通过内部报告模式对Catalyst SD-WAN Manager上的许可证同步进行故障排除
下载选项
非歧视性语言
此产品的文档集力求使用非歧视性语言。在本文档集中,非歧视性语言是指不隐含针对年龄、残障、性别、种族身份、族群身份、性取向、社会经济地位和交叉性的歧视的语言。由于产品软件的用户界面中使用的硬编码语言、基于 RFP 文档使用的语言或引用的第三方产品使用的语言,文档中可能无法确保完全使用非歧视性语言。 深入了解思科如何使用包容性语言。
关于此翻译
思科采用人工翻译与机器翻译相结合的方式将此文档翻译成不同语言,希望全球的用户都能通过各自的语言得到支持性的内容。 请注意:即使是最好的机器翻译,其准确度也不及专业翻译人员的水平。 Cisco Systems, Inc. 对于翻译的准确性不承担任何责任,并建议您总是参考英文原始文档(已提供链接)。
简介
本文档介绍如何通过内部报告模式对Catalyst SD-WAN Manager上同步许可证时遇到的错误进行故障排除。
要求
对于Catalyst SD-WAN Manager未直接连接到互联网的情况,使用代理服务器可以提供对基于互联网的服务(例如Cisco SSM)或本地内部SSM的访问。
最低版本:Catalyst SD-WAN Manager版本20.9.1
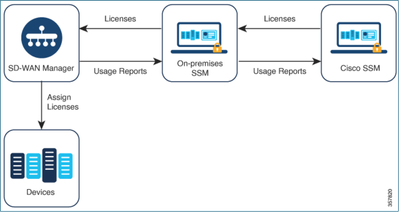
思科本地智能软件管理器(SSM on-prem)是思科智能许可解决方案,使您能够从本地服务器管理许可证,而不必直接连接到思科SSM。该解决方案涉及设置思科SSM内部许可证服务器,该服务器定期将其许可证数据库与思科SSM同步,并且功能与思科SSM类似,同时在本地运行。
Catalyst SD-WAN Manager支持使用思科SSM内部服务器管理许可证,使用一种称为内部服务器的模式。内部模式对于使用Cisco SSM内部模式以满足严格安全策略的组织(该策略不允许网络设备通过直接互联网连接与Cisco SSM通信)非常有用。
在内部模式中运行时,Catalyst SD-WAN Manager每24小时与思科SSM内部许可证服务器同步许可证信息。在此同步过程中,Catalyst SD-WAN Manager接收对可用许可证的任何更新,并将许可证使用情况报告发送到Cisco SSM内部许可证服务器。您可以随时同步许可证。
使用本地思科智能软件管理器的优势
安全策略或其他情况要求Catalyst SD-WAN Manager未连接到互联网的组织有两个选项可用于使用策略管理智能许可证的许可证:
- 使用离线模式,这需要在Catalyst SD-WAN Manager和Cisco SSM之间手动传输文件。
- 使用可通过本地连接访问Catalyst SD-WAN Manager的Cisco SSM内部服务器。
这两种方法都解决了在Cisco SSM和Catalyst SD-WAN Manager之间传输许可证信息的需要。只要可以使用内部模式,此模式就可以显著减少在Catalyst SD-WAN Manager和Cisco SSM之间手动传输文件的维护开销,这是离线模式所必需的。
Error
从Catalyst SD-WAN Manager GUI同步智能凭证时,我们会收到以下错误:
Failed to authenticate Smart Account credentials.: Failed to authenticate user - 'admin'. {"error":"invalid_client","error_message":"Grant not found. Ensure that the given grant details are correct."}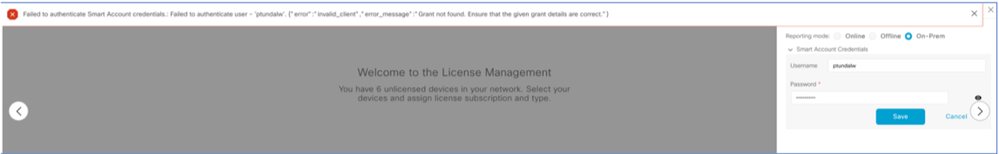
故障排除方法
- vManage必须位于代码20.9.1或更高版本上。
- 在Catalyst SD-WAN Manager License Management部分放置智能帐户凭证时,检查Catalyst SD-WAN Manager (vmanage-server.logs)上的日志。
- 确保本地SSM团队共享的客户端ID和密钥正确。
- CSSM服务器IP的vManage上的TCPDUMP
- 验证Catalyst SD-WAN Manager上的DNS配置正确且能够ping通cloudsso.cisco.com
- 让内部SSM团队参与,并请求SSM团队在内部服务器端进行调试。
Catalyst SD-WAN Manager IP:10.66.76.81 / 192.168.10.1
CSSM服务器IP:10.106.66.55
SSM服务器IP的vManage上的TCPDump:
um8_vManage# tcpdump vpn 0 interface eth0 options "host 10.106.66.55 -nn -vv"
tcpdump -p -i eth0 -s 128 host 10.106.66.55 -nn -vv in VPN 0
tcpdump: listening on eth0, link-type EN10MB (Ethernet), capture size 128 bytes
12:15:06.407513 IP (tos 0x0, ttl 64, id 24618, offset 0, flags [DF], proto TCP (6), length 52)
