SDWAN Configuração de Syslog TLS Cisco IOS XE no Servidor syslog-ng
Opções de download
Linguagem imparcial
O conjunto de documentação deste produto faz o possível para usar uma linguagem imparcial. Para os fins deste conjunto de documentação, a imparcialidade é definida como uma linguagem que não implica em discriminação baseada em idade, deficiência, gênero, identidade racial, identidade étnica, orientação sexual, status socioeconômico e interseccionalidade. Pode haver exceções na documentação devido à linguagem codificada nas interfaces de usuário do software do produto, linguagem usada com base na documentação de RFP ou linguagem usada por um produto de terceiros referenciado. Saiba mais sobre como a Cisco está usando a linguagem inclusiva.
Sobre esta tradução
A Cisco traduziu este documento com a ajuda de tecnologias de tradução automática e humana para oferecer conteúdo de suporte aos seus usuários no seu próprio idioma, independentemente da localização. Observe que mesmo a melhor tradução automática não será tão precisa quanto as realizadas por um tradutor profissional. A Cisco Systems, Inc. não se responsabiliza pela precisão destas traduções e recomenda que o documento original em inglês (link fornecido) seja sempre consultado.
Contents
Introdução
Este documento descreve um guia abrangente para configurar um servidor Syslog TLS em dispositivos Cisco IOS® XE SD-WAN.
Pré-requisitos
Antes de prosseguir com a configuração de um servidor TLS Syslog em dispositivos SD-WAN Cisco IOS XE, certifique-se de atender aos requisitos:
Requisitos
A Cisco recomenda que você tenha conhecimento destes tópicos:
-
Controladores SD-WAN - Certifique-se de que sua rede inclua controladores SD-WAN configurados corretamente.
-
Roteador SD-WAN Cisco IOS XE - Um roteador compatível que executa a imagem SD-WAN do Cisco IOS XE.
-
Servidor Syslog - Um servidor Syslog baseado em Ubuntu, como syslog-ng, para coletar e gerenciar dados de log.
Componentes Utilizados
As informações neste documento são baseadas nestas versões de software e hardware:
-
vManage: Versão 20.9.4
-
SD-WAN do Cisco IOS XE: Versão 17.9.4
-
Ubuntu Versão 22.04
-
syslog-ng: Versão 3.27
As informações neste documento foram criadas a partir de dispositivos em um ambiente de laboratório específico. Todos os dispositivos utilizados neste documento foram iniciados com uma configuração (padrão) inicial. Se a rede estiver ativa, certifique-se de que você entenda o impacto potencial de qualquer comando.
Configuração
1. Instalação do syslog-ng na máquina Ubuntu
Para configurar o syslog-ng no servidor Ubuntu, siga estas etapas para garantir a instalação e a configuração adequadas.
Etapa 1. Configure network settings
Depois de instalar o servidor Ubuntu, configure um endereço IP estático e um servidor DNS para garantir que a máquina possa acessar a Internet. Isso é crucial para o download de pacotes e atualizações.
Etapa 2. Instalar o syslog-ng
Abra um terminal em sua máquina Ubuntu e execute:
sudo apt-get install syslog-ng sudo apt-get install syslog-ng openssl2. Instalar a Autoridade de Certificação Raiz no Servidor Syslog para Autenticação do Servidor
Criar diretórios e gerar chaves
cd /etc/syslog-ng mkdir cert.d key.d ca.d cd cert.d openssl genrsa -out ca.key 2048 openssl req -new -x509 -key ca.key -out PROXY-SIGNING-CA.ca -days 730 # Copy key to the key.d folder cp ca.key ../key.dCalcular impressão digital
Execute o comando e copie a saída:
openssl x509 -in PROXY-SIGNING-CA.ca -fingerprint -noout | awk -F "=" '{print $2}' | sed 's/://g' | tee fingerprint.txt
# Exemplo de saída: 54F371C8EE2BFB06E2C2D0944245C288FBB07163
3. Configurar o Arquivo de Configuração do Servidor syslog-ng
Edite o arquivo de configuração syslog-ng:
sudo nano /etc/syslog-ng/syslog-ng.confAdicione a configuração:
source s_src { network( ip(0.0.0.0) port(6514) transport("tls") tls( key-file("/etc/syslog-ng/key.d/ca.key") cert-file("/etc/syslog-ng/cert.d/PROXY-SIGNING-CA.ca") peer-verify(optional-untrusted) ) ); }; destination remote { file("/var/log/syslog"); }; log { source(s_src); destination(remote); };4. Instalar a Root Certificate Authority no Dispositivo SD-WAN do Cisco IOS XE para Autenticação do Servidor
Configurar a partir do CLI
-
Entre no modo de configuração:
config-t-
Configure o ponto confiável:
crypto pki trustpoint PROXY-SIGNING-CA enrollment url bootflash: revocation-check none rsakeypair PROXY-SIGNING-CA 2048 subject-name cn=proxy-signing-cert fqdn none fingerprint 54F371C8EE2BFB06E2C2D0944245C288FBB07163 >> The fingerprint configured was obtained from the fingerprint.txt file above commit-
Copie o PROXY-SIGNING-CA.ca do servidor syslog para o bootflash do roteador usando o mesmo nome.
