在ECE中为代理和分区管理配置SSO并对其进行故障排除
下载选项
非歧视性语言
此产品的文档集力求使用非歧视性语言。在本文档集中,非歧视性语言是指不隐含针对年龄、残障、性别、种族身份、族群身份、性取向、社会经济地位和交叉性的歧视的语言。由于产品软件的用户界面中使用的硬编码语言、基于 RFP 文档使用的语言或引用的第三方产品使用的语言,文档中可能无法确保完全使用非歧视性语言。 深入了解思科如何使用包容性语言。
关于此翻译
思科采用人工翻译与机器翻译相结合的方式将此文档翻译成不同语言,希望全球的用户都能通过各自的语言得到支持性的内容。 请注意:即使是最好的机器翻译,其准确度也不及专业翻译人员的水平。 Cisco Systems, Inc. 对于翻译的准确性不承担任何责任,并建议您总是参考英文原始文档(已提供链接)。
简介
本文档介绍在ECE解决方案中为代理和分区管理员配置单一登录(SSO)所需的步骤。
先决条件
要求
Cisco 建议您了解以下主题:
思科套装联系中心企业版(PCCE)
思科统一联系中心企业版(UCCE)
企业聊天和电子邮件(ECE)
Microsoft Active Directory
使用的组件
本文档中的信息基于以下软件和硬件版本:
UCCE版本:12.6(1)
ECE版本:12.6(1)
Windows Server 2016上的Microsoft Active Directory联合身份验证服务(ADFS)
本文档中的信息都是基于特定实验室环境中的设备编写的。本文档中使用的所有设备最初均采用原始(默认)配置。如果您的网络处于活动状态,请确保您了解所有命令的潜在影响。
背景信息
可以在Finesse外部访问企业聊天和邮件(ECE)控制台,但是,必须启用SSO以允许座席和主管通过Finesse登录到ECE。
还可以为新分区管理员配置单一登录。这可确保登录到Cisco Administrator桌面的新用户有权访问企业聊天和电子邮件管理控制台。
有关单点登录的重要注意事项:
- 分区用户必须在分区级别对安全节点执行为单点登录配置系统的过程,执行必要的操作:查看应用安全和管理应用安全。
- 为了使管理引擎和管理员能够登录代理控制台以外的控制台,一旦启用SSO,您必须在分区设置中提供应用的有效外部URL。有关详细信息,请参阅常规分区设置。
- 配置SSO需要Java密钥库(JKS)证书,以允许具有管理员或主管角色的用户使用其SSO登录凭证登录到Finesse外部的ECE的分区1。请咨询您的IT部门以接收JKS证书。
- 在安装过程中,必须将思科IDS的安全套接字层(SSL)证书导入到所有应用服务器。要获取必要的SSL证书文件,请联系您的IT部门或思科IDS支持。
- Unified CCE的数据库服务器归类区分大小写。从用户信息终端URL返回的声明中的用户名和Unified CCE中的用户名必须相同。如果座席不相同,则单点登录座席无法识别为已登录,并且ECE无法将座席可用性发送到Unified CCE。
- 为Cisco IDS配置SSO会影响已在Unified CCE中配置单点登录的用户。确保在Unified CCE中为您希望在ECE中启用SSO的用户配置为SSO。有关详细信息,请咨询您的Unified CCE管理员。

注意:
