| Step 2 |
show
ip
mroute
Displays the
contents of the multicast routing (mroute) table.
Device# show ip mroute
IP Multicast Routing Table
Flags: D - Dense, S - Sparse, B - Bidir Group, s - SSM Group, C - Connected,
L - Local, P - Pruned, R - RP-bit set, F - Register flag,
T - SPT-bit set, J - Join SPT, M - MSDP created entry, E - Extranet,
X - Proxy Join Timer Running, A - Candidate for MSDP Advertisement,
U - URD, I - Received Source Specific Host Report,
Z - Multicast Tunnel, z - MDT-data group sender,
Y - Joined MDT-data group, y - Sending to MDT-data group,
G - Received BGP C-Mroute, g - Sent BGP C-Mroute,
N - Received BGP Shared-Tree Prune, n - BGP C-Mroute suppressed,
Q - Received BGP S-A Route, q - Sent BGP S-A Route,
V - RD & Vector, v - Vector, p - PIM Joins on route,
x - VxLAN group
Outgoing interface flags: H - Hardware switched, A - Assert winner, p - PIM Join
Timers: Uptime/Expires
Interface state: Interface, Next-Hop or VCD, State/Mode
(*, 203.0.113.1), 04:33:39/stopped, RP 0.0.0.0, flags: D
Incoming interface: Null, RPF nbr 0.0.0.0
Outgoing interface list:
GigabitEthernet0/0/2, Forward/Sparse-Dense, 04:33:39/stopped
GigabitEthernet0/0/0, Forward/Sparse-Dense, 04:33:39/stopped
(10.0.0.3, 203.0.113.1), 04:33:36/00:00:36, flags: T
Incoming interface: GigabitEthernet0/0/2, RPF nbr 10.1.1.3
Outgoing interface list:
GigabitEthernet0/0/0, Forward/Sparse-Dense, 04:33:36/stopped
(10.0.0.1, 203.0.113.1), 04:33:39/00:02:44, flags: T
Incoming interface: GigabitEthernet0/0/0, RPF nbr 10.1.1.0
Outgoing interface list:
GigabitEthernet0/0/2, Forward/Sparse-Dense, 04:33:39/stopped
|
| Step 3 |
show
ip
mroute
vrf
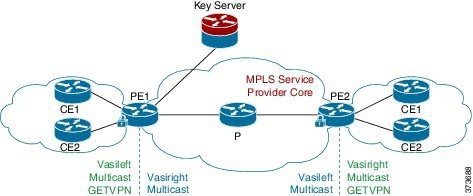
Filters the
output to display only the contents of the multicast routing table that
pertains to the Multicast VPN (MVPN) routing and forwarding (MVRF) instance
specified for the
vrf-name argument.
Device# show ip mroute vrf cust1
(10.2.1.1, 203.1.113.4), 00:40:09/00:02:44, flags: sTI
Incoming interface: vasileft1, RPF nbr 36.1.1.2
Outgoing interface list:
GigabitEthernet0/0/1.1, Forward/Sparse-Dense, 00:40:09/00:02:44
PE1#sh ip mroute vrf cust1-core
(10.2.1.1, 203.1.113.4), 04:22:09/00:02:50, flags: sT
Incoming interface: Tunnel0, RPF nbr 10.0.0.3
Outgoing interface list:
vasiright1, Forward/Sparse-Dense, 04:22:09/00:02:50
PE1#sh ip mroute
(*, 203.1.113.4), 21:08:36/stopped, RP 0.0.0.0, flags: DCZ
Incoming interface: Null, RPF nbr 0.0.0.0
Outgoing interface list:
GigabitEthernet0/0/0, Forward/Sparse-Dense, 04:27:50/stopped
MVRF cust1-core, Forward/Sparse-Dense, 21:06:53/stopped
(10.0.0.3, 203.1.113.4), 04:26:53/00:01:22, flags: TZ
Incoming interface: GigabitEthernet0/0/0, RPF nbr 10.1.1.1
Outgoing interface list:
MVRF cust1-core, Forward/Sparse-Dense, 04:26:53/stopped
|




 Feedback
Feedback