Contents
- IPsec IPv6 Phase 2 Support
- Finding Feature Information
- Information About IPsec IPv6 Phase 2 Support
- IPsec for IPv6
- IPv6 IPsec Site-to-Site Protection Using Virtual Tunnel Interface
- How to Configure IPsec IPv6 Phase 2 Support
- Configuring a VTI for Site-to-Site IPv6 IPsec Protection
- Creating an IKE Policy and a Preshared Key in IPv6
- Configuring ISAKMP Aggressive Mode
- Configuring an IPsec Transform Set and IPsec Profile
- Defining an ISAKMP Profile in IPv6
- Configuring IPv6 IPsec VTI
- Verifying IPsec Tunnel Mode Configuration
- Troubleshooting IPsec for IPv6 Configuration and Operation
- Configuration Examples for IPsec IPv6 Phase 2 Support
- Example: Configuring ISAKMP Aggressive Mode
- Example: Configuring an ISAKMP Profile in IPv6
- Example: Configuring a VTI for Site-to-Site IPv6 IPsec Protection
- Additional References
- Feature Information for IPsec IPv6 Phase 2 Support
IPsec IPv6 Phase 2 Support
Cisco IOS IPv6 security features for your Cisco networking devices can protect your network against degradation or failure and also against data loss or compromise resulting from intentional attacks and from unintended but damaging mistakes by well-meaning network users.
Cisco IOS IPsec functionality provides network data encryption at the IP packet level, offering a robust, standards-based security solution. IPsec provides data authentication and anti-replay services in addition to data confidentiality services.
IPsec is a mandatory component of IPv6 specification. OSPF for IPv6 provides IPsec authentication support and protection, and IPv6 IPsec tunnel mode and encapsulation is used to protect IPv6 unicast and multicast traffic. This document provides information about implementing IPsec in IPv6 security.
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the Feature Information Table at the end of this document.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
Information About IPsec IPv6 Phase 2 Support
IPsec for IPv6
IP Security, or IPsec, is a framework of open standards developed by the Internet Engineering Task Force (IETF) that provide security for transmission of sensitive information over unprotected networks such as the Internet. IPsec acts at the network layer, protecting and authenticating IP packets between participating IPsec devices (peers), such as Cisco routers. IPsec provides the following optional network security services. In general, local security policy will dictate the use of one or more of these services:
- Data confidentiality--The IPsec sender can encrypt packets before sending them across a network.
- Data integrity--The IPsec receiver can authenticate packets sent by the IPsec sender to ensure that the data has not been altered during transmission.
- Data origin authentication--The IPsec receiver can authenticate the source of the IPsec packets sent. This service depends upon the data integrity service.
- Antireplay--The IPsec receiver can detect and reject replayed packets.
With IPsec, data can be sent across a public network without observation, modification, or spoofing. IPsec functionality is similar in both IPv6 and IPv4; however, site-to-site tunnel mode only is supported in IPv6.
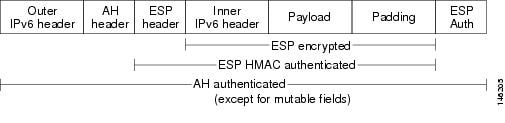
In IPv6, IPsec is implemented using the AH authentication header and the ESP extension header. The authentication header provides integrity and authentication of the source. It also provides optional protection against replayed packets. The authentication header protects the integrity of most of the IP header fields and authenticates the source through a signature-based algorithm. The ESP header provides confidentiality, authentication of the source, connectionless integrity of the inner packet, antireplay, and limited traffic flow confidentiality.
The Internet Key Exchange (IKE) protocol is a key management protocol standard that is used in conjunction with IPsec. IPsec can be configured without IKE, but IKE enhances IPsec by providing additional features, flexibility, and ease of configuration for the IPsec standard.
