Verifieer Intelligent Traffic Director met behulp van IP-bronmethode
Inclusief taalgebruik
De documentatie van dit product is waar mogelijk geschreven met inclusief taalgebruik. Inclusief taalgebruik wordt in deze documentatie gedefinieerd als taal die geen discriminatie op basis van leeftijd, handicap, gender, etniciteit, seksuele oriëntatie, sociaaleconomische status of combinaties hiervan weerspiegelt. In deze documentatie kunnen uitzonderingen voorkomen vanwege bewoordingen die in de gebruikersinterfaces van de productsoftware zijn gecodeerd, die op het taalgebruik in de RFP-documentatie zijn gebaseerd of die worden gebruikt in een product van een externe partij waarnaar wordt verwezen. Lees meer over hoe Cisco gebruikmaakt van inclusief taalgebruik.
Over deze vertaling
Cisco heeft dit document vertaald via een combinatie van machine- en menselijke technologie om onze gebruikers wereldwijd ondersteuningscontent te bieden in hun eigen taal. Houd er rekening mee dat zelfs de beste machinevertaling niet net zo nauwkeurig is als die van een professionele vertaler. Cisco Systems, Inc. is niet aansprakelijk voor de nauwkeurigheid van deze vertalingen en raadt aan altijd het oorspronkelijke Engelstalige document (link) te raadplegen.
Inleiding
Dit document beschrijft de manier om zowel het besturingsplane als het dataplane van de Intelligent Traffic Director (ITD) op het Nexus 9K-platform te controleren.
Voorwaarden
Vereisten
Cisco raadt kennis van de volgende onderwerpen aan:
- Nexus NX-OS-software.
- Toegangslijst (ACL).
- IP-serviceovereenkomst (IP SLA).
- Op beleid gebaseerde routing (PBR).
- Intelligent Traffic Director (ITD).
Gebruikte componenten
De informatie in dit document is gebaseerd op Cisco Nexus 9000 met NXOS versie 10.2(5).
De informatie in dit document is gebaseerd op de apparaten in een specifieke laboratoriumomgeving. Alle apparaten die in dit document worden beschreven, hadden een opgeschoonde (standaard)configuratie. Als uw netwerk live is, moet u zorgen dat u de potentiële impact van elke opdracht begrijpt.
Configureren
ITD is een intelligente, op hardware gebaseerde multi-terabit oplossing waarmee u een schaalbare architectuur kunt bouwen voor Layer 3 en Layer 4 verkeersdistributie, taakverdeling en omleiding.
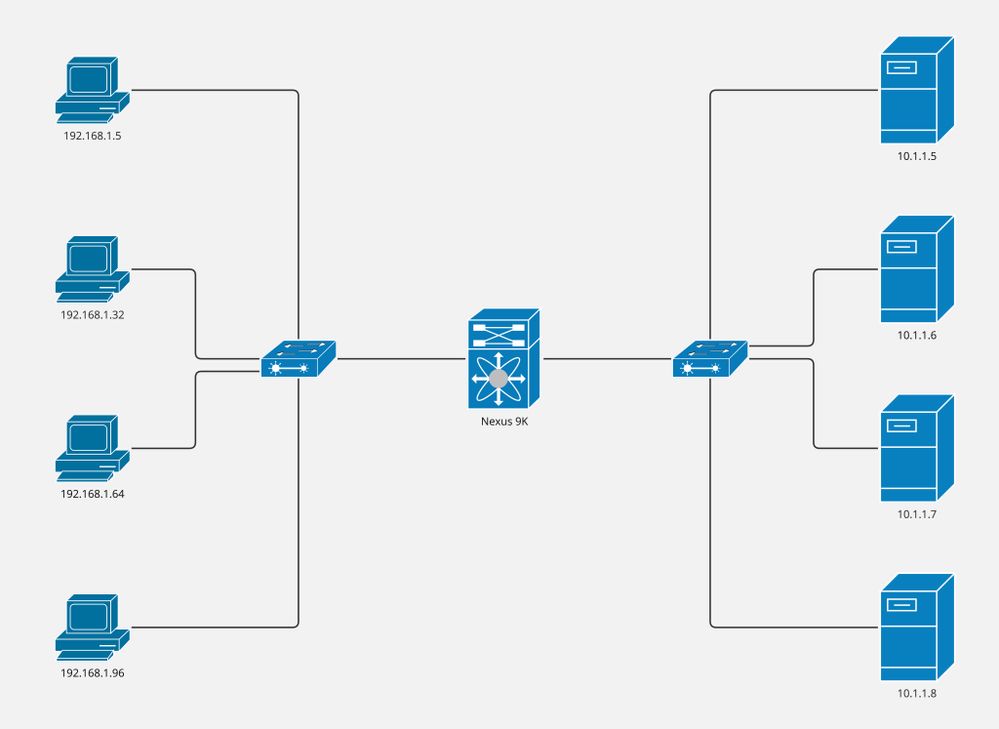
Netwerkdiagram
- Computers: 4
- Servers: 4
- Layer 2 switches: 2
- Nexus 9K switches: 1

Opmerking: Layer 2-switches voegen de verbinding tussen servers/computers en Nexus 9K-switches samen, waar ITD draait.