- 确保在Unified CCE中为您希望在ECE中启用SSO的用户配置为SSO。
- 本文档指定在单一AD FS部署中为ECE配置信赖部件信任的步骤,其中资源联合服务器和帐户联合服务器安装在同一台计算机上。
- 对于拆分AD FS部署,请导航至相应版本的ECE安装和配置指南。
配置步骤
为ECE配置信赖方信任
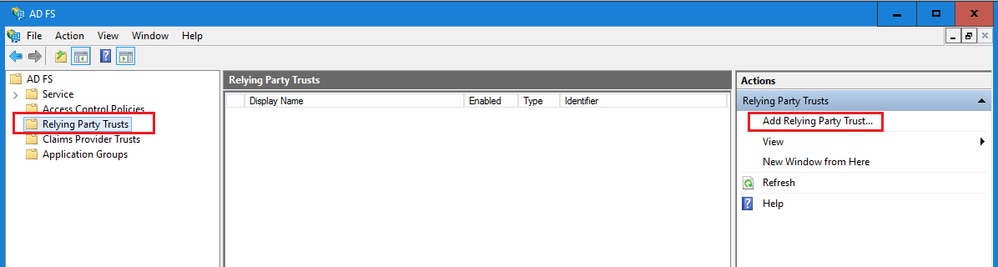
打开AD FS管理控制台并导航到AD FS >“信任关系”>“信赖方信任”。
在“操作”部分中,单击添加信赖方信任。.
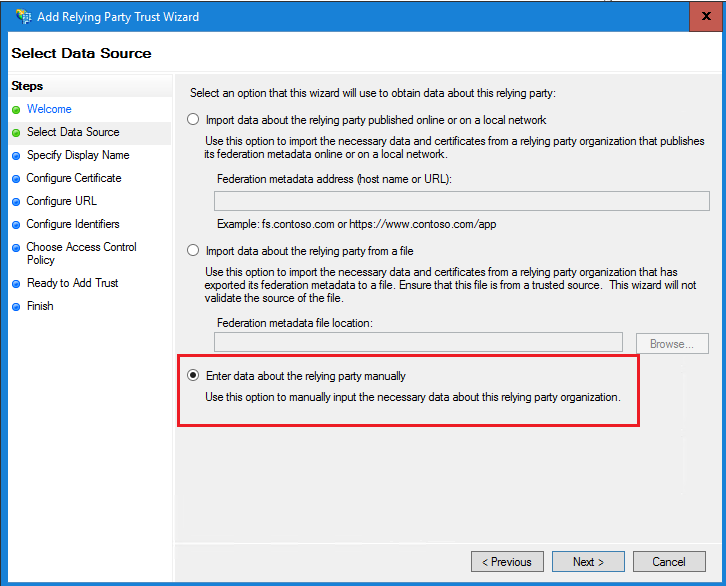
在“添加信赖方信任”向导中,单击“开始”并完成以下步骤:
a.在“选择数据源”页中,选择手动输入关于应答方的数据选项,然后单击“下一步”。
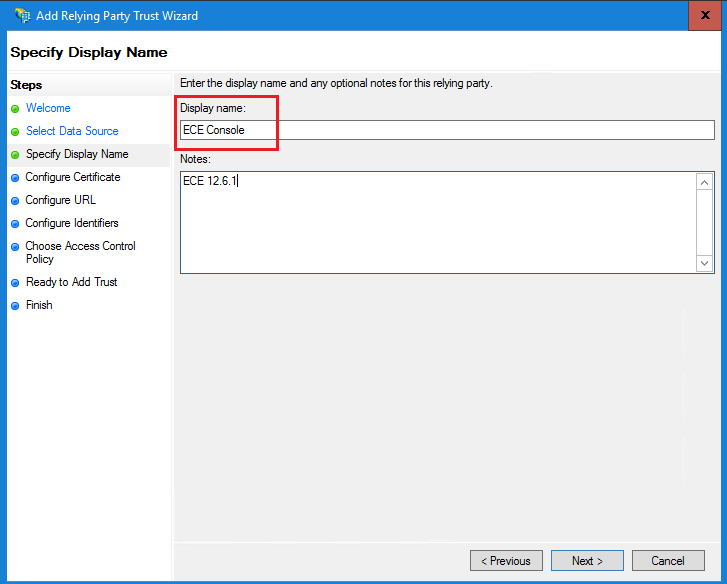
b.在“指定显示名称”页中,为信赖方提供显示名称。单击“下一步”
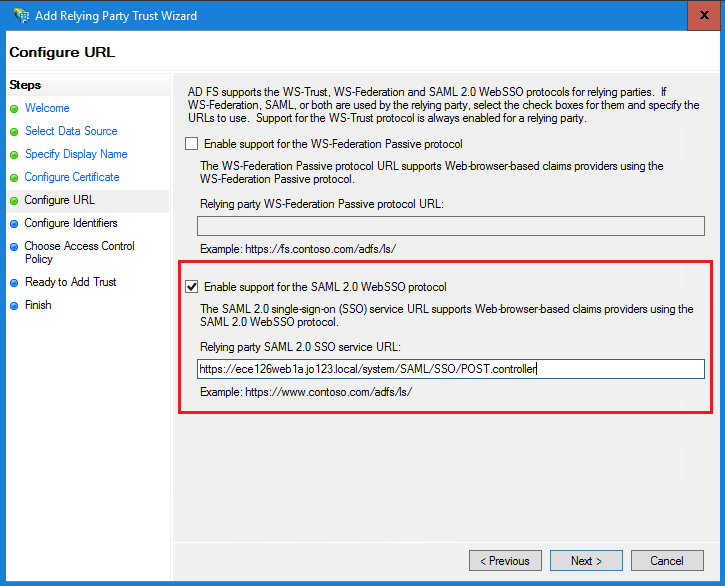
c.在Configure URL(配置URL)页面中:
i.选择Enable support for the SAML 2.0 Web SSO protocol选项。
ii.在信赖方SAML 2.0 SSO服务器URL字段中,按照以下格式提供URL:https://<Web-Server-Or-Load-Balancer-FQDN>/system/SAML/SSO/POST.controller
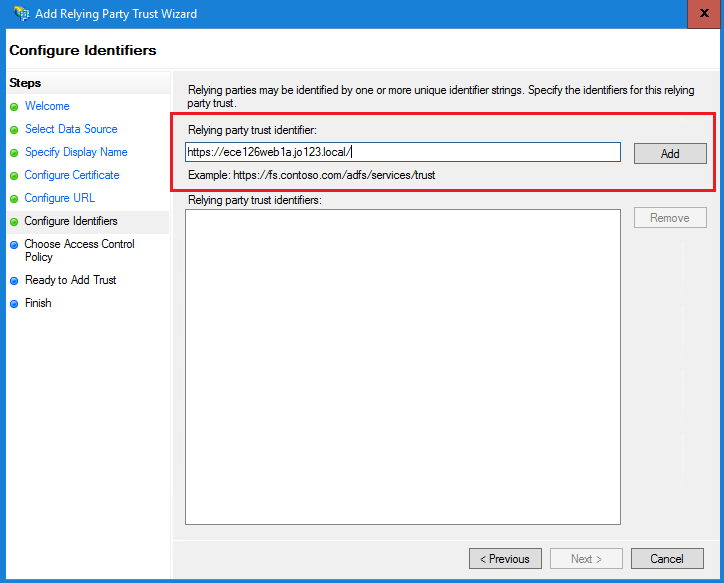
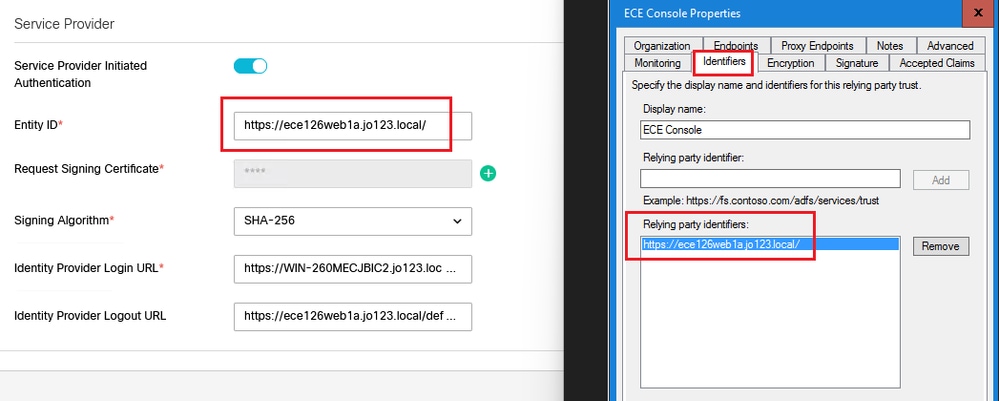
d.在“配置标识符”页上,提供信赖方信任标识符,然后单击“添加”。
-
值必须采用以下格式:https:// <Web-Server-Or-Load-Balancer-FQDN>/
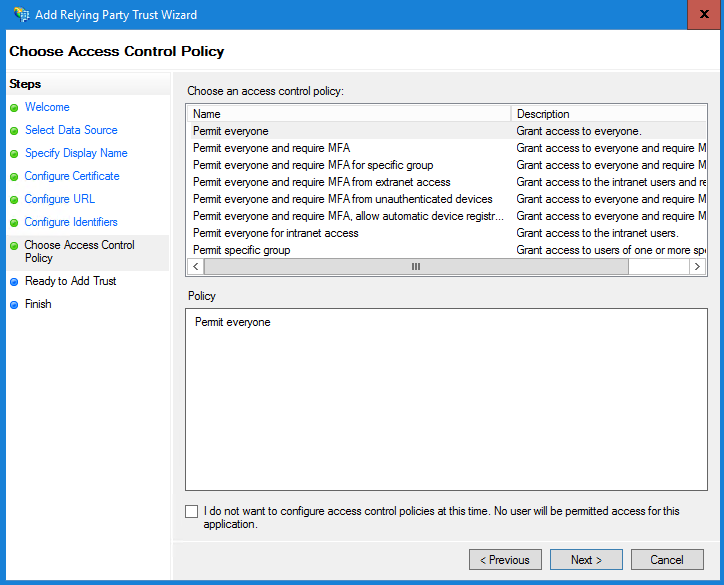
e.在Choose Access Control Policy页中,单击具有默认值“Permit everyone”策略的“next”。
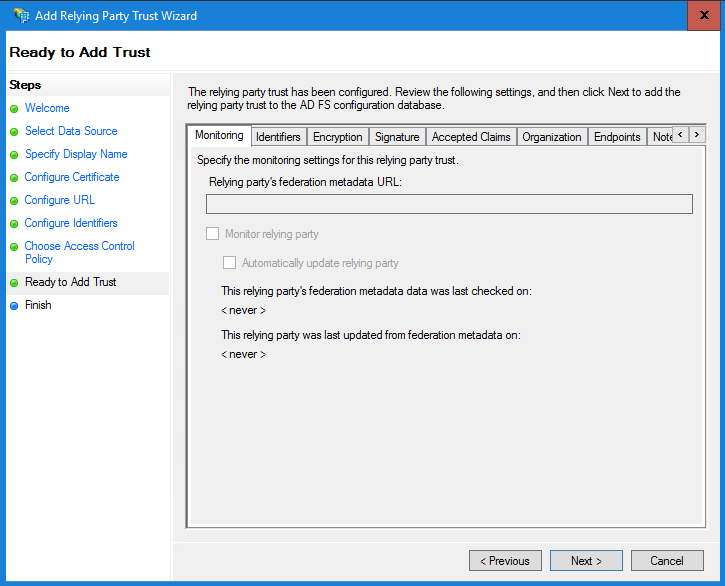
f.在“准备添加信任”页中,单击“下一步”。
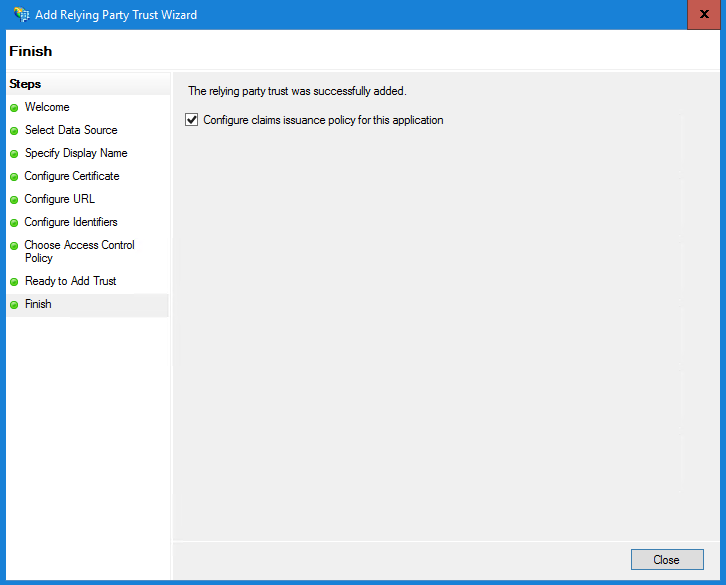
g.成功添加信赖方信任后,点击“关闭”。
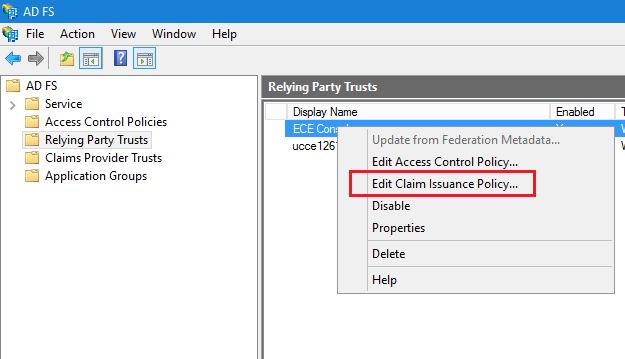
在信赖提供程序信任列表中,选择为ECE创建的信赖方信任,并在“操作”部分中单击属性。
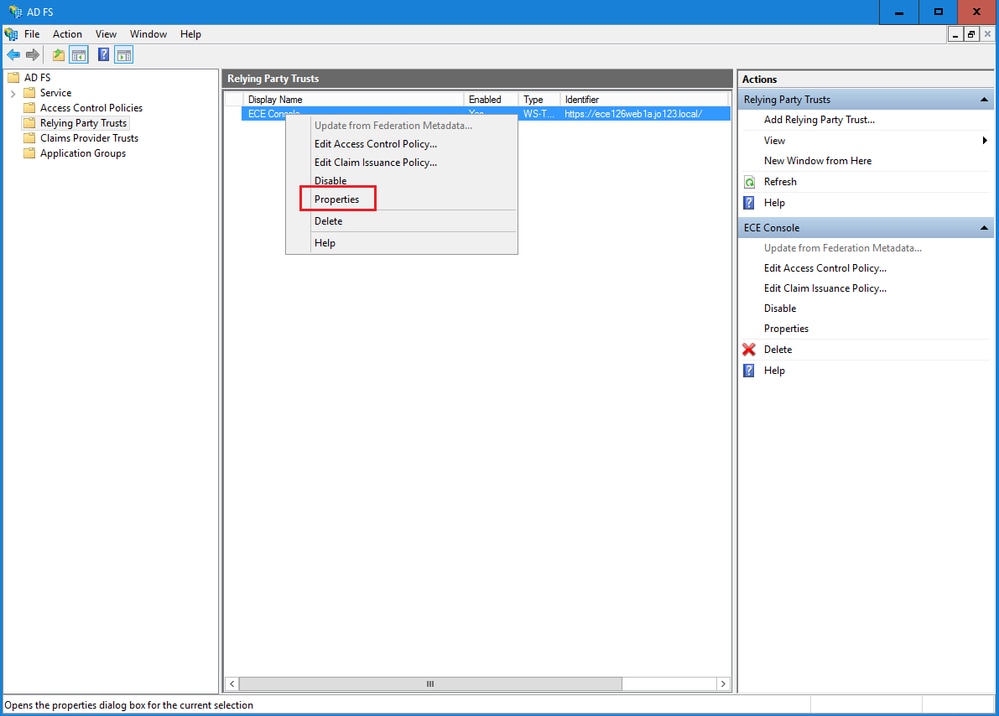
在“属性”窗口中,导航到终端选项卡,然后单击添加SAML..按钮
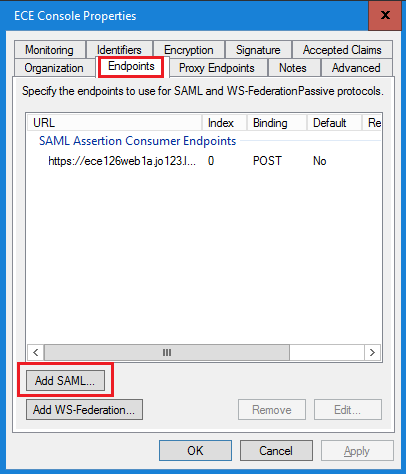
在Add an Endpoint窗口中,按照说明进行配置:
- 选择SAML Logout作为终端类型。
- 将受信任URL指定为https://<ADFS-server-FQDN>/adfs/ls/?wa=wsignoutcleanup1.0
- Click OK.
