PIX/ASA 7.x : Port Redirection(Forwarding) with nat, global, static and access-list Commands
Available Languages
Contents
Introduction
In order to maximize security when you implement Cisco PIX Security Appliance version 7.0, it is important to understand how packets pass between higher security interfaces and lower security interfaces when you use the nat-control, nat, global, static, access-list and access-group commands. This document explains the differences between these commands and how to configure Port Redirection(Forwarding) and the outside Network Address Translation (NAT) features in PIX software version 7.x, with the use of the command line interface or the Adaptive Security Device Manager (ASDM).
Note: Some options in ASDM 5.2 and later can appear different than the options in ASDM 5.1. Refer to the ASDM documentation for more information.
Prerequisites
Requirements
Refer to Allowing HTTPS Access for ASDM in order to allow the device to be configured by the ASDM.
Components Used
The information in this document is based on these software and hardware versions:
-
Cisco PIX 500 Series Security Appliance Software version 7.0 and later
-
ASDM version 5.x and later
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Related Products
You can also use this configuration with Cisco ASA Security Appliance version 7.x and later.
Conventions
Refer to the Cisco Technical Tips Conventions for more information on document conventions.
Network Diagram
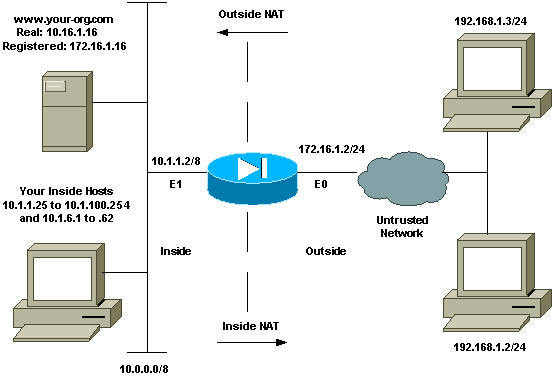
The IP addressing schemes used in this configuration are not legally routable on the Internet. They are RFC 1918 addresses which have been used in a lab environment.
Initial Configuration
The interface names are:
-
interface ethernet 0—nameif outside
-
interface ethernet 1—nameif inside
Note: In order to find additional information on the commands used in this document, use the Command Lookup Tool (registered customers only) .
Allow Outbound Access
Outbound access describes connections from a higher security level interface to a lower security level interface. This includes connections from inside to outside, inside to Demilitarized Zones (DMZs), and DMZs to outside. This can also include connections from one DMZ to another, as long as the connection source interface has a higher security level than the destination. Review the "security-level" configuration on the PIX interfaces in order to confirm this.
This example shows the security level and interface name configuration:
pix(config)#interface ethernet 0 pix(config-if)#security-level 0 pix(config-if)#nameif outside pix(config-if)#exit
PIX 7.0 introduces the nat-control command. You can use the nat-control command in configuration mode in order to specify if NAT is required for outside communications. With NAT control enabled, configuration of NAT rules is required in order to allow outbound traffic, as is the case with previous versions of PIX software. If NAT control is disabled (no nat-control), inside hosts can communicate with outside networks without the configuration of a NAT rule. However, if you have inside hosts that do not have public addresses, you still need to configure NAT for those hosts.
