Guia de migração do EzVPN-NEM para FlexVPN
Contents
Introduction
Este documento fornece assistência no processo de migração da configuração do EzVPN (Internet Key Exchange v1 (IKEv1) para a instalação do FlexVPN (IKEv2) com o menor número possível de problemas. Como o Acesso Remoto IKEv2 difere do Acesso Remoto IKEv1 de certas maneiras que tornam a migração um pouco difícil, este documento ajuda a escolher diferentes abordagens de design na migração do modelo EzVPN para o modelo de Acesso Remoto FlexVPN.
Este documento trata do cliente IOS FlexVPN ou do cliente de hardware, este documento não discute o cliente de software. Para obter mais informações sobre o cliente de software, consulte:
-
FlexVPN: IKEv2 com cliente Windows incorporado e autenticação de certificado
-
Exemplo de configuração de cliente FlexVPN e Anyconnect IKEv2
-
Implantação de FlexVPN: Acesso remoto do AnyConnect IKEv2 com EAP-MD5
Prerequisites
Requirements
A Cisco recomenda que você tenha conhecimento destes tópicos:
-
IKEv2
-
Cisco FlexVPN
-
Cisco AnyConnect Secure Mobility Client
-
Cisco VPN Client
Componentes Utilizados
Este documento não se restringe a versões de software e hardware específicas.
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Conventions
Consulte as Convenções de Dicas Técnicas da Cisco para obter mais informações sobre convenções de documentos.
EzVPN versus FlexVPN
Modelo EzVPN - O que sobressai
Como o nome sugere, o objetivo do EzVPN é facilitar a configuração de VPN nos clientes remotos. Para conseguir isso, o cliente é configurado com detalhes mínimos necessários para entrar em contato com o servidor EzVPN correto, também conhecido como perfil do cliente.
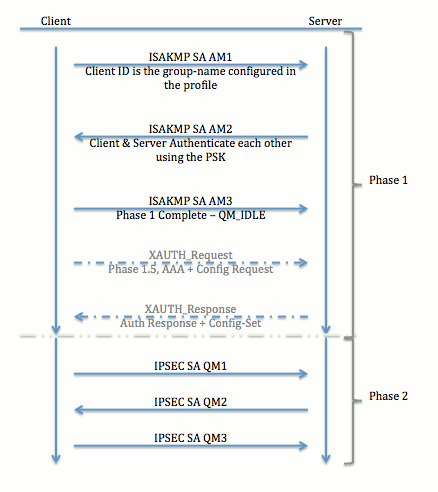
Negociação de túnel
Modelo VPN de acesso remoto FlexVPN
Servidor FlexVPN
Uma diferença importante entre o FlexVPN normal e uma configuração de acesso remoto FlexVPN é que o servidor precisa se autenticar para os clientes FlexVPN através do uso apenas do método de chaves e certificados pré-compartilhados (RSA-SIG). O FlexVPN permite que você decida quais métodos de autenticação o iniciador e o respondedor usam, independentemente um do outro. Por outras palavras, podem ser iguais ou podem ser diferentes. No entanto, quando se trata de acesso remoto FlexVPN, o servidor não tem uma escolha.
Métodos de autenticação de cliente FlexVPN do IOS
O cliente suporta os seguintes métodos de autenticação:
-
RSA-SIG — Autenticação de certificado digital.
-
Pré-compartilhamento — Autenticação de chave pré-compartilhada (PSK).
-
Extensible Authentication Protocol (EAP) - EAP Authentication. EAP-Support para cliente IOS FlexVPN foi adicionado em 15.2(3)T.
Os métodos EAP suportados pelo cliente IOS FlexVPN incluem:
-
Extensible Authentication Protocol-Message Digest 5 (EAP-MD5),
-
Extensible Authentication Protocol-Microsoft Challenge Handshake Authentication Protocol Version 2 (EAP-MSCHAPv2) e
-
Extensible Authentication Protocol-Generic Token Card (EAP-GTC).
-
Este documento descreve somente o uso da autenticação RSA-SIG, por estes motivos:
-
Escalável — Cada cliente recebe um certificado e, no servidor, uma parte genérica da identidade do cliente é autenticada em relação a ele.