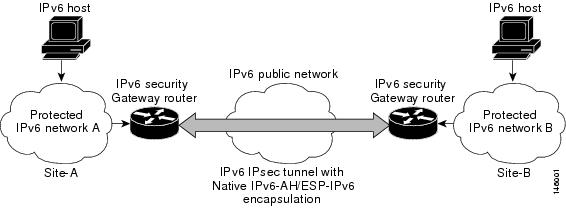
IKE is a hybrid protocol that implements the Oakley key exchange and Skeme key exchange inside the Internet Security Association Key Management Protocol (ISAKMP) framework (ISAKMP, Oakley, and Skeme are security protocols implemented by IKE) (see the figure below). This functionality is similar to the security gateway model using IPv4 IPsec protection.
IPv6 IPsec Site-to-Site Protection Using Virtual Tunnel Interface
The IPsec virtual tunnel interface (VTI) provides site-to-site IPv6 crypto protection of IPv6 traffic. Native IPv6 IPsec encapsulation is used to protect all types of IPv6 unicast and multicast traffic.
The IPsec VTI allows IPv6 routers to work as security gateways, establish IPsec tunnels between other security gateway routers, and provide crypto IPsec protection for traffic from internal networks when it is sent across the public IPv6 Internet (see the figure below). This functionality is similar to the security gateway model using IPv4 IPsec protection.
When the IPsec tunnel is configured, IKE and IPsec security associations (SAs) are negotiated and set up before the line protocol for the tunnel interface is changed to the UP state. The remote IKE peer is the same as the tunnel destination address; the local IKE peer will be the address picked from tunnel source interface which has the same IPv6 address scope as tunnel destination address.
The following figures shows the IPsec packet format.
How to Configure IPsec IPv6 Phase 2 Support
- Configuring a VTI for Site-to-Site IPv6 IPsec Protection
- Verifying IPsec Tunnel Mode Configuration
- Troubleshooting IPsec for IPv6 Configuration and Operation
Configuring a VTI for Site-to-Site IPv6 IPsec Protection
- Creating an IKE Policy and a Preshared Key in IPv6
- Configuring ISAKMP Aggressive Mode
- Configuring an IPsec Transform Set and IPsec Profile
- Defining an ISAKMP Profile in IPv6
- Configuring IPv6 IPsec VTI
Creating an IKE Policy and a Preshared Key in IPv6
Because IKE negotiations must be protected, each IKE negotiation begins by agreement of both peers on a common (shared) IKE policy. This policy states which security parameters will be used to protect subsequent IKE negotiations and mandates how the peers are authenticated.
After the two peers agree upon a policy, the security parameters of the policy are identified by an SA established at each peer, and these SAs apply to all subsequent IKE traffic during the negotiation.
You can configure multiple, prioritized policies on each peer--each with a different combination of parameter values. However, at least one of these policies must contain exactly the same encryption, hash, authentication, and Diffie-Hellman parameter values as one of the policies on the remote peer. For each policy that you create, you assign a unique priority (1 through 10,000, with 1 being the highest priority).
When the IKE negotiation begins, IKE searches for an IKE policy that is the same on both peers. The peer that initiates the negotiation will send all its policies to the remote peer, and the remote peer will try to find a match. The remote peer looks for a match by comparing its own highest priority policy against the policies received from the other peer. The remote peer checks each of its policies in order of its priority (highest priority first) until a match is found.
A match is made when both policies from the two peers contain the same encryption, hash, authentication, and Diffie-Hellman parameter values, and when the remote peer's policy specifies a lifetime that is less than or equal to the lifetime in the policy being compared. (If the lifetimes are not identical, the shorter lifetime--from the remote peer's policy--will be used.)
If a match is found, IKE will complete negotiation, and IPsec security associations will be created. If no acceptable match is found, IKE refuses negotiation and IPsec will not be established.
You should set the ISAKMP identity for each peer that uses preshared keys in an IKE policy.
When two peers use IKE to establish IPsec SAs, each peer sends its identity to the remote peer. Each peer sends either its hostname or its IPv6 address, depending on how you have set the ISAKMP identity of the router.
