将ASA配置为使用基于多证书身份验证的AnyConnect客户端的SSL网关
下载选项
非歧视性语言
此产品的文档集力求使用非歧视性语言。在本文档集中,非歧视性语言是指不隐含针对年龄、残障、性别、种族身份、族群身份、性取向、社会经济地位和交叉性的歧视的语言。由于产品软件的用户界面中使用的硬编码语言、基于 RFP 文档使用的语言或引用的第三方产品使用的语言,文档中可能无法确保完全使用非歧视性语言。 深入了解思科如何使用包容性语言。
关于此翻译
思科采用人工翻译与机器翻译相结合的方式将此文档翻译成不同语言,希望全球的用户都能通过各自的语言得到支持性的内容。 请注意:即使是最好的机器翻译,其准确度也不及专业翻译人员的水平。 Cisco Systems, Inc. 对于翻译的准确性不承担任何责任,并建议您总是参考英文原始文档(已提供链接)。
目录
简介
本文档介绍如何将自适应安全设备(ASA)配置为使用基于多证书身份验证的Cisco AnyConnect安全移动客户端的安全套接字层(SSL)网关。
先决条件
要求
Cisco 建议您了解以下主题:
- ASA CLI配置和SSL VPN配置的基础知识
- X509证书的基础知识
使用的组件
本文档中的信息基于以下软件版本:
- 思科自适应安全设备(ASA)软件9.7(1)版及更高版本
- Windows 10及Cisco AnyConnect安全移动客户端4.4
注意:从思科软件下载(仅限注册客户)下载AnyConnect VPN客户端软件包(anyconnect-win*.pkg)。将 AnyConnect VPN Client 复制到 ASA 的闪存中以供远程用户计算机下载,以便建立与 ASA 的 SSL VPN 连接。有关 ASA 配置指南的详细信息,请参阅安装 AnyConnect 客户端部分。
本文档中的信息都是基于特定实验室环境中的设备编写的。本文档中使用的所有设备最初均采用原始(默认)配置。如果您使用的是真实网络,请确保您已经了解所有命令的潜在影响。
背景信息
在软件版本9.7(1)之前,ASA支持基于单个证书的身份验证,这意味着对于单个连接尝试,可以对用户或计算机进行身份验证,但不能对两者同时进行身份验证。
基于多证书的身份验证使能够让ASA验证计算机或设备证书,以确保设备是公司颁发的设备,此外还能对用户的身份证书进行身份验证以允许VPN访问。
限制
- 多个证书身份验证当前将证书数量限制为正好两个。
- AnyConnect客户端必须表示支持多证书身份验证。否则,网关使用一种传统身份验证方法或连接失败。AnyConnect版本4.4.04030或更高版本支持基于多证书的身份验证。
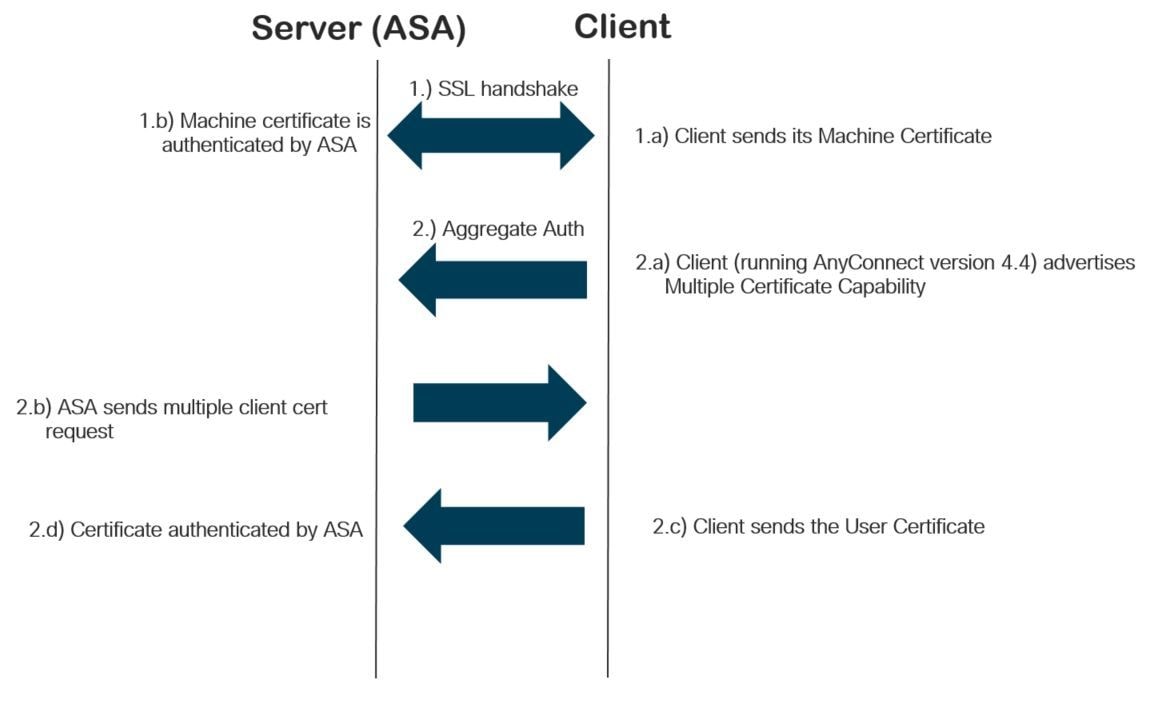
- 对于Windows平台,在初始SSL握手期间发送计算机证书,随后在聚合身份验证协议下发送用户证书。不支持来自Windows计算机存储区的两个证书。
- 多证书身份验证忽略XML配置文件下的Enable automatic Certificate Selection首选项,这意味着客户端将尝试所有组合以验证两个证书,直到失败。这可能在Anyconnect尝试连接时造成相当长的延迟。因此,建议在客户端计算机上存在多个用户/计算机证书的情况下使用证书匹配。
- Anyconnect SSL VPN仅支持基于RSA的证书。
- 在聚合身份验证期间,仅支持基于SHA256、SHA384和SHA512的证书。
Windows v/s非Windows平台上的证书选择