Configuraties
Deze configuratie is geïmplementeerd op Nexus 9K switch en dekt alleen het ITD-onderdeel. De computers maken deel uit van VLAN 5 en de servers maken deel uit van VLAN 10, terwijl Nexus 9K de gateway van beide VLAN's is.
Stap 1. Schakel de vereiste functies in.
feature itd
feature sla sender
feature sla responder
feature pbrStap 2. Definieer de apparaatgroep, wijs naar de knooppunten en geef de sonde aan.
itd device-group CiscoGroup
probe icmp frequency 5 timeout 5 retry-down-count 2 retry-up-count 2
node ip 10.1.1.5
node ip 10.1.1.6
node ip 10.1.1.7
node ip 10.1.1.8Stap 3. Definieer de service. De gebruikers kunnen op virtuele ip wijzen of een toegangslijst omvatten.

Opmerking: NX-OS verdeelt het laatste octet door het aangegeven aantal emmers. Bij dit voorbeeld delen we 256 door 8. Daarom bevat elke emmer 32 hosts.
Bucket 1: From x.x.x.0 to x.x.x.31
Bucket 2: From x.x.x.32 to x.x.x.63
Bucket 3: From x.x.x.64 to x.x.x.95
Bucket 4: From x.x.x.96 to x.x.x.127
Bucket 5: From x.x.x.128 to x.x.x.159
Bucket 6: From x.x.x.160 to x.x.x.191
Bucket 7: From x.x.x.192 to x.x.x.223
Bucket 8: From x.x.x.224 to x.x.x.255itd CiscoService
device-group CiscoGroup
virtual ip 192.168.255.1 255.255.255.255 advertise enable
ingress interface Vlan5
failaction node reassign
load-balance method src ip buckets 8
no shutStap 4. Statistieken voor gedefinieerde service inschakelen.
itd statistics CiscoServiceVerifiëren
1. Bevestig dat de ITD-service actief is en dat de status van de knooppunt ok is.
Nexus# show itd CiscoService brief
Legend:
C-S(Config-State): A-Active,S-Standby,F-Failed
ST(Status): ST-Standby,LF-Link Failed,PF-Probe Failed,PD-Peer Down,IA-Inactive,SH-Shut,HD-Hold-down
Name LB Scheme Status Buckets Interface
-------------- ---------- -------- --------- --------------
CiscoService src-ip ACTIVE 8 Vlan5
Source Interface
----------------
Device Group Probe Port VRF
-------------------------------------------------- ----- ------ ---------
CiscoGroup ICMP
Virtual IP Netmask/Prefix Protocol Port
------------------------------------------------------ ------------ ----------
192.168.255.1 / 255.255.255.255 IP 0
Node IP Cluster-id C-S WGT Probe Port Probe-IP STS
------------------------- ---------- -- --- ---- ----- --------------- --
1 10.1.1.5 A 1 ICMP OK
2 10.1.1.6 A 1 ICMP OK
3 10.1.1.7 A 1 ICMP OK
4 10.1.1.8 A 1 ICMP OK2. Controleer of er een routebeleid is gemaakt en gekoppeld aan de toegangsinterface.

