Router a tre interfacce senza configurazione NAT Cisco IOS Firewall
Sommario
Introduzione
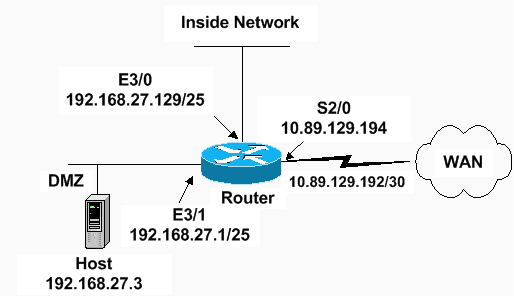
In questo documento viene illustrato un esempio di configurazione tipica per una piccola azienda connessa a Internet che esegue i propri server. La connessione a Internet avviene tramite una linea seriale. Ethernet 0 è collegato alla rete interna (una singola LAN). Ethernet 1 è collegato a una rete DMZ, che ha un singolo nodo utilizzato per fornire servizi al mondo esterno. L'ISP ha assegnato alla società il netblock 192.168.27.0/24. Tale subnet mask è suddivisa in due parti: la DMZ e la LAN interna con subnet mask 255.255.255.128. La policy di base prevede quanto segue:
-
Consente agli utenti della rete interna di connettersi a qualsiasi servizio della rete Internet pubblica.
-
Consentire a tutti gli utenti di Internet di connettersi ai servizi WWW, FTP e SMTP (Simple Mail Transfer Protocol) nel server DMZ e di eseguire query DNS (Domain Name System) in tale server. Questo consente agli utenti esterni di visualizzare le pagine Web della società, prelevare i file inviati dalla società per l'utilizzo esterno e inviare messaggi alla società.
-
Consentire agli utenti interni di connettersi al servizio POP sul server DMZ (per ritirare la posta) e di connettersi in modalità Telnet (per amministrarla).
-
Non consentire a nessun utente della zona demilitarizzata di avviare connessioni, né alla rete privata né a Internet.
-
Controllare tutte le connessioni che attraversano il firewall per raggiungere un server SYSLOG nella rete privata. I computer nella rete interna utilizzano il server DNS nella DMZ. Gli elenchi degli accessi agli input vengono usati su tutte le interfacce per impedire lo spoofing. Gli elenchi degli accessi di output vengono utilizzati per controllare il traffico che può essere inviato a una determinata interfaccia.
Per configurare un router a due interfacce senza NAT con Cisco IOS Firewall, consultare il documento sulla configurazione del firewall a due interfacce senza NAT con Cisco IOS® Firewall.
Per configurare un router a due interfacce con NAT usando un Cisco IOS Firewall, consultare il documento sulla configurazione del firewall a due interfacce con NAT.
Prerequisiti
Requisiti
Nessun requisito specifico previsto per questo documento.
Componenti usati
Le informazioni fornite in questo documento si basano sulle versioni software e hardware:
-
Software Cisco IOS release 12.2(15)T13 con set di funzionalità firewall
-
Router Cisco 7204 VXR
Le informazioni discusse in questo documento fanno riferimento a dispositivi usati in uno specifico ambiente di emulazione. Su tutti i dispositivi menzionati nel documento la configurazione è stata ripristinata ai valori predefiniti. Se la rete è operativa, valutare attentamente eventuali conseguenze derivanti dall'uso dei comandi.
Convenzioni
Fare riferimento a Cisco Technical Tips Conventions per ulteriori informazioni sulle convenzioni dei documenti.
Configurazione
In questa sezione vengono presentate le informazioni necessarie per configurare le funzionalità descritte più avanti nel documento.
Nota: per ulteriori informazioni sui comandi menzionati in questa sezione, usare lo strumento di ricerca dei comandi (solo utenti registrati).
