简介
本文档介绍如何检查Nexus 9K平台中智能流量导向器(ITD)的控制平面和数据平面。
先决条件
要求
Cisco 建议您了解以下主题:
- Nexus NX-OS 软件。
- 访问列表(ACL)。
- IP服务级别协议(IP SLA)。
- 策略型路由(PBR)。
- 智能流量导向器(ITD)。
使用的组件
本文档中的信息基于NXOS版本10.2(5)的Cisco Nexus 9000。
本文档中的信息都是基于特定实验室环境中的设备编写的。本文档中使用的所有设备最初均采用原始(默认)配置。如果您的网络处于活动状态,请确保您了解所有命令的潜在影响。
配置
ITD是基于硬件的多TB智能解决方案,允许您为第3层和第4层流量分配、负载均衡和重定向构建可扩展的架构。
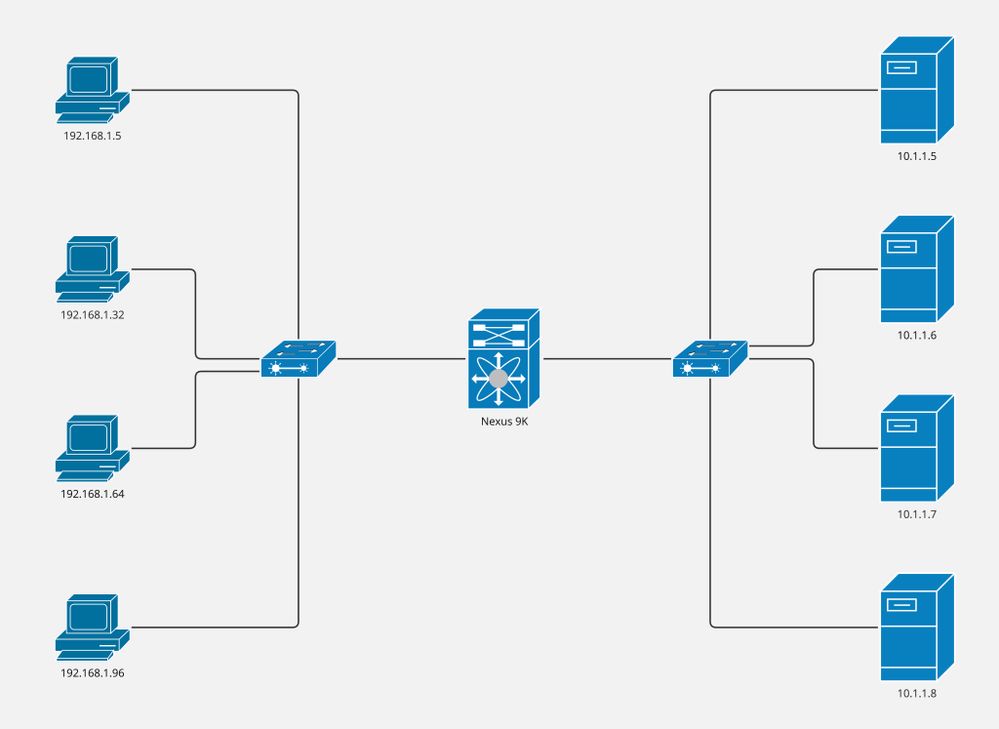
网络图
- 计算机:4
- 服务器:4
- 第2层交换机:2
- Nexus 9K交换机:1

注意:第2层交换机合并服务器/计算机与Nexus 9K交换机(ITD在其中运行)之间的连接。
配置
此配置在Nexus 9K交换机上实施,仅涵盖ITD部分。计算机是VLAN 5的一部分,服务器是VLAN 10的一部分,而Nexus 9K是两个VLAN的网关。
步骤1:启用所需功能。
feature itd
feature sla sender
feature sla responder
feature pbr
第二步:定义设备组,指向节点,并指示探测方法。
itd device-group CiscoGroup
probe icmp frequency 5 timeout 5 retry-down-count 2 retry-up-count 2
node ip 10.1.1.5
node ip 10.1.1.6
node ip 10.1.1.7
node ip 10.1.1.8
第三步:定义服务。用户可以指示虚拟ip或包括访问列表。