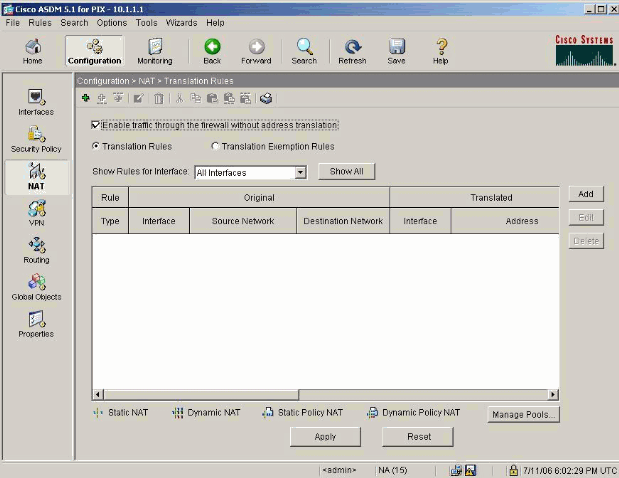
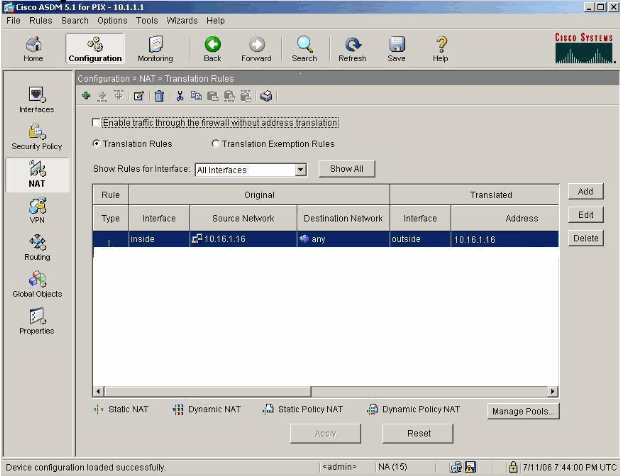
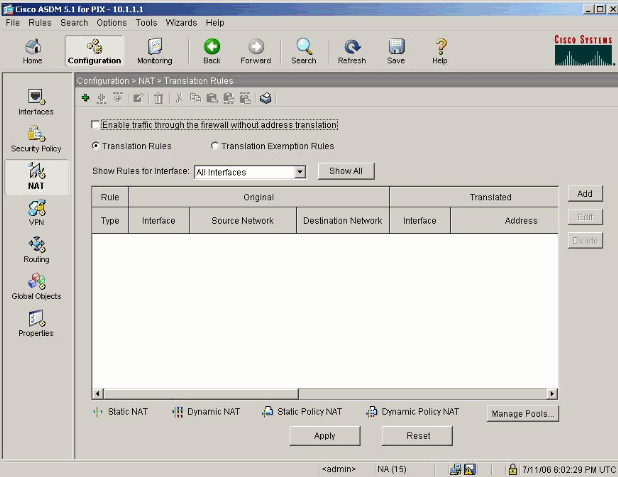
In order to configure NAT control with the use of ASDM, select the Configuration tab from the ASDM Home window and choose NAT from the features menu.
Enable traffic through the firewall without translation: This option was introduced in PIX version 7.0(1). When this option is checked, no nat-control command is issued in the configuration. This command means that no translation is required for traversing through the firewall. This option is usually checked only when internal hosts have public IP addresses or the network topology does not require internal hosts to be translated to any IP address.
If internal hosts have private IP addresses, then this option has to be unchecked so that internal hosts can get translated to a public IP address and access the Internet.
There are two policies that are required in order to allow outbound access with NAT control. The first one is a translation method. This can be a static translation with the use of the static command, or a dynamic translation with the use of a nat/global rule. This is not required if NAT control is disabled and your inside hosts have public addresses.
The other requirement for outbound access (which applies whether NAT control is enabled or disabled), is if there is an access control list (ACL) present. If an ACL is present, then it must allow the source host access to the destination host with the use of the specific protocol and port. By default, there are no access restrictions on outbound connections through the PIX. This means that if there is no ACL configured for the source interface, then by default, the outbound connection is allowed if there is a translation method configured.
Allow Inside Hosts Access to Outside Networks with NAT
This configuration gives all of the hosts on the subnet 10.1.6.0/24 access to the outside. In order to accomplish this, use the nat and global commands as this procedure demonstrates.
-
Define the inside group you want to include for NAT.
nat (inside) 1 10.1.6.0 255.255.255.0
-
Specify a pool of addresses on the outside interface to which the hosts defined in the NAT statement are translated.