Windows上的AnyConnect区分从计算机存储区(只能由特权进程访问)和用户存储区(只能由登录用户拥有的进程访问)检索的证书。 在非Windows平台上,AnyConnect没有这样的区别。
ASA可以根据收到的证书的实际类型,选择实施由ASA管理员配置的连接策略。 对于Windows,类型可以是:
- 一台机器和一个用户,或者
- 两个用户。
对于非Windows平台,指示始终为两个用户证书。
多证书身份验证的连接流
配置
通过ASDM配置多证书身份验证
本节介绍如何将Cisco ASA配置为带有多证书身份验证的AnyConnect客户端的SSL网关。
通过ASDM完成以下步骤,以设置Anyconnect客户端进行多证书身份验证:
步骤1:在ASA上安装用户和计算机证书的CA证书。
有关证书安装的信息,请参阅配置ASA:SSL数字证书安装和续订
第二步:导航到Configuration > Remote Access > Group Policy并配置组策略。

第三步: 配置新的连接配置文件,并选择Authentication Method作为多个证书,并选择第1步中创建的组策略。

第四步:有关其他详细配置,请参阅VPN客户端和AnyConnect客户端访问本地LAN配置示例
通过CLI配置ASA进行多证书身份验证
注意:要获取有关本部分中所使用命令的更多信息,可使用命令查找工具(仅限已注册客户)。
ASA Version 9.7(1)
!
hostname GCE-ASA
!
! Configure the VPN Pool
ip local pool ANYCONNECT-POOL 192.168.100.1-192.168.100.254 mask 255.255.255.0
!
interface GigabitEthernet0/0
nameif outside
security-level 100
ip address 10.197.223.81 255.255.254.0
!
interface GigabitEthernet0/1
nameif inside
security-level 100
ip address 192.168.1.1 255.255.255.0
!
! Configure Objects
object network obj-AnyConnect_pool
subnet 192.168.100.0 255.255.255.0
object network obj-Local_Lan
subnet 192.168.1.0 255.255.255.0
!
! Configure Split-tunnel access-list
access-list split standard permit 192.168.1.0 255.255.255.0
!
! Configure Nat-Exemption for VPN traffic
nat (inside,outside) source static obj-Local_Lan obj-Local_Lan destination static obj-AnyConnect_pool obj-AnyConnect_pool no-proxy-arp route-lookup
!
! TrustPoint for User CA certificate
crypto ca trustpoint UserCA
enrollment terminal
crl configure
!