-
Autenticar o ponto confiável:
crypto pki authenticate PROXY-SIGNING-CA
example:
Router#crypto pki authenticate PROXY-SIGNING-CA
Reading file from bootflash:PROXY-SIGNING-CA.ca
Certificate has the attributes:
Fingerprint MD5: 7A97B30B 2AE458FF D9E7D91F 66488DCF
Fingerprint SHA1: 21E0F09B B67B2E9D 706DBE69 856E5AA3 D39A268A
Trustpoint Fingerprint: 21E0F09B B67B2E9D 706DBE69 856E5AA3 D39A268A
Certificate validated - fingerprints matched.
Trustpoint CA certificate accepted.-
Registre o ponto confiável:
crypto pki enroll PROXY-SIGNING-CA
example:
vm32#crypto pki enroll PROXY-SIGNING-CA
Start certificate enrollment ..
The subject name in the certificate will include: cn=proxy-signing-cert
The fully-qualified domain name will not be included in the certificate
Certificate request sent to file system
The 'show crypto pki certificate verbose PROXY-SIGNING-CA' commandwill show the fingerprint.
-
Copie o PROXY-SIGNING-CA.req do roteador para o Servidor syslog.
Assine o certificado no Servidor Syslog
openssl x509 -in PROXY-SIGNING-CA.req -req -CA PROXY-SIGNING-CA.ca -CAkey ca.key -out PROXY-SIGNING-CA.crt -CAcreateserial -extensions ca_extensions-
Copiar o arquivo gerado (PROXY-SIGNING-CA.crt) para o bootflash do roteador. copiar scp: flash de inicialização:
-
Importar o certificado:
crypto pki import PROXY-SIGNING-CA certificate
example:
Router# crypto pki import PROXY-SIGNING-CA certificate
% The fully-qualified domain name will not be included in the certificate
% Request to retrieve Certificate queuedValidar a configuração
show crypto pki trustpoint PROXY-SIGNING-CA status
example:
Router#show crypto pki trustpoint PROXY-SIGNING-CA status
Trustpoint PROXY-SIGNING-CA:
Issuing CA certificate configured:
Subject Name:
o=Internet Widgits Pty Ltd,st=Some-State,c=AU
Fingerprint MD5: 7A97B30B 2AE458FF D9E7D91F 66488DCF
Fingerprint SHA1: 21E0F09B B67B2E9D 706DBE69 856E5AA3 D39A268A
Router General Purpose certificate configured:
Subject Name:
cn=proxy-signing-cert
Fingerprint MD5: 140A1EAB FE945D56 D1A53855 FF361F3F
Fingerprint SHA1: ECA67413 9C102869 69F582A4 73E2B98C 80EFD6D5
Last enrollment status: Granted
State:
Keys generated ............. Yes (General Purpose, non-exportable)
Issuing CA authenticated ....... Yes
Certificate request(s) ..... Yes5. Configurar o servidor TLS Syslog no roteador Cisco IOS XE SD-WAN
Configure o Servidor syslog usando os comandos:
logging trap syslog-format rfc5424 logging source-interface GigabitEthernet0/0/0 logging tls-profile tls-profile logging host X.X.X.X transport tls profile tls-profile tls-version TLSv1.26. Verificações
Verificar registros no roteador
show logging
Showing last 10 lines
Log Buffer (512000 bytes):
Apr 9 05:59:48.025: %DMI-5-CONFIG_I: R0/0: dmiauthd: Configured from NETCONF/RESTCONF by admin, transaction-id 189410
Apr 9 05:59:48.709: %DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:58393 for netconf over ssh. External groups:
Apr 9 05:59:50.015: %LINK-5-CHANGED: Interface GigabitEthernet0/0/1, changed state to administratively down
Apr 9 05:59:51.016: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0/1, changed state to down
Apr 9 05:59:52.242: %SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Verificar logs no Servidor Syslog
tail -f /var/log/syslog
root@server1:/etc/syslog-ng# tail -f /var/log/syslog