Esempio di rete
Nel documento viene usata questa impostazione di rete:
Configurazioni
Nel documento viene usata questa configurazione.
| Router 7204 VXR |
|---|
version 12.2 service timestamps debug datetime msec service timestamps log datetime msec service password-encryption ! hostname Router ! logging queue-limit 100 enable secret 5 <something> ! ip subnet-zero ip cef no ip domain lookup ! ip inspect audit-trail ! !--- Sets the length of time a TCP session !--- is still managed after no activity. ! ip inspect tcp idle-time 14400 ! !--- Sets the length of time a UDP session !--- is still managed after no activity. ! ip inspect udp idle-time 1800 ! !--- Sets the length of time a DNS name lookup session !--- is still managed after no activity. ! ip inspect dns-timeout 7 ! !--- Sets up inspection list "standard" !--- to be used for inspection of inbound Ethernet 0 !--- and inbound serial (applied to both interfaces). ! ip inspect name standard cuseeme ip inspect name standard ftp ip inspect name standard h323 ip inspect name standard http ip inspect name standard rcmd ip inspect name standard realaudio ip inspect name standard smtp ip inspect name standard sqlnet ip inspect name standard streamworks ip inspect name standard tcp ip inspect name standard tftp ip inspect name standard udp ip inspect name standard vdolive ip audit notify log ip audit po max-events 100 ! no voice hpi capture buffer no voice hpi capture destination ! mta receive maximum-recipients 0 ! interface ethernet 3/0 ip address 192.168.27.129 255.255.255.128 ! !--- Apply the access list to allow all legitimate !--- traffic from the inside network and prevent spoofing. ! ip access-group 101 in ! !--- Apply inspection list "standard" for inspection !--- of inbound Ethernet traffic. This inspection opens !--- temporary entries on access lists 111 and 121. ! ip inspect standard in duplex full interface ethernet 3/1 ip address 192.168.27.1 255.255.255.128 ! !--- Apply the access list to permit DMZ traffic (except spoofing) !--- on the DMZ interface inbound. The DMZ is not permitted to initiate !--- any outbound traffic except Internet Control Message Protocol (ICMP). ! ip access-group 111 in ! !--- Apply inspection list "standard" for inspection of outbound !--- traffic from e1. This adds temporary entries on access list 111 !--- to allow return traffic, and protects servers in DMZ from !--- distributed denial of service (DDoS) attacks. ip inspect standard out duplex full ! interface serial 2/0 ip address 10.89.129.194 255.255.255.252 !--- Apply the access list to allow legitimate traffic. ! ip access-group 121 in serial restart_delay 0 ! ip classless no ip http-server !--- A syslog server is located at this address. logging 192.168.27.131 !--- This command enables the logging of session !--- information (addresses and bytes). !--- Access list 20 is used to control which !--- network management stations can access via SNMP. ! access-list 20 permit 192.168.27.5 ! !--- Use an access list to allow all legitimate traffic from !--- the inside network and prevent spoofing. The inside !--- network can only connect to the Telnet and POP3 !--- service of 192.168.27.3 on DMZ, and can ping (ICMP) to the DMZ. !--- Additional entries can be added to permit SMTP, WWW, and !--- so forth, if necessary. In addition, the inside network can !--- connect to any service on the Internet. ! access-list 101 permit tcp 192.168.27.128 0.0.0.127 host 192.168.27.3 eq pop3 access-list 101 permit tcp 192.168.27.128 0.0.0.127 host 192.168.27.3 eq telnet access-list 101 permit icmp 192.168.27.128 0.0.0.127 192.168.27.0 0.0.0.127 access-list 101 deny ip 192.168.27.128 0.0.0.127 192.168.27.0 0.0.0.127 access-list 101 permit ip 192.168.27.128 0.0.0.127 any access-list 101 deny ip any any ! ! !