! Trustpoint for Machine CA certificate
crypto ca trustpoint MachineCA
enrollment terminal
crl configure
!
!
crypto ca certificate chain UserCA
certificate ca 00ea473dc301c2fdc7
30820385 3082026d a0030201 02020900 ea473dc3 01c2fdc7 300d0609 2a864886
<snip>
3d57bea7 3e30c8f0 f391bab4 855562fd 8e21891f 4acb6a46 281af1f2 20eb0592
012d7d99 e87f6742 d5
quit
crypto ca certificate chain MachineCA
certificate ca 00ba27b1f331aea6fc
30820399 30820281 a0030201 02020900 ba27b1f3 31aea6fc 300d0609 2a864886
f70d0101 0b050030 63310b30 09060355 04061302 494e3112 30100603 5504080c
<snip>
2c214c7a 79eb8651 6ad1eabd ae1ffbba d0750f3e 81ce5132 b5546f93 2c0d6ccf
606add30 2a73b927 7f4a73e5 2451a385 d9a96b50 6ebeba66 fc2e496b fa
quit
!
! Enable AnyConnect
webvpn
enable outside
anyconnect image disk0:/anyconnect-win-4.4.00243-webdeploy-k9.pkg 2
anyconnect enable
tunnel-group-list enable
!
! Configure Group-Policy
group-policy Grouppolicy-MCA internal
group-policy Grouppolicy-MCA attributes
vpn-tunnel-protocol ssl-client
split-tunnel-policy tunnelspecified
split-tunnel-network-list value split
!
! Configure Tunnel-Group
tunnel-group ANYCONNECT-MCA type remote-access
tunnel-group ANYCONNECT-MCA general-attributes
address-pool ANYCONNECT-POOL
default-group-policy Grouppolicy-MCA
tunnel-group ANYCONNECT-MCA webvpn-attributes
authentication multiple-certificate
group-alias ANYCONNECT-MCA enable
group-url https://10.197.223.81/MCA enable
验证
使用本部分可确认配置能否正常运行。
注意:输出解释器工具(仅限注册客户)支持某些show命令。使用输出解释器工具来查看 show 命令输出的分析。
通过CLI查看ASA上安装的证书
show crypto ca certificate
GCE-ASA(config)# show crypto ca certificate
CA Certificate
Status: Available
Certificate Serial Number: 00ea473dc301c2fdc7
Certificate Usage: General Purpose
Public Key Type: RSA (2048 bits)
Signature Algorithm: SHA256 with RSA Encryption
Issuer Name:
cn=UserCA.cisco.com
o=Cisco
l=Dallas
st=Texas
c=IN
Subject Name:
cn=UserCA.cisco.com
o=Cisco
l=Dallas
st=Texas
c=IN
Validity Date:
start date: 15:40:28 UTC Sep 30 2017
enddate: 15:40:28 UTC Jul202020
Storage: config
Associated Trustpoints: UserCA
CA Certificate
Status: Available
Certificate Serial Number: 00ba27b1f331aea6fc
Certificate Usage: General Purpose
Public Key Type: RSA (2048 bits)
Signature Algorithm: SHA256 with RSA Encryption
Issuer Name:
cn=MachineCA.cisco.com
o=Cisco
l=Bangalore
st=Karnataka
c=IN
Subject Name:
cn=MachineCA.cisco.com
o=Cisco
l=Bangalore
st=Karnataka
c=IN
Validity Date:
start date: 15:29:23 UTC Sep 30 2017
enddate: 15:29:23 UTC Jul202020
Storage: config
Associated Trustpoints: MachineCA
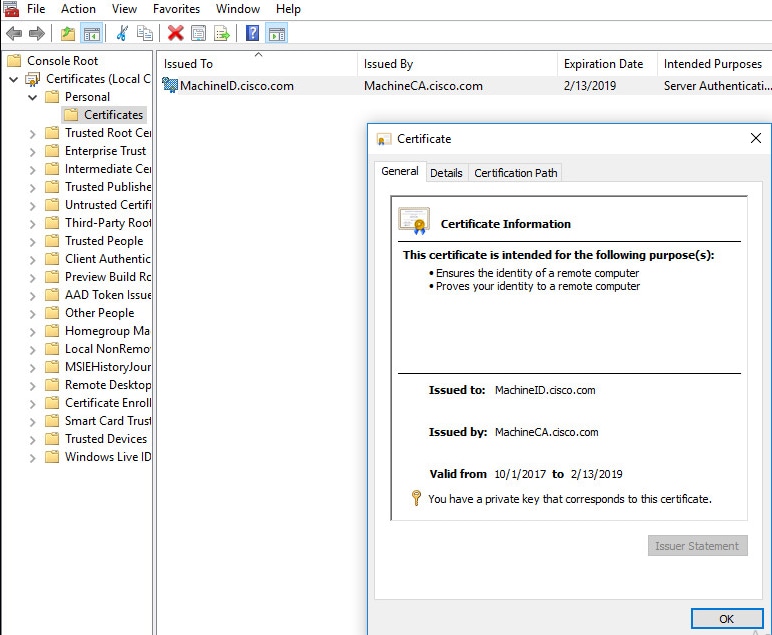
查看客户端上安装的证书
要验证安装,请使用证书管理器(certmgr.msc):
计算机证书
用户证书

执行以下命令以验证连接:
GCE-ASA# sh vpn-sessiondb detail anyconnect
Session Type: AnyConnect Detailed
