簡介
本文檔介紹如何在CSM上使用LDAP身份驗證配置AnyConnect。
必要條件
需求
思科建議您瞭解以下主題:
- CSM 4.23
- AnyConnect配置
- SSL協定
採用元件
本文中的資訊係根據以下軟體和硬體版本:
- CSM 4.23
- ASA 5515
- AnyConnect 4.10.6090
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路運作中,請確保您瞭解任何指令可能造成的影響。
設定
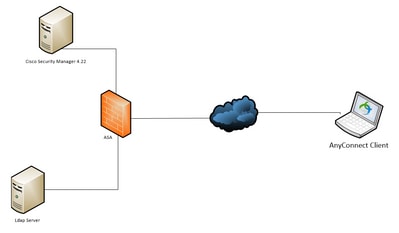
網路圖表
組態
步驟 1.配置SSLVPN訪問
轉至Policies > SSL VPN > Access:
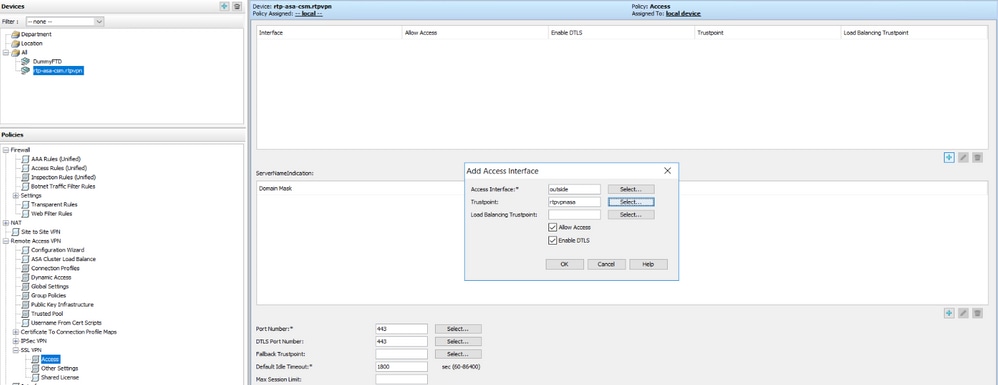
設定存取介面後,請務必按一下Save:

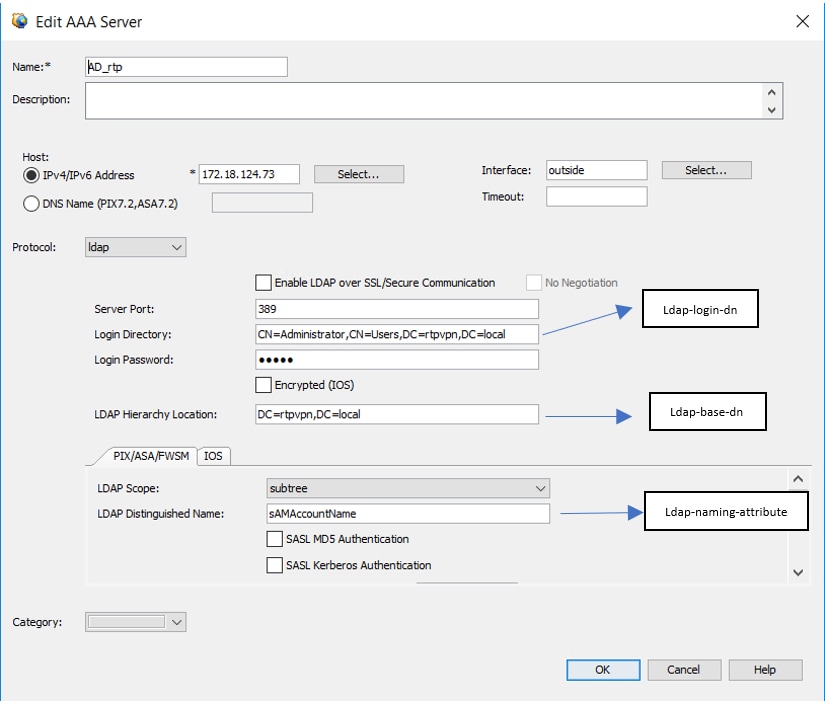
步驟 2.配置身份驗證伺服器
轉至Policy Object Manager > All Object Types > AAA Servers > Add。
配置伺服器的IP、源介面、登入目錄、登入密碼、LDAP層次結構位置、LDAP作用域和LDAP唯一判別名:
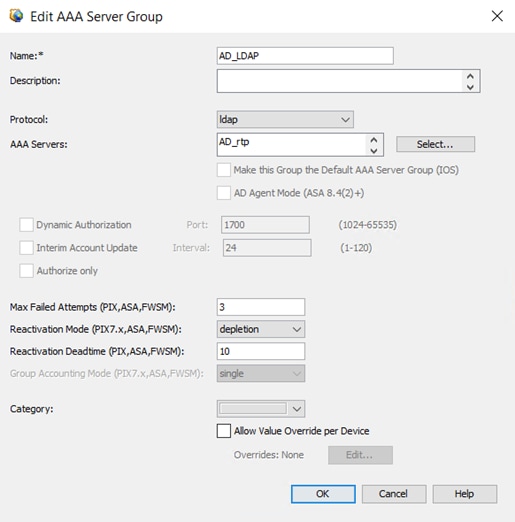
現在將AAA伺服器新增到AAA伺服器組>新增。
步驟 3.配置連線配置檔案
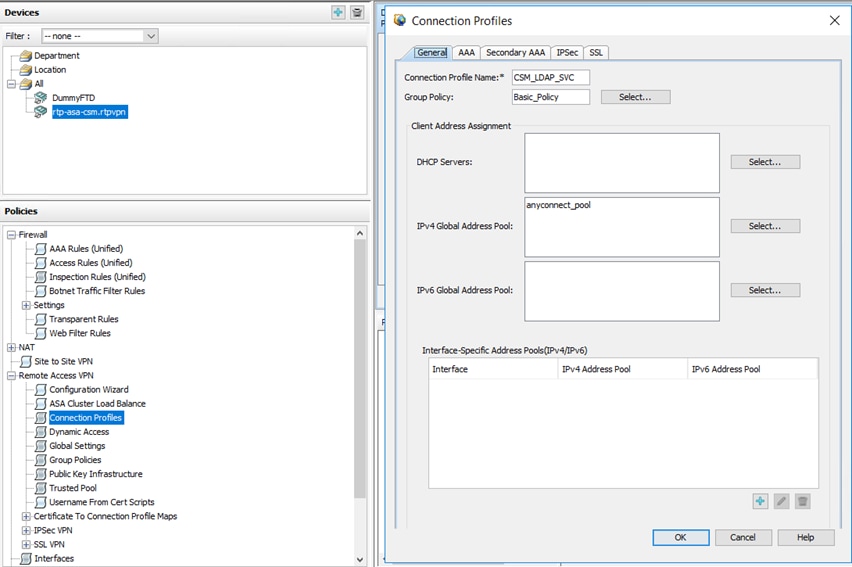
轉到Policies > Connection Profiles > Add。 
在此您必須配置IPv4全域性地址池(AnyConnect池)、組策略、AAA和組別名/URL:
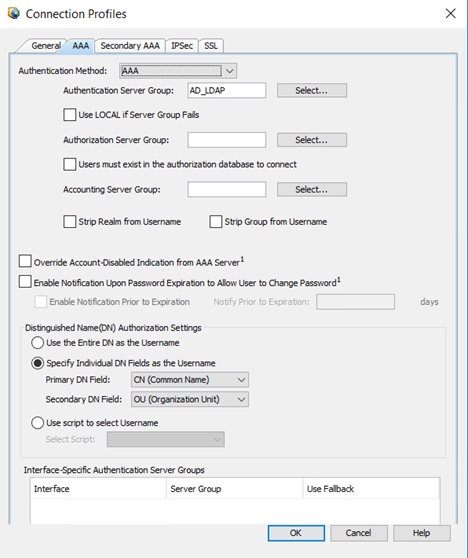
要選擇AAA伺服器,請按一下AAA頁籤,然後選擇在第2步中建立的伺服器:
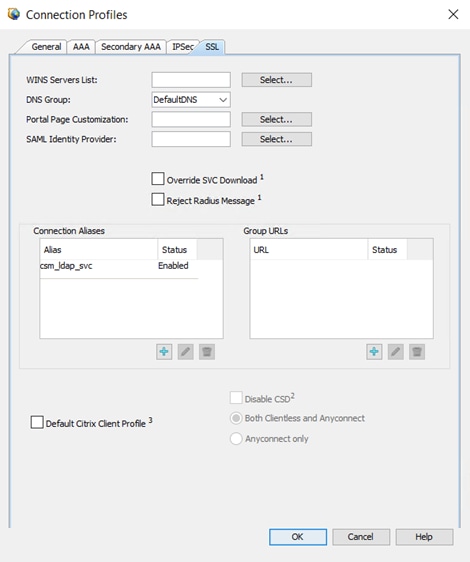
要在連線配置檔案中配置組別名/組url、dns或wins伺服器,請轉到SSL頁籤:
步驟 4.部署
點選部署圖示。
