorization policy default
pool SPOKES
route set interface
route accept any tag 20
!
!
! IKEv2 profile for Spokes - Smart Defaults used
crypto ikev2 profile default
match identity remote any
authentication remote pre-share key cisco
authentication local pre-share key cisco
aaa authorization group psk list default default
virtual-template 1
!
interface Loopback0
ip address 10.0.1.1 255.255.255.255
!
! GRE Tunnel configured to second HUB. It is required for spoke-to-spoke connectivity
! to work in all possible circumstances
! no BFD echo configuration is required to avoid Traffic Indication sent by remote HUB
! (BFD echo is having the same source and destination IP address)
!
interface Tunnel0
ip address 10.0.0.1 255.255.255.0
ip nhrp network-id 1
ip nhrp redirect
bfd interval 50 min_rx 50 multiplier 3
no bfd echo
tunnel source Ethernet0/2
tunnel destination 192.168.0.2
!
interface Ethernet0/0
ip address 172.16.0.1 255.255.255.0
!
interface Ethernet0/2
ip address 192.168.0.1 255.255.255.0
bfd interval 50 min_rx 50 multiplier 5
!
interface Virtual-Template1 type tunnel
ip unnumbered Loopback0
ip nhrp network-id 1
ip nhrp redirect
tunnel protection ipsec profile default
!
! BGP Configuration
router bgp 1
bgp log-neighbor-changes
! dynamic peer-groups are used for AGGR routers and SPOKES
bgp listen range 192.168.0.0/24 peer-group DC
bgp listen range 10.0.1.0/24 peer-group SPOKES
! BGP timers configured
timers bgp 15 30
neighbor SPOKES peer-group
neighbor SPOKES remote-as 1
neighbor DC peer-group
neighbor DC remote-as 1
! Within DC BFD is used to determine neighbour status
neighbor DC fall-over bfd
neighbor 10.0.0.2 remote-as 1
! BFD is used to detect HUB2 status
neighbor 10.0.0.2 fall-over bfd
!
address-family ipv4
redistribute connected
! route-map which determines what should be the local-pref
redistribute static route-map LOCALPREF
neighbor SPOKES activate
! to spokes only Aggregate/Summary routes are sent
neighbor SPOKES route-map AGGR out
neighbor DC activate
neighbor DC route-reflector-client
neighbor 10.0.0.2 activate
neighbor 10.0.0.2 route-reflector-client
exit-address-family
!
ip local pool SPOKES 10.0.1.2 10.0.1.254
!
! When HUB2 goes down Static Routes with Tag 500 are added and admin distance of 1
ip route 10.0.0.0 255.0.0.0 Null0 tag 500 track 2
ip route 192.168.0.0 255.255.0.0 Null0 tag 500 track 2
! Default static routes are with Tag 200 and admin distance of 150
ip route 10.0.0.0 255.0.0.0 Null0 150 tag 200
ip route 192.168.0.0 255.255.0.0 Null0 150 tag 200
!
!
ip prefix-list AGGR seq 5 permit 192.168.0.0/16
ip prefix-list AGGR seq 10 permit 10.0.0.0/8
!
route-map AGGR permit 10
match ip address prefix-list AGGR
!
route-map LOCALPREF permit 5
match tag 500
set local-preference 500
!
route-map LOCALPREF permit 10
match tag 200
set local-preference 200
!
route-map LOCALPREF permit 15
match tag 20
Configuración R2-HUB2
hostname R2-HUB2
!
aaa new-model
!
aaa authorization network default local
!
track timer ip route msec 500
!
track 1 ip route 10.0.1.1 255.255.255.255 reachability
!
track 2 list boolean and
object 1 not
object 3
object 4
!
track 3 ip route 10.0.5.1 255.255.255.255 reachability
!
track 4 ip route 10.0.6.1 255.255.255.255 reachability
!
!
crypto ikev2 authorization policy default
pool SPOKES
route set interface
route accept any tag 20
!
!
crypto ikev2 profile default
match identity remote any
authentication remote pre-share key cisco
authentication local pre-share key cisco
aaa authorization group psk list default default
virtual-template 1
!
