簡介
此示例配置提供有關如何設定自適應安全裝置(ASA)以訪問位於外部網路上的郵件伺服器的資訊。
請參閱ASA 8.3及更高版本:有關如何設定ASA安全裝置以訪問位於DMZ網路上的郵件/SMTP伺服器的詳細資訊,請參閱DMZ上的郵件(SMTP)伺服器訪問配置示例。
請參閱ASA 8.3及更高版本:內部網路上的郵件(SMTP)伺服器訪問配置示例,用於設定ASA安全裝置以訪問內部網路上的郵件/SMTP伺服器。
請參閱PIX/ASA 7.x及更高版本:在版本8.2及更低版本的Cisco Adaptive Security Appliance(ASA)上相同配置的外部網路上的郵件(SMTP)伺服器訪問配置示例。
必要條件
需求
本文件沒有特定需求。
採用元件
本文中的資訊係根據以下軟體和硬體版本:
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路正在作用,請確保您已瞭解任何指令可能造成的影響。
慣例
請參閱思科技術提示慣例以瞭解更多有關文件慣例的資訊。
設定
本節提供用於設定本文件中所述功能的資訊。
註:使用Cisco CLI Analyzer獲取本節所用命令的詳細資訊。
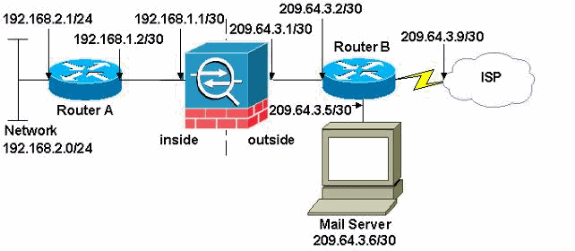
網路圖表
本檔案會使用以下網路設定:
注意:此配置中使用的IP編址方案在Internet上不能合法路由。這些地址是在實驗室環境中使用的RFC 1918地址。
本示例中使用的網路設定包含具有內部網路(192.168.1.0/30)和外部網路(209.64.3.0/30)的ASA。 IP地址為209.64.3.6的郵件伺服器位於外部網路中。配置NAT語句,以便從192.168.2.x網路通過內部介面(Ethernet0)到外部介面(Ethernet 1)的任何流量轉換為209.64.3.129到209.64.3.253範圍內的地址。最後一個可用地址(209.64.3.254)保留用於埠地址轉換(PAT)。
組態
本檔案會使用以下設定:
| ASA |
ASA#show run
: Saved
:
ASA Version 8.3(1)
!
hostname ASA
enable password 8Ry2YjIyt7RRXU24 encrypted
passwd 2KFQnbNIdI.2KYOU encrypted
names
!
interface Ethernet0
shutdown
no nameif
no security-level
no ip address
!
interface Ethernet1
shutdown
no nameif
no security-level
no ip address
!
interface Ethernet2
shutdown
no nameif
no security-level
no ip address
!
!--- Configure the inside interface.
?
interface Ethernet3
nameif inside
security-level 100
ip address 192.168.1.1 255.255.255.252
!
!--- Configure the outside interface.
interface Ethernet4
nameif outside
security-level 0
ip address 209.64.3.1 255.255.255.252
!
interface Ethernet5
shutdown
no nameif
no security-level
no ip address
!
passwd 2KFQnbNIdI.2KYOU encrypted
boot system disk0:/asa831-k8.bin
ftp mode passive
pager lines 24
mtu inside 1500
mtu outside 1500
no failover
no asdm history enable
arp timeout 14400
!--- This command states that any traffic !--- from the 192.168.2.x network that passes from the inside interface (Ethernet0) !--- to the outside interface (Ethernet 1) translates into an address !--- in the range of 209.64.3.129 through 209.64.3.253 and contains a subnet !--- mask of 255.255.255.128.
object network obj-209.64.3.129_209.64.3.253
range 209.64.3.129-209.64.3.253
!--- This command reserves the last available address (209.64.3.254) for !--- for Port Address Translation (PAT). In the previous statement, !--- each address inside that requests a connection uses one !--- of the addresses specified. If all of these addresses are in use, !--- this statement provides a failsafe to allow additional inside stations !--- to establish connections.
object network obj-209.64.3.254
host 209.64.3.254
!--- This command indicates that all addresses in the 192.168.2.x range !--- that pass from the inside (Ethernet0) to a corresponding global !--- designation are done with NAT. !--- As outbound traffic is permitted by default on the ASA, no !--- static commands are needed.