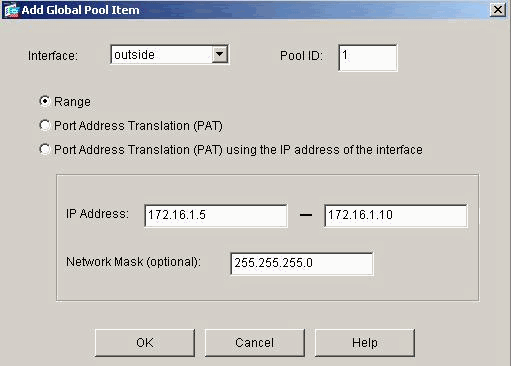
global (outside) 1 172.16.1.5-172.16.1.10 netmask 255.255.255.0
-
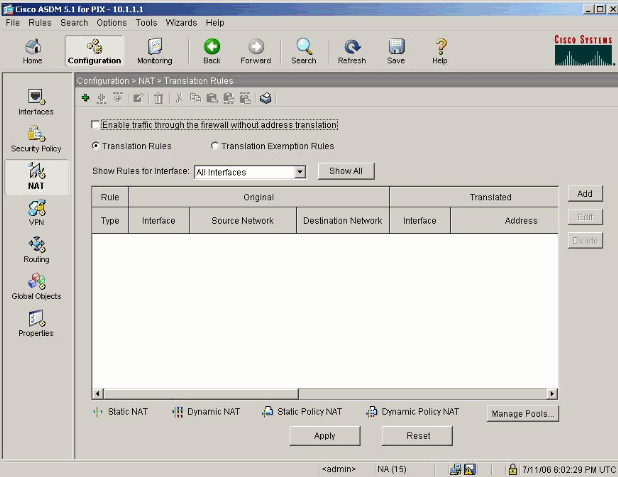
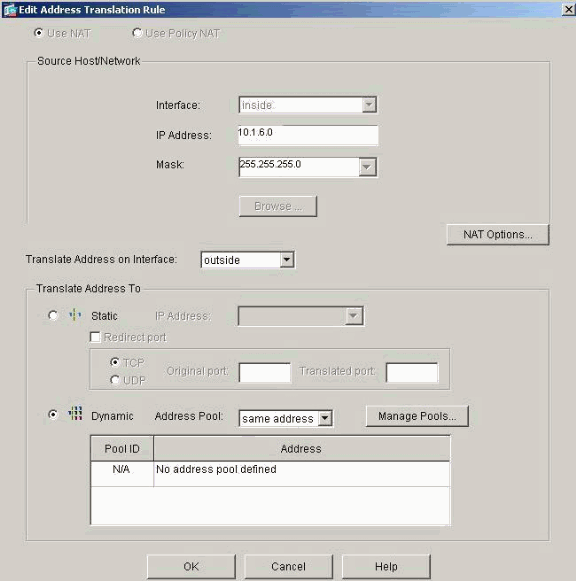
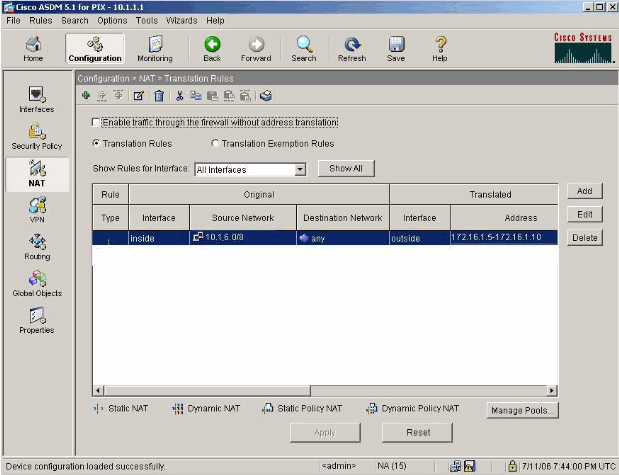
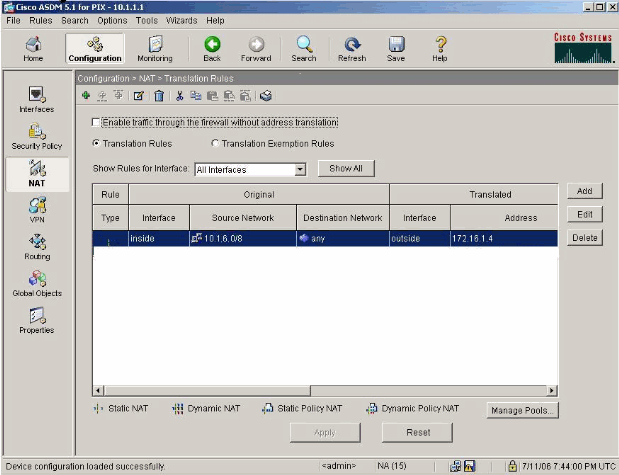
Use ASDM in order to create your global address pool. Choose Configuration > Features > NAT and uncheck Enable traffic through the firewall without address translation. Then click Add in order to configure the NAT Rule.