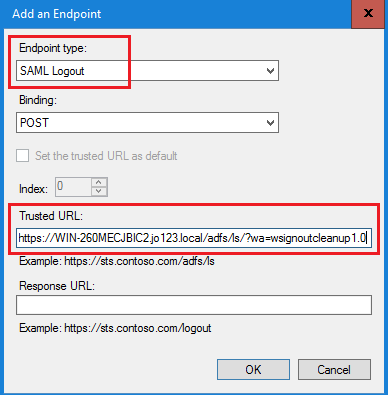
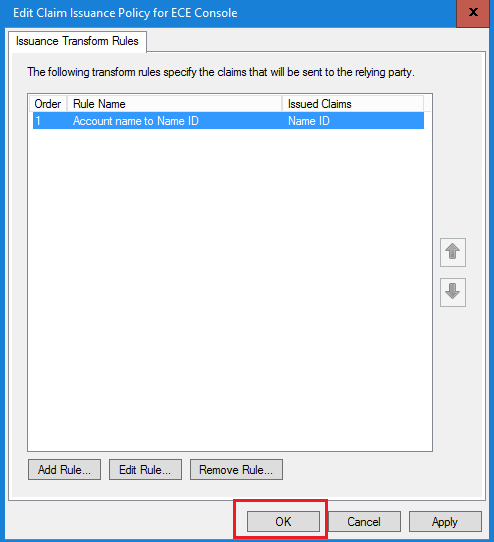
在“信赖提供商信任”列表中,选择为ECE创建的信任,并在“操作”部分中点击编辑索赔保险单。
在“Edit Claim Insurance Policy”窗口的“Issuance Transform Rules”选项卡下,单击Add Rule...按钮并进行如下配置:
a.在“选择规则类型”页中,从下拉菜单中选择将LDAP属性作为声明发送,然后单击“下一步”。
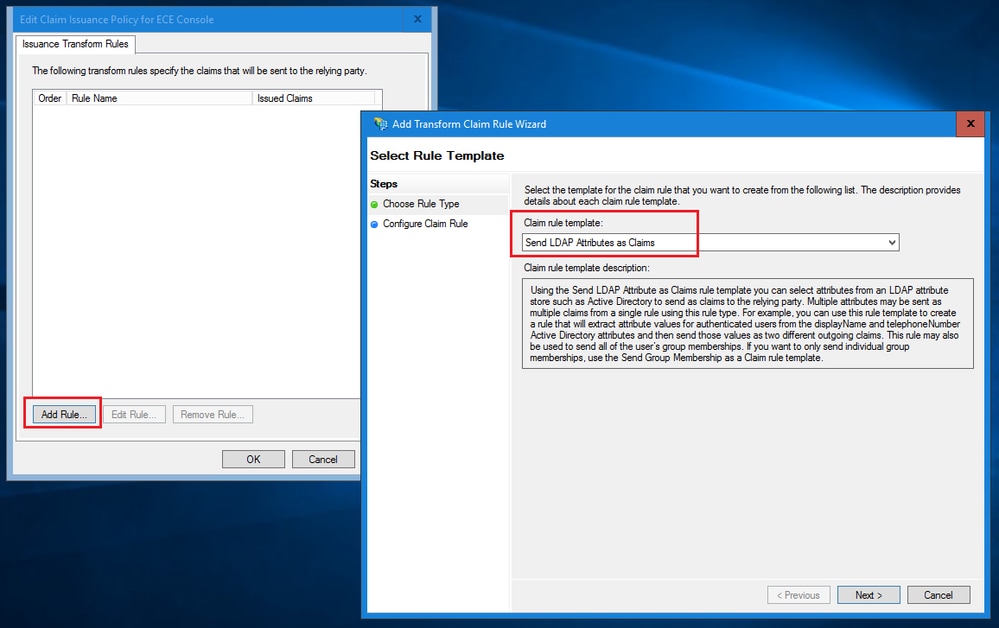
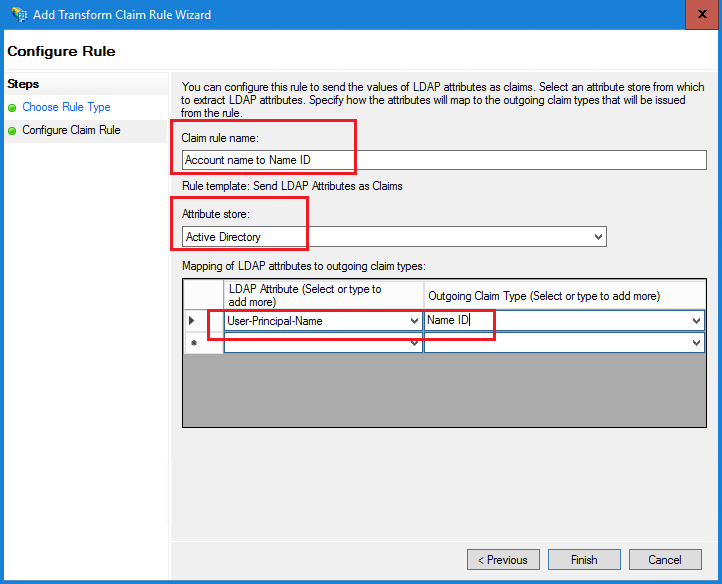
b.在“配置声明规则”页中:
- 提供声明规则名称并选择属性存储。
- 定义LDAP属性和传出声明类型的映射。
- 选择Name ID作为传出声明类型名称。
- 点击Finish返回Edit Claim Insurance Policy窗口,然后点击OK。
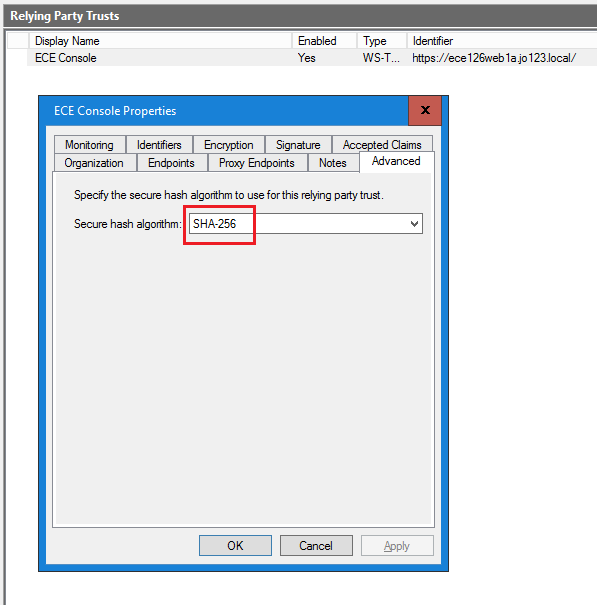
在Relying Provider Trusts列表中,双击您创建的ECE信赖方信任。
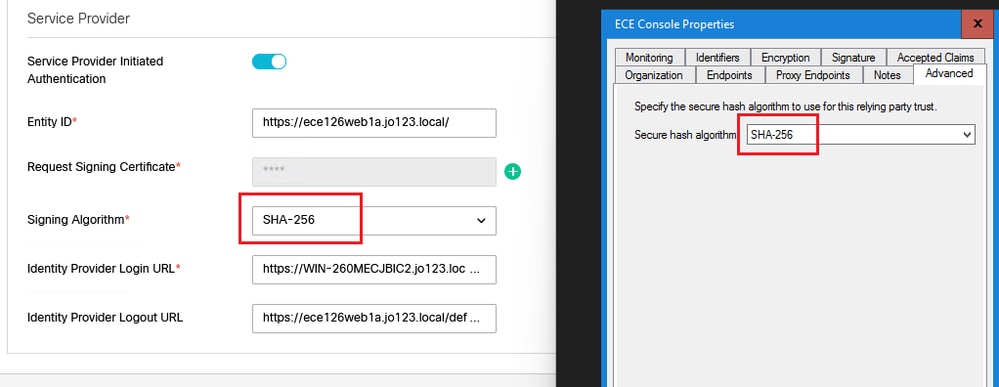
在打开的“属性”窗口中,转到“高级”选项卡,将“安全散列算法”设置为SHA-1或SHA-256。请单击“确定”关闭窗口。

注意:此值必须与ECE中“SSO配置”下的“服务提供商”设置的“签名算法”值匹配
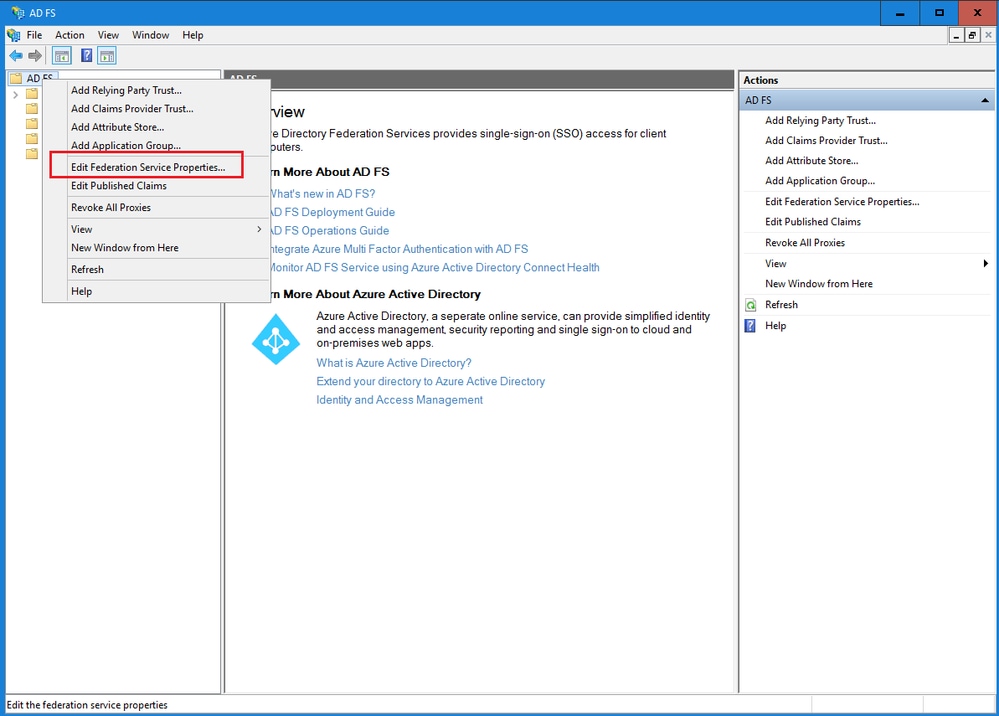
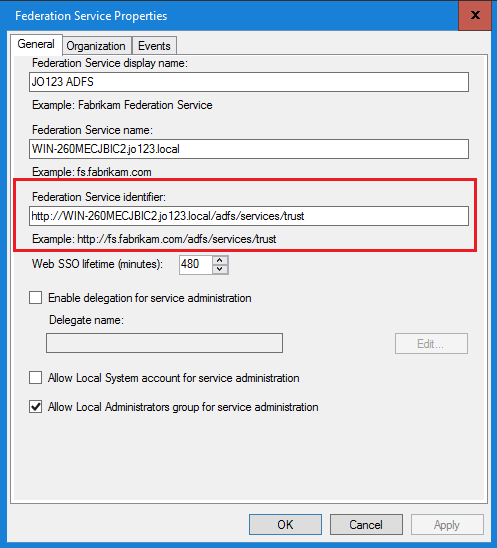
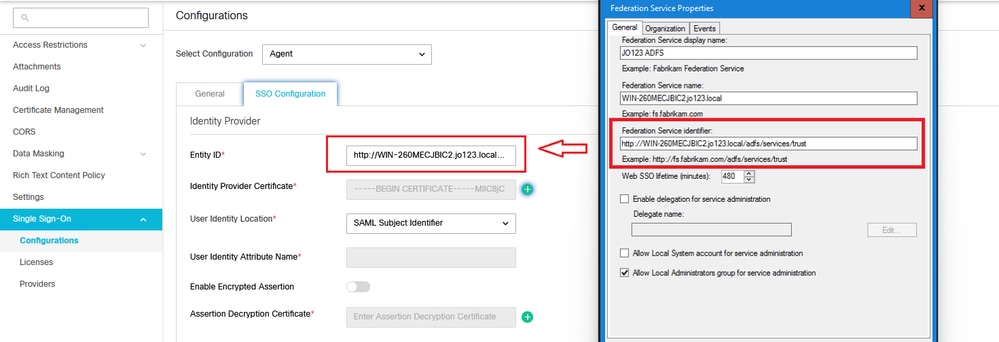
验证并记下联合身份验证服务标识符值。
- 在AD FS管理控制台中,选择并右键单击AD FS >编辑联合身份验证服务属性>常规选项卡>联合身份验证服务标识符

注意:
- 必须完全按照在ECE中的SSO配置下为身份提供程序配置“实体ID”值的方式添加此值。
- 使用http://并不意味着ADFS不安全,它只是一个标识符。
配置身份提供程序
配置SSO需要Java密钥库(JKS)证书,以允许具有管理员或主管角色的用户使用其SSO登录凭证登录到Finesse外部的ECE分区。
如果要将SSO配置为允许具有管理员或主管角色的用户使用其SSO登录凭证登录到Finesse外部的ECE分区,则必须将Java密钥库(JKS)证书转换为公钥证书,并在为ECE在IdP服务器上创建的信赖方信任中对其进行配置。
请咨询您的IT部门以接收JKS证书。

注意:这些步骤适用于使用ADFS作为身份提供程序的系统。其他身份提供程序可以使用不同的方法来配置公钥证书。
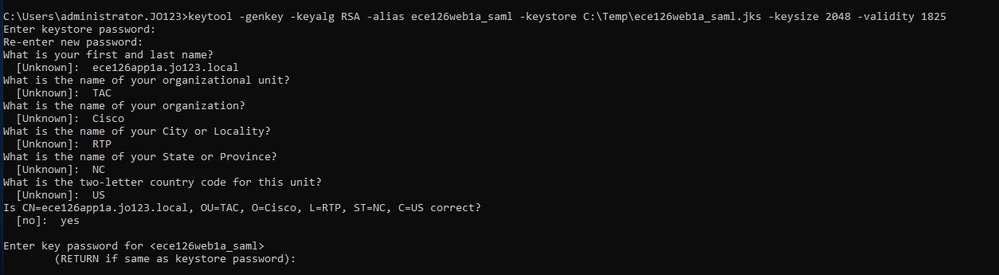
以下示例展示了如何在实验中生成JKS文件:
a.生成JKS:
keytool -genkey -keyalg RSA -alias ece126web1a_saml -keystore C:\Temp\ece126web1a_saml.jks -keysize 2048 -validity 1825

注意:此处输入的密钥库密码、别名和密钥密码用于在ECE的“SSO配置”下配置“服务提供商”配置。
b.导出证书:
此keytool命令将file name为ece126web1a_saml.crt的.crt格式的证书文件导出到C:\Temp目录中。
keytool -exportcert -alias ece126web1a_saml -keystore C:\Temp\ece126web1a_saml.jks -rfc -file C:\Temp\ece126web1a_saml.crt
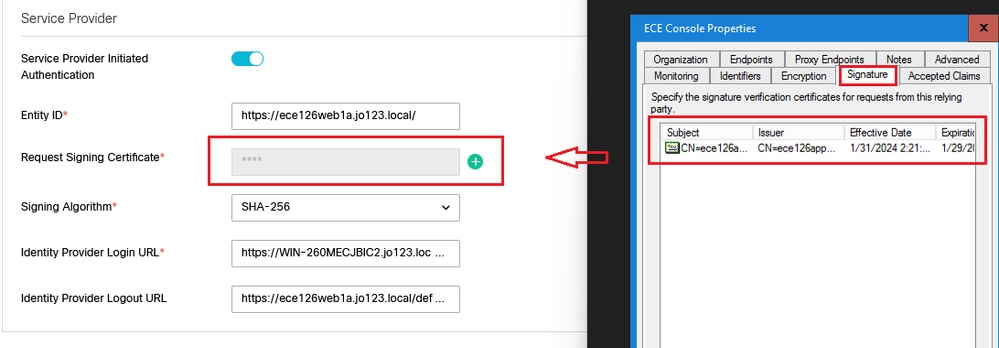
配置身份提供程序
- 在AD FS管理控制台上,选择并右键单击为ECE创建的信赖方信任。
- 打开信任的“属性”窗口,然后在“签名”选项卡下单击“添加”按钮。
- 添加公共证书(在上一步中生成的.crt文件),然后点击OK。
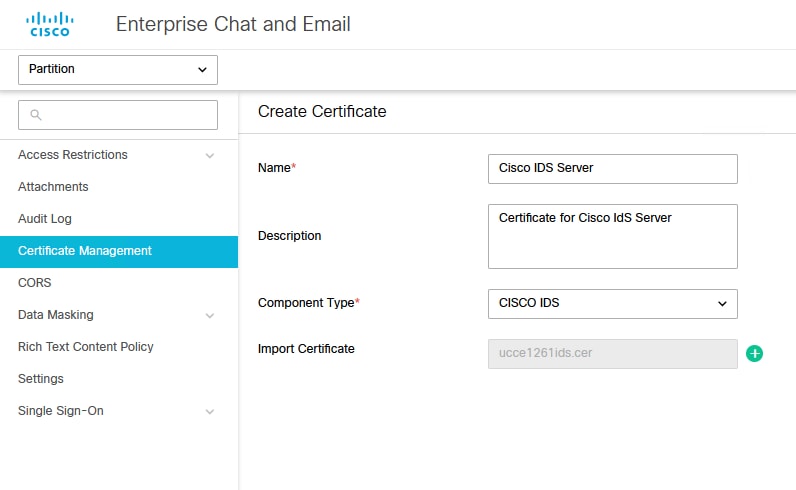
创建和导入证书
在将SSO配置为使用Cisco IDS进行代理的单点登录之前,必须将Cisco IdS服务器的Tomcat证书导入到应用中。
a.在ECE管理控制台的分区级菜单下,单击Security选项,然后从左侧菜单中选择Certificate Management。
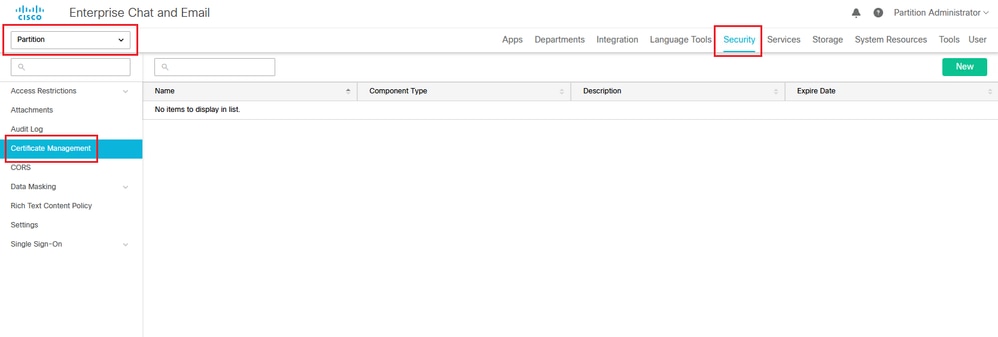
b.在证书管理空间中,单击“新建”按钮并输入相应的详细信息:
- Name:键入证书的名称。
- Description:为证书添加说明。
- Component Type:选择CISCO IDS。
- 导入证书(Import Certificate):要导入证书,请点击搜索和添加(Search and Add)按钮并输入请求的详细信息:
- 证书文件(Certificate file):点击浏览(Browse)按钮并选择您要导入的证书。只能以.pem、.der (BINARY)或.cer/cert格式导入证书。
- Alias Name:为您的证书提供别名。
c.点击“保存”
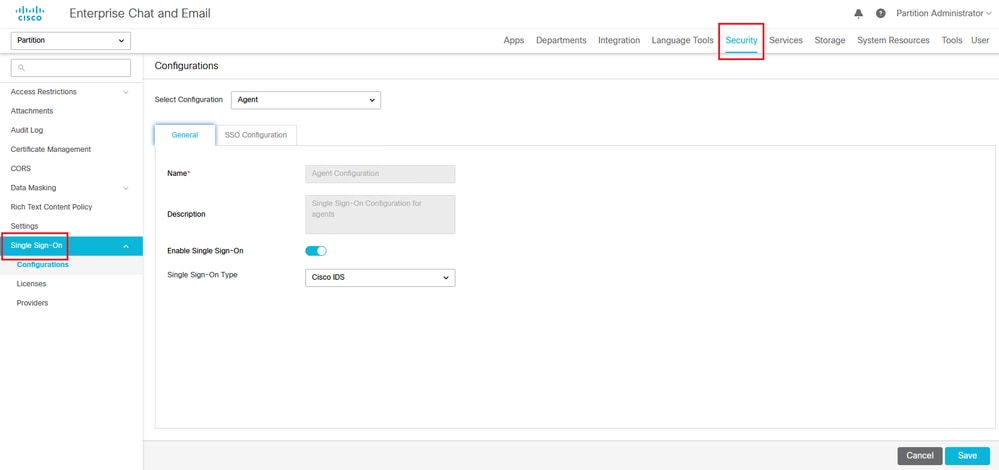
配置代理单一登录
- 在ECE管理控制台的分区级菜单下,单击“Security”选项,然后从左侧菜单中选择Single Sign-On > Configurations。
- 在Select Configuration下拉列表中,选择Agent并在General选项卡下设置配置:
- 启用单点登录:点击切换按钮以启用SSO。
- Single Sign-On Type:选择Cisco IDS。
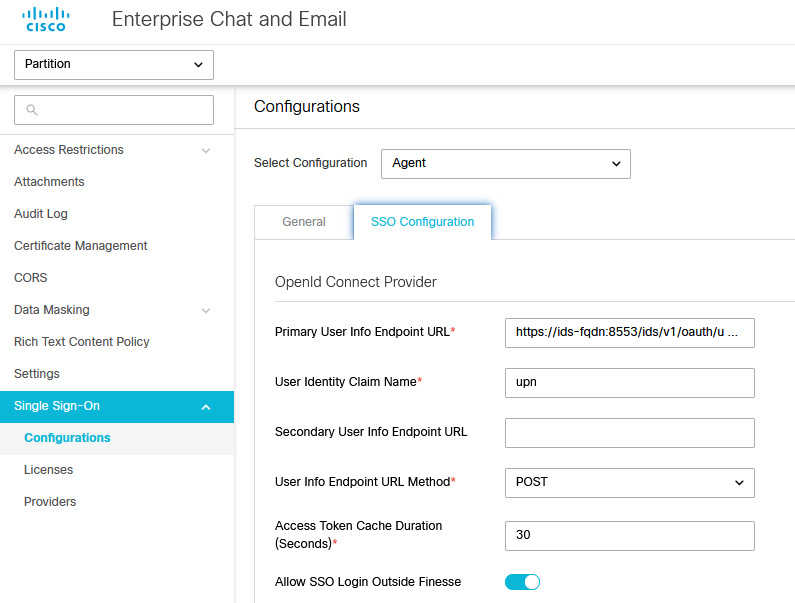
点击SSO配置选项卡并提供配置详细信息:
a. OpenID Connect提供程序
主要用户信息终端URL
- 主Cisco IDS服务器的用户信息终端URL。
- 此URL验证用户令牌/用户信息API。
- 其格式为:https://cisco-ids-1:8553/ids/v1/oauth/userinfo,其中cisco-ids-1表示主Cisco IDS服务器的完全限定域名(FQDN)。
用户身份声明名称
- 由用户信息终端URL返回的声明的名称,用于标识统一或打包CCE中的用户名。