-
Seguro — mais seguro que uma PSK curinga (no caso de autorização local). Embora, no caso da autorização AAA (authentication, authorization, and accounting), seja mais fácil escrever PSKs separadas com base na identidade IKE gerenciada.
A configuração do cliente FlexVPN mostrada neste documento pode parecer pouco exaustiva em comparação com o cliente EasyVPN. Isso ocorre porque a configuração inclui algumas partes da configuração que não precisam ser configuradas pelo usuário devido a padrões inteligentes. Padrões inteligentes é o termo usado para se referir à configuração preconfigurada ou padrão para vários itens, como proposta, política, conjunto de transformação de IPSec etc. E ao contrário dos valores padrão IKEv1, os valores padrão inteligentes IKEv2 são fortes. Por exemplo, ele usa o Advanced Encryption Standard (AES-256), o Secure Hash Algorithm (SHA-512) e o Group-5 nas propostas e assim por diante.
Negociação de túnel
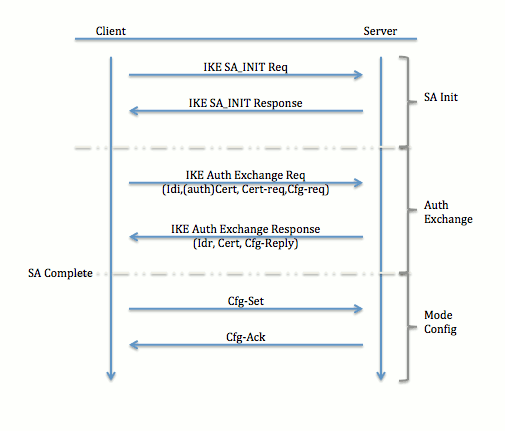
Para obter mais informações sobre a troca de pacotes para uma troca de IKEv2, consulte IKEv2 Packet Exchange and Protocol Level Debugging.
Configuração inicial
Topologia
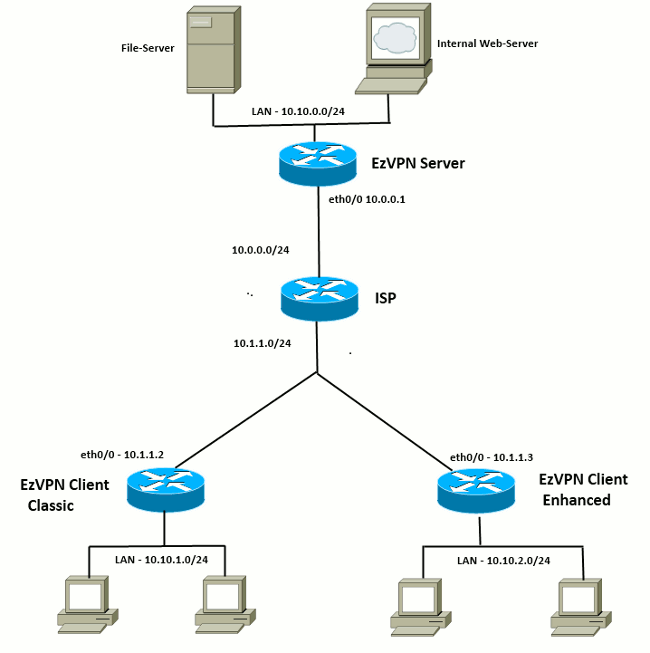
Configuração inicial
Hub EzVPN - baseado em dVTI
!! AAA Config for EzVPN clients. We are using Local AAA Server. aaa new-model aaa authentication login default local aaa authorization network default local !! ISAKMP Policy crypto isakmp policy 1 encr 3des authentication pre-share group 2 !! ISAKMP On-Demand Keep-Alive crypto isakmp keepalive 10 2 !! EzVPN Split ACL access-list 101 permit ip 10.10.0.0 0.0.0.255 any !! EzVPN Client Group Configuration. This is what holds all the config attributes crypto isakmp client configuration group cisco key cisco dns 6.0.0.2 wins 7.0.0.1 domain cisco.com acl 101 save-password !! ISAKMP Profile. This ties Client IKE identity to AAA. !! And since this is dVTI setup, ISAKMP Profile tells the IOS !! from which Virtual-Template (VT1) to clone the Virtual Access interfaces crypto isakmp profile vi match identity group cisco client authentication list default isakmp authorization list default virtual-template 1 !! IPSec Transform Set. crypto ipsec transform-set set esp-3des esp-sha-hmac !! IPSec Profile. This ties Transform set and ISAKMP Profile together. crypto ipsec profile vi set transform-set set set isakmp-profile vi !! The loopback interface. And virtual-template borrows the address from here. interface Loopback0 ip address 10.10.10.1 255.255.255.252 !! dVTI interface. interface Virtual-Template1 type tunnel ip unnumbered Loopback0 tunnel mode ipsec ipv4 tunnel protection ipsec profile vi