!
interface Loopback0
ip address 10.0.2.1 255.255.255.255
!
interface Tunnel0
ip address 10.0.0.2 255.255.255.0
ip nhrp network-id 1
ip nhrp redirect
bfd interval 50 min_rx 50 multiplier 3
no bfd echo
tunnel source Ethernet0/2
tunnel destination 192.168.0.1
!
interface Ethernet0/0
ip address 172.16.0.2 255.255.255.0
!
interface Ethernet0/2
ip address 192.168.0.2 255.255.255.0
bfd interval 50 min_rx 50 multiplier 5
!
interface Virtual-Template1 type tunnel
ip unnumbered Loopback0
ip nhrp network-id 1
ip nhrp redirect
tunnel protection ipsec profile default
!
router bgp 1
bgp log-neighbor-changes
bgp listen range 192.168.0.0/24 peer-group DC
bgp listen range 10.0.2.0/24 peer-group SPOKES
timers bgp 15 30
neighbor SPOKES peer-group
neighbor SPOKES remote-as 1
neighbor DC peer-group
neighbor DC remote-as 1
neighbor DC fall-over bfd
neighbor 10.0.0.1 remote-as 1
neighbor 10.0.0.1 fall-over bfd
!
address-family ipv4
redistribute connected
redistribute static route-map LOCALPREF
neighbor SPOKES activate
neighbor SPOKES route-map AGGR out
neighbor DC activate
neighbor DC route-reflector-client
neighbor 10.0.0.1 activate
neighbor 10.0.0.1 route-reflector-client
exit-address-family
!
ip local pool SPOKES 10.0.2.2 10.0.2.254
ip forward-protocol nd
!
!
ip route 192.168.0.0 255.255.0.0 Null0 tag 500 track 2
ip route 10.0.0.0 255.0.0.0 Null0 tag 500 track 2
ip route 10.0.0.0 255.0.0.0 Null0 150 tag 200
ip route 192.168.0.0 255.255.0.0 Null0 150 tag 200
!
!
ip prefix-list AGGR seq 5 permit 192.168.0.0/16
ip prefix-list AGGR seq 10 permit 10.0.0.0/8
!
route-map AGGR permit 10
match ip address prefix-list AGGR
!
route-map LOCALPREF permit 5
match tag 500
set local-preference 500
!
route-map LOCALPREF permit 10
match tag 200
set local-preference 100
!
route-map LOCALPREF permit 15
match tag 20
Configuración de R3-SPOKE1
hostname R3-SPOKE1
!
aaa new-model
!
aaa authorization network default local
!
!
crypto ikev2 authorization policy default
route set interface
!
!
crypto ikev2 profile default
match identity remote any
authentication remote pre-share key cisco
authentication local pre-share key cisco
dpd 10 2 on-demand
aaa authorization group psk list default default
!
! Tunnel to the HUB1
!
interface Tunnel0
ip address negotiated
ip nhrp network-id 1
ip nhrp shortcut virtual-template 2
tunnel source Ethernet0/0
tunnel destination 172.16.0.1
tunnel protection ipsec profile default
!
! Tunnel to the HUB2
!
interface Tunnel1
ip address negotiated
ip nhrp network-id 1
ip nhrp shortcut virtual-template 2
tunnel source Ethernet0/0
tunnel destination 172.16.0.2
tunnel protection ipsec profile default
!
interface Ethernet0/0
description INTERNET-CLOUD
ip address 172.16.0.3 255.255.255.0
!
interface Ethernet0/1
description LAN
ip address 192.168.3.3 255.255.255.0
!
interface Virtual-Template2 type tunnel
ip unnumbered Ethernet0/1
ip nhrp network-id 1
ip nhrp shortcut virtual-template 2
tunnel protection ipsec profile default
!
router bgp 1
bgp log-neighbor-changes
timers bgp 15 30
neighbor 10.0.1.1 remote-as 1
neighbor 10.0.2.1 remote-as 1
!
address-family ipv4
network 192.168.3.0
neighbor 10.0.1.1 activate
neighbor 10.0.2.1 activate
exit-address-family
Configuración de R4-SPOKE2
hostname R4-SPOKE2
!
aaa new-model
!
aaa authorization network default local
!
!
crypto ikev2 authorization policy default
route set interface
!
crypto ikev2 profile default
match identity remote any
authentication remote pre-share key cisco
authentication local pre-share key cisco
dpd 10 2 on-demand
aaa authorization group psk list default default
!
interface Tunnel0
ip address negotiated
ip nhrp network-id 1
ip nhrp shortcut virtual-template 2
tunnel source Ethernet0/0
tunnel destination 172.16.0.1
tunnel protection ipsec profile default
!
interface Tunnel1
ip address negotiated
ip nhrp network-id 1
ip nhrp shortcut virtual-template 2
tunnel source Ethernet0/0
tunnel destination 172.16.0.2
tunnel protection ipsec profile default
!
interface Ethernet0/0
ip address 172.16.0.4 255.255.255.0
!
interface Ethernet0/1
ip address 192.168.4.4 255.255.255.0
!
interface Virtual-Template2 type tunnel
ip unnumbered Ethernet0/1
ip nhrp network-id 1
ip nhrp shortcut virtual-template 2
tunnel protection ipsec profile default
!
router bgp 1
bgp log-neighbor-changes
timers bgp 15 30
neighbor 10.0.1.1 remote-as 1
neighbor 10.0.2.1 remote-as 1
!
address-family ipv4
network 192.168.4.0
neighbor 10.0.1.1 activate
neighbor 10.0.2.1 activate
exit-address-family
!
