簡介
本檔案介紹如何在Cisco Catalyst交換器9300上設定和驗證Cisco Inline Tagging功能。
需求
思科建議您瞭解以下主題:
- Cisco TrustSec(CTS)元件的基礎知識
-
Catalyst交換器CLI組態的基本知識
-
身分識別服務引擎(ISE)配置體驗
您必須在網路中部署思科ISE,終端使用者必須在有線連線時通過802.1x(或其他方法)向思科ISE進行身份驗證。思科ISE向您的有線網路進行身份驗證後分配安全組標籤(SGT)。
採用元件
本文中的資訊係根據以下軟體和硬體版本:
- 執行3.0 P5的Cisco身分識別服務引擎
- 運行17.03.02a的Cisco Catalyst 9300交換機
- 執行17.07.01的Cisco Catalyst 9300交換器
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路運作中,請確保您瞭解任何指令可能造成的影響。
背景資訊
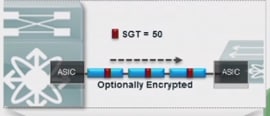
內聯標籤在接入層實施,因為這是資訊的第一個聯絡點。換句話說,您的所有終端裝置都連線到接入層。一旦接入層裝置完成分類,就有必要與實施該分類的裝置共用此資訊。為此, NAS可以向乙太網幀新增20個位元組。這是幀的CMD(思科後設資料)欄位。其中包含SGT。
設定
網路圖表
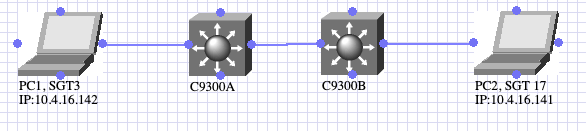 拓撲圖
拓撲圖
- PC1進行身份驗證,ISE動態分配SGT3。
- C9300A與C9300B的內嵌標籤
- PC2身份驗證和ISE動態分配SGT 17
- C9300B執行從SGT3到SGT17的ICMP流量。
內嵌標籤
C9300A
interface TwoGigabitEthernet1/0/4
switchport trunk allowed vlan 761
switchport mode trunk
cts manual
policy static sgt 2 trusted
end
C9300B
interface GigabitEthernet1/0/4
switchport trunk allowed vlan 761
switchport mode trunk
cts manual
policy static sgt 2 trusted
end
必須使用命令cts manual和policy static啟用內聯標籤。命令上使用的sgt可以是網路裝置的sgt或任何其它其佔位符。trusted命令的功能是指示交換機在接收到帶有CMD報頭的流量時遵守SGT。如果沒有trusted命令,交換機將使用定義的SGT標籤從該介面流過的所有流量。
支票
訪問會話下載SGT
電腦 1
Switch#show authentication session interface Tw1/0/3 details
Interface: TwoGigabitEthernet1/0/3
IIF-ID: 0x1FB0D90E
MAC Address: 507b.9df0.34bb
IPv6 Address: Unknown
IPv4 Address: 10.4.16.142
User-Name: 50-7B-9D-F0-34-BB
Status: Authorized
Domain: DATA
Oper host mode: multi-auth
Oper control dir: both
Session timeout: N/A
Common Session ID: 3D781F0A0000000F2AE95F4A
Acct Session ID: 0x00000005
Handle: 0x02000004
Current Policy: POLICY_Tw1/0/3
Local Policies:
Service Template: DEFAULT_LINKSEC_POLICY_SHOULD_SECURE (priority 150)
Security Policy: Should Secure
Server Policies:
SGT Value: 3
Method status list:
Method State
mab Authc Success
電腦 2
Switch#show authentication session interface Gi1/0/1 details
Interface: GigabitEthernet1/0/1
IIF-ID: 0x1D1CA5C7
MAC Address: 507b.9df8.02ed
IPv6 Address: fe80::114c:dce1:ffa1:1642
IPv4 Address: 10.4.16.141
User-Name: 50-7B-9D-F8-02-ED
Status: Authorized
Domain: DATA
Oper host mode: multi-auth
Oper control dir: both
Session timeout: N/A
Common Session ID: 21781F0A000000242AF41195
Acct Session ID: 0x00000004
Handle: 0x4300000f
Current Policy: POLICY_Gi1/0/1
Local Policies:
Service Template: DEFAULT_LINKSEC_POLICY_SHOULD_SECURE (priority 150)
Security Policy: Should Secure
Server Policies:
SGT Value: 17
Method status list:
Method State
mab Authc Success
交換機學習IP-SGT繫結
C9300A
Switch#show cts role-based sgt-map all
Active IPv4-SGT Bindings Information
IP Address SGT Source
============================================
10.4.16.142 3 LOCAL
C9300B
Switch#show cts role-based sgt-map all
Active IPv4-SGT Bindings Information
IP Address SGT Source
============================================
10.4.16.141 17 LOCAL
10.31.120.33 2 INTERNAL
C9300A和C9300B之間的授權狀態
C9300A
Switch#show cts interface Two 1/0/4
Global Dot1x feature is Disabled
Interface TwoGigabitEthernet1/0/4:
CTS is enabled, mode: MANUAL
IFC state: OPEN
Interface Active for 01:36:44.332
Authentication Status: NOT APPLICABLE
Peer identity: "unknown"
Peer's advertised capabilities: ""
Authorization Status: SUCCEEDED
Peer SGT: 2:TrustSec_Devices
Peer SGT assignment: Trusted
SAP Status: NOT APPLICABLE
Propagate SGT: Enabled
Cache Info:
Expiration : N/A
Cache applied to link : NONE
Statistics:
authc success: 0
authc reject: 0
authc failure: 0
authc no response: 0
authc logoff: 0
sap success: 0
sap fail: 0
authz success: 0
authz fail: 0
port auth fail: 0
L3 IPM: disabled.