Opmerking: Het routebeleid wordt toegepast in de lopende configuratie (onder ingangsinterface) tot NXOS 10.1(2), het starten van NXOS 10.2(1) u kunt routebeleid geassocieerd in het systeem vinden met de opdracht ip-beleid tonen.
Nexus# show ip policy
Interface Route-map Status VRF-Name
Vlan5 CiscoService_itd_pool Active default
3. Bevestig dat de routekaart op de juiste manier is gegenereerd, gekoppeld aan de verwachte knooppunten en dat deze de tracering (IP SLA) aangeeft.

Opmerking: Verwacht wordt dat er één routekaartingang per emmer is.
Verwacht wordt dat er één spoor per knooppunt is.
Nexus# show route-map dynamic CiscoService_itd_pool
route-map CiscoService_itd_pool, permit, sequence 10
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_1
Set clauses:
ip next-hop verify-availability 10.1.1.5 track 2 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 11
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_2
Set clauses:
ip next-hop verify-availability 10.1.1.6 track 3 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 12
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_3
Set clauses:
ip next-hop verify-availability 10.1.1.7 track 4 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 13
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_4
Set clauses:
ip next-hop verify-availability 10.1.1.8 track 5 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 14
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_5
Set clauses:
ip next-hop verify-availability 10.1.1.5 track 2 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 15
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_6
Set clauses:
ip next-hop verify-availability 10.1.1.6 track 3 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 16
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_7
Set clauses:
ip next-hop verify-availability 10.1.1.7 track 4 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 17
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_8
Set clauses:
ip next-hop verify-availability 10.1.1.8 track 5 [ UP ] force-order 4. Bevestig dat de toegangslijst correct is gegenereerd en de verwachte ip-matchvoorwaarde heeft.

Opmerking: ACL’s worden gegenereerd in lopende configuratie tot NXOS 9.3(2), met NXOS 9.3(3) kunnen we ACL’s in systeem vinden met behulp van dynamisch commando tonen van IP-toegangslijst.
Nexus# show ip access-lists CiscoService_itd_vip_1_bucket_1 dynamic
IP access list CiscoService_itd_vip_1_bucket_1
10 permit ip 1.1.1.0 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_2 dynamic
IP access list CiscoService_itd_vip_1_bucket_2
10 permit ip 1.1.1.32 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_3 dynamic
IP access list CiscoService_itd_vip_1_bucket_3
10 permit ip 1.1.1.64 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_4 dynamic
IP access list CiscoService_itd_vip_1_bucket_4
10 permit ip 1.1.1.96 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_5 dynamic
IP access list CiscoService_itd_vip_1_bucket_5
10 permit ip 1.1.1.128 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_6 dynamic
IP access list CiscoService_itd_vip_1_bucket_6
10 permit ip 1.1.1.160 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_7 dynamic
IP access list CiscoService_itd_vip_1_bucket_7
10 permit ip 1.1.1.192 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_8 dynamic
IP access list CiscoService_itd_vip_1_bucket_8
10 permit ip 1.1.1.224 255.255.255.31 192.168.255.1/32 5. Zorg ervoor dat toegangslijsten zijn geprogrammeerd in TCAM.