- Unified或Packaged CCE中的声明名称和用户名必须匹配。
- 这是响应承载令牌验证获得的声明之一。
- 如果Unified或Packaged CCE中代理的用户名与User Principal Name匹配,请提供“upn”作为User Identity Claim name字段的值。
- 如果Unified或Packaged CCE中代理的用户名与SAM帐户名称匹配,请提供“sub”作为User Identity Claim name字段的值。
辅助用户信息终端URL (Secondary User Info Endpoint URL)
- Cisco IDS服务器的辅助用户Info Endpoint URL。
- 其格式为:https://cisco-ids-2:8553/ids/v1/oauth/userinfo,其中cisco-ids-2表示辅助Cisco IDS服务器的完全限定域名(FQDN)。
用户信息终端URL方法
- ECE用于对用户信息终端URL进行承载令牌验证调用的HTTP方法。
- 从显示的选项列表中选择POST(此处选择POST以匹配IDS服务器的方法)。
POST:用于发送数据到指定终端上的Cisco IDS服务器的方法。
访问令牌缓存持续时间(秒)
- 必须在ECE中缓存承载令牌的持续时间(秒)。
- 验证调用成功的承载令牌仅存储在缓存中。(最小值:1;最大值:30)
允许SSO在Finesse外部登录
- 如果您希望允许具有管理员或主管角色的用户使用其SSO登录凭证登录Finesse外部的ECE分区,请单击此切换按钮。
- 如果启用,则必须提供“身份提供程序”和“服务提供程序”部分下的信息。
- 这要求您的IdP配置允许共享IdP服务器。
b.身份提供者
实体Id
- IdP服务器的实体ID。

注意:此值必须与AD FS管理控制台中的“联合身份验证服务标识符”值完全匹配。
身份提供程序证书
- 公钥证书。
- 证书必须以“-----BEGIN CERTIFICATE-----”开头,以“-----END CERTIFICATE-----”结尾
- 这是位于AD FS管理控制台>服务>证书>令牌签名中的令牌签名证书。
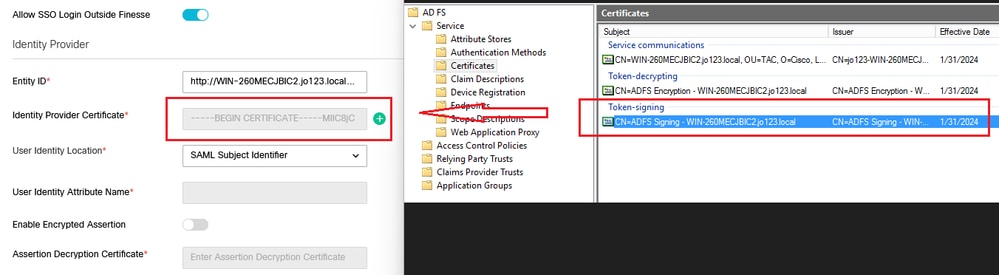
用户身份位置
- 选择SAML Subject Identifier,将证书中的标识位置设置为默认SAML主题标识符,如SAML断言中的主题,如<saml:Subject>中的用户名。
- 选择SAML Attribute以将身份位置分配给证书中的特定属性,例如email.address。在User Identity Attribute Name字段中提供属性。
用户身份属性名称
- 仅当User ID Location值是SAML属性时适用。
- 这可以在SAML断言中调整,并用于为用户身份验证选择其他属性,例如邮件地址。
- 它还可以用于创建具有SAML属性的新用户。
- 例如,如果通过email.address属性中提供的值识别用户,并且提供的电子邮件地址值与系统中的任何用户都不匹配,则会使用提供的SAML属性创建新用户。
启用加密断言(可选)
- 如果您希望通过身份提供者为控制台登录启用加密断言,请点击Toggle按钮将值设置为Enabled。
- 否则,将该值设置为Disabled。
断言解密证书
如果Enable encrypted assertion设置为Enabled,请点击Search and Add按钮,并确认您更改证书的选择。
在Assertion Decryption Certificate窗口中提供详细信息:
- Java Keystore File:提供Java Keystore File的文件路径。此文件为.jks格式,包含系统访问由身份提供程序保护的文件所需的解密密钥。
- Alias Name:解密密钥的唯一标识符。
- 密钥库密码:访问Java密钥库文件所需的密码。
- 密钥密码:访问别名的解密密钥所需的密码。

注意:这需要与AD FS管理控制台上已配置的ECE信赖方信任的“加密”选项卡中的证书匹配。
c.服务提供商
服务提供商发起的身份验证
- 将切换按钮设置为“启用”。
实体Id
- 提供ECE应用程序的外部URL。
请求签名证书
- 需要Java密钥库(JKS)证书才能提供必要的信息。
- 使用步骤11中生成的别名和密钥库/密钥密码上传.jks文件。

注意:这必须与上传到AD FS管理控制台上已配置的ECE信赖方信任的“签名”选项卡的证书匹配。
签名算法
- 设置服务提供商的签名算法。
- 如果使用ADFS,该值必须与“高级”选项卡下为ECE创建的信赖方信任中选择的算法匹配。
标识提供程序登录URL
- SAML身份验证的URL。
- 例如,对于ADFS,应为http://<ADFS>/adfs/ls。
标识提供程序注销URL
- 注销时将用户重定向到的URL。这是可选的,可以是任何URL。
- 例如,在SSO注销后,可以将代理重定向到https://www.cisco.com或任何其他URL。
点击保存
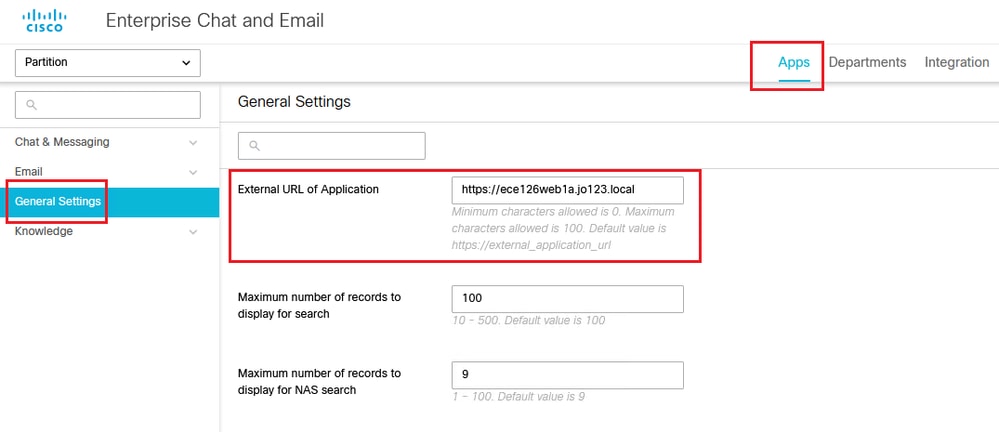
在分区设置中设置Web服务器/LB URL
确保在“Partition settings”下输入正确的Web Server/LB URL >选择Apps选项卡,然后导航到General Settings > External URL of the Application
为分区管理员配置SSO

注意:
- 此步骤仅适用于PCCE。
- 这是用于在CCE管理网络界面https:///cceadmin中访问的ECE小工具。
为分区管理员配置SSO
- 在ECE管理控制台的分区级菜单下,点击Security选项,然后从左侧菜单中选择Single Sign-On > Configurations。
- 在选择配置下拉列表中,选择分区管理员,然后输入配置详细信息:
LDAP URL
- LDAP服务器的URL。
- 这可以是LDAP服务器的域控制器URL(例如,ldap://LDAP_server:389)或全局目录URL(例如,ldap://LDAP_server:3268)。
- 如果ECE配置了LDAP查找,则通过CCE管理控制台访问ECE时,可以自动将分区添加到系统中。
- 但是,在单个林中具有多个域或配置了备用UPN的Active Directory部署中,不得使用具有标准LDAP端口389和636的域控制器URL。
- LDAP集成可以配置为使用端口3268和3269的全局目录URL。

注意:最佳做法是使用全局目录URL。 如果不使用GC,则ApplicationServer日志中的错误如下。
- LDAP身份验证中发生异常<@>
