SDWAN Configuration Syslog Cisco IOS XE TLS sur le serveur syslog-ng
Options de téléchargement
-
ePub (347.9 KB)
Consulter à l’aide de différentes applications sur iPhone, iPad, Android ou Windows Phone -
Mobi (Kindle) (210.8 KB)
Consulter sur un appareil Kindle ou à l’aide d’une application Kindle sur plusieurs appareils
Langage exempt de préjugés
Dans le cadre de la documentation associée à ce produit, nous nous efforçons d’utiliser un langage exempt de préjugés. Dans cet ensemble de documents, le langage exempt de discrimination renvoie à une langue qui exclut la discrimination en fonction de l’âge, des handicaps, du genre, de l’appartenance raciale de l’identité ethnique, de l’orientation sexuelle, de la situation socio-économique et de l’intersectionnalité. Des exceptions peuvent s’appliquer dans les documents si le langage est codé en dur dans les interfaces utilisateurs du produit logiciel, si le langage utilisé est basé sur la documentation RFP ou si le langage utilisé provient d’un produit tiers référencé. Découvrez comment Cisco utilise le langage inclusif.
À propos de cette traduction
Cisco a traduit ce document en traduction automatisée vérifiée par une personne dans le cadre d’un service mondial permettant à nos utilisateurs d’obtenir le contenu d’assistance dans leur propre langue. Il convient cependant de noter que même la meilleure traduction automatisée ne sera pas aussi précise que celle fournie par un traducteur professionnel.
Table des matières
Introduction
Ce document décrit un guide complet de configuration d'un serveur Syslog TLS sur des périphériques SD-WAN Cisco IOS® XE.
Conditions préalables
Avant de procéder à la configuration d'un serveur Syslog TLS sur des périphériques SD-WAN Cisco IOS XE, assurez-vous que vous remplissez les conditions suivantes :
Exigences
Cisco vous recommande de prendre connaissance des rubriques suivantes :
-
Contrôleurs SD-WAN - Assurez-vous que votre réseau inclut des contrôleurs SD-WAN correctement configurés.
-
Routeur SD-WAN Cisco IOS XE : routeur compatible exécutant l'image SD-WAN Cisco IOS XE.
-
Serveur Syslog : serveur Syslog basé sur Ubuntu, tel que syslog-ng, afin de collecter et de gérer les données de journal.
Composants utilisés
Les informations contenues dans ce document sont basées sur les versions de matériel et de logiciel suivantes :
-
vManage: Version 20.9.4
-
SD-WAN Cisco IOS XE : Version 17.9.4
-
Ubuntu : Version 22.04
-
syslog-ng : Version 3.27
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. Si votre réseau est en ligne, assurez-vous de bien comprendre l’incidence possible des commandes.
Configuration
1. Installation de syslog-ng sur la machine Ubuntu
Afin de configurer syslog-ng sur votre serveur Ubuntu, suivez ces étapes pour assurer une installation et une configuration correctes.
Étape 1. Configurer les paramètres réseau
Après avoir installé Ubuntu Server, configurez une adresse IP statique et un serveur DNS afin de garantir que la machine peut accéder à Internet. C'est essentiel pour télécharger des paquets et des mises à jour.
Étape 2 : installation de syslog-ng
Ouvrez un terminal sur votre machine Ubuntu et exécutez :
sudo apt-get install syslog-ng sudo apt-get install syslog-ng openssl2. Installer l'autorité de certification racine sur le serveur Syslog pour l'authentification du serveur
Créer des répertoires et générer des clés
cd /etc/syslog-ng mkdir cert.d key.d ca.d cd cert.d openssl genrsa -out ca.key 2048 openssl req -new -x509 -key ca.key -out PROXY-SIGNING-CA.ca -days 730 # Copy key to the key.d folder cp ca.key ../key.dCalculer les empreintes
Exécutez la commande et copiez le résultat :
openssl x509 -in PROXY-SIGNING-CA.ca -fingerprint -noout | awk -F "=" '{print $2}' | sed 's/://g' | empreinte digitale.txt
# Exemple de résultat : 54F371C8EE2BFB06E2C2D0944245C288FBB07163
3. Configurez le fichier de configuration du serveur syslog-ng
Modifiez le fichier de configuration syslog-ng :
sudo nano /etc/syslog-ng/syslog-ng.confAjoutez la configuration :
source s_src { network( ip(0.0.0.0) port(6514) transport("tls") tls( key-file("/etc/syslog-ng/key.d/ca.key") cert-file("/etc/syslog-ng/cert.d/PROXY-SIGNING-CA.ca") peer-verify(optional-untrusted) ) ); }; destination remote { file("/var/log/syslog"); }; log { source(s_src); destination(remote); };4. Installer l'autorité de certification racine sur le périphérique SD-WAN Cisco IOS XE pour l'authentification du serveur
Configurer à partir de CLI
-
Passez en mode de configuration :
config-t-
Configurez le point de confiance :
crypto pki trustpoint PROXY-SIGNING-CA enrollment url bootflash: revocation-check none rsakeypair PROXY-SIGNING-CA 2048 subject-name cn=proxy-signing-cert fqdn none fingerprint 54F371C8EE2BFB06E2C2D0944245C288FBB07163 >> The fingerprint configured was obtained from the fingerprint.txt file above commit-
Copiez le PROXY-SIGNING-CA.ca de votre serveur syslog vers le bootflash du routeur en utilisant le même nom.
