簡介
本文檔介紹在將trustsec與ISE(身份服務引擎)配合使用時,如何配置種子和非種子裝置。
在允許新裝置加入trustsec域之前,Trustsec使用NDAC(網路裝置准入控制)對新裝置進行身份驗證。這可防止未經授權的裝置參與交換trustsec資訊。種子裝置/身份驗證器(本例中為6500交換機)需要手動配置並使用RADIUS over IP連線到ISE。非種子裝置/請求方(本例中為3560X)沒有與ISE的直接IP連線,並要求種子裝置使用802.1X註冊並驗證其在網路上的身份。一旦請求方(非種子裝置)通過身份驗證,將從ISE調配PAC(受保護訪問憑證)並下載伺服器資訊。PAC包含共用金鑰和加密令牌,以便將來提供與ISE的安全聯絡。
必要條件
ISE身份驗證伺服器
支援Trustsec的種子裝置/身份驗證器
支援Trustsec的非種子裝置/請求方
請參考最新的trustsec相容性矩陣:
http://www.cisco.com/c/en/us/solutions/enterprise-networks/trustsec/solution-overview-listing.html
採用元件
- WS-C6509-E [VS-SUP2T-10G]
- s2t54-ipservicesk9-mz.SPA.152-1.SY3.bin
- WS-C3560X-24P-S
- c3560e-universalk9-mz.152-4.E4.bin
網路圖表
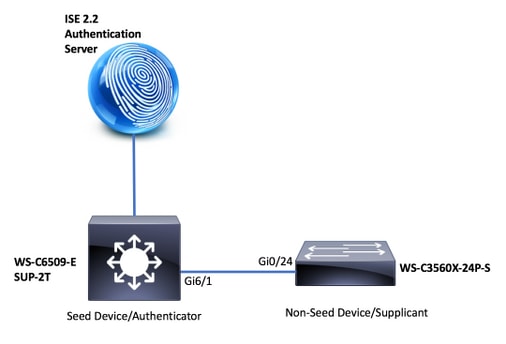 NDAC拓撲
NDAC拓撲
IP地址
ISE:14.36.143.18
6509:10.122.165.35
3560X:10.122.160.118
ISE 組態
新增網路裝置
6500(種子)
WorkCenters > TrustSec > Components > Network Devices > Add
裝置名稱和IP地址