-
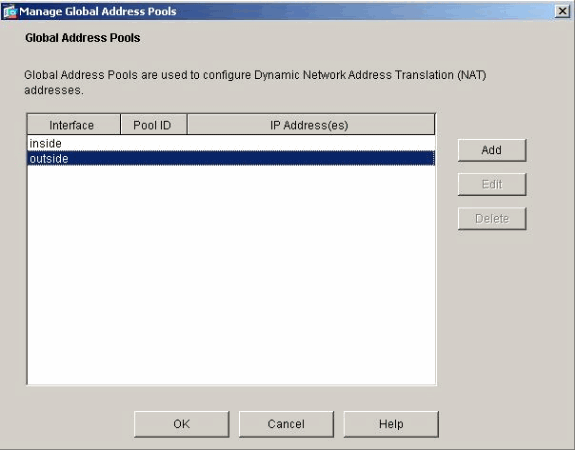
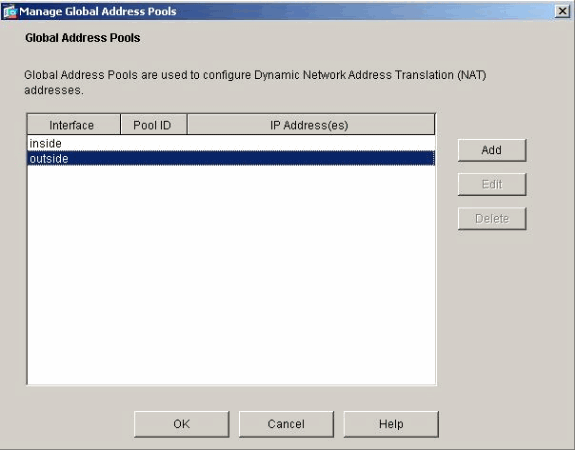
Click Manage Pools in order to define the NAT pool addresses.
-
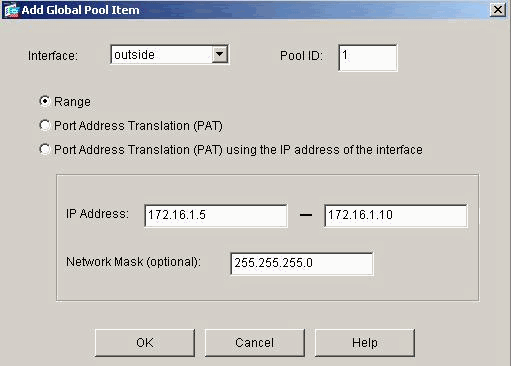
Choose Outside > Add, and choose a range to specify a pool of addresses.
-
Enter your address range, enter a Pool ID, and click OK.
-
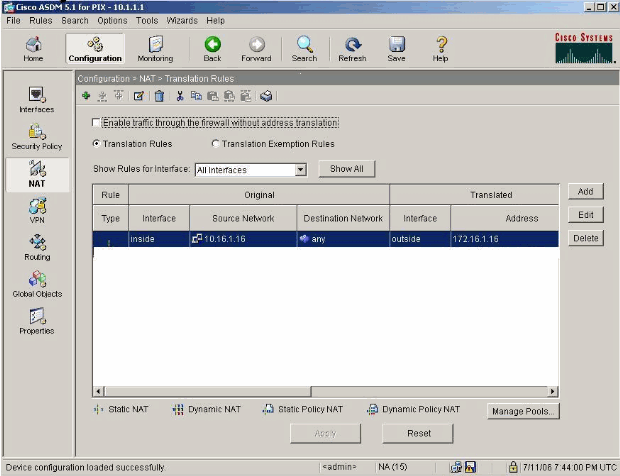
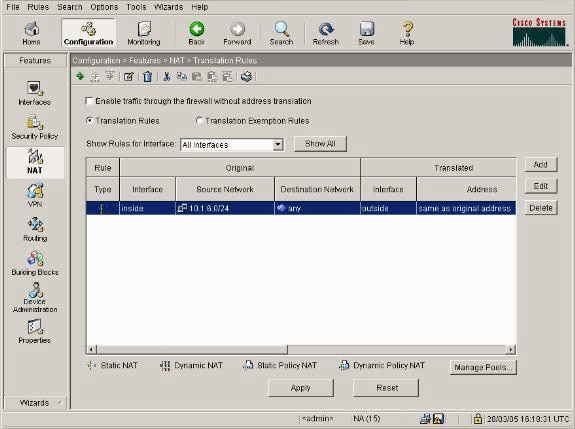
Choose Configuration > Features > NAT > Translation Rules in order to create the translation rule.