Username : MachineID.cisco.com Index : 296
Assigned IP : 192.168.100.1 Public IP : 10.197.223.235
Protocol : AnyConnect-Parent SSL-Tunnel DTLS-Tunnel
License : AnyConnect Premium
Encryption : AnyConnect-Parent: (1)none SSL-Tunnel: (1)AES128 DTLS-Tunnel: (1)AES256
Hashing : AnyConnect-Parent: (1)none SSL-Tunnel: (1)SHA1 DTLS-Tunnel: (1)SHA1
Bytes Tx : 11542 Bytes Rx : 2097
Pkts Tx : 8 Pkts Rx : 29
Pkts Tx Drop : 0 Pkts Rx Drop : 0
Group Policy : Grouppolicy-MCA Tunnel Group : ANYCONNECT-MCA
Login Time : 22:26:27 UTC Sun Oct 1 2017
Duration : 0h:00m:21s
Inactivity : 0h:00m:00s
VLAN Mapping : N/A VLAN : none
Audt Sess ID : 0ac5df510012800059d16b93
Security Grp : none
AnyConnect-Parent Tunnels: 1
SSL-Tunnel Tunnels: 1
DTLS-Tunnel Tunnels: 1
AnyConnect-Parent:
Tunnel ID : 296.1
Public IP : 10.197.223.235
Encryption : none Hashing : none
TCP Src Port : 51609 TCP Dst Port : 443
Auth Mode : Multiple-certificate
Idle Time Out: 30 Minutes Idle TO Left : 29 Minutes
Client OS : win
Client OS Ver: 10.0.14393
Client Type : AnyConnect
Client Ver : Cisco AnyConnect VPN Agent for Windows 4.4.01054
Bytes Tx : 5771 Bytes Rx : 0
Pkts Tx : 4 Pkts Rx : 0
Pkts Tx Drop : 0 Pkts Rx Drop : 0
SSL-Tunnel:
Tunnel ID : 296.2
Assigned IP : 192.168.100.1 Public IP : 10.197.223.235
Encryption : AES128 Hashing : SHA1
Ciphersuite : AES128-SHA
Encapsulation: TLSv1.2 TCP Src Port : 51612
TCP Dst Port : 443 Auth Mode : Multiple-certificate
Idle Time Out: 30 Minutes Idle TO Left : 29 Minutes
Client OS : Windows
Client Type : SSL VPN Client
Client Ver : Cisco AnyConnect VPN Agent for Windows 4.4.01054
Bytes Tx : 5771 Bytes Rx : 446
Pkts Tx : 4 Pkts Rx : 5
Pkts Tx Drop : 0 Pkts Rx Drop : 0
DTLS-Tunnel:
Tunnel ID : 296.3
Assigned IP : 192.168.100.1 Public IP : 10.197.223.235
Encryption : AES256 Hashing : SHA1
Ciphersuite : AES256-SHA
Encapsulation: DTLSv1.0 UDP Src Port : 63385
UDP Dst Port : 443 Auth Mode : Multiple-certificate
Idle Time Out: 30 Minutes Idle TO Left : 29 Minutes
Client OS : Windows
Client Type : DTLS VPN Client
Client Ver : Cisco AnyConnect VPN Agent for Windows 4.4.01054
Bytes Tx : 0 Bytes Rx : 1651
Pkts Tx : 0 Pkts Rx : 24
Pkts Tx Drop : 0 Pkts Rx Drop : 0
故障排除
本部分提供可用于对配置进行故障排除的信息。
注意:使用debug命令之前,请参阅有关Debug命令的重要信息。
注意:在ASA上,您可以设置各种调试级别;默认情况下,使用级别1。如果更改调试级别,调试的冗余可能会增加。请谨慎执行此操作,尤其是在生产环境中。
- debug crypto ca messages 127
- Debug crypto ca transaction 127
