TACACS+ verificatie voor VPDN’s configureren
Inhoud
Inleiding
Een Virtual Private Dial-Up Network (VPDN) maakt het mogelijk dat een inbelverbinding van een privaat netwerk zich over de externe toegangsservers uitstrekt (gedefinieerd als de L2TP Access Concentrator [LAC]). Wanneer een Point-to-Point Protocol (PPP)-client in een LAC wordt gedraaid, bepaalt de LAC dat die PPP-sessie moet worden doorgestuurd naar een L2TP-netwerkserver (LNS) voor die client, die vervolgens de gebruiker verifieert en de PPP-onderhandeling start. Zodra de PPP-instelling is voltooid, worden alle frames via de LAC naar de client en de LAN’s verzonden.
Met deze voorbeeldconfiguratie kunt u TACACS+ verificatie gebruiken met Virtual Private Dial-Up Networks (VPDN’s). De LAC vraagt de TACACS+ server, bepaalt welke LNS om de gebruiker door te sturen, en stelt de juiste tunnel vast.
Raadpleeg begrip van VPDN voor meer informatie over VPDN’s.
Voorwaarden
Vereisten
Er zijn geen specifieke vereisten van toepassing op dit document.
Gebruikte componenten
De informatie in dit document is gebaseerd op de volgende software- en hardware-versies:
-
Cisco Secure ACS voor UNIX versie 2.x.x en hoger voor TACACS+ freeware
-
Cisco IOS®-softwarerelease 11.2 en hoger
De informatie in dit document is gebaseerd op de apparaten in een specifieke laboratoriumomgeving. Alle apparaten die in dit document worden beschreven, hadden een opgeschoonde (standaard)configuratie. Als uw netwerk live is, moet u de potentiële impact van elke opdracht begrijpen.
Conventies
Raadpleeg Cisco Technical Tips Conventions (Conventies voor technische tips van Cisco) voor meer informatie over documentconventies.
Configureren
In deze sectie wordt de informatie weergegeven die nodig is om de functies te configureren die in dit document worden beschreven.
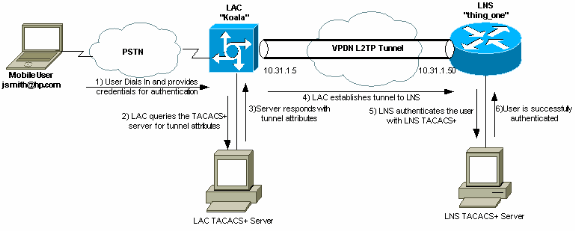
In dit voorbeeld, is de gebruiker "jsmith@hp.com" met wachtwoord "test". Wanneer "jsmith@hp.com" in de ISP router inschakelt, stuurt de ISP router "hp.com" user-id naar de ISP TACACS+ server. De ISP server vindt de "hp.com"-gebruikersnaam en stuurt zijn tunnel-id ("isp"), het IP-adres van de thuisgateway (HGW)-router (10.31.1.50), het wachtwoord van de Network Access Server (NAS) ("hello") en het gateway-wachtwoord ("daar") terug naar de ISP-router.
De ISP router initieert een tunnel en verbindt met de HGW router, die de wachtwoorden voor gebruikerid "hp-gw" ("daar") en toen gebruikerid "isp" ("hello") aan de HGW TACACS+ server door:sturen. Zodra de tunnels zijn opgezet, stuurt de ISP router de gebruikersnaam ("jsmith@hp.com") en het wachtwoord ("test") van de gebruiker die inbelt naar de HGW router. Deze gebruiker wordt geverifieerd op de HGW-server. In de voorbeeldconfiguraties in dit document is de naam van de ISP-routerhost "koala" en de naam van de HGW-routerhost "thing_one".
Opmerking: Gebruik Command Lookup Tool (alleen voor geregistreerde klanten) voor meer informatie over de opdrachten die in dit document worden gebruikt.
Netwerkdiagram
Dit document gebruikt de netwerkinstallatie die in dit diagram wordt getoond.