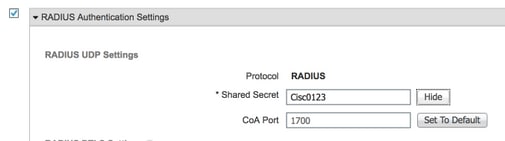
Radius共用密碼
Trustsec憑據

3560X(非種子)
WorkCenters > TrustSec > Components > Network Devices > Add
裝置名稱和IP地址

Radius共用密碼

Trustsec憑據

TrustSec安全組
工作中心> TrustSec >元件> 安全組

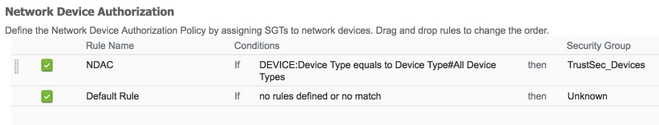
網路裝置授權策略
工作中心> TrustSec > TrustSec策略>網路裝置授權
種子裝置配置(6500)
TrustSec Credentials
6500#cts credentials id 6500 password Cisc0123
AAA configuration
6500(config)#aaa new-model
6500(config)#aaa authentication dot1x default group radius
6500(config)#aaa accounting identity default start-stop group radius
6500(config)#aaa authorization network CTSlist group radius
6500(config)#cts authorization list CTSlist
Radius Server Configuration
6500(config)#radius server ISE
6500(config-radius-server)#address ipv4 14.36.143.18 auth-port 1812 acct-port 1813
6500(config-radius-server)#pac key Cisc0123
Recognize and use vendor-specific attributes
6500(config)#radius-server vsa send authentication
Enable Change of Authorization
6500(config)#aaa server radius dynamic-author
6500(config-locsvr-da-radius)#client 14.36.143.18 server-key Cisc0123
Enable 802.1X
6500(config)#dot1x system-auth-control
Switchport TrustSec Configuration
6500(config)#int gi6/1
6500(config-if)#switchport mode trunk
6500(config-if)#cts dot1x
6500(config-if-cts-dot1x)#sap mode-list null
6500(config-if-cts-dot1x)#propagate sgt
驗證
PAC Download
6500#show cts pac
AID: 6F5719523570B8D229F23073404E2D37
PAC-Info:
PAC-type = Cisco Trustsec
AID: 6F5719523570B8D229F23073404E2D37
I-ID: 6500
A-ID-Info: ISE 2.2p1
Credential Lifetime: 04:27:29 UTC Oct 26 2017
PAC-Opaque: 000200B000030001000400106F5719523570B8D229F23073404E2D370006009400030100801062F6BE70E2CCB6B0D25BFC81CB5D00000013597A55C100093A8059F0E1A3FAF83A2B7C8332479B7324C0FDC4CBAE9AE4AFD19C614A7DB13C9DBD06798A344423897745F0F91F19489772E543ED205A9CD0F276A96C4505BF34CB75F132377FE770B77A3D822842DFE3A0A858130612D08DD58965B09C352E33E74DB3F6B5C7E1F6EC8C30FF215A6FEB3EA7BBC95E
Refresh timer is set for 12w5d
Environment Data
6500#show cts environment-data
CTS Environment Data
====================
Current state = COMPLETE
Last status = Successful
Local Device SGT:
SGT tag = 2-02:TrustSec_Devices
Server List Info:
Installed list: CTSServerList1-0001, 1 server(s):
*Server: 14.36.143.18, port 1812, A-ID 6F5719523570B8D229F23073404E2D37
Status = ALIVE
auto-test = TRUE, keywrap-enable = FALSE, idle-time = 60 mins, deadtime = 20 secs
Multicast Group SGT Table:
Security Group Name Table:
0-fb:Unknown
2-fb:TrustSec_Devices
3-fb:Network_Services
4-fb:Employees
5-fb:Contractors
6-fb:Guests
7-fb:Production_Users
8-fb:Developers
9-fb:Auditors
10-fb:Point_of_Sale_Systems
11-fb:Production_Servers
12-fb:Development_Servers
13-fb:Test_Servers
14-fb:PCI_Servers
15-fb:BYOD
255-fb:Quarantined_Systems
Environment Data Lifetime = 86400 secs
Last update time = 20:28:36 UTC Thu Jul 27 2017
Env-data expires in 0:23:47:05 (dd:hr:mm:sec)
Env-data refreshes in 0:23:47:05 (dd:hr:mm:sec)
Cache data applied = NONE
State Machine is running
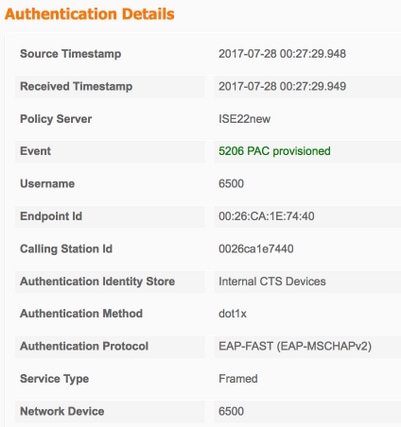
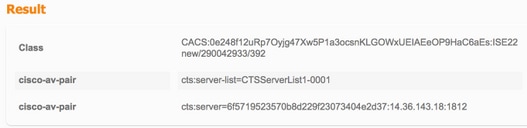
ISE 即時記錄
Operations > RADIUS > Live Logs
PAC調配


TrustSec資料下載





非種子裝置配置(3560X)
TrustSec Credentials
3560X#cts credentials id 3560X password Cisc0123
AAA configuration
3560X(config)#aaa new-model
3560X(config)#aaa authentication dot1x default group radius
3560X(config)#aaa authorization network default group radius
3560X(config)#aaa accounting identity default start-stop group radius
Recognize and use vendor-specific attributes
3560X(config)#radius-server vsa send authentication
Enable Change of Authorization
3560X(config)#aaa server radius dynamic-author
3560X(config-locsvr-da-radius)#client 14.36.143.18 server-key Cisc0123
Enable 802.1X
3560X(config)#dot1x system-auth-control
Switchport TrustSec Configuration
3560X(config)#int gi0/24
3560X(config-if)#switchport trunk encapsulation dot1q
3560X(config-if)#switchport mode trunk
3560X(config-if)#cts dot1x
3560X(config-if-cts-dot1x)#sap mode-list null
3560X(config-if-cts-dot1x)#propagate sgt
驗證
Pac Download
3560X#show cts pac
AID: 6F5719523570B8D229F23073404E2D37
PAC-Info:
PAC-type = Cisco Trustsec
AID: 6F5719523570B8D229F23073404E2D37
I-ID: 3560X
A-ID-Info: ISE 2.2p1
Credential Lifetime: 05:32:57 UTC Oct 26 2017
PAC-Opaque: 000200B000030001000400106F5719523570B8D229F23073404E2D3700060094000301009F9B0624C0A0C5D2AFDAAE89C173D34300000013597A55C100093A8059F0E1A3FAF83A2B7C8332479B7324C0B224F18D8654C2DB14544B58296A0A97C7B52EB1B7C0725776FE16F715094AC8A766E1F6D16A2A151B70632D6EAB34C5E1874409779FADA53F5892AD4ACC3533B5A61F89D028C076D94B52744A328C23437306AF428162AC680742003C6BDDB207A08F57
Refresh timer is set for 11y42w
Environment Data
3560X#show cts environment-data
CTS Environment Data
====================
Current state = COMPLETE
Last status = Successful
Local Device SGT:
SGT tag = 2-02:TrustSec_Devices
Server List Info:
Installed list: CTSServerList1-0001, 1 server(s):
*Server: 14.36.143.18, port 1812, A-ID 6F5719523570B8D229F23073404E2D37
Status = ALIVE
auto-test = TRUE, keywrap-enable = FALSE, idle-time = 60 mins, deadtime = 20 secs
Multicast Group SGT Table:
Security Group Name Table:
0-d1:Unknown
2-d1:TrustSec_Devices
3-d1:Network_Services
4-d1:Employees
5-d1:Contractors
6-d1:Guests
7-d1:Production_Users
8-d1:Developers
9-d1:Auditors
10-d1:Point_of_Sale_Systems
11-d1:Production_Servers
12-d1:Development_Servers
13-d1:Test_Servers
14-d1:PCI_Servers
15-d1:BYOD
255-d1:Quarantined_Systems
Environment Data Lifetime = 86400 secs
Last update time = 02:41:21 UTC Mon Jan 2 2006
Env-data expires in 0:23:56:36 (dd:hr:mm:sec)
Env-data refreshes in 0:23:56:36 (dd:hr:mm:sec)
Cache data applied = NONE
State Machine is running
ISE 即時記錄
Operations > RADIUS > Live Logs
PAC調配