192.168.10.1.57886 > 10.106.66.55.8443: Flags [S], cksum 0xfadb (incorrect -> 0xdf91), seq 746386211, win 29200, options [mss 1460,nop,nop,sackOK,nop,wscale 7], length 0
12:15:06.651698 IP (tos 0x20, ttl 44, id 0, offset 0, flags [DF], proto TCP (6), length 52)
10.106.66.55.8443 > 192.168.10.1.57886: Flags [S.], cksum 0x1b34 (correct), seq 2758352947, ack 746386212, win 29200, options [mss 1380,nop,nop,sackOK,nop,wscale 7], length 0
12:15:06.651768 IP (tos 0x0, ttl 64, id 24619, offset 0, flags [DF], proto TCP (6), length 40)
192.168.10.1.57886 > 10.106.66.55.8443: Flags [.], cksum 0xfacf (incorrect -> 0xcce1), seq 1, ack 1, win 229, length 0
12:15:06.654592 IP (tos 0x0, ttl 64, id 24620, offset 0, flags [DF], proto TCP (6), length 212)
192.168.10.1.57886 > 10.106.66.55.8443: Flags [P.], seq 1:173, ack 1, win 229, length 172
12:15:06.899695 IP (tos 0x0, ttl 41, id 44470, offset 0, flags [DF], proto TCP (6), length 40)
10.106.66.55.8443 > 192.168.10.1.57886: Flags [.], cksum 0xcc2d (correct), seq 1, ack 173, win 237, length 0
12:15:06.911484 IP (tos 0x0, ttl 41, id 44471, offset 0, flags [DF], proto TCP (6), length 1420)
10.106.66.55.8443 > 192.168.10.1.57886: Flags [.], seq 1:1381, ack 173, win 237, length 1380
12:15:06.911542 IP (tos 0x0, ttl 41, id 44472, offset 0, flags [DF], proto TCP (6), length 254)
10.106.66.55.8443 > 192.168.10.1.57886: Flags [P.], seq 1381:1595, ack 173, win 237, length 214
12:15:06.911573 IP (tos 0x0, ttl 64, id 24621, offset 0, flags [DF], proto TCP (6), length 40)
192.168.10.1.57886 > 10.106.66.55.8443: Flags [.], cksum 0xfacf (incorrect -> 0xc6bb), seq 173, ack 1381, win 251, length 0
12:15:06.911598 IP (tos 0x0, ttl 64, id 24622, offset 0, flags [DF], proto TCP (6), length 40)
192.168.10.1.57886 > 10.106.66.55.8443: Flags [.], cksum 0xfacf (incorrect -> 0xc5cf), seq 173, ack 1595, win 273, length 0
12:15:06.923929 IP (tos 0x0, ttl 64, id 24623, offset 0, flags [DF], proto TCP (6), length 234)
192.168.10.1.57886 > 10.106.66.55.8443: Flags [P.], seq 173:367, ack 1595, win 273, length 194
内部服务器日志:
[root@SSM-On-Prem log]# tail -f messages
Jan 13 11:13:36 SSM-On-Prem chronyd[1319]: Source 172.20.226.229https://172.20.226.229 replaced with 172.30.5.123https://172.30.5.123
Jan 13 11:14:09 SSM-On-Prem b09c1e3b5d81: 1:M 13 Jan 2023 11:14:09.049 * 100 changes in 300 seconds. Saving...
