简介
本文档介绍如何使用设置配置ASA,以从VPN连接中排除发往Microsoft Office 365(Microsoft Teams)和Cisco Webex的流量。
背景信息
配置自适应安全设备(ASA)还为支持ASA的AnyConnect客户端引入网络地址排除和基于动态完全限定域名(FQDN)的排除。
Split Tunneling
需要将ASA配置为排除要从隧道中排除的指定IPv4和IPv6目标列表。遗憾的是,地址列表是动态的,可能会发生变化。请参阅Python脚本的“配置”部分,以及指向可用于检索列表和生成示例配置的在线python读取评估打印循环(REPL)的链接。
动态拆分隧道
除了拆分排除网络地址列表之外,Windows和Mac版的AnyConnect 4.6中还添加了动态拆分隧道。动态拆分隧道使用FQDN来确定连接能否通过隧道。python脚本还确定要添加到自定义AnyConnect属性的终端的FQDN。
配置
在Python 3 REPL中运行此脚本,或在公共REPL环境(例如AnyConnectO365DynamicExclude)中运行此脚本
import urllib.request
import uuid
import json
import re
def print_acl_lines(acl_name, ips, section_comment):
slash_to_mask = (
"0.0.0.0",
"192.0.2.1",
"192.0.2.1",
"10.224.0.0",
"10.240.0.0",
"10.248.0.0",
"10.252.0.0",
"10.254.0.0",
"10.255.0.0",
"10.255.128.0",
"10.255.192.0",
"10.255.224.0",
"10.255.240.0",
"10.255.248.0",
"10.255.252.0",
"10.255.254.0",
"10.255.255.0",
"10.255.255.128",
"10.255.255.192",
"10.255.255.224",
"10.255.255.240",
"10.255.255.248",
"10.255.255.252",
"10.255.255.254",
"10.255.255.255",
"10.255.255.255",
"10.255.255.255",
"10.255.255.255",
"10.255.255.240",
"10.255.255.248",
"10.255.255.252",
"10.255.255.254",
"10.255.255.255",
)
print(
"access-list {acl_name} remark {comment}".format(
acl_name=acl_name, comment=section_comment
)
)
for ip in sorted(ips):
if ":" in ip:
# IPv6 address
print(
"access-list {acl_name} extended permit ip {ip} any6".format(
acl_name=acl_name, ip=ip
)
)
else:
# IPv4 address. Convert to a mask
addr, slash = ip.split("/")
slash_mask = slash_to_mask[int(slash)]
print(