javax.naming.PartialResultException:未处理的连续引用;剩余名称“DC=example,DC=com”
DN属性
- 包含用户登录名的DN的属性。
- 例如,userPrincipalName。
基础
- 为Base指定的值由应用程序用作搜索库。
- Search base是在LDAP目录树中搜索的开始位置。
- 例如,DC=mycompany, DC=com。
用于LDAP搜索的DN
- 如果LDAP系统不允许匿名绑定,请提供在LDAP目录树上具有搜索权限的用户的可分辨名称(DN)。
- 如果LDAP服务器允许匿名绑定,请将此字段留空。
密码
- 如果LDAP系统不允许匿名绑定,请提供在LDAP目录树上具有搜索权限的用户的密码。
- 如果LDAP服务器允许匿名绑定,请将此字段留空。
点击保存
现在即可完成ECE中代理和分区管理员的单点登录配置。
故障排除
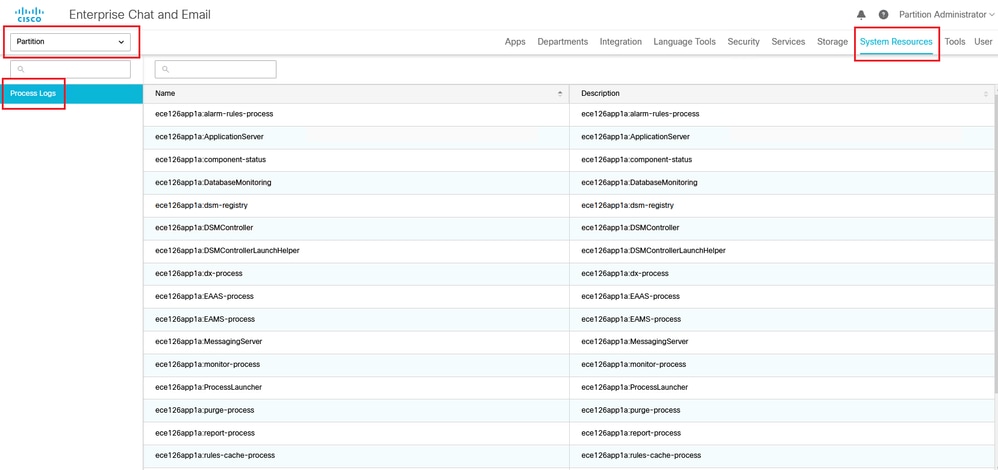
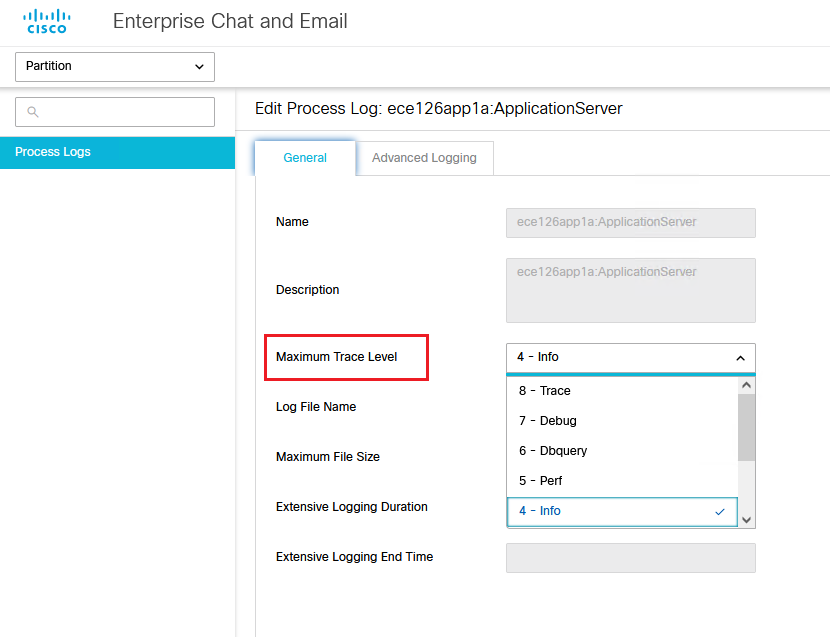
设置跟踪级别
- 在ECE管理控制台的分区级菜单下,单击System Resources选项,然后从左侧菜单中选择Process Logs。
- 从进程列表中选择ApplicationServer进程>从“Maximum Trace Level”下拉菜单设置所需的跟踪级别。

注意:
- 要排除初始设置或重新配置期间的SSO登录错误,请将ApplicationServer进程跟踪设置为级别7。
- 重现错误后,请将跟踪级别重新设置为默认级别4,以避免覆盖日志。
故障排除场景1
Error
- 错误代码:500
- 错误说明:应用程序此时无法登录用户,因为身份提供程序登录失败。
日志分析
- IdP登录失败- <samlp:Status><samlp:StatusCode Value="urn:oasis:names:tc:SAML:2.0:status:Responder" /></samlp:Status>
- 此处,状态“Responder”表示AD FS端存在一些问题-在这种情况下,主要是通过ECE管理控制台(SSO配置>服务提供商)上传的“请求签名证书”,以及通过“签名”选项卡上传到ECE信赖方信任的证书。
- 这是使用Java密钥库文件生成的证书。
unmarshallAndValidateResponse:
2022-09-21 18:18:15.002 GMT+0000 <@> ERROR <@> [392364:qtp1158258131-392364] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:72d5a2a7-5520-4e8a-83a0-bc2b5d87ee38 <@> com.egain.platform.module.security.sso.handler.SAML2_0_Handler <@> unmarshallAndValidateResponse() <@> IdP login failed. Status code is NOT 'Success' in SAML Response token: <samlp:Response ID="_99e9ec67-5c53-43e3-9d53-79afb5fe95ee" Version="2.0" IssueInstant="2022-09-21T18:18:14.640Z" Destination="<fqdn>/system/SAML/SSO/POST.controller" Consent="urn:oasis:names:tc:SAML:2.0:consent:unspecified" InResponseTo="EG_f75b996b-0fe5-4236-a4ad-fa634dcbc6f6" xmlns:samlp="urn:oasis:names:tc:SAML:2.0:protocol"><Issuer xmlns="urn:oasis:names:tc:SAML:2.0:assertion">adfs/adfs/services/trust</Issuer><ds:Signature xmlns:ds="<fqdn>/2000/09/xmldsig#"><ds:SignedInfo><ds:CanonicalizationMethod Algorithm="<fqdn>/2001/10/xml-exc-c14n#" /><ds:SignatureMethod Algorithm="<fqdn>/2001/04/xmldsig-more#rsa-sha256" /><ds:Reference URI="#_99e9ec67-5c53-43e3-9d53-79afb5fe95ee"><ds:Transforms><ds:Transform Algorithm="<fqdn>/2000/09/xmldsig#enveloped-signature" /><ds:Transform Algorithm="<fqdn>/2001/10/xml-exc-c14n#" /></ds:Transforms><ds:DigestMethod Algorithm="<fqdn>/2001/04/xmlenc#sha256" /><ds:DigestValue>gAlphYvLYvUBRdX6WJSFCOZ0Ph+/HB2JHnDxUmbluXg=</ds:DigestValue></ds:Reference></ds:SignedInfo><ds:SignatureValue>HRLRYAL94nIB14/LVlrGpxNyz1ddR/pfCN4pDVTVuBWXJCCpXPHcIVuqWYHKh9gnj/QPqNwZktmKcOZTB2tviOucNhDO5r4DiqEk90R29spAVvlWEsUiVmq+hJOafoDwXk0p+uCXGAJuIsEgOVOtMQrGZSi1zHT6r6hzBb9lC2MhKryey+p34bGHxA2doHSshXpbYhVRjVGUAqpkh614Mb9bfW0fzjgVgxrXQzevRAJBKmoj+nuiOInBISxMD+bjJ1mcTCcnUCQQQ7lYwQZ/v/ux0ht5HelI9VGt90ExwjNiEUXQTzxvqGbAlDDX4K/lEGfIS/JwWo+rWDa4j1IN5Q==</ds:SignatureValue><KeyInfo