TACACS+ serverconfiguraties
Dit document maakt gebruik van de serverconfiguraties die hier worden getoond.
Software voor TACACS+
!--- This user is on the ISP TACACS+ server. !--- The profile includes the Tunnel ID ("isp"), the IP address !--- of the Peer (10.31.1.50), !--- and the passwords used to authenticate the tunnel. !--- The ISP uses these attibutes to establish the tunnel.
user = hp.com {
service = ppp protocol = vpdn {
tunnel-id = isp
ip-addresses = "10.31.1.50"
nas-password = "hello"
gw-password = "there"
}
}
!--- The next three users are on the HGW server.
user = isp {
chap = cleartext "hello"
service = ppp protocol = ip {
default attribute = permit
}
}
user = hp-gw {
chap = cleartext "there"
service = ppp protocol = ip {
default attribute = permit
}
}
user = jsmith@hp.com {
chap = cleartext "test"
service = ppp protocol = ip {
default attribute = permit
}
}
Cisco Secure ACS voor UNIX 2.x.x
!--- This user is on the ISP server.
# ./ViewProfile -p 9900 -u hp.com
User Profile Information
user = hp.com{
profile_id = 83
profile_cycle = 1
service=ppp {
protocol=vpdn {
set tunnel-id=isp
set ip-addresses="10.31.1.50"
set nas-password="hello"
set gw-password="there"
}
protocol=lcp {
}
}
}
!--- The next three users are on the HGW server. !--- The next two usernames are used to authenticate the LAC !--- during tunnel initialization.
# ./ViewProfile -p 9900 -u isp
User Profile Information
user = isp{
profile_id = 84
profile_cycle = 1
password = chap "********"
service=ppp {
protocol=ip {
default attribute=permit
}
protocol=lcp {
}
}
}
# ./ViewProfile -p 9900 -u hp-gw
User Profile Information
user = hp-gw{
profile_id = 82
profile_cycle = 1
password = chap "********"
service=ppp {
protocol=ip {
default attribute=permit
}
protocol=lcp {
}
}
}
!--- This username is used to authenticate the end user !--- after the tunnel is established.
# ./ViewProfile -p 9900 -u jsmith@hp.com
User Profile Information
user = jsmith@hp.com{
profile_id = 85
profile_cycle = 1
password = chap "********"
service=ppp {
protocol=ip {
default attribute=permit
}
protocol=lcp {
}
}
}
Routerconfiguraties
Dit document maakt gebruik van de hier getoonde configuraties.
| Configuratie van ISP-router |
|---|
koala#show running config Building configuration... Current configuration: ! version 11.2 no service password-encryption service udp-small-servers service tcp-small-servers ! hostname koala ! aaa new-model aaa authentication ppp default tacacs+ none aaa authorization network tacacs+ none aaa accounting network start-stop tacacs+ enable password ww ! !--- VPDN is enabled. vpdn enable ! interface Ethernet0 ip address 10.31.1.5 255.255.255.0 ! interface Serial0 shutdown ! interface Serial1 shutdown ! interface Async1 ip unnumbered Ethernet0 encapsulation ppp async mode dedicated no cdp enable ppp authentication chap ! ip default-gateway 10.31.1.1 no ip classless ip route 0.0.0.0 0.0.0.0 10.31.1.1 ! !--- Specify the TACACS server information on the NAS. tacacs-server host 171.68.120.194 tacacs-server key cisco no tacacs-server directed-request snmp-server community public RW snmp-server enable traps config ! line con 0 password ww line 1 16 password ww autoselect ppp modem InOut transport input all stopbits 1 rxspeed 115200 txspeed 115200 flowcontrol hardware line aux 0 line vty 0 4 exec-timeout 0 0 password ww ! end |
| Configuratie van HGW-router |
|---|
thing_one#show running config
Building configuration...
Current configuration:
!
version 11.2
no service password-encryption
no service udp-small-servers
no service tcp-small-servers
!
hostname thing_one
!
aaa new-model
aaa authentication ppp default tacacs+ none
aaa authorization network tacacs+ none
enable password ww
!