object-group network nat-pat-group
network-object object obj-209.64.3.129_209.64.3.253
network-object object obj-209.64.3.254
object network obj-192.168.2.0
subnet 192.168.2.0 255.255.255.0
nat (inside,outside) dynamic nat-pat-group
!--- Creates a static route for the 192.168.2.x network with 192.168.1.2. !--- The ASA forwards packets with these addresses to the router !--- at 192.168.1.2.
route inside 192.168.2.0 255.255.255.0 192.168.1.2 1
!--- Sets the default route for the ASA Firewall at 209.64.3.2.
route outside 0.0.0.0 0.0.0.0 209.64.3.2 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00
timeout mgcp-pat 0:05:00 sip 0:30:00 sip_media 0:02:00
timeout uauth 0:05:00 absolute
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
telnet timeout 5
ssh timeout 5
console timeout 0
!
class-map inspection_default
match default-inspection-traffic
!
!
!--- SMTP/ESMTP is inspected since "inspect esmtp" is included in the map.
policy-map global_policy
class inspection_default
inspect dns maximum-length 512
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect esmtp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect sip
inspect netbios
inspect tftp
!
service-policy global_policy global
Cryptochecksum:8a63de5ae2643c541a397c2de7901041
: end |
| 路由器A |
Current configuration:
!
version 12.4
service timestamps debug uptime
service timestamps log uptime
no service password-encryption
!
hostname 2522-R4
!
enable secret 5 $1$N0F3$XE2aJhJlCbLWYloDwNvcV.
!
ip subnet-zero
!
!
!
!
!
interface Ethernet0
!--- Assigns an IP address to the inside Ethernet interface.
ip address 192.168.2.1 255.255.255.0
no ip directed-broadcast
!
interface Ethernet1
!--- Assigns an IP address to the ASA-facing interface.
ip address 192.168.1.2 255.255.255.252
no ip directed-broadcast
!
interface Serial0
no ip address
no ip directed-broadcast
shutdown
!
interface Serial1
no ip address
no ip directed-broadcast
shutdown
!
ip classless
!--- This route instructs the inside router to forward all !--- non-local packets to the ASA.
ip route 0.0.0.0 0.0.0.0 192.168.1.1
!
!
line con 0
transport input none
line aux 0
autoselect during-login
line vty 0 4
exec-timeout 5 0
password ww
login
!
end |
| 路由器B |
Current configuration:
!
version 12.4
service timestamps debug uptime
service timestamps log uptime
no service password-encryption
!
hostname 2522-R4
!
enable secret 5 $1$N0F3$XE2aJhJlCbLWYloDwNvcV.
!
ip subnet-zero
!
!
!
!
interface Ethernet0
!--- Assigns an IP address to the ASA-facing Ethernet interface.
ip address 209.64.3.2 255.255.255.252
no ip directed-broadcast
!
interface Ethernet1
!--- Assigns an IP address to the server-facing Ethernet interface.
ip address 209.64.3.5 255.255.255.252
no ip directed-broadcast
!
interface Serial0
!--- Assigns an IP address to the Internet-facing interface.
ip address 209.64.3.9 255.255.255.252
no ip directed-broadcast
no ip mroute-cache
!
interface Serial1
no ip address
no ip directed-broadcast
!
ip classless
!--- All non-local packets are to be sent out serial 0. In this case, !--- the IP address on the other end of the serial interface is not known, !--- or you can specify it here.
ip route 0.0.0.0 0.0.0.0 serial 0
!
!--- This statement is required to direct traffic destined to the !--- 209.64.3.128 network (the ASA global pool) to the ASA to be translated !--- back to the inside addresses.
ip route 209.64.3.128 255.255.255.128 209.64.3.1
!
!
line con 0
transport input none
line aux 0
autoselect during-login
line vty 0 4
exec-timeout 5 0
password ww
login
!
end |
ESMTP TLS配置
注意:如果您對電子郵件通訊使用傳輸層安全(TLS)加密,則ASA中的ESMTP檢查功能(預設情況下啟用)會丟棄資料包。要允許啟用TLS的電子郵件,請按照此輸出所示禁用ESMTP檢查功能。如需詳細資訊,請參閱Cisco錯誤ID CSCtn08326。
ciscoasa(config)#
policy-map global_policy
ciscoasa(config-pmap)#class inspection_default
ciscoasa(config-pmap-c)#no inspect esmtp
ciscoasa(config-pmap-c)#exit
ciscoasa(config-pmap)#exit
驗證
目前沒有適用於此組態的驗證程序。
疑難排解
Cisco CLI Analyzer支援某些show指令。使用CLI Analyzer檢視show指令輸出的分析。
logging buffered 7 命令將消息定向到ASA控制檯。如果與郵件伺服器的連線存在問題,請檢查控制檯調試消息以找到傳送站和接收站的IP地址以確定問題。
相關資訊