驗證
本節提供的資訊可用於驗證您的組態。
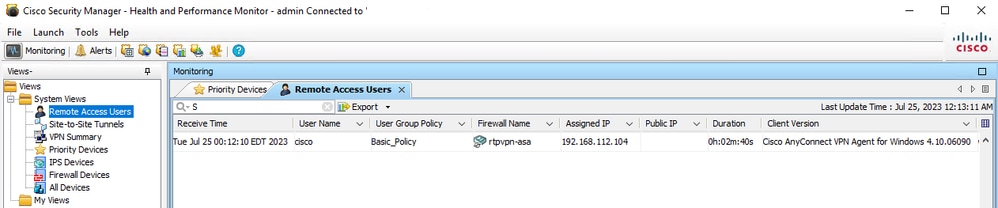
通過CSM訪問:
開啟Health and Performance Monitor > Tools > Device Selector > Select the ASA > Next > Select Remote Access Users
通過CLI:
ASA#show vpn-sessiondb anyconnect
Session Type: AnyConnect
Username : cisco Index : 23719
Assigned IP : 192.168.20.1 Public IP : 209.165.201.25
Protocol : AnyConnect-Parent SSL-Tunnel DTLS-Tunnel
License : AnyConnect Premium
Encryption : AnyConnect-Parent: (1)none SSL-Tunnel: (1)AES-GCM-256 DTLS-Tunnel: (1)AES-GCM-256
Hashing : AnyConnect-Parent: (1)none SSL-Tunnel: (1)SHA384 DTLS-Tunnel: (1)SHA384
Bytes Tx : 15856 Bytes Rx : 3545
Group Policy : Basic_Policy Tunnel Group : CSM_LDAP_SVC
Login Time : 10:29:42 UTC Tue Jul 25 2023
Duration : 0h:010m:16s
Inactivity : 0h:00m:00s
VLAN Mapping : N/A VLAN : none
Audt Sess ID : 0e26864905ca700064bf3396
Security Grp : none
疑難排解
為了檢查LDAP身份驗證或anyconnect建立期間可能出現的故障,您可以在CLI上執行以下命令:
debug ldap 255
debug webvpn anyconnect 255