!--- Enable VPDN.
vpdn enable
!--- Specify the remote host ("isp" on the network access server) !--- and the local name ("hp-gw" on the home gateway) to use to authenticate. !--- Also specify the virtual template to use. !--- The local name and the remote host name must match !--- the ones in the TACACS server.
vpdn incoming isp hp-gw virtual-template 1
!
interface Loopback0
shutdown
!
interface Ethernet0
ip address 10.31.1.50 255.255.255.0
!
interface Virtual-Template1
!--- Create a virtual template interface.
ip unnumbered Ethernet0
!--- Un-number the Virtual interface to an available LAN interface.
peer default ip address pool async
!--- Use the pool "async" to assign the IP address for incoming connections.
ppp authentication chap
!--- Use CHAP authentication for the incoming connection.
!
interface Serial0
shutdown
!
interface Serial1
shutdown
!
ip local pool async 15.15.15.15
no ip classless
ip route 0.0.0.0 0.0.0.0 10.31.1.1
!
tacacs-server host 171.68.118.101
no tacacs-server directed-request
tacacs-server key cisco
!--- Specify the TACACS+ server information on the NAS.
!
line con 0
exec-timeout 0 0
line 1 8
line aux 0
line vty 0 4
!
end |
Verifiëren
Er is momenteel geen verificatieprocedure beschikbaar voor deze configuratie.
Problemen oplossen
Deze sectie bevat informatie waarmee u problemen met de configuratie kunt oplossen.
Opdrachten voor troubleshooting
Opmerking: Voordat u debug-opdrachten uitgeeft, raadpleegt u Belangrijke informatie over debug-opdrachten.
-
debug aaa verificatie—Hier wordt informatie weergegeven over verificatie, autorisatie en accounting (AAA)/TACACS+ verificatie.
-
debug aaa-autorisatie—Hier wordt informatie weergegeven over AAA/TACACS+ autorisatie.
-
debug ppp-onderhandeling—Hier worden PPP-pakketten weergegeven die tijdens het opstarten van PPP worden verzonden, waar PPP-opties worden onderhandeld.
-
debug tacacs+—Hier wordt gedetailleerde debuginformatie weergegeven die aan TACACS+ is gekoppeld.
-
debug vpdn fouten-Toont fouten die verhinderen dat een PPP-tunnel wordt gemaakt of fouten die ervoor zorgen dat een ingestelde tunnel wordt gesloten.
-
debug vpdn gebeurtenissen—Hier worden berichten weergegeven over gebeurtenissen die deel uitmaken van de normale PPP-tunnelinstelling of -sluiting.
-
debug vpdn l2f-fouten—Hier wordt Layer 2-protocolfouten weergegeven die Layer 2-vestiging voorkomen of de normale werking ervan verhinderen.
-
debug vpdn l2f-gebeurtenissen—Hier worden berichten weergegeven over gebeurtenissen die deel uitmaken van de normale PPP-tunnelinstelling of afsluiten voor Layer 2.
-
debug vpdn l2f-pakketten—Hier worden berichten weergegeven over Layer 2 Forwarding-protocolkopregels en -status.
-
debug vpDN-pakketten—Hier worden Layer 2 Tunnel Protocol (L2TP)-fouten en -gebeurtenissen weergegeven die deel uitmaken van de normale tunnelinstelling of -sluiting voor VPDN’s.
-
debug vtemplate—Hier wordt informatie over klonen voor een virtuele toegangsinterface weergegeven vanaf het moment dat de interface wordt gekloond van een virtuele sjabloon tot het moment waarop de virtuele toegangsinterface neerkomt wanneer de oproep eindigt.
Voorbeeld van output van foutopsporing
Deze debugs zijn bedoeld als referentie.