-
Authentifiez le point de confiance :
crypto pki authenticate PROXY-SIGNING-CA
example:
Router#crypto pki authenticate PROXY-SIGNING-CA
Reading file from bootflash:PROXY-SIGNING-CA.ca
Certificate has the attributes:
Fingerprint MD5: 7A97B30B 2AE458FF D9E7D91F 66488DCF
Fingerprint SHA1: 21E0F09B B67B2E9D 706DBE69 856E5AA3 D39A268A
Trustpoint Fingerprint: 21E0F09B B67B2E9D 706DBE69 856E5AA3 D39A268A
Certificate validated - fingerprints matched.
Trustpoint CA certificate accepted.-
Inscrivez le point de confiance :
crypto pki enroll PROXY-SIGNING-CA
example:
vm32#crypto pki enroll PROXY-SIGNING-CA
Start certificate enrollment ..
The subject name in the certificate will include: cn=proxy-signing-cert
The fully-qualified domain name will not be included in the certificate
Certificate request sent to file system
The 'show crypto pki certificate verbose PROXY-SIGNING-CA' commandwill show the fingerprint.
-
Copiez le PROXY-SIGNING-CA.req du routeur vers le serveur syslog.
Signature du certificat sur le serveur Syslog
openssl x509 -in PROXY-SIGNING-CA.req -req -CA PROXY-SIGNING-CA.ca -CAkey ca.key -out PROXY-SIGNING-CA.crt -CAcreateserial -extensions ca_extensions-
Copier le fichier généré (PROXY-SIGNING-CA.crt) au bootflash du routeur. copy scp : bootflash:
-
Importer le certificat :
crypto pki import PROXY-SIGNING-CA certificate
example:
Router# crypto pki import PROXY-SIGNING-CA certificate
% The fully-qualified domain name will not be included in the certificate
% Request to retrieve Certificate queuedValider la configuration
show crypto pki trustpoint PROXY-SIGNING-CA status
example:
Router#show crypto pki trustpoint PROXY-SIGNING-CA status
Trustpoint PROXY-SIGNING-CA:
Issuing CA certificate configured:
Subject Name:
o=Internet Widgits Pty Ltd,st=Some-State,c=AU
Fingerprint MD5: 7A97B30B 2AE458FF D9E7D91F 66488DCF
Fingerprint SHA1: 21E0F09B B67B2E9D 706DBE69 856E5AA3 D39A268A
Router General Purpose certificate configured:
Subject Name:
cn=proxy-signing-cert
Fingerprint MD5: 140A1EAB FE945D56 D1A53855 FF361F3F
Fingerprint SHA1: ECA67413 9C102869 69F582A4 73E2B98C 80EFD6D5
Last enrollment status: Granted
State:
Keys generated ............. Yes (General Purpose, non-exportable)
Issuing CA authenticated ....... Yes
Certificate request(s) ..... Yes5. Configuration du serveur Syslog TLS sur le routeur SD-WAN Cisco IOS XE
Configurez le serveur syslog à l'aide des commandes suivantes :
logging trap syslog-format rfc5424 logging source-interface GigabitEthernet0/0/0 logging tls-profile tls-profile logging host X.X.X.X transport tls profile tls-profile tls-version TLSv1.26. Vérifications
Vérification des journaux sur le routeur
show logging
Showing last 10 lines
Log Buffer (512000 bytes):
Apr 9 05:59:48.025: %DMI-5-CONFIG_I: R0/0: dmiauthd: Configured from NETCONF/RESTCONF by admin, transaction-id 189410
Apr 9 05:59:48.709: %DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:58393 for netconf over ssh. External groups:
Apr 9 05:59:50.015: %LINK-5-CHANGED: Interface GigabitEthernet0/0/1, changed state to administratively down
Apr 9 05:59:51.016: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0/1, changed state to down
Apr 9 05:59:52.242: %SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Vérification des journaux sur le serveur Syslog