"access-list {acl_name} extended permit ip {addr} {mask} any4".format(
acl_name=acl_name, addr=addr, mask=slash_mask
)
)
# Fetch the current endpoints for O365
http_res = urllib.request.urlopen(
url="https://endpoints.office.com/endpoints/worldwide?clientrequestid={}".format(
uuid.uuid4()
)
)
res = json.loads(http_res.read())
o365_ips = set()
o365_fqdns = set()
for service in res:
if service["category"] == "Optimize":
for ip in service.get("ips", []):
o365_ips.add(ip)
for fqdn in service.get("urls", []):
o365_fqdns.add(fqdn)
# Generate an acl for split excluding For instance
print("##### Step 1: Create an access-list to include the split-exclude networks\n")
acl_name = "ExcludeSass"
# O365 networks
print_acl_lines(
acl_name=acl_name,
ips=o365_ips,
section_comment="v4 and v6 networks for Microsoft Office 365",
)
# Microsoft Teams
# https://docs.microsoft.com/en-us/office365/enterprise/office-365-vpn-implement-split-tunnel#configuring-and-securing-teams-media-traffic
print_acl_lines(
acl_name=acl_name,
ips=["10.107.60.1/32"],
section_comment="v4 address for Microsoft Teams"
)
# Cisco Webex - Per https://help.webex.com/en-us/WBX000028782/Network-Requirements-for-Webex-Teams-Services
webex_ips = [
"10.68.96.1/19",
"10.114.160.1/20",
"10.163.32.1/19",
"192.0.2.1/18",
"192.0.2.2/19",
"198.51.100.1/20",
"203.0.113.1/19",
"203.0.113.254/19",
"203.0.113.2/19",
"172.29.192.1/19",
"203.0.113.1/20",
"10.26.176.1/20",
"10.109.192.1/18",
"10.26.160.1/19",
]
print_acl_lines(
acl_name=acl_name,
ips=webex_ips,