Cliente EzVPN - Clássico (sem VTI)
!! ISAKMP On-Demand Keep-Alive crypto isakmp keepalive 10 2 !! EzVPN Client - Group Name and The key (as configured on the Server), !! Peer address and XAUTH config go here. crypto ipsec client ezvpn ez connect auto group cisco key cisco local-address Ethernet0/0 mode network-extension peer 10.0.0.1 username cisco password cisco xauth userid mode local !! EzVPn outside interface - i.e. WAN interface interface Ethernet0/0 ip address 10.1.1.2 255.255.255.0 crypto ipsec client ezvpn ez !! EzVPN inside interface !! Traffic sourced from this LAN is sent over established Tunnel interface Ethernet0/1 ip address 10.10.1.1 255.255.255.0 crypto ipsec client ezvpn ez inside
Cliente EzVPN - Avançado (baseado em VTI)
!! VTI - interface Virtual-Template1 type tunnel no ip address tunnel mode ipsec ipv4 !! ISAKMP On-Demand Keep-Alive crypto isakmp keepalive 10 2 !! EzVPN Client - Group Name and The key (as configured on the Server), !! Peer address and XAUTH config go here. !! Also this config says which Virtual Template to use. crypto ipsec client ezvpn ez connect auto group cisco key cisco local-address Ethernet0/0 mode network-extension peer 10.0.0.1 virtual-interface 1 username cisco password cisco xauth userid mode local !! EzVPn outside interface - WAN interface interface Ethernet0/0 ip address 10.1.1.3 255.255.255.0 crypto ipsec client ezvpn ez !! EzVPN inside interface - !! Traffic sourced from this LAN is sent over established Tunnel interface Ethernet0/1 ip address 10.10.2.1 255.255.255.0 crypto ipsec client ezvpn ez inside
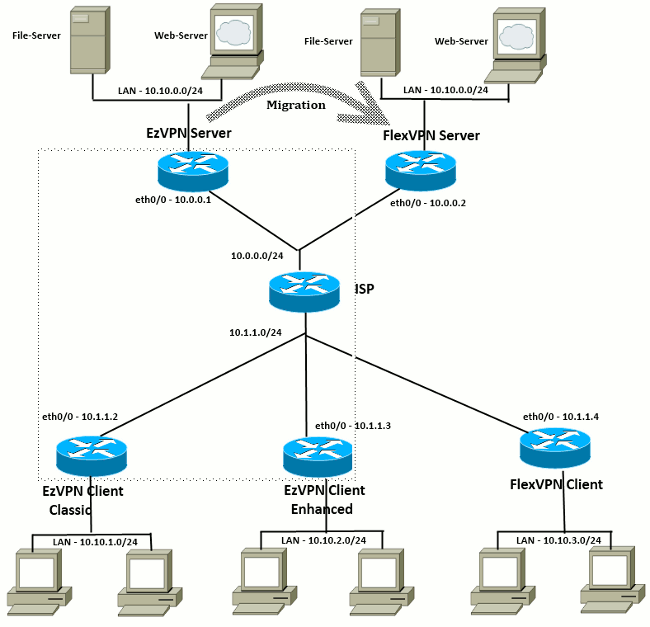
Abordagem de migração de EzVPN para FlexVPN
O servidor que atua como um servidor EzVPN também pode atuar como um servidor FlexVPN desde que ele suporte a configuração de Acesso Remoto IKEv2. Para um suporte completo à configuração de IKEv2, recomenda-se qualquer coisa acima do IOS v15.2(3)T. Nesses exemplos, 15.2(4)M1 foi usado.
Há duas abordagens possíveis:
-
Configure o servidor EzVPN como o servidor FlexVPN e, em seguida, migre os clientes EzVPN para a configuração Flex.