xmlns="<fqdn>/2000/09/xmldsig#"><ds:X509Data><ds:X509Certificate>MIIC6DCCAdCgAwIBAgIQE/XRfyPrEYpMPM0XB1NU/DANBgkqhkiG9w0BAQsFADAwMS4wLAYDVQQDEyVBREZTIFNpZ25pbmcgLSBhZGZzLm9zZmhlYWx0aGNhcmUub3JnMB4XDTIwMDgxNjA5MjkyNVoXDTIzMDgxNjA5MjkyNVowMDEuMCwGA1UEAxMlQURGUyBTaWduaW5nIC0gYWRmcy5vc2ZoZWFsdGhjYXJlLm9yZzCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAO7LWemQO5VBCOCuXEhzx89HwlhAUyweAIC9RKkEbZGEI4oqI7OKhwuG5IerHo1qM2I08A4bOYZV7rgWD6Kn8MCyn4UsByw0TRjdu2FZQlMzJA1xnfzVhFMAsWPj3wATjpPnHivqzUK1nBLgalc/GgqSOr7dacjCQSngKqDIAJwgrRLZDapEdbI3ZfTsxHugMR5g9eFwpwAsfoizR63EHhd+NRJ2NUhRQoej/WMGhMqJpxxiZQ0vmllZHfw7CRLRPCpkMlALpEFz0DQnozpOMMlz7uEgTuXxFTfdPhA6j5AL1YoF6ZNBo/8+HiPu6+aE0melxEl6AJOghSQY60JsmkECAwEAATANBgkqhkiG9w0BAQsFAAOCAQEAwTl/KRw4cHb615bO3bqWf9YqkMQ40+hGO27Hv/So3vuQFh5b0vzdK35diOAQSjh8RUgeNT3x7CXOGic5qYtXpZVkYsEFWMO8l0O517v576no1IQNtv+rEa3cU3J0NR5U6JfGXtzfTiqu1MFCoGybVZZi9oZeBSiICObO13YBdavZUDrhIRAXenQD0yWtbWKqMMV5gxEhSAn9LAXpctaYPJx4LAw1Q1xvJ52AzyaSm3AxLkfzw0RPF4twCUuX4O+bCFRw+3ibAib1h1eCCItryBNBeIpP7mMnDpZDVJdEjX40pvku80i3c5gxzuVOwak+dd5KzqghxrSUblIdEBWoEg==</ds:X509Certificate></ds:X509Data></KeyInfo></ds:Signature><samlp:Status><samlp:StatusCode Value="urn:oasis:names:tc:SAML:2.0:status:Responder" /></samlp:Status></samlp:Response>. => Check IdP error log at the time of this error. <@>
2022-09-21 18:18:15.002 GMT+0000 <@> INFO <@> [392364:qtp1158258131-392364] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:72d5a2a7-5520-4e8a-83a0-bc2b5d87ee38 <@> com.egain.platform.module.security.sso.admin.SSOAdministrator <@> validateRequestWithAttributes() <@> tokenState: NULL <@>
L10N_USER_STATUS_CODE_ERROR:
2022-09-21 18:18:15.002 GMT+0000 <@> ERROR <@> [392364:qtp1158258131-392364] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:72d5a2a7-5520-4e8a-83a0-bc2b5d87ee38 <@> com.egain.platform.module.security.sso.controller.SSOControllerServlet <@> redirectToApiErrorPage() <@> User SSO: SSOLoginException caught. L10N file path: pl/resourcetype/sso. L10N string: L10N_USER_STATUS_CODE_ERROR <@> - com.egain.platform.module.security.sso.exception.SSOLoginException: null
at com.egain.platform.module.security.sso.handler.SAML2_0_Handler.unmarshallAndValidateResponse(SAML2_0_Handler.java:514) ~[egpl_application_classes.jar:?]
at com.egain.platform.module.security.sso.handler.SAML2_0_Handler.validateReqWithAttributes(SAML2_0_Handler.java:208) ~[egpl_application_classes.jar:?]
at com.egain.platform.module.security.sso.handler.SAML2_0_Handler.validateReqWithAttributes(SAML2_0_Handler.java:163) ~[egpl_application_classes.jar:?]
at com.egain.platform.module.security.sso.handler.OpenIDConnect_Handler.validateReqWithAttributes(OpenIDConnect_Handler.java:441) ~[egpl_application_classes.jar:?]
at com.egain.platform.module.security.sso.admin.SSOAdministrator.validateRequestWithAttributes(SSOAdministrator.java:131) ~[egpl_application_classes.jar:?]
at com.egain.platform.module.security.sso.controller.SSOControllerServlet.doPost(SSOControllerServlet.java:106) ~[egpl_application_classes.jar:?]