Goede debug van IPS-router
koala#show debug General OS: AAA Authentication debugging is on AAA Authorization debugging is on AAA Accounting debugging is on VPN: VPN events debugging is on VPN errors debugging is on koala# %LINK-3-UPDOWN: Interface Async1, changed state to up 15:04:47: VPDN: Looking for tunnel -- hp.com -- 15:04:47: AAA/AUTHEN: create_user (0x15FA80) user='hp.com' ruser='' port='Async1' rem_addr='' authen_type=NONE service=LOGIN priv=0 15:04:47: AAA/AUTHOR/VPDN: : (2445181346): user='hp.com' 15:04:47: AAA/AUTHOR/VPDN: : (2445181346): send AV service=ppp 15:04:47: AAA/AUTHOR/VPDN: : (2445181346): send AV protocol=vpdn 15:04:47: AAA/AUTHOR/VPDN: : (2445181346): Method=TACACS+ 15:04:47: AAA/AUTHOR/TAC+: (2445181346): user=hp.com 15:04:47: AAA/AUTHOR/TAC+: (2445181346): send AV service=ppp 15:04:47: AAA/AUTHOR/TAC+: (2445181346): send AV protocol=vpdn 15:04:47: TAC+: (2445181346): received author response status = PASS_ADD 15:04:47: AAA/AUTHOR (2445181346): Post authorization status = PASS_ADD 15:04:47: AAA/AUTHOR/VPDN: Processing AV service=ppp 15:04:47: AAA/AUTHOR/VPDN: Processing AV protocol=vpdn 15:04:47: AAA/AUTHOR/VPDN: Processing AV tunnel-id=isp 15:04:47: AAA/AUTHOR/VPDN: Processing AV ip-addresses=10.31.1.50 15:04:47: AAA/AUTHOR/VPDN: Processing AV nas-password=hello 15:04:47: AAA/AUTHOR/VPDN: Processing AV gw-password=there 15:04:47: VPDN: Get tunnel info with NAS isp GW hp.com, IP 10.31.1.50 !--- The TACACS+ server returns the attributes the !--- NAS should use for the tunnel. !--- The tunnel-id is "ISP" and the IP address of HGW is 10.31.1.50. 15:04:47: AAA/AUTHEN: free_user (0x15FA80) user='hp.com' ruser='' port='Async1' rem_addr='' authen_type=NONE service=LOGIN priv=0 15:04:47: VPDN: Forward to address 10.31.1.50 15:04:47: As1 VPDN: Forwarding... 15:04:47: AAA/AUTHEN: create_user (0x118008) user='jsmith@hp.com' ruser='' port='Async1' rem_addr='async' authen_type=CHAP service=PPP priv=1 15:04:47: As1 VPDN: Bind interface direction=1 15:04:47: As1 VPDN: jsmith@hp.com is forwarded %LINEPROTO-5-UPDOWN: Line protocol on Interface Async1, changed state to up 15:04:49: AAA/ACCT: NET acct start. User jsmith@hp.com, Port Async1: Async1 !--- User finishes and disconnects. %LINEPROTO-5-UPDOWN: Line protocol on Interface Async1, changed state to down %LINK-5-CHANGED: Interface Async1, changed state to reset 15:05:27: As1 VPDN: Cleanup 15:05:27: As1 VPDN: Reset 15:05:27: As1 VPDN: Reset 15:05:27: As1 VPDN: Unbind interface 15:05:27: AAA/ACCT: Network acct stop. User jsmith@hp.com, Port Async1: task_id=2 timezone=UTC service=vpdn bytes_in=1399 bytes_out=150 paks_in=27 paks_out=9 elapsed_time=38 %LINK-3-UPDOWN: Interface Async1, changed state to down 15:05:30: AAA/AUTHEN: free_user (0x118008) user='jsmith@hp.com' ruser='' port='Async1' rem_addr='async' authen_type=CHAP service=PPP priv=1 koala#
Goede debug van HGW router
thing_one#show debug
General OS:
AAA Authentication debugging is on
AAA Authorization debugging is on
AAA Accounting debugging is on
VPN:
VPN events debugging is on
VPN errors debugging is on
VTEMPLATE:
Virtual Template debugging is on
thing_one#
15:04:46: AAA/AUTHEN: create_user (0x15E6E0) user='isp' ruser='' port=''
rem_addr='' authen_type=CHAP service=PPP priv=1
15:04:46: TAC+: ver=192 id=969200103 received AUTHEN status = PASS
15:04:46: AAA/AUTHEN: free_user (0x15E6E0) user='isp' ruser='' port=''
rem_addr='' authen_type=CHAP service=PPP priv=1
15:04:46: AAA/AUTHEN (3252085483): status = PASS
15:04:46: AAA/AUTHEN: free_user (0x15CBEC) user='isp' ruser='' port=''
rem_addr='' authen_type=CHAP service=PPP priv=1
15:04:46: AAA/AUTHEN: create_user (0x15F1B8) user='isp' ruser='' port=''
rem_addr='' authen_type=CHAP service=PPP priv=1
15:04:46: AAA/AUTHEN/START (3897539709): port='' list='default'
action=LOGIN service=PPP
15:04:46: AAA/AUTHEN/START (3897539709): found list default
15:04:46: AAA/AUTHEN/START (3897539709): Method=TACACS+
15:04:46: TAC+: send AUTHEN/START packet ver=193 id=3897539709
15:04:46: TAC+: ver=192 id=3897539709 received AUTHEN status = GETPASS
15:04:46: AAA/AUTHEN: create_user (0x15E6F0) user='isp' ruser='' port=''
rem_addr='' authen_type=CHAP service=PPP priv=1
15:04:46: TAC+: ver=192 id=2306139011 received AUTHEN status = PASS
15:04:46: AAA/AUTHEN: free_user (0x15E6F0) user='isp' ruser='' port=''
rem_addr='' authen_type=CHAP service=PPP priv=1
15:04:46: AAA/AUTHEN (3897539709): status = PASS
15:04:46: VPDN: Chap authentication succeeded for isp
!--- The LAC ("ISP") is succesfully authenticated.
15:04:46: AAA/AUTHEN: free_user (0x15F1B8) user='isp' ruser='' port=''
rem_addr='' authen_type=CHAP service=PPP priv=1
15:04:46: Vi1 VTEMPLATE: Reuse Vi1, recycle queue size 0
15:04:46: Vi1 VTEMPLATE: Set default settings with no ip address
15:04:47: Vi1 VTEMPLATE: Hardware address 00e0.1e68.942c
15:04:47: Vi1 VPDN: Virtual interface created for jsmith@hp.com
15:04:47: Vi1 VPDN: Set to Async interface
15:04:47: Vi1 VPDN: Clone from Vtemplate 1 filterPPP=0 blocking
15:04:47: Vi1 VTEMPLATE: Has a new cloneblk vtemplate, now it has vtemplate
15:04:47: Vi1 VTEMPLATE: Undo default settings
15:04:47: Vi1 VTEMPLATE: ************* CLONE VACCESS1 *****************
15:04:47: Vi1 VTEMPLATE: Clone from vtemplate1
interface Virtual-Access1
no ip address
encap ppp
ip unnum eth 0
peer default ip address pool async
ppp authen chap
end
%LINK-3-UPDOWN: Interface Virtual-Access1, changed state to up
15:04:48: Vi1 VPDN: Bind interface direction=2
15:04:48: Vi1 VPDN: PPP LCP accepted sent & rcv CONFACK
15:04:48: Vi1 VPDN: Virtual interface iteration
15:04:48: AAA/AUTHEN: create_user (0x161688) user='jsmith@hp.com' ruser=''
port='Virtual-Access1' rem_addr='async' authen_type=CHAP service=PPP priv=1
15:04:48: AAA/AUTHEN/START (580760432): port='Virtual-Access1' list=''
action=LOGIN service=PPP
15:04:48: AAA/AUTHEN/START (580760432): using "default" list
15:04:48: AAA/AUTHEN/START (580760432): Method=TACACS+
15:04:48: TAC+: send AUTHEN/START packet ver=193 id=580760432
15:04:48: Vi1 VPDN: Virtual interface iteration
15:04:49: TAC+: ver=192 id=580760432 received AUTHEN status = GETPASS
!--- Authenticate user jsmith@hp.com with the TACACS+ server.