注意:NX-OS将最后一个二进制八位数除以指示的时段数。在本例中,我们将256除以8。因此,每个桶包含32台主机。
Bucket 1: From x.x.x.0 to x.x.x.31
Bucket 2: From x.x.x.32 to x.x.x.63
Bucket 3: From x.x.x.64 to x.x.x.95
Bucket 4: From x.x.x.96 to x.x.x.127
Bucket 5: From x.x.x.128 to x.x.x.159
Bucket 6: From x.x.x.160 to x.x.x.191
Bucket 7: From x.x.x.192 to x.x.x.223
Bucket 8: From x.x.x.224 to x.x.x.255
itd CiscoService
device-group CiscoGroup
virtual ip 192.168.255.1 255.255.255.255 advertise enable
ingress interface Vlan5
failaction node reassign
load-balance method src ip buckets 8
no shut
第四步:为定义的服务启用统计信息。
itd statistics CiscoService
验证
1.确认ITD服务处于活动状态,并且节点状态正常。
Nexus# show itd CiscoService brief
Legend:
C-S(Config-State): A-Active,S-Standby,F-Failed
ST(Status): ST-Standby,LF-Link Failed,PF-Probe Failed,PD-Peer Down,IA-Inactive,SH-Shut,HD-Hold-down
Name LB Scheme Status Buckets Interface
-------------- ---------- -------- --------- --------------
CiscoService src-ip ACTIVE 8 Vlan5
Source Interface
----------------
Device Group Probe Port VRF
-------------------------------------------------- ----- ------ ---------
CiscoGroup ICMP
Virtual IP Netmask/Prefix Protocol Port
------------------------------------------------------ ------------ ----------
192.168.255.1 / 255.255.255.255 IP 0
Node IP Cluster-id C-S WGT Probe Port Probe-IP STS
------------------------- ---------- -- --- ---- ----- --------------- --
1 10.1.1.5 A 1 ICMP OK
2 10.1.1.6 A 1 ICMP OK
3 10.1.1.7 A 1 ICMP OK
4 10.1.1.8 A 1 ICMP OK
2.确认已创建路由策略并将其与入口接口关联。

注意:在NXOS 10.1(2)之前,在running-config(在入口接口下)中应用路由策略,从NXOS 10.2(1)开始,您可以使用show ip policy命令查找系统中关联的路由策略。
Nexus# show ip policy
Interface Route-map Status VRF-Name
Vlan5 CiscoService_itd_pool Active default
3.确认已正确生成与预期节点关联的路由映射,并指示跟踪(IP SLA)。

注:每个桶应具有一个路由映射条目。
预期每个节点有一个跟踪。
Nexus# show route-map dynamic CiscoService_itd_pool
route-map CiscoService_itd_pool, permit, sequence 10
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_1
Set clauses:
ip next-hop verify-availability 10.1.1.5 track 2 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 11
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_2
Set clauses:
ip next-hop verify-availability 10.1.1.6 track 3 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 12
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_3
Set clauses:
ip next-hop verify-availability 10.1.1.7 track 4 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 13
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_4
Set clauses:
ip next-hop verify-availability 10.1.1.8 track 5 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 14
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_5
Set clauses:
ip next-hop verify-availability 10.1.1.5 track 2 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 15
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_6
Set clauses:
ip next-hop verify-availability 10.1.1.6 track 3 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 16
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_7
Set clauses:
ip next-hop verify-availability 10.1.1.7 track 4 [ UP ] force-order
route-map CiscoService_itd_pool, permit, sequence 17
Match clauses:
ip address (access-lists): CiscoService_itd_vip_1_bucket_8
Set clauses:
ip next-hop verify-availability 10.1.1.8 track 5 [ UP ] force-order
4.确认访问列表已正确生成,并具有预期的ip匹配条件。