--- The access list permits ping (ICMP) from the DMZ and denies all !--- traffic initiated from the DMZ. Inspection opens !--- temporary entries to this list. ! access-list 111 permit icmp 192.168.27.0 0.0.0.127 any access-list 111 deny ip any any ! ! ! !--- Access list 121 allows anyone on the Internet to connect to !--- WWW, FTP, DNS, and SMTP services on the DMZ host. It also !--- allows some ICMP traffic. access-list 121 permit udp any host 192.168.27.3 eq domain access-list 121 permit tcp any host 192.168.27.3 eq domain access-list 121 permit tcp any host 192.168.27.3 eq www access-list 121 permit tcp any host 192.168.27.3 eq ftp access-list 121 permit tcp any host 192.168.27.3 eq smtp access-list 121 permit icmp any 192.168.27.0 0.0.0.255 administratively-prohibited access-list 121 permit icmp any 192.168.27.0 0.0.0.255 echo access-list 121 permit icmp any 192.168.27.0 0.0.0.255 echo-reply access-list 121 permit icmp any 192.168.27.0 0.0.0.255 packet-too-big access-list 121 permit icmp any 192.169.27.0 0.0.0.255 time-exceeded access-list 121 permit icmp any 192.168.27.0 0.0.0.255 traceroute access-list 121 permit icmp any 192.168.27.0 0.0.0.255 unreachable access-list 121 deny ip any any ! !--- Apply access list 20 for SNMP process. ! snmp-server community secret RO 20 snmp-server enable traps tty ! call rsvp-sync ! mgcp profile default ! dial-peer cor custom ! gatekeeper shutdown ! line con 0 exec-timeout 5 0 password 7 14191D1815023F2036 login local line vty 0 4 exec-timeout 5 0 password 7 14191D1815023F2036 login local length 35 end |
Verifica
Per verificare che la configurazione funzioni correttamente, consultare questa sezione.
Lo strumento Output Interpreter (solo utenti registrati) (OIT) supporta alcuni comandi show. Usare l'OIT per visualizzare un'analisi dell'output del comando show.
-
show access-list: verifica la configurazione corretta degli elenchi degli accessi configurati nella configurazione corrente.
Router#show access-list Standard IP access list 20 10 permit 192.168.27.5 Extended IP access list 101 10 permit tcp 192.168.27.128 0.0.0.127 host 192.168.27.3 eq pop3 20 permit tcp 192.168.27.128 0.0.0.127 host 192.168.27.3 eq telnet 30 permit icmp 192.168.27.128 0.0.0.127 192.168.27.0 0.0.0.127 40 deny ip 192.168.27.128 0.0.0.127 192.168.27.0 0.0.0.127 50 permit ip 192.168.27.128 0.0.0.127 any 60 deny ip any any Extended IP access list 111 10 permit icmp 192.168.27.0 0.0.0.127 any 20 deny ip any any (9 matches) Extended IP access list 121 10 permit udp any host 192.168.27.3 eq domain 20 permit tcp any host 192.168.27.3 eq domain 30 permit tcp any host 192.168.27.3 eq www 40 permit tcp any host 192.168.27.3 eq ftp 50 permit tcp any host 192.168.27.3 eq smtp 60 permit icmp any 192.168.27.0 0.0.0.255 administratively-prohibited 70 permit icmp any 192.168.27.0 0.0.0.255 echo 80 permit icmp any 192.168.27.0 0.0.0.255 echo-reply 90 permit icmp any 192.168.27.0 0.0.0.255 packet-too-big 100 permit icmp any 192.169.27.0 0.0.0.255 time-exceeded 110 permit icmp any 192.168.27.0 0.0.0.255 traceroute 120 permit icmp any 192.168.27.0 0.0.0.255 unreachable 130 deny ip any any (4866 matches) Router# -
show ip audit all: verifica la configurazione dei comandi di log.
Router#show ip audit all Event notification through syslog is enabled Event notification through Net Director is disabled Default action(s) for info signatures is alarm Default action(s) for attack signatures is alarm Default threshold of recipients for spam signature is 250 PostOffice:HostID:0 OrgID:0 Msg dropped:0 :Curr Event Buf Size:0 Configured:100 Post Office is not enabled - No connections are active Router# -
show ip inspect all: verifica la configurazione delle regole di ispezione del firewall Cisco IOS per interfaccia.