.
.
.
.
at java.lang.Thread.run(Thread.java:834) ~[?:?]
errorCode=500&errorString=The application is not able to login the user at this time as Identity Provider login failed:
2022-09-21 18:18:15.003 GMT+0000 <@> DEBUG <@> [392364:qtp1158258131-392364] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:72d5a2a7-5520-4e8a-83a0-bc2b5d87ee38 <@> com.egain.platform.client.util.i18n.L10NUtil <@> getLocalizedMessage(CallerContext, Locale, String, l10nKey, String[]) <@> In method getLocalizedMessage: pl/resourcetype/sso L10N_USER_STATUS_CODE_ERROR null <@>
2022-09-21 18:18:15.003 GMT+0000 <@> DEBUG <@> [392364:qtp1158258131-392364] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:72d5a2a7-5520-4e8a-83a0-bc2b5d87ee38 <@> com.egain.platform.module.security.sso.controller.SSOControllerServlet <@> redirectToApiErrorPage() <@> WS API SSO errorURL => /system/web/view/platform/admin/security/sso/context/errorpage.html?errorCode=500&errorString=The application is not able to login the user at this time as Identity Provider login failed. If the problem persists, please contact your system administrator.&errorKey=L10N_USER_STATUS_CODE_ERROR&locale=en-US <@>
分辨率
- 请参阅“配置代理单一登录-服务提供商”部分中的请求签名证书配置。
- 确保将步骤11中生成的Java Keystore .jks文件上传到ECE管理控制台上的“Request Signing certificate”字段,该字段位于“SSO Configuration”>“Select Configuration 'Agent'”>“SSO Configuration”选项卡>“Service Provider”>“Request Signing certificate”下。
- 确保在ECE信赖方信任的“签名”(Signature)选项卡下上传.crt文件(第12步)。
故障排除场景2
Error
- 错误代码:400
- 错误说明:SAML响应令牌无效:签名验证失败。
日志分析
- 此错误表明ADFS上的“令牌签名证书”和ECE SSO配置上的“身份提供程序证书”之间的证书不匹配。
Entering 'validateSSOCertificate' and validating the saml response against certificate:
2022-10-07 15:27:34.523 GMT+0000 <@> DEBUG <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.security.sso.handler.SAML2_0_Handler <@> validateSSOCertificate() <@> Entering validateSignatureAndCertificate() method.validating the saml response against certificate <@>
2022-10-07 15:27:34.520 GMT+0000 <@> DEBUG <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.sso.util.SSOUtil <@> decodeBase64String() <@> Exiting decodeBase64String() method with retString: <samlp:Response ID="_2e893c54-7a6f-4bdf-bca8-8ae31a4a6074" Version="2.0" IssueInstant="2022-10-07T15:27:32.518Z" Destination="fqdn/system/SAML/SSO/POST.controller" Consent="urn:oasis:names:tc:SAML:2.0:consent:unspecified" InResponseTo="EG_a9ebbc9a-e457-4cac-a22e-bd3e92ad13eb" xmlns:samlp="urn:oasis:names:tc:SAML:2.0:protocol"><Issuer xmlns="urn:oasis:names:tc:SAML:2.0:assertion">adfs/adfs/services/trust</Issuer><samlp:Status><samlp:StatusCode Value="urn:oasis:names:tc:SAML:2.0:status:Success" /></samlp:Status><Assertion ID="_046b645f-7352-4c6b-af3c-3aec8817df54" IssueInstant="2022-10-07T15:27:32.518Z" Version="2.0" xmlns="urn:oasis:names:tc:SAML:2.0:assertion"><Issuer>adfs/adfs/services/trust</Issuer><ds:Signature xmlns:ds="<fqdn/2000/09/xmldsig#"><ds:SignedInfo><ds:CanonicalizationMethod Algorithm="<fqdn/2001/10/xml-exc-c14n#" /><ds:SignatureMethod Algorithm="<fqdn/2001/04/xmldsig-more#rsa-sha256" /><ds:Reference URI="#_046b645f-7352-4c6b-af3c-3aec8817df54"><ds:Transforms><ds:Transform Algorithm="<fqdn/2000/09/xmldsig#enveloped-signature" /><ds:Transform Algorithm="<fqdn/2001/10/xml-exc-c14n#" /></ds:Transforms><ds:DigestMethod Algorithm="<fqdn/2001/04/xmlenc#sha256" /><ds:DigestValue>+++=</ds:DigestValue></ds:Reference></ds:SignedInfo><ds:SignatureValue>...
2022-10-07 15:27:34.521 GMT+0000 <@> DEBUG <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.security.sso.handler.SAML2_0_Handler <@> validateReqWithAttributes() <@> Exiting getDecodedSAMLResponse() method with decodedString: <samlp:Response ID="_2e893c54-7a6f-4bdf-bca8-8ae31a4a6074" Version="2.0" IssueInstant="2022-10-07T15:27:32.518Z" Destination="fqdn/system/SAML/SSO/POST.controller" Consent="urn:oasis:names:tc:SAML:2.0:consent:unspecified" InResponseTo="EG_a9ebbc9a-e457-4cac-a22e-bd3e92ad13eb" xmlns:samlp="urn:oasis:names:tc:SAML:2.0:protocol"><Issuer xmlns="urn:oasis:names:tc:SAML:2.0:assertion">adfs/adfs/services/trust</Issuer><samlp:Status><samlp:StatusCode Value="urn:oasis:names:tc:SAML:2.0:status:Success" /></samlp:Status><Assertion ID="_046b645f-7352-4c6b-af3c-3aec8817df54" IssueInstant="2022-10-07T15:27:32.518Z" Version="2.0" xmlns="urn:oasis:names:tc:SAML:2.0:assertion"><Issuer>adfs/adfs/services/trust</Issuer><ds:Signature xmlns:ds="<fqdn/2000/09/xmldsig#"><ds:SignedInfo><ds:CanonicalizationMethod Algorithm="<fqdn/2001/10/xml-exc-c14n#" /><ds:SignatureMethod Algorithm="<fqdn/2001/04/xmldsig-more#rsa-sha256" /><ds:Reference URI="#_046b645f-7352-4c6b-af3c-3aec8817df54"><ds:Transforms><ds:Transform Algorithm="<fqdn/2000/09/xmldsig#enveloped-signature" /><ds:Transform Algorithm="<fqdn/2001/10/xml-exc-c14n#" /></ds:Transforms><ds:DigestMethod Algorithm="<fqdn/2001/04/xmlenc#sha256" /><ds:DigestValue>+++=</ds:DigestValue></ds:Reference></ds:SignedInfo><ds:SignatureValue>...
2022-10-07 15:27:34.521 GMT+0000 <@> DEBUG <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.security.sso.handler.SAML2_0_Handler <@> unmarshallAndValidateResponse() <@> Entering unmarshallAndValidateResponse() method with base64decodedResponse: <samlp:Response ID="_2e893c54-7a6f-4bdf-bca8-8ae31a4a6074" Version="2.0" IssueInstant="2022-10-07T15:27:32.518Z" Destination="fqdn/system/SAML/SSO/POST.controller" Consent="urn:oasis:names:tc:SAML:2.0:consent:unspecified" InResponseTo="EG_a9ebbc9a-e457-4cac-a22e-bd3e92ad13eb" xmlns:samlp="urn:oasis:names:tc:SAML:2.0:protocol"><Issuer xmlns="urn:oasis:names:tc:SAML:2.0:assertion">adfs/adfs/services/trust</Issuer><samlp:Status><samlp:StatusCode Value="urn:oasis:names:tc:SAML:2.0:status:Success" /></samlp:Status><Assertion ID="_046b645f-7352-4c6b-af3c-3aec8817df54" IssueInstant="2022-10-07T15:27:32.518Z" Version="2.0" xmlns="urn:oasis:names:tc:SAML:2.0:assertion"><Issuer>adfs/adfs/services/trust</Issuer><ds:Signature xmlns:ds="<fqdn/2000/09/xmldsig#"><ds:SignedInfo><ds:CanonicalizationMethod Algorithm="<fqdn/2001/10/xml-exc-c14n#" /><ds:SignatureMethod Algorithm="<fqdn/2001/04/xmldsig-more#rsa-sha256" /><ds:Reference URI="#_046b645f-7352-4c6b-af3c-3aec8817df54"><ds:Transforms><ds:Transform Algorithm="<fqdn/2000/09/xmldsig#enveloped-signature" /><ds:Transform Algorithm="<fqdn/2001/10/xml-exc-c14n#" /></ds:Transforms><ds:DigestMethod Algorithm="<fqdn/2001/04/xmlenc#sha256" /><ds:DigestValue>+++=</ds:DigestValue></ds:Reference></ds:SignedInfo><ds:SignatureValue>...
2022-10-07 15:27:34.521 GMT+0000 <@> DEBUG <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.security.sso.handler.SAML2_0_Handler <@> getRootElement() <@> Entering getRootElement() with responseSAMLString: <samlp:Response ID="_2e893c54-7a6f-4bdf-bca8-8ae31a4a6074" Version="2.0" IssueInstant="2022-10-07T15:27:32.518Z" Destination="fqdn/system/SAML/SSO/POST.controller" Consent="urn:oasis:names:tc:SAML:2.0:consent:unspecified" InResponseTo="EG_a9ebbc9a-e457-4cac-a22e-bd3e92ad13eb" xmlns:samlp="urn:oasis:names:tc:SAML:2.0:protocol"><Issuer xmlns="urn:oasis:names:tc:SAML:2.0:assertion">adfs/adfs/services/trust</Issuer><samlp:Status><samlp:StatusCode Value="urn:oasis:names:tc:SAML:2.0:status:Success" /></samlp:Status><Assertion ID="_046b645f-7352-4c6b-af3c-3aec8817df54" IssueInstant="2022-10-07T15:27:32.518Z" Version="2.0" xmlns="urn:oasis:names:tc:SAML:2.0:assertion"><Issuer>adfs/adfs/services/trust</Issuer><ds:Signature xmlns:ds="<fqdn/2000/09/xmldsig#"><ds:SignedInfo><ds:CanonicalizationMethod Algorithm="<fqdn/2001/10/xml-exc-c14n#" /><ds:SignatureMethod Algorithm="<fqdn/2001/04/xmldsig-more#rsa-sha256" /><ds:Reference URI="#_046b645f-7352-4c6b-af3c-3aec8817df54"><ds:Transforms><ds:Transform Algorithm="<fqdn/2000/09/xmldsig#enveloped-signature" /><ds:Transform Algorithm="<fqdn/2001/10/xml-exc-c14n#" /></ds:Transforms><ds:DigestMethod Algorithm="<fqdn/2001/04/xmlenc#sha256" /><ds:DigestValue>+++=</ds:DigestValue></ds:Reference></ds:SignedInfo><ds:SignatureValue>...