注意:ACL在running-config中生成,直到NXOS 9.3(2),从NXOS 9.3(3)开始,我们可以使用show ip access-list dynamic命令在系统中找到ACL。
Nexus# show ip access-lists CiscoService_itd_vip_1_bucket_1 dynamic
IP access list CiscoService_itd_vip_1_bucket_1
10 permit ip 1.1.1.0 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_2 dynamic
IP access list CiscoService_itd_vip_1_bucket_2
10 permit ip 1.1.1.32 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_3 dynamic
IP access list CiscoService_itd_vip_1_bucket_3
10 permit ip 1.1.1.64 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_4 dynamic
IP access list CiscoService_itd_vip_1_bucket_4
10 permit ip 1.1.1.96 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_5 dynamic
IP access list CiscoService_itd_vip_1_bucket_5
10 permit ip 1.1.1.128 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_6 dynamic
IP access list CiscoService_itd_vip_1_bucket_6
10 permit ip 1.1.1.160 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_7 dynamic
IP access list CiscoService_itd_vip_1_bucket_7
10 permit ip 1.1.1.192 255.255.255.31 192.168.255.1/32
513E-A-15-C9336C-FX-2-1# show ip access-lists CiscoService_itd_vip_1_bucket_8 dynamic
IP access list CiscoService_itd_vip_1_bucket_8
10 permit ip 1.1.1.224 255.255.255.31 192.168.255.1/32
5.确保在TCAM中对访问列表进行编程。
Nexus# show system internal access-list input entries detail | begin "VLAN 5"
VLAN 5 :
=========
INSTANCE 0x0
---------------
Tcam 1 resource usage:
----------------------
LBL B = 0x1
Bank 1
------
IPv4 Class
Policies: PBR(CiscoService_itd_vip_1_bucket_8)
Netflow profile: 0
Netflow deny profile: 0
Entries:
[Index] Entry [Stats]
---------------------
[0x0000:0x0002:0x0002] permit ip 0.0.0.0/0 224.0.0.0/4 routeable 0x1 [0]
[0x0002:0x0004:0x0004] permit ip 0.0.0.0/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x0003:0x0005:0x0005] permit ip 0.0.0.32/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x0004:0x0006:0x0006] permit ip 0.0.0.64/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x0005:0x0007:0x0007] permit ip 0.0.0.96/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000b:0x000d:0x000d] permit ip 0.0.0.128/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000c:0x000e:0x000e] permit ip 0.0.0.160/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000d:0x000f:0x000f] permit ip 0.0.0.192/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000e:0x0010:0x0010] permit ip 0.0.0.224/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000f:0x0011:0x0011] permit ip 0.0.0.0/0 0.0.0.0/0 routeable 0x1 [0]
L4 protocol cam entries usage: none
No mac protocol cam entries are in use
INSTANCE 0x1
---------------
Tcam 1 resource usage:
----------------------
LBL B = 0x1
Bank 1
------
IPv4 Class
Policies: PBR(CiscoService_itd_vip_1_bucket_8)
Netflow profile: 0
Netflow deny profile: 0
Entries:
[Index] Entry [Stats]
---------------------
[0x0000:0x0002:0x0002] permit ip 0.0.0.0/0 224.0.0.0/4 routeable 0x1 [0]
[0x0002:0x0004:0x0004] permit ip 0.0.0.0/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x0003:0x0005:0x0005] permit ip 0.0.0.32/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x0004:0x0006:0x0006] permit ip 0.0.0.64/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x0005:0x0007:0x0007] permit ip 0.0.0.96/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000b:0x000d:0x000d] permit ip 0.0.0.128/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000c:0x000e:0x000e] permit ip 0.0.0.160/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000d:0x000f:0x000f] permit ip 0.0.0.192/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000e:0x0010:0x0010] permit ip 0.0.0.224/0.0.0.224 192.168.255.1/32 routeable 0x1 [0]
[0x000f:0x0011:0x0011] permit ip 0.0.0.0/0 0.0.0.0/0 routeable 0x1 [0]
L4 protocol cam entries usage: none
No mac protocol cam entries are in use
6.将流量发送到虚拟IP地址,并确认预期节点的计数器(数据包数)增加。
Nexus# show itd CiscoService statistics
Service Device Group VIP/mask #Packets
-------------------------------------------------------------------------------------------------------------------------------------------
CiscoService CiscoGroup 192.168.255.1 / 255.255.255.255 0 (0%)
Traffic Bucket Assigned to Mode Original Node #Packets
--------------- -------------- ----- -------------- ---------
CiscoService_itd_vip_1_bucket_1 10.1.1.5 Redirect 10.1.1.5 0 (0%)
CiscoService_itd_vip_1_bucket_5 10.1.1.5 Redirect 10.1.1.5 0 (0%)
Traffic Bucket Assigned to Mode Original Node #Packets
--------------- -------------- ----- -------------- ---------
CiscoService_itd_vip_1_bucket_2 10.1.1.6 Redirect 10.1.1.6 0 (0%)
CiscoService_itd_vip_1_bucket_6 10.1.1.6 Redirect 10.1.1.6 0 (0%)
Traffic Bucket Assigned to Mode Original Node #Packets
--------------- -------------- ----- -------------- ---------
CiscoService_itd_vip_1_bucket_3 10.1.1.7 Redirect 10.1.1.7 0 (0%)
CiscoService_itd_vip_1_bucket_7 10.1.1.7 Redirect 10.1.1.7 0 (0%)
Traffic Bucket Assigned to Mode Original Node #Packets
--------------- -------------- ----- -------------- ---------
CiscoService_itd_vip_1_bucket_4 10.1.1.8 Redirect 10.1.1.8 0 (0%)
CiscoService_itd_vip_1_bucket_8 10.1.1.8 Redirect 10.1.1.8 0 (0%)