15:04:49: AAA/AUTHEN: create_user (0x1667C0) user='jsmith@hp.com' ruser=''
port='Virtual-Access1' rem_addr='async' authen_type=CHAP service=PPP priv=1
15:04:49: TAC+: ver=192 id=2894253624 received AUTHEN status = PASS
15:04:49: AAA/AUTHEN: free_user (0x1667C0) user='jsmith@hp.com' ruser=''
port='Virtual-Access1' rem_addr='async' authen_type=CHAP service=PPP priv=1
15:04:49: AAA/AUTHEN (580760432): status = PASS
15:04:49: AAA/AUTHOR/LCP Vi1: Authorize LCP
15:04:49: AAA/AUTHOR/LCP: Virtual-Access1: (687698354): user='jsmith@hp.com'
15:04:49: AAA/AUTHOR/LCP: Virtual-Access1: (687698354): send AV service=ppp
15:04:49: AAA/AUTHOR/LCP: Virtual-Access1: (687698354): send AV protocol=lcp
15:04:49: AAA/AUTHOR/LCP: Virtual-Access1: (687698354): Method=TACACS+
15:04:49: AAA/AUTHOR/TAC+: (687698354): user=jsmith@hp.com
15:04:49: AAA/AUTHOR/TAC+: (687698354): send AV service=ppp
15:04:49: AAA/AUTHOR/TAC+: (687698354): send AV protocol=lcp
15:04:49: TAC+: (687698354): received author response status = PASS_ADD
15:04:49: AAA/AUTHOR (687698354): Post authorization status = PASS_ADD
15:04:49: AAA/ACCT: NET acct start. User jsmith@hp.com, Port Virtual-Access1:
Virtual-Access1
15:04:49: AAA/AUTHOR/FSM Vi1: (0): Can we start IPCP?
15:04:49: AAA/AUTHOR/FSM: Virtual-Access1: (3562892028): user='jsmith@hp.com'
15:04:49: AAA/AUTHOR/FSM: Virtual-Access1: (3562892028): send AV service=ppp
15:04:49: AAA/AUTHOR/FSM: Virtual-Access1: (3562892028): send AV protocol=ip
15:04:49: AAA/AUTHOR/FSM: Virtual-Access1: (3562892028): Method=TACACS+
15:04:49: AAA/AUTHOR/TAC+: (3562892028): user=jsmith@hp.com
15:04:49: AAA/AUTHOR/TAC+: (3562892028): send AV service=ppp
15:04:49: AAA/AUTHOR/TAC+: (3562892028): send AV protocol=ip
%LINEPROTO-5-UPDOWN: Line protocol on Interface Virtual-Access1,
changed state to up
15:04:49: TAC+: (3562892028): received author response status = PASS_ADD
15:04:49: AAA/AUTHOR (3562892028): Post authorization status = PASS_ADD
!--- IPCP negotiation begins.