-
Configure um roteador diferente como um servidor FlexVPN. Os clientes EzVPN e os clientes FlexVPN migrados continuam a se comunicar através da criação de uma conexão entre o servidor FlexVPN e o servidor EzVPN.
Este documento descreve a segunda abordagem e usa um novo spoke (por exemplo, Spoke3), como o cliente FlexVPN. Esse spoke pode ser usado como referência para migrar outros clientes no futuro.
Etapas de migração
Observe que ao migrar de um spoke EzVPN para um spoke FlexVPN, você pode optar por carregar a configuração FlexVPN no spoke EzVPN. No entanto, durante todo o corte, você pode precisar de um acesso de gerenciamento fora de banda (não VPN) para a caixa.
Topologia migrada
Configuração
Hub FlexVPN
!! AAA Authorization done Locally aaa new-model aaa authorization network Flex local !! PKI TrustPoint to Sign and Validate Certificates. !! Contains Identity Certificate and CA Certificate crypto pki trustpoint FlexServer enrollment terminal revocation-check none rsakeypair FlexServer subject-name CN=flexserver.cisco.com,OU=FlexVPN !! Access-list used in Config-Reply in order to push routes access-list 1 permit 10.10.0.0 0.0.0.255 !! IKEv2 Authorization done locally. Used in Config-Set. crypto ikev2 authorization policy FlexClient-Author def-domain cisco.com route set interface route set access-list 1 !! IKEv2 Proposal. Optional Config. Smart-Default takes care of this. crypto ikev2 proposal FlexClient-Proposal encryption aes-cbc-128 aes-cbc-192 3des integrity sha256 sha512 sha1 group 5 2 !! If IKEv2 Proposal was left out default, then IKEv2 Policy can be left out too. !! Ties Proposal to Peer address/fvrf crypto ikev2 policy FlexClient-Policy match fvrf any proposal FlexClient-Proposal !! IKEv2 Profile. This is the main Part !! Clients are configured to send their FQDN. And we match the domain 'cisco.com' !! We are sending 'flexserver.cisco.com' as the fqdn identity. !! Local and Remote authentication is RSA-SIG !! Authorization (config-reply) is done locally with the user-name !! 'FlexClient-Author' !! This whole profile is tied to Virtual-Template 1 crypto ikev2 profile FlexClient-Profile match identity remote fqdn domain cisco.com identity local fqdn flexserver.cisco.com authentication remote rsa-sig authentication local rsa-sig pki trustpoint FlexServer aaa authorization group cert list Flex FlexClient-Author virtual-template 1 !! IPSec Transform set. Optional Config, since Smart Default takes care of this. crypto ipsec transform-set ESP-AES-SHA1 esp-aes esp-sha-hmac !! IPSec Profile ties default/Configured transform set with the IKEv2 Profile crypto ipsec profile FlexClient-IPSec set transform-set ESP-AES-SHA1 set ikev2-profile FlexClient-Profile !! Loopback interface lends ip address to Virtual-template and !! eventually to Virtual-Access interfaces spawned. interface Loopback0 ip address 10.10.10.1 255.255.255.252 !! The IKEv2 enabled Virtual-Template interface Virtual-Template1 type tunnel ip unnumbered Loopback0 tunnel protection ipsec profile FlexClient-IPSec !! WAN interface interface Ethernet0/0 ip address 10.0.0.2 255.255.255.0 !! LAN interfaces interface Ethernet0/1 ip address 10.10.0.1 255.255.255.0
Nota sobre certificados de servidor
O uso de chave (KU) define a finalidade ou o uso pretendido da chave pública. O Enhanced/Extended Key Usage (EKU) aperfeiçoa o uso principal. O FlexVPN requer que o certificado do servidor tenha uma EKU de autenticação do servidor (OID = 1.3.6.1.5.5.7.3.1 ) com os atributos da KU de Assinatura Digital e Elemento de Chave para que o certificado seja aceito pelo cliente.