C9300B
Switch#show cts interfac Gig 1/0/4
Global Dot1x feature is Disabled
Interface GigabitEthernet1/0/4:
CTS is enabled, mode: MANUAL
IFC state: OPEN
Interface Active for 01:34:18.433
Authentication Status: NOT APPLICABLE
Peer identity: "unknown"
Peer's advertised capabilities: ""
Authorization Status: SUCCEEDED
Peer SGT: 2:TrustSec_Devices
Peer SGT assignment: Trusted
SAP Status: NOT APPLICABLE
Propagate SGT: Enabled
Cache Info:
Expiration : N/A
Cache applied to link : NONE
Statistics:
authc success: 0
authc reject: 0
authc failure: 0
authc no response: 0
authc logoff: 0
sap success: 0
sap fail: 0
authz success: 0
authz fail: 0
port auth fail: 0
L3 IPM: disabled.
疑難排解
若要排除任何問題,請考慮:
- 幀始終在支援SGT的裝置的入口埠進行標籤。
- 在其他第2層服務(例如QoS)之前進行標籤過程。
- 無影響IP MTU/分段。
- L2幀MTU影響: ~ 40位元組(約1600位元組和1552位元組MTU)
- MACsec對於功能強大的硬體是可選的。
封包擷取/EPC
 內聯標籤流
內聯標籤流
如果要對內嵌標籤進行故障排除,需要在入口處捕獲資料包。

提示:如果您在SW的上行鏈路中使用了一個封包,您看不到該標籤,因為此封包包含在介面級別中,因此可以在應用標籤之前獲取EPC。

注意:C4500等裝置也有一些例外。由於C4500的架構,即使您在輸入介面取得pcap,它也無法偵測CMD標頭。對於此特定情況,可以使用Netflow、Netflow Trustsec配置
在C9300B的輸入連線埠上採用嵌入式封包擷取(EPC)
Switch#monitor capture test interface Gig 1/0/4 both
Switch#monitor capture test match any
Switch#monitor capture test start
<
> Switch#
monitor capture test stop
採用EPC後,可以使用show monitor capture buffer brief 命令檢查ICMP請求的幀號。
Switch#show monitor capture test buffer
..
..
44 17.059569 10.4.16.142 b^F^R 10.4.16.141 ICMP 86 Echo (ping) request id=0x0001, seq=147/37632, ttl=128
45 17.061079 10.4.16.141 b^F^R 10.4.16.142 ICMP 74 Echo (ping) reply id=0x0001, seq=147/37632, ttl=128 (request in 44)
..
..
從先前的輸出中觀察到ICMP資料包位於幀44中。現在可使用此命令運行:show monitor capture <name> buffer detailed | begin Frame <number>以檢視內容:
..
..