2022-10-07 15:27:34.523 GMT+0000 <@> DEBUG <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.sso.util.SSOUtil <@> loadcertificate() <@> Entering loadcertificate() method with publicCertificateString: ----BEGIN CERTIFICATE-----
.....
-----END CERTIFICATE----- <@>
2022-10-07 15:27:34.523 GMT+0000 <@> INFO <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.sso.util.SSOUtil <@> loadcertificate() <@> cf: java.security.cert.CertificateFactory@10365e4c <@>
Error: Could not parse certificate: java.io.IOException: Incomplete data:
2022-10-07 15:27:34.523 GMT+0000 <@> ERROR <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.sso.util.SSOUtil <@> loadcertificate() <@> Could not parse certificate: java.io.IOException: Incomplete data <@>
2022-10-07 15:27:34.524 GMT+0000 <@> DEBUG <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.sso.util.SSOUtil <@> loadcertificate() <@> Exiting loadcertificate() method with xcert: null <@>
2022-10-07 15:27:34.525 GMT+0000 <@> DEBUG <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.security.sso.handler.SAML2_0_Handler <@> validateSSOCertificate() <@> certificate: null <@>
2022-10-07 15:27:34.525 GMT+0000 <@> DEBUG <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.security.sso.handler.SAML2_0_Handler <@> validateSSOCertificate() <@> Exiting validateSignatureAndCertificate() with retBoolean: false <@>
Signature validation failed:
2022-10-07 15:27:34.525 GMT+0000 <@> ERROR <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.security.sso.handler.SAML2_0_Handler <@> unmarshallAndValidateResponse() <@> Signature validation failed. SAML Response: <samlp:Response ID="_2e893c54-7a6f-4bdf-bca8-8ae31a4a6074" Version="2.0" IssueInstant="2022-10-07T15:27:32.518Z" Destination="fqdn/system/SAML/SSO/POST.controller" Consent="urn:oasis:names:tc:SAML:2.0:consent:unspecified" InResponseTo="EG_a9ebbc9a-e457-4cac-a22e-bd3e92ad13eb" xmlns:samlp="urn:oasis:names:tc:SAML:2.0:protocol"><Issuer xmlns="urn:oasis:names:tc:SAML:2.0:assertion">adfs/adfs/services/trust</Issuer><samlp:Status><samlp:StatusCode Value="urn:oasis:names:tc:SAML:2.0:status:Success" /></samlp:Status><Assertion ID="_046b645f-7352-4c6b-af3c-3aec8817df54" IssueInstant="2022-10-07T15:27:32.518Z" Version="2.0" xmlns="urn:oasis:names:tc:SAML:2.0:assertion"><Issuer>adfs/adfs/services/trust</Issuer><ds:Signature xmlns:ds="<fqdn/2000/09/xmldsig#"><ds:SignedInfo><ds:CanonicalizationMethod Algorithm="<fqdn/2001/10/xml-exc-c14n#" /><ds:SignatureMethod Algorithm="<fqdn/2001/04/xmldsig-more#rsa-sha256" /><ds:Reference URI="#_046b645f-7352-4c6b-af3c-3aec8817df54"><ds:Transforms><ds:Transform Algorithm="<fqdn/2000/09/xmldsig#enveloped-signature" /><ds:Transform Algorithm="<fqdn/2001/10/xml-exc-c14n#" /></ds:Transforms><ds:DigestMethod Algorithm="<fqdn/2001/04/xmlenc#sha256" /><ds:DigestValue>+++=</ds:DigestValue></ds:Reference></ds:SignedInfo><ds:SignatureValue>...
2022-10-07 15:27:34.525 GMT+0000 <@> INFO <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.security.sso.admin.SSOAdministrator <@> validateRequestWithAttributes() <@> tokenState: NULL <@>
2022-10-07 15:27:34.525 GMT+0000 <@> ERROR <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.module.security.sso.controller.SSOControllerServlet <@> redirectToApiErrorPage() <@> User SSO: SSOLoginException caught. L10N file path: pl/resourcetype/sso. L10N string: L10N_USER_SIGNATURE_INVALID <@>
2022-10-07 15:27:34.525 GMT+0000 <@> DEBUG <@> [537838:qtp1158258131-537838] <@> ProcessId:3272 <@> PID:1 <@> UID:12 <@> UserSessionId:a5a413c1-24a0-aaaa-bed2-83b50f1a9915 <@> com.egain.platform.client.util.i18n.L10NUtil <@> getLocalizedMessage(CallerContext, Locale, String, l10nKey, String[]) <@> In method getLocalizedMessage: pl/resourcetype/sso L10N_USER_SIGNATURE_INVALID null <@>
分辨率
- 日志代码片段中看到的错误“无法解析证书:java.io.IO异常:数据不完整”表明“身份提供程序证书”内容未正确输入
- 要解决此问题:在AS FS Management > AD FS > Service > Certificates > Token-Signing > Export this certificate > open in a text editor > copy all contents > paste under 'Identity provider certificate' fixed in the SSO configuration > Save。
- 请参阅“配置代理单一登录-身份提供程序”部分中的“身份提供程序证书”配置(步骤15)。
故障排除场景3
Error
- 错误代码:401-114
- 错误说明:在SAML属性中找不到用户身份。
日志分析
getSSODataFromSAMLToken:
2024-02-01 01:44:32.081 GMT+0000 <@> ERROR <@> [1220:qtp815320891-1220] <@> ProcessId:7716 <@> PID:1 <@> UID:12 <@> UserSessionId: <@> ClientIP: <@> com.egain.platform.module.security.sso.handler.SAML2_0_Handler <@> getSSODataFromSAMLToken() <@> User identity not found in SAML_ATTRIBUTE <@>
2024-02-01 01:44:32.081 GMT+0000 <@> TRACE <@> [1220:qtp815320891-1220] <@> ProcessId:7716 <@> PID:1 <@> UID:12 <@> UserSessionId: <@> ClientIP: <@> com.egain.platform.module.security.sso.controller.SSOControllerServlet <@> redirectToApiErrorPage() <@> Entering redirectToApiErrorPage() <@>
L10N_USER_IDENTIFIER_NOT_FOUND_IN_ATTRIBUTE:
2024-02-01 01:44:32.081 GMT+0000 <@> ERROR <@> [1220:qtp815320891-1220] <@> ProcessId:7716 <@> PID:1 <@> UID:12 <@> UserSessionId: <@> ClientIP: <@> com.egain.platform.module.security.sso.controller.SSOControllerServlet <@> redirectToApiErrorPage() <@> User SSO: SSOLoginException caught. L10N file path: pl/resourcetype/sso. L10N string: L10N_USER_IDENTIFIER_NOT_FOUND_IN_ATTRIBUTE. Dynamic strings: upn <@>
com.egain.platform.module.security.sso.exception.SSOLoginException: null
at com.egain.platform.module.security.sso.handler.SAML2_0_Handler.getSSODataFromSAMLToken(SAML2_0_Handler.java:762) ~[egpl_application_classes.jar:?]
at com.egain.platform.module.security.sso.handler.SAML2_0_Handler.unmarshallAndValidateResponse(SAML2_0_Handler.java:604) ~[egpl_application_classes.jar:?]
at com.egain.platform.module.security.sso.handler.SAML2_0_Handler.validateReqWithAttributes(SAML2_0_Handler.java:208) ~[egpl_application_classes.jar:?]
at com.egain.platform.module.security.sso.handler.SAML2_0_Handler.validateReqWithAttributes(SAML2_0_Handler.java:163) ~[egpl_application_classes.jar:?]
at com.egain.platform.module.security.sso.handler.OpenIDConnect_Handler.validateReqWithAttributes(OpenIDConnect_Handler.java:445) ~[egpl_application_classes.jar:?]
at com.egain.platform.module.security.sso.admin.SSOAdministrator.validateRequestWithAttributes(SSOAdministrator.java:131) ~[egpl_application_classes.jar:?]
at com.egain.platform.module.security.sso.controller.SSOControllerServlet.doPost(SSOControllerServlet.java:113) ~[egpl_application_classes.jar:?]
.
.
.
at java.lang.Thread.run(Thread.java:830) [?:?]
errorCode=401-114&errorString=User Identity not found in SAML attribute: 'upn':
2024-02-01 01:44:32.083 GMT+0000 <@> DEBUG <@> [1220:qtp815320891-1220] <@> ProcessId:7716 <@> PID:1 <@> UID:12 <@> UserSessionId: <@> ClientIP: <@> com.egain.platform.module.security.sso.controller.SSOControllerServlet <@> redirectToApiErrorPage() <@> WS API SSO errorURL => /system/web/view/platform/admin/security/sso/context/errorpage.html?errorCode=401-114&errorString=User Identity not found in SAML attribute: 'upn'.&errorKey=L10N_USER_IDENTIFIER_NOT_FOUND_IN_ATTRIBUTE&locale=en-US <@>
2024-02-01 01:44:32.083 GMT+0000 <@> TRACE <@> [1220:qtp815320891-1220] <@> ProcessId:7716 <@> PID:1 <@> UID:12 <@> UserSessionId: <@> ClientIP: <@> com.egain.platform.module.security.sso.controller.SSOControllerServlet <@> redirectToApiErrorPage() <@> Exiting redirectToApiErrorPage() <@>
分辨率
- 此错误表示“用户身份位置”(User Identity Location)和“用户身份属性名称”(User Identity Attribute Name)字段中存在配置问题/不匹配。
- 在ECE管理控制台中的“用户身份位置”和“用户身份属性名称”检查并更正,在“选择配置”下拉菜单中的“单一登录”>“配置”下,选择“代理”>“SSO配置”选项卡>“标识提供程序”(第15步)。
相关信息
这些是您在开始安装或整合欧洲经委会之前必须仔细审查的重要文件。这不是一份欧洲经委会文件的综合清单。

注意:
- 大多数欧洲经委会文件有两个版本。请确保下载并使用适用于PCCE的版本。文档标题在版本号后为Packaged Contact Center Enterprise或(用于PCCE)或(用于UCCE和PCCE)。
- 在安装、升级或集成之前,确保您查看思科企业聊天和电子邮件文档的开始页面以了解任何更新。
- https://www.cisco.com/c/en/us/support/customer-collaboration/cisco-enterprise-chat-email/series.html
ECE版本12.6(1)
修订历史记录
| 版本 | 发布日期 | 备注 |
|---|---|---|
1.0 |
14-Feb-2024 |
初始版本 |
 反馈
反馈