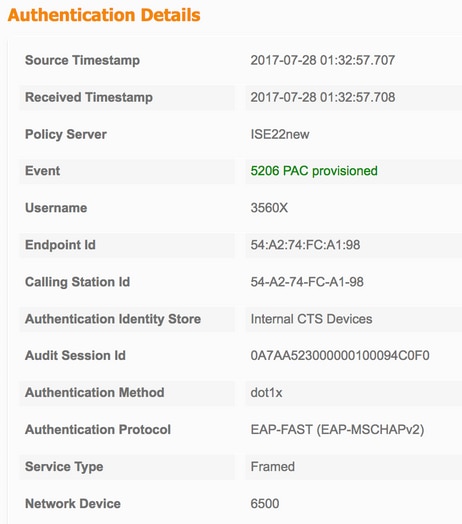
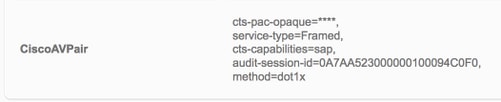
非種子驗證

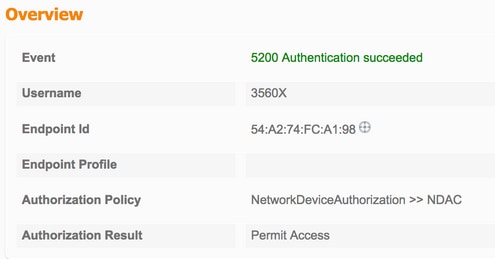

相互對等原則下載




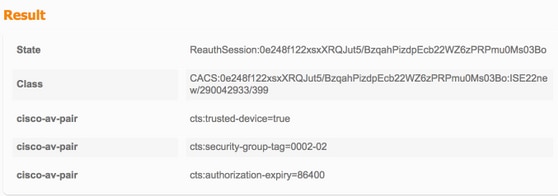
TrustSec資料下載






介面驗證
Seed (6500)
6500#show cts interface gi6/1
Global Dot1x feature is Enabled
Interface GigabitEthernet6/1:
CTS is enabled, mode: DOT1X
IFC state: OPEN
Interface Active for 00:38:50.744
Authentication Status: SUCCEEDED
Peer identity: "3560X"
Peer's advertised capabilities: "sap"
802.1X role: Authenticator
Authorization Status: SUCCEEDED
Peer SGT: 2:TrustSec_Devices
Peer SGT assignment: Trusted
SAP Status: SUCCEEDED
Dot1x Info for GigabitEthernet6/1
-----------------------------------
PAE = AUTHENTICATOR
Non-Seed (3560X)
3560X#show cts interface gi0/24
Global Dot1x feature is Enabled
Interface GigabitEthernet0/24:
CTS is enabled, mode: DOT1X
IFC state: OPEN
Interface Active for 00:08:51.317
Authentication Status: SUCCEEDED
Peer identity: "6500"
Peer's advertised capabilities: "sap"
802.1X role: Supplicant
Reauth period applied to link: Not applicable to Supplicant role
Authorization Status: SUCCEEDED
Peer SGT: 2:TrustSec_Devices
Peer SGT assignment: Trusted
SAP Status: SUCCEEDED
Version: 2
Dot1x Info for GigabitEthernet0/24
-----------------------------------
PAE = SUPPLICANT