By default, a peer's ISAKMP identity is the IPv6 address of the peer. If appropriate, you could change the identity to be the peer's hostname instead. As a general rule, set the identities of all peers the same way--either all peers should use their IPv6 addresses or all peers should use their hostnames. If some peers use their hostnames and some peers use their IPv6 addresses to identify themselves to each other, IKE negotiations could fail if the identity of a remote peer is not recognized and a DNS lookup is unable to resolve the identity.
DETAILED STEPS
Configuring ISAKMP Aggressive Mode
You likely do not need to configure aggressive mode in a site-to-site scenario. The default mode is typically used.
DETAILED STEPS
Configuring an IPsec Transform Set and IPsec Profile
A transform set is a combination of security protocols and algorithms that is acceptable to the IPsec routers.
DETAILED STEPS
Defining an ISAKMP Profile in IPv6
DETAILED STEPS
Configuring IPv6 IPsec VTI
DETAILED STEPS
Verifying IPsec Tunnel Mode Configuration
DETAILED STEPS
Troubleshooting IPsec for IPv6 Configuration and Operation
DETAILED STEPS
Configuration Examples for IPsec IPv6 Phase 2 Support
- Example: Configuring ISAKMP Aggressive Mode
- Example: Configuring an ISAKMP Profile in IPv6
- Example: Configuring a VTI for Site-to-Site IPv6 IPsec Protection
Example: Configuring an ISAKMP Profile in IPv6
The following sample output shows the ISAKMP profiles that are defined on an IPv6 router.
Router# show crypto isakmp profile ISAKMP PROFILE tom Identities matched are: ipv6-address 2001:DB8:0:1::1/32 Certificate maps matched are: Identity presented is: ipv6-address fqdn keyring(s): <none> trustpoint(s): <all>
Example: Configuring a VTI for Site-to-Site IPv6 IPsec Protection
crypto isakmp policy 1 authentication pre-share ! crypto isakmp key myPreshareKey0 address ipv6 3FFE:2002::A8BB:CCFF:FE01:2C02/128 crypto isakmp keepalive 30 30 ! crypto ipsec transform-set 3des ah-sha-hmac esp-3des ! crypto ipsec profile profile0 set transform-set 3des ! ipv6 cef ! interface Tunnel0 ipv6 address 3FFE:1001::/64 eui-64 ipv6 enable ipv6 cef tunnel source Ethernet2/0 tunnel destination 3FFE:2002::A8BB:CCFF:FE01:2C02 tunnel mode ipsec ipv6 tunnel protection ipsec profile profile0
Additional References
Related Documents
Technical Assistance
| Description | Link |
|---|---|
|
The Cisco Support and Documentation website provides online resources to download documentation, software, and tools. Use these resources to install and configure the software and to troubleshoot and resolve technical issues with Cisco products and technologies. Access to most tools on the Cisco Support and Documentation website requires a Cisco.com user ID and password. |
Feature Information for IPsec IPv6 Phase 2 Support
The following table provides release information about the feature or features described in this module. This table lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
| Table 1 | Feature Information for IPsec IPv6 Phase 2 Support |
| Feature Name | Releases | Feature Information |
|---|---|---|
|
IPsec IPv6 Phase 2 Support |
12.4(4)T |
Features in this phase support tunnel mode for site-to-site IPsec protection of IPv6 traffic. This feature allows the use of IPv6 IPsec encapsulation to protect IPv6 unicast and multicast traffic. The following commands were introduced or modified: authentication (IKE policy), crypto ipsec profile, crypto isakmp key, crypto isakmp peer, crypto isakmp policy, crypto isakmp profile, crypto keyring, debug crypto ipv6 ipsec, encryption (IKE policy), group (IKE policy), hash (IKE policy), lifetime (IKE policy), match identity, pre-shared-key, self-identity, set aggressive-mode client-endpoint, set transform-set, show adjacency, show crypto engine, show crypto ipsec sa, show crypto isakmp peers, show crypto isakmp policy, show crypto isakmp profile, show crypto map, show crypto session, show crypto socket, show ipv6 access-list, show ipv6 cef, tunnel destination, tunnel mode, tunnel source. |
Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R)
Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental.

 Feedback
Feedback