tail -f /var/log/syslog
root@server1:/etc/syslog-ng# tail -f /var/log/syslog
Apr 9 15:51:14 10.66.91.94 188 <189>1 2024-04-09T05:51:51.037Z - - - - - BOM%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:38032 for netconf over ssh. External groups:
Apr 9 15:59:10 10.66.91.94 177 <189>1 2024-04-09T05:59:47.463Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Apr 9 15:59:10 10.66.91.94 177 <189>1 2024-04-09T05:59:47.463Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Apr 9 15:59:10 10.66.91.94 143 <189>1 2024-04-09T05:59:47.463Z - - - - - BOM%DMI-5-CONFIG_I: R0/0: dmiauthd: Configured from NETCONF/RESTCONF by admin, transaction-id 189410
Apr 9 15:59:11 10.66.91.94 188 <189>1 2024-04-09T05:59:48.711Z - - - - - BOM%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:58393 for netconf over ssh. External groups:
Apr 9 15:59:13 10.66.91.94 133 <189>1 2024-04-09T05:59:50.016Z - - - - - BOM%LINK-5-CHANGED: Interface GigabitEthernet0/0/1, changed state to administratively down
Apr 9 15:59:13 10.66.91.94 137 <189>1 2024-04-09T05:59:50.016Z - - - - - BOM%LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0/1, changed state to down
Apr 9 15:59:15 10.66.91.94 177 <189>1 2024-04-09T05:59:52.242Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Apr 9 15:59:15 10.66.91.94 177 <189>1 2024-04-09T05:59:52.242Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Apr 9 15:59:18 10.66.91.94 188 <189>1 2024-04-09T05:59:55.286Z - - - - - BOM%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:34575 for netconf over ssh. External groups:
Apr 9 15:59:21 10.66.91.94 113 <187>1 2024-04-09T05:59:58.882Z - - - - - BOM%LINK-3-UPDOWN: Interface GigabitEthernet0/0/1, changed state to up
Apr 9 15:59:21 10.66.91.94 135 <189>1 2024-04-09T05:59:59.882Z - - - - - BOM%LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0/1, changed state to up
Apr 9 15:59:28 10.66.91.94 177 <189>1 2024-04-09T06:00:05.536Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
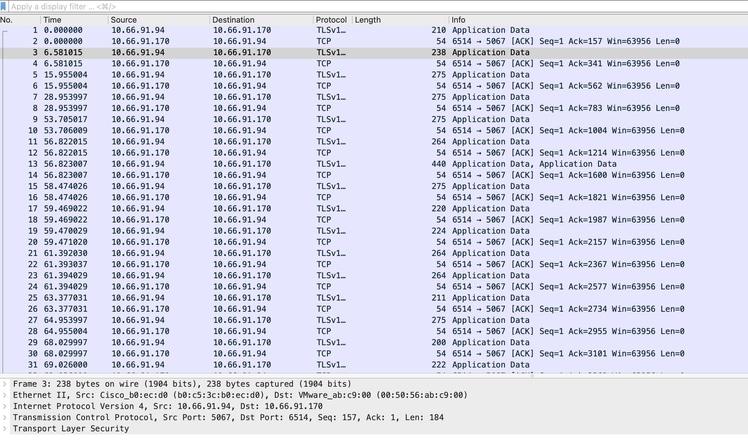
Apr 9 15:59:43 10.66.91.94 188 <189>1 2024-04-09T06:00:20.537Z - - - - - BOM%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:43530 for netconf over ssh. External groups:Capture d'écran de capture de paquets et affichage des communications chiffrées :
ISR4331-branch-NEW_Branch#show logging
Trap logging: level informational, 6284 message lines logged
Logging to 10.66.91.170 (tls port 6514, audit disabled,
link up),
131 message lines logged,
0 message lines rate-limited,
0 message lines dropped-by-MD,
xml disabled, sequence number disabled
filtering disabled
tls-profile: tls-proile
Logging Source-Interface: VRF Name:
GigabitEthernet0/0/0
TLS Profiles:
Profile Name: tls-proile
Ciphersuites: Default
Trustpoint: Default
TLS version: TLSv1.2Vérifier
Aucune procédure de vérification n'est disponible pour cette configuration.
Dépannage
Il n'existe actuellement aucune information de dépannage spécifique pour cette configuration.
Historique de révision
| Révision | Date de publication | Commentaires |
|---|---|---|
1.0 |
18-Dec-2024 |
Première publication |
Contribution d’experts de Cisco
- Md Aamir SadiqueResponsable technique du TAC Cisco
Contacter Cisco
- Ouvrir un dossier d’assistance

- (Un contrat de service de Cisco est requis)
 Commentaires
Commentaires