Jan 13 11:14:09 SSM-On-Prem b09c1e3b5d81: 1:M 13 Jan 2023 11:14:09.050 * Background saving started by pid 4617
Jan 13 11:14:09 SSM-On-Prem b09c1e3b5d81: 4617:C 13 Jan 2023 11:14:09.052 * DB saved on disk
Jan 13 11:14:09 SSM-On-Prem b09c1e3b5d81: 4617:C 13 Jan 2023 11:14:09.053 * RDB: 0 MB of memory used by copy-on-write
Jan 13 11:14:09 SSM-On-Prem b09c1e3b5d81: 1:M 13 Jan 2023 11:14:09.150 * Background saving terminated with success
Jan 13 11:14:46 SSM-On-Prem 1a1fca641d0a: Redis#exists(key) will return an Integer in redis-rb 4.3. exists? returns a boolean, you should use it instead. To opt-in to the new behavior now you can set Redis.exists_returns_integer = true. To disable this message and keep the current (boolean) behaviour of 'exists' you can set Redis.exists_returns_integer = false, but this option will be removed in 5.0. (/usr/local/lib/ruby/gems/2.6.0/gems/redis-session-store-0.11.1/lib/redis-session-store.rb:70:in `session_exists?')
Jan 13 11:14:46 SSM-On-Prem 1a1fca641d0a: [active_model_serializers] Rendered UserSerializer with ActiveModelSerializers::Adapter::Attributes (3.0ms)
Jan 13 11:14:46 SSM-On-Prem 1a1fca641d0a: method=GET path=/sessions/get_user format=json controller=SessionsController action=get_user status=200 duration=24.86 view=3.23 db=7.98 params={"controller"=>"sessions", "action"=>"get_user", "session"=>{}} session_id=[FILTERED] uid=admin time=2023-07-13T11:14:46Z http_referer=https://172.20.85.137:8443/admin/ client_ip=10.110.35.124https://10.110.35.124 user_agent=Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/10.120.0.0 Safari/537.36
Jan 13 11:14:46 SSM-On-Prem 504f06c0d581: 10.110.35.124https://10.110.35.124 - - [13/Jan/2023:11:14:46 +0000] "GET /backend/sessions/get_user HTTP/1.1" 200 271 https://172.20.85.137:8443/admin/ "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/10.120.0.0 Safari/537.36" "-"
Jan 13 11:17:01 SSM-On-Prem 504f06c0d581: 2023/07/13 11:17:01 [error] 47#47: *1576 connect() failed (111: Connection refused) while connecting to upstream, client: 10.66.76.85, server: , request: "POST /backend/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=admin&password=CiscoLab%21234567 HTTP/1.1", upstream: http://[fd00:dead:beef::5]:3000/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=admin&password=CiscoLab%21234567, host: "172.20.85.137:8443"
Jan 13 11:17:01 SSM-On-Prem 504f06c0d581: 2023/07/13 11:17:01 [warn] 47#47: *1576 upstream server temporarily disabled while connecting to upstream, client: 10.66.76.85, server: , request: "POST /backend/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=admin&password=CiscoLab%21234567 HTTP/1.1", upstream: http://[fd00:dead:beef::5]:3000/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=admin&password=CiscoLab%21234567, host: "172.20.85.137:8443"
Jan 13 11:17:01 SSM-On-Prem 1a1fca641d0a: [active_model_serializers] Rendered ActiveModel::Serializer::Null with Hash (0.09ms)
Jan 13 11:17:01 SSM-On-Prem 1a1fca641d0a: method=POST path=/oauth/token format=json controller=Doorkeeper::OauthTokensController action=create status=403 duration=4.21 view=0.53 db=1.12