CRYPTO_PKI: Begin sorted cert chain ---------Certificate--------: Serial: 00B6D609E1D68B9334 Subject: cn=MachineID.cisco.com,ou=Cisco,l=Bangalore,st=Karnataka,c=IN Issuer: cn=MachineCA.cisco.com,o=Cisco,l=Bangalore,st=Karnataka,c=IN CRYPTO_PKI: End sorted cert chain CRYPTO_PKI: Cert chain pre-processing: List size is 1, trustpool is not in use CRYPTO_PKI: List pruning is not necessary. CRYPTO_PKI: Sorted chain size is: 1 CRYPTO_PKI: Found ID cert. serial number: 00B6D609E1D68B9334, subject name: cn=MachineID.cisco.com,ou=Cisco,l=Bangalore,st=Karnataka,c=IN CRYPTO_PKI: Verifying certificate with serial number: 00B6D609E1D68B9334, subject name: cn=MachineID.cisco.com,ou=Cisco,l=Bangalore,st=Karnataka,c=IN, issuer_name: cn=MachineCA.cisco.com,o=Cisco,l=Bangalore,st=Karnataka,c=IN, signature alg: SHA256/RSA. CRYPTO_PKI(Cert Lookup) issuer="cn=MachineCA.cisco.com,o=Cisco,l=Bangalore,st=Karnataka,c=IN" serial number=00 b6 d6 09 e1 d6 8b 93 34 | ........4 CRYPTO_PKI: valid cert with warning. CRYPTO_PKI: valid cert status. CRYPTO_PKI: Begin sorted cert chain ---------Certificate--------: Serial: 00B6D609E1D68B9334 Subject: cn=MachineID.cisco.com,ou=Cisco,l=Bangalore,st=Karnataka,c=IN Issuer: cn=MachineCA.cisco.com,o=Cisco,l=Bangalore,st=Karnataka,c=IN CRYPTO_PKI: End sorted cert chain CRYPTO_PKI: Cert chain pre-processing: List size is 1, trustpool is not in use CRYPTO_PKI: List pruning is not necessary. CRYPTO_PKI: Sorted chain size is: 1 CRYPTO_PKI: Found ID cert. serial number: 00B6D609E1D68B9334, subject name: cn=MachineID.cisco.com,ou=Cisco,l=Bangalore,st=Karnataka,c=IN CRYPTO_PKI: Verifying certificate with serial number: 00B6D609E1D68B9334, subject name: cn=MachineID.cisco.com,ou=Cisco,l=Bangalore,st=Karnataka,c=IN, issuer_name: cn=MachineCA.cisco.com,o=Cisco,l=Bangalore,st=Karnataka,c=IN, signature alg: SHA256/RSA. CRYPTO_PKI(Cert Lookup) issuer="cn=MachineCA.cisco.com,o=Cisco,l=Bangalore,st=Karnataka,c=IN" serial number=00 b6 d6 09 e1 d6 8b 93 34 | ........4 CRYPTO_PKI: valid cert with warning. CRYPTO_PKI: valid cert status. CRYPTO_PKI: Begin sorted cert chain ---------Certificate--------: Serial: 00A5A42E24A345E11A Subject: cn=UserID.cisco.com,ou=TAC,o=Cisco,l=Dallas,st=Texas,c=IN Issuer: cn=UserCA.cisco.com,o=Cisco,l=Dallas,st=Texas,c=IN CRYPTO_PKI: End sorted cert chain CRYPTO_PKI: Cert chain pre-processing: List size is 1, trustpool is not in use CRYPTO_PKI: List pruning is not necessary. CRYPTO_PKI: Sorted chain size is: 1 CRYPTO_PKI: Found ID cert. serial number: 00A5A42E24A345E11A, subject name: cn=UserID.cisco.com,ou=TAC,o=Cisco,l=Dallas,st=Texas,c=IN CRYPTO_PKI: Verifying certificate with serial number: 00A5A42E24A345E11A, subject name: cn=UserID.cisco.com,ou=TAC,o=Cisco,l=Dallas,st=Texas,c=IN, issuer_name: cn=UserCA.cisco.com,o=Cisco,l=Dallas,st=Texas,c=IN, signature alg: SHA256/RSA. CRYPTO_PKI(Cert Lookup) issuer="cn=UserCA.cisco.com,o=Cisco,l=Dallas,st=Texas,c=IN" serial number=00 a5 a4 2e 24 a3 45 e1 1a | ....$.E.. CRYPTO_PKI: valid cert with warning. CRYPTO_PKI: valid cert status.