Nexus# show system internal access-list input entries detail | begin "VLAN 5"
VLAN 5 :
=========
INSTANCE 0x0
---------------
Tcam 1 resource usage:
----------------------
LBL B = 0x1
Bank 1
------
IPv4 Class
Policies: PBR(CiscoService_itd_vip_1_bucket_8)
Netflow profile: 0
Netflow deny profile: 0
Entries:
[Index] Entry [Stats]
---------------------
[0x0000:0x0002:0x0002] permit ip 0.0.0.0/0 224.0.0.0/4 routeable 0x1 [0]
[0x0002:0x0004:0x0004] permit ip 0.0.0.0/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x0003:0x0005:0x0005] permit ip 0.0.0.32/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x0004:0x0006:0x0006] permit ip 0.0.0.64/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x0005:0x0007:0x0007] permit ip 0.0.0.96/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000b:0x000d:0x000d] permit ip 0.0.0.128/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000c:0x000e:0x000e] permit ip 0.0.0.160/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000d:0x000f:0x000f] permit ip 0.0.0.192/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000e:0x0010:0x0010] permit ip 0.0.0.224/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000f:0x0011:0x0011] permit ip 0.0.0.0/0 0.0.0.0/0 routeable 0x1 [0]
L4 protocol cam entries usage: none
No mac protocol cam entries are in use
INSTANCE 0x1
---------------
Tcam 1 resource usage:
----------------------
LBL B = 0x1
Bank 1
------
IPv4 Class
Policies: PBR(CiscoService_itd_vip_1_bucket_8)
Netflow profile: 0
Netflow deny profile: 0
Entries:
[Index] Entry [Stats]
---------------------
[0x0000:0x0002:0x0002] permit ip 0.0.0.0/0 224.0.0.0/4 routeable 0x1 [0]
[0x0002:0x0004:0x0004] permit ip 0.0.0.0/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x0003:0x0005:0x0005] permit ip 0.0.0.32/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x0004:0x0006:0x0006] permit ip 0.0.0.64/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x0005:0x0007:0x0007] permit ip 0.0.0.96/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000b:0x000d:0x000d] permit ip 0.0.0.128/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000c:0x000e:0x000e] permit ip 0.0.0.160/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000d:0x000f:0x000f] permit ip 0.0.0.192/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000e:0x0010:0x0010] permit ip 0.0.0.224/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000f:0x0011:0x0011] permit ip 0.0.0.0/0 0.0.0.0/0 routeable 0x1 [0]
L4 protocol cam entries usage: none
No mac protocol cam entries are in use6. Verzend verkeer naar het virtuele IP-adres en bevestig de toename van tellers (aantal pakketten) voor het verwachte knooppunt.
Nexus# show itd CiscoService statistics
Service Device Group VIP/mask #Packets
-------------------------------------------------------------------------------------------------------------------------------------------
CiscoService CiscoGroup 192.168.255.1 / 255.255.255.255 0 (0%)
Traffic Bucket Assigned to Mode Original Node #Packets
--------------- -------------- ----- -------------- ---------
CiscoService_itd_vip_1_bucket_1 10.1.1.5 Redirect 10.1.1.5 0 (0%)
CiscoService_itd_vip_1_bucket_5 10.1.1.5 Redirect 10.1.1.5 0 (0%)
Traffic Bucket Assigned to Mode Original Node #Packets
--------------- -------------- ----- -------------- ---------
CiscoService_itd_vip_1_bucket_2 10.1.1.6 Redirect 10.1.1.6 0 (0%)
CiscoService_itd_vip_1_bucket_6 10.1.1.6 Redirect 10.1.1.6 0 (0%)
Traffic Bucket Assigned to Mode Original Node #Packets
--------------- -------------- ----- -------------- ---------
CiscoService_itd_vip_1_bucket_3 10.1.1.7 Redirect 10.1.1.7 0 (0%)
CiscoService_itd_vip_1_bucket_7 10.1.1.7 Redirect 10.1.1.7 0 (0%)
Traffic Bucket Assigned to Mode Original Node #Packets
--------------- -------------- ----- -------------- ---------
CiscoService_itd_vip_1_bucket_4 10.1.1.8 Redirect 10.1.1.8 0 (0%)
CiscoService_itd_vip_1_bucket_8 10.1.1.8 Redirect 10.1.1.8 0 (0%)Revisiegeschiedenis
| Revisie | Publicatiedatum | Opmerkingen |
|---|---|---|
1.0 |
21-Jul-2023 |
Eerste vrijgave |
Bijgedragen door Cisco-engineers
- Bidkar Herson Paez LamponTechnisch adviseur-engineer
Contact Cisco
- Een ondersteuningscase openen

- (Vereist een Cisco-servicecontract)
 Feedback
Feedback