Frame 44: 86 bytes on wire (688 bits), 86 bytes captured (688 bits) on interface 0
Interface id: 0 (/tmp/epc_ws/wif_to_ts_pipe)
Interface name: /tmp/epc_ws/wif_to_ts_pipe
Encapsulation type: Ethernet (1)
Arrival Time: Jun 3, 2022 19:12:00.140014000 UTC
[Time shift for this packet: 0.000000000 seconds]
Epoch Time: 1654283520.140014000 seconds
[Time delta from previous captured frame: 0.362660000 seconds]
[Time delta from previous displayed frame: 0.362660000 seconds]
[Time since reference or first frame: 17.059569000 seconds]
Frame Number: 44
Frame Length: 86 bytes (688 bits)
Capture Length: 86 bytes (688 bits)
[Frame is marked: False]
[Frame is ignored: False]
[Protocols in frame: eth:ethertype:vlan:ethertype:cmd:ethertype:ip:icmp:data]
Ethernet II, Src: 50:7b:9d:f0:34:bb (50:7b:9d:f0:34:bb), Dst: 50:7b:9d:f8:02:ed (50:7b:9d:f8:02:ed)
Destination: 50:7b:9d:f8:02:ed (50:7b:9d:f8:02:ed)
Address: 50:7b:9d:f8:02:ed (50:7b:9d:f8:02:ed)
.... ..0. .... .... .... .... = LG bit: Globally unique address (factory default)
.... ...0 .... .... .... .... = IG bit: Individual address (unicast)
Source: 50:7b:9d:f0:34:bb (50:7b:9d:f0:34:bb)
Address: 50:7b:9d:f0:34:bb (50:7b:9d:f0:34:bb)
.... ..0. .... .... .... .... = LG bit: Globally unique address (factory default)
.... ...0 .... .... .... .... = IG bit: Individual address (unicast)
Type: 802.1Q Virtual LAN (0x8100)
802.1Q Virtual LAN, PRI: 0, DEI: 0, ID: 761
000. .... .... .... = Priority: Best Effort (default) (0)
...0 .... .... .... = DEI: Ineligible
.... 0010 1111 1001 = ID: 761
Type: CiscoMetaData (0x8909)
Cisco MetaData <<<<<<<<<<<<<<<<<<<<<<< CMD header
Version: 1
Length: 1
Options: 0x0001
SGT: 3 <<<<<<<<<<<<<<<<<<<<<<<<<< SGT of PC1
Type: IPv4 (0x0800)
Internet Protocol Version 4, Src: 10.4.16.142, Dst: 10.4.16.141
0100 .... = Version: 4
.... 0101 = Header Length: 20 bytes (5)
Differentiated Services Field: 0x00 (DSCP: CS0, ECN: Not-ECT)
0000 00.. = Differentiated Services Codepoint: Default (0)
.... ..00 = Explicit Congestion Notification: Not ECN-Capable Transport (0)
Total Length: 60
Identification: 0x7d1f (32031)
Flags: 0x0000
0... .... .... .... = Reserved bit: Not set
.0.. .... .... .... = Don't fragment: Not set
..0. .... .... .... = More fragments: Not set
...0 0000 0000 0000 = Fragment offset: 0
Time to live: 128
Protocol: ICMP (1)
Header checksum: 0x887f [validation disabled]
[Header checksum status: Unverified]
Source: 10.4.16.142
Destination: 10.4.16.141
Internet Control Message Protocol
Type: 8 (Echo (ping) request)
Code: 0
Checksum: 0x4cc8 [correct]
[Checksum Status: Good]
Identifier (BE): 1 (0x0001)
Identifier (LE): 256 (0x0100)
Sequence number (BE): 147 (0x0093)
Sequence number (LE): 37632 (0x9300)
Data (32 bytes)
0000 61 62 63 64 65 66 67 68 69 6a 6b 6c 6d 6e 6f 70 abcdefghijklmnop
0010 71 72 73 74 75 76 77 61 62 63 64 65 66 67 68 69 qrstuvwabcdefghi
Data: 6162636465666768696a6b6c6d6e6f707172737475767761...
[Length: 32]
..
..
SGACL檢查
交換機僅下載與從不同方法(本地、SXP、內聯標籤等)獲取的IP-SGT繫結匹配的SGACL。C9300B從ISE動態學習目標安全組。它如何獲知源安全組?使用內嵌標籤。由於命令show cts role-based sgt-map all不會顯示從內聯標籤學習的SGT,因此您可以斷定,如果下載了SGACL,交換機將從源(內聯標籤)和目標(本地)安全組進行感知。
Switch#show cts role-based permissions
IPv4 Role-based permissions default:
Permit_IP_Log-00
IPv4 Role-based permissions from group 3:DataCenter to group 17:MedicalDevices:
denyJonsICMP-06 <<<<
DENY_PRINTER_80_04-01
permitJons-01
IPv4 Role-based permissions from group 16:IUH_Office to group 17:MedicalDevices:
denyJonsICMP-06
RBACL Monitor All for Dynamic Policies : FALSE
RBACL Monitor All for Configured Policies : FALSE
從PC1從PC2 ping時,ICMP被阻止:
cisco>ping -S 10.4.16.142 10.4.16.141
Pinging 10.4.16.141 from 10.4.16.142 with 32 bytes of data:
Request timed out.
Request timed out.
Request timed out.
Request timed out.
Ping statistics for 10.4.16.141:
Packets: Sent = 4, Received = 0, Lost = 4 (100% loss),
相關資訊