- Debug aggregate-auth xml 127
Received XML message below from the client <?xml version="1.0" encoding="UTF-8"?> <config-auth client="vpn" type="init" aggregate-auth-version="2"> <version who="vpn">4.4.01054</version> <device-id device-type="VMware, Inc. VMware Virtual Platform" platform-version="10.0.14393 #snip# win</device-id> <mac-address-list> <mac-address>00-0c-29-e4-f5-bd</mac-address></mac-address-list> <group-select>ANYCONNECT-MCA</group-select> <group-access>https://10.197.223.81/MCA</group-access> <capabilities> <auth-method>single-sign-on</auth-method> <auth-method>multiple-cert</auth-method></capabilities> </config-auth> Generated XML message below <?xml version="1.0" encoding="UTF-8"?> <config-auth client="vpn" type="auth-request" aggregate-auth-version="2"> <opaque is-for="sg"> <tunnel-group>ANYCONNECT-MCA</tunnel-group> <aggauth-handle>136775778</aggauth-handle> <auth-method>multiple-cert</auth-method> <auth-method>single-sign-on</auth-method> <config-hash>1506879881148</config-hash> </opaque> <multiple-client-cert-request> <hash-algorithm>sha256</hash-algorithm> <hash-algorithm>sha384</hash-algorithm> <hash-algorithm>sha512</hash-algorithm> </multiple-client-cert-request> <random>FA4003BD87436B227####snip####C138A08FF724F0100015B863F750914839EE79C86DFE8F0B9A0199E2</random> </config-auth>
Received XML message below from the client
<?xml version="1.0" encoding="UTF-8"?>
<config-auth client="vpn" type="auth-reply" aggregate-auth-version="2">
<version who="vpn">4.4.01054</version>
<device-id device-type="VMware, Inc. VMware Virtual Platform" platform-version="10.0.14393 ##snip## win</device-id>
<mac-address-list>
<mac-address>00-0c-29-e4-f5-bd</mac-address></mac-address-list>
<session-token></session-token>
<session-id></session-id>
<opaque is-for="sg">
<tunnel-group>ANYCONNECT-MCA</tunnel-group>
<aggauth-handle>608423386</aggauth-handle>
<auth-method>multiple-cert</auth-method>
<auth-method>single-sign-on</auth-method>
<config-hash>1506879881148</config-hash></opaque>
<auth>
<client-cert-chain cert-store="1M">
<client-cert-sent-via-protocol></client-cert-sent-via-protocol></client-cert-chain>
<client-cert-chain cert-store="1U">
<client-cert cert-format="pkcs7">MIIG+AYJKoZIhvcNAQcCoIIG6TCCBuU
yTCCAzwwggIkAgkApaQuJKNF4RowDQYJKoZIhvcNAQELBQAwWTELMAkGA1UEBhMC
#Snip#
gSCx8Luo9V76nPjDI8PORurSFVWL9jiGJH0rLakYoGv
</client-cert>
<client-cert-auth-signature hash-algorithm-chosen="sha512">FIYur1Dzb4VPThVZtYwxSsCVRBUin/8MwWK+G5u2Phr4fJ
#snip#
EYt4G2hQ4hySySYqD4L4iV91uCT5b5Bmr5HZmSqKehg0zrDBjqxx7CLMSf2pSmQnjMwi6D0ygT=</client-cert-auth-signature>
</client-cert-chain>
</auth>
</config-auth>
Received attribute hash-algorithm-chosen in XML message from client
Base64 Signature (len=349):
FIYur1Dzb4VPThVZtYwxSsCVRBUin/8MwWK+G5u2Phr4fJI9aWFqd1BbV9WhSTsF
EYt4G2hQ4hySySYqD4L4iV91uCT5b5Bmr5HZmSqKehg0zrDBjqxx7CLMSf2pSmQn
ABXv++cN7lNWGHK91EAvNRcpCX4TdZ+6ZKpL4sClu8vZJeW2jwGmPnYesG3sttrS
TFBRqg74+1TFSbUuIEzn8MLXZqHbOnA19B9gyXZJon8eh3Z7cDspFiR0xKBu8iYH
L+ES84UNtDQjatIN4EiS8SD/5QPAunCyvAUBvK5FZ4c4TpnF6MIEPhjMwi6D0ygT
sm2218mstLDNKBouaTjB3A==
Successful Base64 signature decode, len 256