FlexServer#show crypto pki certificates verbose
Certificate
Status: Available
Version: 3
Certificate Serial Number (hex): 09
Certificate Usage: General Purpose
Issuer:
l=lal-bagh
c=IN
o=Cisco
ou=TAC
cn=Praveen
Subject:
Name: flexserver.cisco.com
ou=FlexVPN
cn=flexserver.cisco.com
CRL Distribution Points:
http://10.48.67.33:80/Praveen/Praveen.crl
<snip>
Signature Algorithm: MD5 with RSA Encryption
Fingerprint MD5: F3646C9B 1CC26A81 C3CB2034 061302AA
Fingerprint SHA1: 7E9E99D4 B66C70E3 CBA8C4DB DD94629C 023EEBE7
X509v3 extensions:
X509v3 Key Usage: E0000000
Digital Signature
Non Repudiation
Key Encipherment
<snip>
Authority Info Access:
Extended Key Usage:
Client Auth
Server Auth
Associated Trustpoints: FlexServer
Storage: nvram:lal-bagh#9.cer
Key Label: FlexServer
Key storage device: private config
CA Certificate
<snip>
Configuração do cliente FlexVPN
!! AAA Authorization done Locally aaa new-model aaa authorization network Flex local !! PKI TrustPoint to Sign and Validate Certificates. !! Contains Identity Certificate and CA Certificate crypto pki trustpoint Spoke3-Flex enrollment terminal revocation-check none subject-name CN=spoke3.cisco.com,OU=FlexVPN rsakeypair Spoke3-Flex !! Access-list used in Config-Set in order to push routes access-list 1 permit 10.10.3.0 0.0.0.255 !! IKEv2 Authorization done locally. Used in Config-Set. crypto ikev2 authorization policy FlexClient-Author route set interface route set access-list 1 !! IKEv2 Proposal. Optional Config. Smart-Default takes care of this. crypto ikev2 proposal FlexClient-Proposal encryption aes-cbc-128 aes-cbc-192 3des integrity sha256 sha512 sha1 group 5 2 !! If IKEv2 Proposal was left out default, then IKEv2 Policy can be left out too. !! Ties Proposal to Peer address/fvrf crypto ikev2 policy FlexClient-Policy match fvrf any proposal FlexClient-Proposal !! IKEv2 Profile. This is the main Part !! Server is configured to send its FQDN type IKE-ID, !! and we match the domain 'cisco.com' !! (If the IKE-ID type is DN (extracted from the certificate), !! we will need a certificate map) !! We are sending 'spoke3.cisco.com' as the IKE-identity of type fqdn. !! Local and Remote authentication is RSA-SIG !! Authorization (config-set) is done locally using the user-name filter !! 'FlexClient-Author' crypto ikev2 profile FlexClient-Profile match identity remote fqdn flexserver.cisco.com identity local fqdn spoke3.cisco.com authentication remote rsa-sig authentication local rsa-sig pki trustpoint Spoke3-Flex aaa authorization group cert list Flex FlexClient-Author !! IPSec Transform set. Optional Config, since Smart Default takes care of this. crypto ipsec transform-set ESP-AES-SHA1 esp-aes esp-sha-hmac !! IPSec Profile ties the transform set with the IKEv2 Profile crypto ipsec profile FlexClient-IPSec set transform-set ESP-AES-SHA1 set ikev2-profile FlexClient-Profile !! FlexVPN Client Tunnel interface. !! If IP-Address of the tunnel is negotiated, !! FlexVPN server is capable of assigning an IP through Config-Set interface Tunnel0 ip unnumbered Ethernet0/1 tunnel source Ethernet0/0 tunnel destination dynamic tunnel protection ipsec profile FlexClient-IPSec !! Final FlexVPN client Part. !! Multiple backup Peer and/or Multiple Tunnel source interfaces can be configured crypto ikev2 client flexvpn FlexClient peer 1 10.0.0.2 client connect Tunnel0 !! WAN interface interface Ethernet0/0 ip address 10.1.1.4 255.255.255.248 !! LAN Interface interface Ethernet0/1 ip address 10.10.3.1 255.255.255.0
Observação sobre certificados de cliente
O FlexVPN requer que o certificado do cliente tenha uma EKU de Autenticação de Cliente (OID = 1.3.6.1.5.5.7.3.2 ) com os atributos de KU de Assinatura Digital e Elemento de Chave para que o certificado seja aceito pelo servidor.