15:04:49: AAA/AUTHOR/FSM Vi1: We can start IPCP
15:04:50: AAA/AUTHOR/IPCP Vi1: Start. Her address 0.0.0.0, we want 0.0.0.0
15:04:50: AAA/AUTHOR/IPCP Vi1: Processing AV service=ppp
15:04:50: AAA/AUTHOR/IPCP Vi1: Processing AV protocol=ip
15:04:50: AAA/AUTHOR/IPCP Vi1: Authorization succeeded
15:04:50: AAA/AUTHOR/IPCP Vi1: Done. Her address 0.0.0.0, we want 0.0.0.0
15:04:51: AAA/AUTHOR/IPCP Vi1: Start. Her address 0.0.0.0,
we want 15.15.15.15
15:04:51: AAA/AUTHOR/IPCP Vi1: Processing AV service=ppp
15:04:51: AAA/AUTHOR/IPCP Vi1: Processing AV protocol=ip
15:04:51: AAA/AUTHOR/IPCP Vi1: Authorization succeeded
15:04:51: AAA/AUTHOR/IPCP Vi1: Done. Her address 0.0.0.0,
we want 15.15.15.15
15:04:51: AAA/AUTHOR/IPCP Vi1: Start. Her address 15.15.15.15,
we want 15.15.15.15
15:04:51: AAA/AUTHOR/IPCP: Virtual-Access1: (3193852847):
user='jsmith@hp.com'
15:04:51: AAA/AUTHOR/IPCP: Virtual-Access1: (3193852847):
send AV service=ppp
15:04:51: AAA/AUTHOR/IPCP: Virtual-Access1: (3193852847):
send AV protocol=ip
15:04:51: AAA/AUTHOR/IPCP: Virtual-Access1: (3193852847):
send AV addr*15.15.15.15
15:04:51: AAA/AUTHOR/IPCP: Virtual-Access1: (3193852847):
Method=TACACS+
15:04:51: AAA/AUTHOR/TAC+: (3193852847): user=jsmith@hp.com
15:04:51: AAA/AUTHOR/TAC+: (3193852847): send AV service=ppp
15:04:51: AAA/AUTHOR/TAC+: (3193852847): send AV protocol=ip
15:04:51: AAA/AUTHOR/TAC+: (3193852847): send AV addr*15.15.15.15
15:04:51: TAC+: (3193852847): received author response status = PASS_ADD
15:04:51: AAA/AUTHOR (3193852847): Post authorization status = PASS_ADD
15:04:51: AAA/AUTHOR/IPCP Vi1: Processing AV service=ppp
15:04:51: AAA/AUTHOR/IPCP Vi1: Processing AV protocol=ip
15:04:51: AAA/AUTHOR/IPCP Vi1: Processing AV addr*15.15.15.15
15:04:51: AAA/AUTHOR/IPCP Vi1: Authorization succeeded
15:04:51: AAA/AUTHOR/IPCP Vi1: Done. Her address 15.15.15.15,
we want 15.15.15.15
!--- User finishes and disconnects.
15:05:24: Vi1 VPDN: Reset
15:05:24: Vi1 VPDN: Reset
%LINK-3-UPDOWN: Interface Virtual-Access1, changed state to down
15:05:24: Vi1 VPDN: Cleanup
15:05:24: Vi1 VPDN: Reset
15:05:24: Vi1 VPDN: Reset
15:05:24: Vi1 VPDN: Unbind interface
15:05:24: Vi1 VTEMPLATE: Free vaccess
15:05:24: Vi1 VPDN: Reset
15:05:24: Vi1 VPDN: Reset
15:05:24: AAA/ACCT: Network acct stop. User jsmith@hp.com,
Port Virtual-Access1:
task_id=2 timezone=UTC service=ppp protocol=ip addr=15.15.15.15
bytes_in=564
bytes_out=142 paks_in=15 paks_out=8 elapsed_time=35
15:05:24: AAA/AUTHEN: free_user (0x161688) user='jsmith@hp.com' ruser=''
port='Virtual-Access1' rem_addr='async'
authen_type=CHAP service=PPP priv=1
%LINEPROTO-5-UPDOWN: Line protocol on Interface Virtual-Access1,
changed state to down
15:05:25: VTEMPLATE: Clean up dirty vaccess queue, size 1
15:05:25: Vi1 VTEMPLATE: Found a dirty vaccess clone with vtemplate
15:05:25: Vi1 VTEMPLATE: ************ UNCLONE VACCESS1 **************
15:05:25: Vi1 VTEMPLATE: Unclone to-be-freed command#5
interface Virtual-Access1
default ppp authen chap
default peer default ip address pool async
default ip unnum eth 0
default encap ppp
default ip address
end
15:05:26: Vi1 VTEMPLATE: Set default settings with no ip address
15:05:26: Vi1 VTEMPLATE: Remove cloneblk vtemplate with vtemplate
15:05:26: Vi1 VTEMPLATE: Add vaccess to recycle queue, queue size=1
thing_one#
Debugs voor mislukte verbinding op ISP router