Loading cert into PKI
Waiting for certificate validation result
Verifying signature
Successfully verified signature
- Debug aggregate-auth ssl 127
/CSCOSSLC/config-auth Processing client request XML successfully parsed Processing request (init) INIT-no-cert: Client has not sent a certificate Found TG ANYCONNECT-MCA by URL https://10.197.223.81/MCA INIT-no-cert: Resolve tunnel group (ANYCONNECT-MCA) alias (NULL) Cert or URL mapped YES INIT-no-cert: Client advertised multi-cert authentication support [332565382] Created auth info for client 10.197.223.235 [332565382] Started timer (3 mins) for auth info for client 10.197.223.235 INIT-no-cert: Tunnel group ANYCONNECT-MCA requires multi-cert authentication [332565382] Generating multiple certificate request [332565382] Saved message of len 699 to verify signature rcode from handler = 0 Sending response /CSCOSSLC/config-auth Processing client request XML successfully parsed Processing request (init) INIT-cert: Client has certificate, groupSelect ANYCONNECT-MCA Found TG ANYCONNECT-MCA by URL https://10.197.223.81/MCA INIT-cert: Found tunnel group (ANYCONNECT-MCA) alias (NULL) url or certmap YES INIT-cert: Client advertised multi-cert authentication support [462466710] Created auth info for client 10.197.223.235 [462466710] Started timer (3 mins) for auth info for client 10.197.223.235 INIT-cert: Tunnel group ANYCONNECT-MCA requires multi-cert authentication Resetting FCADB entry [462466710] Generating multiple certificate request [462466710] Saved message of len 741 to verify signature rcode from handler = 0 Sending response /CSCOSSLC/config-auth Processing client request XML successfully parsed Processing request (auth-reply) auth-reply:[462466710] searching for authinfo [462466710] Found auth info for client 10.197.223.235, update expire timer (3 mins) Found tunnel group (ANYCONNECT-MCA) alias ANYCONNECT-MCA [462466710] Multi cert authentication [462466710] First cert came in SSL protocol, len 891 [462466710] Success loading cert into PKI [462466710] Authenticating second cert [462466710] Sending Message AGGAUTH_MSG_ATHENTICATE_CERT(1) [462466710] Fiber waiting Aggauth Message handler received message AGGAUTH_MSG_ATHENTICATE_CERT [462466710] Process certificate authentication request [462466710] Waiting for async certificate verification [462466710] Verify cert callback [462466710] Certificate Authentication success - verifying signature [462466710] Signature verify success [462466710] Signalling fiber [462466710] Fiber continuing [462466710] Found auth info [462466710] Resolved tunnel group (ANYCONNECT-MCA), Cert or URL mapped YES Resetting FCADB entry Attempting cert only login Authorization username = MachineID.cisco.com Opened AAA handle 335892526 Making AAA request AAA request finished Send auth complete rcode from handler = 0 Sending response Closing AAA handle 335892526 [462466710] Destroy auth info for 10.197.223.235 [462466710] Free auth info for 10.197.223.235
相关信息
修订历史记录
| 版本 | 发布日期 | 备注 |
|---|---|---|
1.0 |
29-Nov-2017 |
初始版本 |
由思科工程师提供
- 沙克蒂·库马尔思科TAC工程师
- 杜鲁夫·戈埃尔思科TAC工程师
 反馈
反馈