Spoke3#show crypto pki certificates verbose
Certificate
Status: Available
Version: 3
Certificate Serial Number (hex): 08
Certificate Usage: General Purpose
Issuer:
l=lal-bagh
c=IN
o=Cisco
ou=TAC
cn=Praveen
Subject:
Name: spoke3.cisco.com
ou=FlexVPN
cn=spoke3.cisco.com
<snip>
Subject Key Info:
Public Key Algorithm: rsaEncryption
RSA Public Key: (1024 bit)
Signature Algorithm: MD5 with RSA Encryption
Fingerprint MD5: 2381D319 906177E1 F45019BC 61059BD5
Fingerprint SHA1: D81FD705 653547F2 D0916710 E6B096A1 23F6C467
X509v3 extensions:
X509v3 Key Usage: E0000000
Digital Signature
Non Repudiation
Key Encipherment
<snip>
Extended Key Usage:
Client Auth
Server Auth
Associated Trustpoints: Spoke3-Flex
Storage: nvram:lal-bagh#8.cer
Key Label: Spoke3-Flex
Key storage device: private config
CA Certificate
<snip>
Verificação de operação FlexVPN
Servidor FlexVPN
FlexServer#show crypto ikev2 session
IPv4 Crypto IKEv2 Session
Session-id:5, Status:UP-ACTIVE, IKE count:1, CHILD count:1
Tunnel-id Local Remote fvrf/ivrf Status
1 10.0.0.2/500 10.1.1.4/500 none/none READY
Encr: AES-CBC, keysize: 192, Hash: SHA512, DH Grp:5, Auth sign: RSA, Auth verify:
RSA
Life/Active Time: 86400/7199 sec
Child sa: local selector 10.0.0.2/0 - 10.0.0.2/65535
remote selector 10.1.1.4/0 - 10.1.1.4/65535
ESP spi in/out: 0xA9571C00/0x822DDAAD
FlexServer#show crypto ikev2 session detailed
IPv4 Crypto IKEv2 Session
Session-id:5, Status:UP-ACTIVE, IKE count:1, CHILD count:1
Tunnel-id Local Remote fvrf/ivrf Status
1 10.0.0.2/500 10.1.1.4/500 none/none READY
Encr: AES-CBC, keysize: 192, Hash: SHA512, DH Grp:5, Auth sign: RSA, Auth verify:
RSA
Life/Active Time: 86400/7244 sec
CE id: 1016, Session-id: 5
Status Description: Negotiation done
Local spi: 648921093349609A Remote spi: 1C2FFF727C8EA465
Local id: flexserver.cisco.com
Remote id: spoke3.cisco.com
Local req msg id: 2 Remote req msg id: 5
Local next msg id: 2 Remote next msg id: 5
Local req queued: 2 Remote req queued: 5
Local window: 5 Remote window: 5
DPD configured for 0 seconds, retry 0
NAT-T is not detected
Cisco Trust Security SGT is disabled
Initiator of SA : No
Remote subnets:
10.10.3.0 255.255.255.0
Child sa: local selector 10.0.0.2/0 - 10.0.0.2/65535
remote selector 10.1.1.4/0 - 10.1.1.4/65535
ESP spi in/out: 0xA9571C00/0x822DDAAD
AH spi in/out: 0x0/0x0
CPI in/out: 0x0/0x0
Encr: AES-CBC, keysize: 128, esp_hmac: SHA96
ah_hmac: None, comp: IPCOMP_NONE, mode transport
FlexServer#show ip route static
10.0.0.0/8 is variably subnetted, 9 subnets, 4 masks
S 10.10.3.0/30 is directly connected, Virtual-Access1
FlexServer#ping 10.10.3.1 repeat 100
Type escape sequence to abort.