section_comment="IPv4 and IPv6 destinations for Cisco Webex",
)
# Edited. April 1st 2020
# Per advice from Microsoft they do NOT advise using dynamic split tunneling for their properties related to Office 365
#
print(
"\n\n##### Step 2: Create an Anyconnect custom attribute for dynamic split excludes\n"
)
print("SKIP. Per Microsoft as of April 2020 they advise not to dynamically split fqdn related to Office365")
#print(
# """
#webvpn
# anyconnect-custom-attr dynamic-split-exclude-domains description dynamic-split-exclude-domains
#
#anyconnect-custom-data dynamic-split-exclude-domains saas {}
#""".format(
# ",".join([re.sub(r"^\*\.", "", f) for f in o365_fqdns])
# )
#)
#
print("\n##### Step 3: Configure the split exclude in the group-policy\n")
print(
"""
group-policy GP1 attributes
split-tunnel-policy excludespecified
ipv6-split-tunnel-policy excludespecified
split-tunnel-network-list value {acl_name}
""".format(
acl_name=acl_name
)
)
注意:Microsoft建议通过使用发布的IPv4和IPv6地址范围配置分割隧道,将发往关键Office 365服务的流量从VPN连接范围中排除。为了获得最佳性能并最有效地使用VPN容量,可以直接将流向这些与Office 365 Exchange Online、SharePoint Online和Microsoft Teams关联的专用IP地址范围(在Microsoft文档中称为“优化”类别)的流量路由到VPN隧道之外。有关此建议的更多详细信息,请参阅使用VPN拆分隧道优化远程用户的Office 365连接。
注:截至2020年4月初,Microsoft Teams有一个依赖关系,即必须从隧道中排除IP范围10.107.60.1/32。有关详细信息,请参阅配置和保护Teams媒体流量。
确认
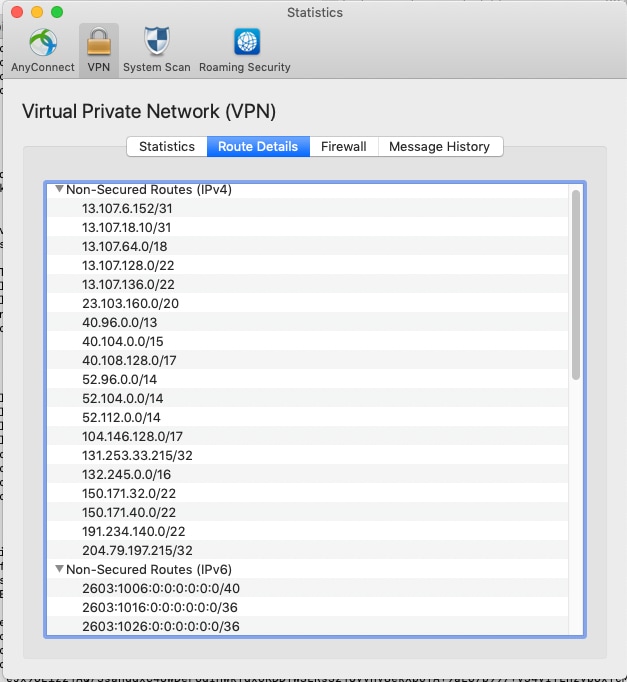
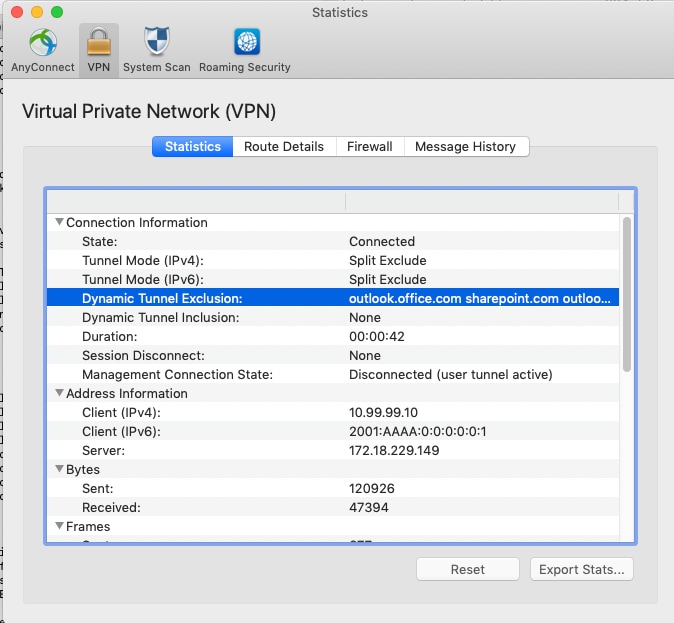
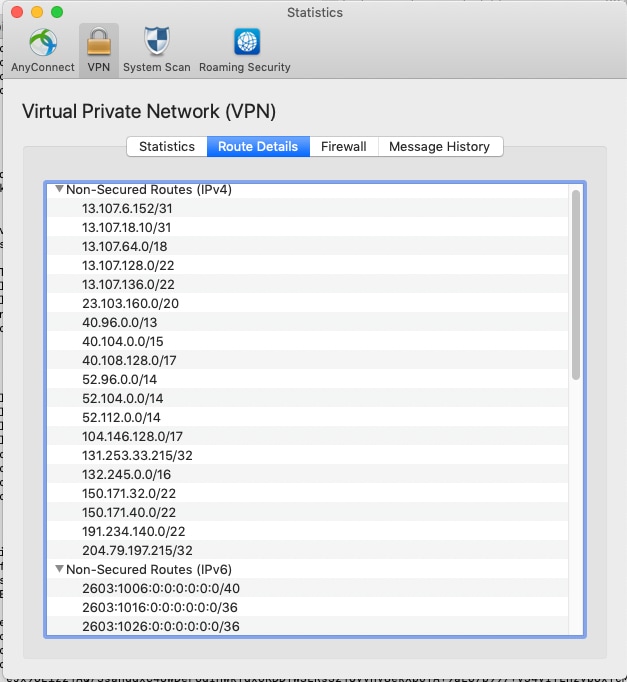
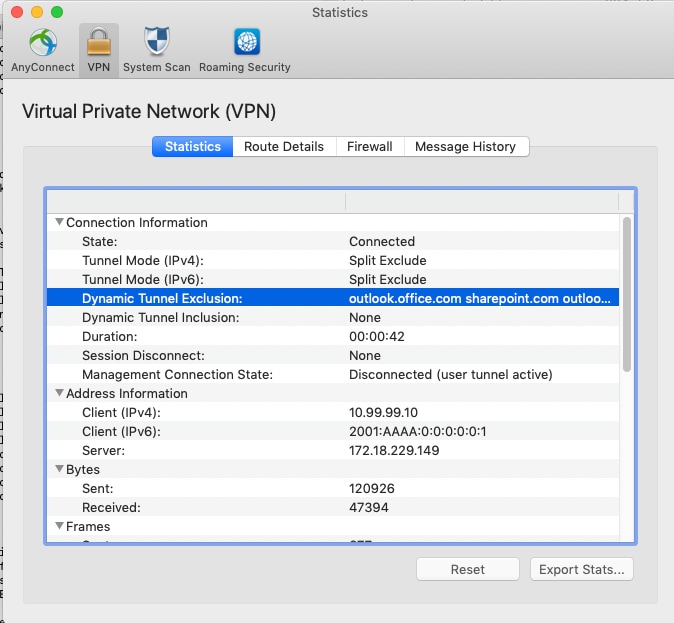
连接用户后,您会看到非安全路由填充了ACL中提供的地址以及Dynamic Tunnel Exclusion列表。
 反馈
反馈