Router#show ip inspect all Session audit trail is enabled Session alert is enabled one-minute (sampling period) thresholds are [400:500] connections max-incomplete sessions thresholds are [400:500] max-incomplete tcp connections per host is 50. Block-time 0 minute. tcp synwait-time is 30 sec -- tcp finwait-time is 5 sec tcp idle-time is 14400 sec -- udp idle-time is 1800 sec dns-timeout is 7 sec Inspection Rule Configuration Inspection name standard cuseeme alert is on audit-trail is on timeout 14400 ftp alert is on audit-trail is on timeout 14400 h323 alert is on audit-trail is on timeout 14400 http alert is on audit-trail is on timeout 14400 rcmd alert is on audit-trail is on timeout 14400 realaudio alert is on audit-trail is on timeout 14400 smtp alert is on audit-trail is on timeout 14400 sqlnet alert is on audit-trail is on timeout 14400 streamworks alert is on audit-trail is on timeout 1800 tcp alert is on audit-trail is on timeout 14400 tftp alert is on audit-trail is on timeout 1800 udp alert is on audit-trail is on timeout 1800 vdolive alert is on audit-trail is on timeout 14400 Interface Configuration Interface Ethernet3/0 Inbound inspection rule is standard cuseeme alert is on audit-trail is on timeout 14400 ftp alert is on audit-trail is on timeout 14400 h323 alert is on audit-trail is on timeout 14400 http alert is on audit-trail is on timeout 14400 rcmd alert is on audit-trail is on timeout 14400 realaudio alert is on audit-trail is on timeout 14400 smtp alert is on audit-trail is on timeout 14400 sqlnet alert is on audit-trail is on timeout 14400 streamworks alert is on audit-trail is on timeout 1800 tcp alert is on audit-trail is on timeout 14400 tftp alert is on audit-trail is on timeout 1800 udp alert is on audit-trail is on timeout 1800 vdolive alert is on audit-trail is on timeout 14400 Outgoing inspection rule is not set Inbound access list is 101 Outgoing access list is not set Interface Ethernet3/1 Inbound inspection rule is not set Outgoing inspection rule is standard cuseeme alert is on audit-trail is on timeout 14400 ftp alert is on audit-trail is on timeout 14400 h323 alert is on audit-trail is on timeout 14400 http alert is on audit-trail is on timeout 14400 rcmd alert is on audit-trail is on timeout 14400 realaudio alert is on audit-trail is on timeout 14400 smtp alert is on audit-trail is on timeout 14400 sqlnet alert is on audit-trail is on timeout 14400 streamworks alert is on audit-trail is on timeout 1800 tcp alert is on audit-trail is on timeout 14400 tftp alert is on audit-trail is on timeout 1800 udp alert is on audit-trail is on timeout 1800 vdolive alert is on audit-trail is on timeout 14400 Inbound access list is 111 Outgoing access list is not set Router#
Risoluzione dei problemi
Dopo aver configurato il router del firewall IOS, se le connessioni non funzionano, verificare di aver abilitato l'ispezione con il comando ip inspect (nome definito) sull'interfaccia in o out. in questa configurazione, lo standard ip inspect in viene applicato all'interfaccia ethernet 3/0 e l'uscita standard ip inspect viene applicata all'interfaccia ethernet 3/1.
Per ulteriori informazioni sulla risoluzione dei problemi, fare riferimento a Risoluzione dei problemi di configurazione di Cisco IOS Firewall.
Informazioni correlate
Cronologia delle revisioni
| Revisione | Data di pubblicazione | Commenti |
|---|---|---|
1.0 |
20-Feb-2007 |
Versione iniziale |
 Feedback
Feedback