Sending 100, 100-byte ICMP Echos to 10.10.3.1, timeout is 2 seconds:
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Success rate is 100 percent (100/100), round-trip min/avg/max = 1/5/13 ms
FlexServer#show crypto ipsec sa | I ident|caps|spi
local ident (addr/mask/prot/port): (10.0.0.2/255.255.255.255/47/0)
remote ident (addr/mask/prot/port): (10.1.1.4/255.255.255.255/47/0)
#pkts encaps: 205, #pkts encrypt: 205, #pkts digest: 205
#pkts decaps: 200, #pkts decrypt: 200, #pkts verify: 200
current outbound spi: 0x822DDAAD(2184043181)
spi: 0xA9571C00(2841058304)
spi: 0x822DDAAD(2184043181)
FlexVPN remoto
Spoke3#show crypto ikev2 session
IPv4 Crypto IKEv2 Session
Session-id:4, Status:UP-ACTIVE, IKE count:1, CHILD count:1
Tunnel-id Local Remote fvrf/ivrf Status
1 10.1.1.4/500 10.0.0.2/500 none/none READY
Encr: AES-CBC, keysize: 192, Hash: SHA512, DH Grp:5, Auth sign: RSA, Auth verify:
RSA
Life/Active Time: 86400/7621 sec
Child sa: local selector 10.1.1.4/0 - 10.1.1.4/65535
remote selector 10.0.0.2/0 - 10.0.0.2/65535
ESP spi in/out: 0x822DDAAD/0xA9571C00
Spoke3#show crypto ikev2 session detailed
IPv4 Crypto IKEv2 Session
Session-id:4, Status:UP-ACTIVE, IKE count:1, CHILD count:1
Tunnel-id Local Remote fvrf/ivrf Status
1 10.1.1.4/500 10.0.0.2/500 none/none READY
Encr: AES-CBC, keysize: 192, Hash: SHA512, DH Grp:5, Auth sign: RSA, Auth verify:
RSA
Life/Active Time: 86400/7612 sec
CE id: 1016, Session-id: 4
Status Description: Negotiation done
Local spi: 1C2FFF727C8EA465 Remote spi: 648921093349609A
Local id: spoke3.cisco.com
Remote id: flexserver.cisco.com
Local req msg id: 5 Remote req msg id: 2
Local next msg id: 5 Remote next msg id: 2
Local req queued: 5 Remote req queued: 2
Local window: 5 Remote window: 5
DPD configured for 0 seconds, retry 0
NAT-T is not detected
Cisco Trust Security SGT is disabled
Initiator of SA : Yes
Default Domain: cisco.com
Remote subnets:
10.10.10.1 255.255.255.255
10.10.0.0 255.255.255.0
Child sa: local selector 10.1.1.4/0 - 10.1.1.4/65535
remote selector 10.0.0.2/0 - 10.0.0.2/65535
ESP spi in/out: 0x822DDAAD/0xA9571C00
AH spi in/out: 0x0/0x0
CPI in/out: 0x0/0x0
Encr: AES-CBC, keysize: 128, esp_hmac: SHA96
ah_hmac: None, comp: IPCOMP_NONE, mode transport
Spoke3#ping 10.10.0.1 repeat 100
Type escape sequence to abort.
Sending 100, 100-byte ICMP Echos to 10.10.0.1, timeout is 2 seconds:
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Success rate is 100 percent (100/100), round-trip min/avg/max = 1/5/12 ms
Spoke3#show crypto ipsec sa | I ident|caps|spi
local ident (addr/mask/prot/port): (10.1.1.4/255.255.255.255/47/0)
remote ident (addr/mask/prot/port): (10.0.0.2/255.255.255.255/47/0)
#pkts encaps: 300, #pkts encrypt: 300, #pkts digest: 300
#pkts decaps: 309, #pkts decrypt: 309, #pkts verify: 309
current outbound spi: 0xA9571C00(2841058304)
spi: 0x822DDAAD(2184043181)
spi: 0xA9571C00(2841058304)
Informações Relacionadas
- FlexVPN: IKEv2 com Cliente Windows incorporado e Certificado de Autenticação TechNote
- Exemplo de configuração de cliente FlexVPN e Anyconnect IKEv2 TechNote
- Implantação de FlexVPN: Acesso remoto do AnyConnect IKEv2 com o EAP-MD5 TechNote
- Nota técnica de depuração de nível de protocolo e troca de pacotes IKEv2
- Cisco FlexVPN
- Negociação IPsec/Protocolos IKE
- Cisco AnyConnect Secure Mobility Client
- Cisco VPN Client
- Suporte Técnico e Documentação - Cisco Systems
Histórico de revisões
| Revisão | Data de publicação | Comentários |
|---|---|---|
1.0 |
15-Mar-2013 |
Versão inicial |
Contate a Cisco
- Abrir um caso de suporte

- (É necessário um Contrato de Serviço da Cisco)
 Feedback
Feedback