koala#show debug General OS: AAA Authentication debugging is on AAA Authorization debugging is on AAA Accounting debugging is on VPN: VPN events debugging is on VPN errors debugging is on koala# !--- Problem 1: !--- The ISP TACACS+ server is down. !--- There is no output on the HGW router !--- because the call has not gone that far. AAA/AUTHOR (3015476150): Post authorization status = ERROR AAA/AUTHOR/VPDN: : (3015476150): Method=NOT_SET AAA/AUTHOR/VPDN: : (3015476150): no methods left to try AAA/AUTHOR (3015476150): Post authorization status = ERROR VPDN: (hp.com) Authorization failed, could not talk to AAA server or local tunnel problem !--- Problem 2: !--- Userid hp.com is not in the ISP server. !--- There is no output on the Gateway router !--- because the call has not gone that far. TAC+: (894828802): received author response status = PASS_ADD AAA/AUTHOR (894828802): Post authorization status = PASS_ADD VPDN: (hp.com) Authorization failed, had talked to AAA server; but both Tunnel ID and IP address are missing AAA/AUTHEN: free_user (0x16A6E4) user='hp.com' ruser='' port='Async1' rem_addr='' authen_type=NONE service=LOGIN priv=0 AAA/AUTHEN: create_user (0x16CA8C) user='jsmith@hp.com' ruser='' port='Async1' rem_addr='async' authen_type=CHAP service=PPP priv=1 AAA/AUTHEN/START (1904487288): port='Async1' list='' action=LOGIN service=PPP AAA/AUTHEN/START (1904487288): using "default" list AAA/AUTHEN (1904487288): status = UNKNOWN AAA/AUTHEN/START (1904487288): Method=TACACS+ TAC+: send AUTHEN/START packet ver=193 id=1904487288 TAC+: ver=193 id=1904487288 received AUTHEN status = FAIL AAA/AUTHEN (1904487288): status = FAIL
Debugs voor mislukte verbindingen op HGW router
thing_one#show debug General OS: AAA Authentication debugging is on AAA Authorization debugging is on AAA Accounting debugging is on VPN: VPN events debugging is on VPN errors debugging is on VTEMPLATE: Virtual Template debugging is on thing_one# !--- Problem 1: !--- The problem is in the tunnel definition on HGW router. !--- In the HGW configuration, vpdn incoming hp-gw isp virtual-template 1 !--- is inserted instead of vpdn incoming isp hp-gw virtual-template 1 !--- The debug vpdn l2f-errors command displays. L2F: Couldn't find tunnel named isp L2F: Couldn't find tunnel named isp !--- Problem 2: !--- This message appears when User hp-gw is not in the HGW server. TAC+: ver=192 id=1920941753 received AUTHEN status = FAIL AAA/AUTHEN: free_user (0x138C34) user='hp-gw' ruser='' port='' rem_addr='' authen_type=CHAP service=PPP priv=1 AAA/AUTHEN (3006335673): status = FAIL VPDN: authentication failed, couldn't find user information for hp-gw !--- Problem 3: !--- This appears when user isp is not in the HGW server. TAC+: ver=192 id=1917558147 received AUTHEN status = FAIL AAA/AUTHEN: free_user (0x15F20C) user='isp' ruser='' port='' rem_addr='' authen_type=CHAP service=PPP priv=1 AAA/AUTHEN (1949507921): status = FAIL VPDN: authentication failed, couldn't find user information for isp !--- Problem 4: !--- This message appears when User jsmith@hp.com is !--- not in the HGW server: TAC+: ver=192 id=755036341 received AUTHEN status = FAIL AAA/AUTHEN: free_user (0x15F89C) user='jsmith@hp.com' ruser='' port='Virtual-Access1' rem_addr='async' authen_type=CHAP service=PPP priv=1 AAA/AUTHEN (2606986667): status = FAIL
Gerelateerde informatie
Revisiegeschiedenis
| Revisie | Publicatiedatum | Opmerkingen |
|---|---|---|
1.0 |
06-Dec-2001 |
Eerste vrijgave |
Contact Cisco
- Een ondersteuningscase openen

- (Vereist een Cisco-servicecontract)
 Feedback
Feedback