Apr 9 15:51:14 10.66.91.94 188 <189>1 2024-04-09T05:51:51.037Z - - - - - BOM%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:38032 for netconf over ssh. External groups:
Apr 9 15:59:10 10.66.91.94 177 <189>1 2024-04-09T05:59:47.463Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Apr 9 15:59:10 10.66.91.94 177 <189>1 2024-04-09T05:59:47.463Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Apr 9 15:59:10 10.66.91.94 143 <189>1 2024-04-09T05:59:47.463Z - - - - - BOM%DMI-5-CONFIG_I: R0/0: dmiauthd: Configured from NETCONF/RESTCONF by admin, transaction-id 189410
Apr 9 15:59:11 10.66.91.94 188 <189>1 2024-04-09T05:59:48.711Z - - - - - BOM%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:58393 for netconf over ssh. External groups:
Apr 9 15:59:13 10.66.91.94 133 <189>1 2024-04-09T05:59:50.016Z - - - - - BOM%LINK-5-CHANGED: Interface GigabitEthernet0/0/1, changed state to administratively down
Apr 9 15:59:13 10.66.91.94 137 <189>1 2024-04-09T05:59:50.016Z - - - - - BOM%LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0/1, changed state to down
Apr 9 15:59:15 10.66.91.94 177 <189>1 2024-04-09T05:59:52.242Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Apr 9 15:59:15 10.66.91.94 177 <189>1 2024-04-09T05:59:52.242Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
Apr 9 15:59:18 10.66.91.94 188 <189>1 2024-04-09T05:59:55.286Z - - - - - BOM%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:34575 for netconf over ssh. External groups:
Apr 9 15:59:21 10.66.91.94 113 <187>1 2024-04-09T05:59:58.882Z - - - - - BOM%LINK-3-UPDOWN: Interface GigabitEthernet0/0/1, changed state to up
Apr 9 15:59:21 10.66.91.94 135 <189>1 2024-04-09T05:59:59.882Z - - - - - BOM%LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0/1, changed state to up
Apr 9 15:59:28 10.66.91.94 177 <189>1 2024-04-09T06:00:05.536Z - - - - - BOM%SYS-5-CONFIG_P: Configured programmatically by process iosp_dmiauthd_conn_100001_vty_100001 from console as admin on vty4294966494
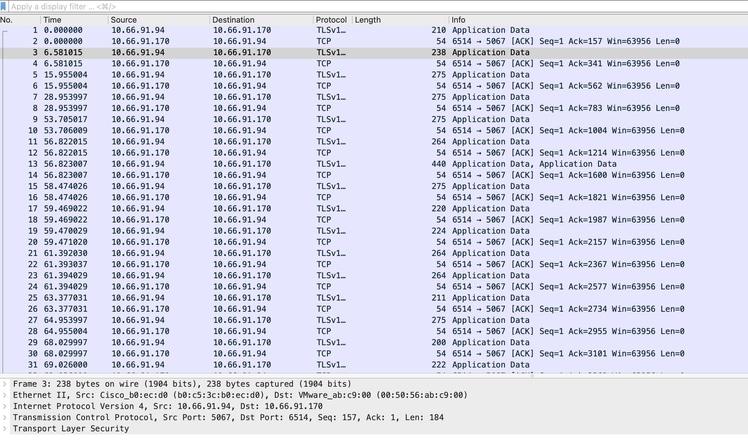
Apr 9 15:59:43 10.66.91.94 188 <189>1 2024-04-09T06:00:20.537Z - - - - - BOM%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'vmanage-admin' authenticated successfully from 1.1.1.1:43530 for netconf over ssh. External groups:Captura de tela do pacote e você pode ver comunicações criptografadas acontecendo:
ISR4331-branch-NEW_Branch#show logging
Trap logging: level informational, 6284 message lines logged
Logging to 10.66.91.170 (tls port 6514, audit disabled,
link up),
131 message lines logged,
0 message lines rate-limited,
0 message lines dropped-by-MD,
xml disabled, sequence number disabled
filtering disabled
tls-profile: tls-proile
Logging Source-Interface: VRF Name:
GigabitEthernet0/0/0
TLS Profiles:
Profile Name: tls-proile
Ciphersuites: Default
Trustpoint: Default
TLS version: TLSv1.2Verificar
No momento, não há procedimento de verificação disponível para esta configuração.
Troubleshooting
Atualmente, não existem informações disponíveis específicas sobre Troubleshooting para esta configuração.
Histórico de revisões
| Revisão | Data de publicação | Comentários |
|---|---|---|
1.0 |
18-Dec-2024 |
Versão inicial |
Colaborado por engenheiros da Cisco
- Aamir SadiqueLíder técnico do Cisco TAC
Contate a Cisco
- Abrir um caso de suporte

- (É necessário um Contrato de Serviço da Cisco)
 Feedback
Feedback