Configuración de R5-AGGR1
hostname R5-LAN1
!
no aaa new-model
!
!
interface Loopback0
ip address 10.0.5.1 255.255.255.255
!
interface Ethernet0/0
ip address 192.168.0.5 255.255.255.0
bfd interval 50 min_rx 50 multiplier 5
!
! HSRP configuration on the LAN side
!
interface Ethernet0/1
ip address 192.168.1.5 255.255.255.0
standby 1 ip 192.168.1.254
!
router bgp 1
bgp log-neighbor-changes
neighbor 192.168.0.1 remote-as 1
neighbor 192.168.0.1 fall-over bfd
neighbor 192.168.0.2 remote-as 1
neighbor 192.168.0.2 fall-over bfd
!
address-family ipv4
redistribute connected
redistribute static
neighbor 192.168.0.1 activate
neighbor 192.168.0.2 activate
exit-address-family
Configuración de R6-AGGR2
hostname R6-LAN2
!
interface Loopback0
ip address 10.0.6.1 255.255.255.255
!
interface Ethernet0/0
ip address 192.168.0.6 255.255.255.0
bfd interval 50 min_rx 50 multiplier 5
!
interface Ethernet0/1
ip address 192.168.1.6 255.255.255.0
standby 1 ip 192.168.1.254
standby 1 priority 200
!
router bgp 1
bgp log-neighbor-changes
neighbor 192.168.0.1 remote-as 1
neighbor 192.168.0.1 fall-over bfd
neighbor 192.168.0.2 remote-as 1
neighbor 192.168.0.2 fall-over bfd
!
address-family ipv4
redistribute connected
redistribute static
neighbor 192.168.0.1 activate
neighbor 192.168.0.2 activate
exit-address-family
!
Configuración R7-HOST (simulación de HOST en esa red)
hostname R7-HOST
!
no aaa new-model
!
interface Ethernet0/0
ip address 192.168.1.7 255.255.255.0
!
ip route 0.0.0.0 0.0.0.0 192.168.1.254
Notas de configuración importantes
Estas son algunas notas importantes sobre las configuraciones que se describen en las secciones anteriores:
- El túnel GRE punto a punto entre los dos concentradores es necesario para que la conectividad de radio a radio funcione en todos los escenarios, específicamente para incluir aquellos escenarios en los que algunos de los radios están conectados solamente a uno de los concentradores y otros a otro concentrador.
- La configuración no bfd echo en la interfaz de túnel GRE entre los dos ejes de conexión es necesaria para evitar la indicación de tráfico que se envía desde otro hub. El eco BFD tiene la misma dirección IP de origen y de destino, que es igual a la dirección IP del router que envía el eco BFD. Dado que estos paquetes son ruteados nuevamente por el router que responde, se generan las Indicaciones de Tráfico NHRP.
- En la configuración de BGP, el filtrado de route-map que anuncia las redes hacia los spokes no es necesario, pero hace que las configuraciones sean más óptimas ya que solamente se anuncian las rutas de agregado/resumen:
neighbor SPOKES route-map AGGR out
- En los hubs, la configuración route-map LOCALPREF es necesaria para configurar la preferencia local BGP adecuada, y filtra las rutas estáticas redistribuidas solamente a las rutas de modo de configuración de resumen e IKEv2.
- Este diseño no aborda la redundancia en las ubicaciones de oficinas remotas (spoke). Si el link WAN en el spoke deja de funcionar, VPN tampoco funciona. Agregue un segundo link al router spoke o un segundo router spoke dentro de la misma ubicación para abordar este problema.
En resumen, el diseño de redundancia que se presenta en este documento puede tratarse como una alternativa moderna a la función Stateful Switchover (SSO)/Stateful. Es muy flexible y se puede ajustar con precisión para cumplir sus requisitos de implementación específicos.
Verificación
Actualmente, no hay un procedimiento de verificación disponible para esta configuración.
Troubleshoot
Actualmente, no hay información específica de troubleshooting disponible para esta configuración.
Información Relacionada
Con la colaboración de ingenieros de Cisco
- Piotr KupisiewiczCisco TAC Engineer
- Wen ZhangCisco TAC Engineer
- Frederic DetienneCisco TAC Engineer
Contacte a Cisco
- Abrir un caso de soporte

- (Requiere un Cisco Service Contract)
 Comentarios
Comentarios