Jan 13 11:17:01 SSM-On-Prem 504f06c0d581: 10.66.76.85https://10.66.76.85 - - [13/Jan/2023:11:17:01 +0000] "POST /backend/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=admin&password=CiscoLab%21234567 HTTP/1.1" 403 121 "-" "Apache-HttpClient/4.5.11 (Java/11.0.7)" "-"
Jan 13 11:17:14 SSM-On-Prem 1a1fca641d0a: [INFO] Session expiring outcome=success在vManage License Management(vManage许可证管理)部分放置智能帐户详细信息时,登录vManage:
13-Jan-2023 17:29:02,775 IST INFO [um8_vManage] [SmartLicensingIntegrationManager] (default task-24) |default| user is using in On Prem mode
13-Jan-2023 17:29:02,776 IST INFO [um8_vManage] [SmartLicensingIntegrationManager] (default task-24) |default| Authenticating on-prem server
13-Jan-2023 17:29:02,780 IST INFO [um8_vManage] [AbstractSettingsManager] (default task-24) |default| Found smart licensing mode is onprem
13-Jan-2023 17:29:02,781 IST INFO [um8_vManage] [SmartLicensingUtil] (default task-24) |default| intializing client Map {clientUrl=172.20.85.137https://172.20.85.137, client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx, client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf}
13-Jan-2023 17:29:02,781 IST INFO [um8_vManage] [SmartLicensingUtil] (default task-24) |default| Getting onPrem server details
13-Jan-2023 17:29:02,793 IST INFO [um8_vManage] [RestAPIClient] (default task-24) |default| RestAPI proxy host
13-Jan-2023 17:29:02,793 IST INFO [um8_vManage] [RestAPIClient] (default task-24) |default| RestAPI proxy port
13-Jan-2023 17:29:02,798 IST INFO [um8_vManage] [SmartLicensingUtil] (default task-24) |default| URL backend/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=ptundalw&password=Carnation%2321
13-Jan-2023 17:29:02,798 IST INFO [um8_vManage] [SmartLicensingUtil] (default task-24) |default| Query Smart Account: backend/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=ptundalw&password=*******
13-Jan-2023 17:29:03,490 IST ERROR [um8_vManage] [RestAPIClient] (default task-24) |default| Failed to process POST request uri: backend/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=ptundalw&password=******* . Code: 403 Message: {"error":"invalid_client","error_message":"Grant not found. Ensure that the given grant details are correct."}
13-Jan-2023 17:29:03,491 IST ERROR [um8_vManage] [SmartLicensingUtil] (default task-24) |default| Failed to authenticate user - 'ptundalw'.
13-Jan-2023 17:29:03,491 IST ERROR [um8_vManage] [SmartLicensingIntegrationRestfulResource] (default task-24) |default| Smart Account User Authentication failed.注意:从vManage GUI同步智能帐户时出现错误403,表明服务器理解该请求,但拒绝对其进行授权。
解决方法
- 登录到Prem Server。
- 导航到API工具包。
- 选择“Resource Owner Grant”,输入详细信息作为Name并保存。
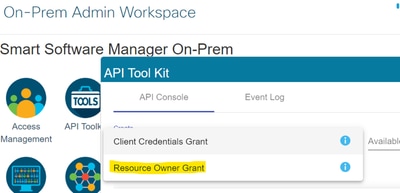
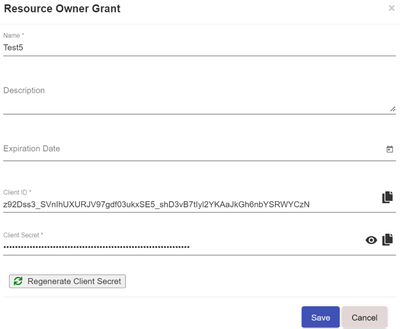
- 选择保存的记录(在以前的快照中提及)并选中“客户端ID”和“客户端密码”。
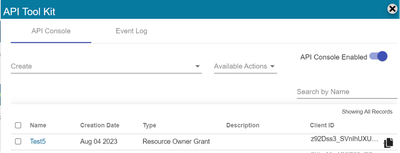
- 在Catalyst SD-WAN Manager门户中共享并输入共享客户端ID和客户端密码。
- 转至vManage中的“同步许可证和刷新设备”,并使用您登录所使用的内部凭证生成客户端ID和客户端密码。
修订历史记录
| 版本 | 发布日期 | 备注 |
|---|---|---|
1.0 |
11-Jul-2024 |
初始版本 |
 反馈
反馈