-
Choose Inside as the Source Interface, and enter the addresses you want to NAT.
-
For Translate Address on Interface, select Outside, choose Dynamic, and select the Address Pool you just configured.
-
Click OK.
-
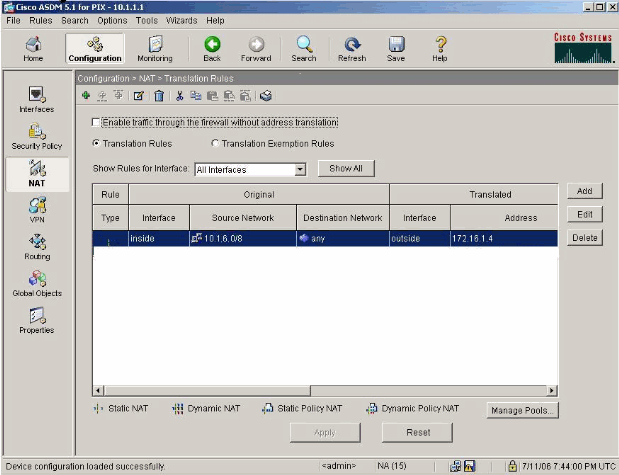
The translation appears in the Translation Rules at Configuration > Features > NAT > Translation Rules.
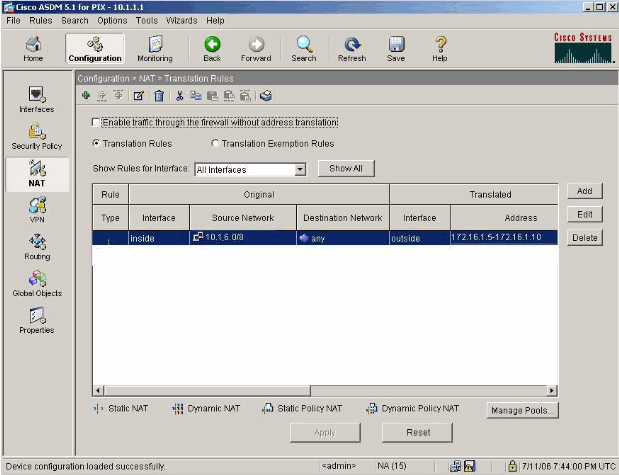
Now the hosts on the inside can access outside networks. When hosts from the inside initiate a connection to the outside, they are translated to an address from the global pool. The addresses are assigned from the global pool on a first-come, first-translated basis, and start with the lowest address in the pool. For example, if host 10.1.6.25 is the first to initiate a connection to the outside, it receives address 172.16.1.5. The next host out receives 172.16.1.6, and so on. This is not a static translation, and the translation times out after a period of inactivity as defined by the timeout xlate hh:mm:ss command. If there are more inside hosts than there are addresses in the pool, the final address in the pool is used for Port Address Translation (PAT).
Allow Inside Hosts Access to Outside Networks with the use of PAT
If you want inside hosts to share a single public address for translation, use PAT. If the global statement specifies one address, that address is port translated. The PIX allows one port translation per interface and that translation supports up to 65,535 active xlate objects to the single global address. Complete these steps in order to allow inside hosts access to outside networks with the use of PAT.
-
Define the inside group you want to include for PAT (when you use 0 0, you select all inside hosts.)
nat (inside) 1 10.1.6.0 255.255.255.0
-
Specify the global address you want to use for PAT. This can be the interface address.
global (outside) 1 172.16.1.4 netmask 255.255.255.0
-
In ASDM, choose Configuration > Features > NAT and uncheck Enable traffic through the firewall without address translation.
-
Click Add in order to configure the NAT rule.
-
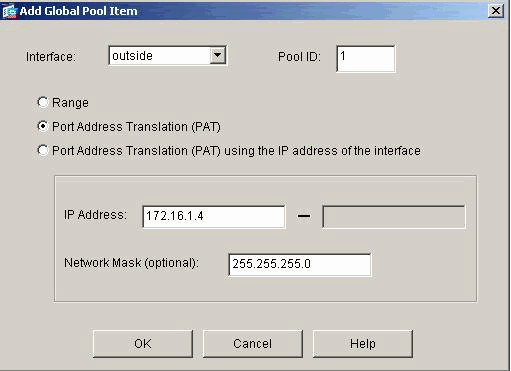
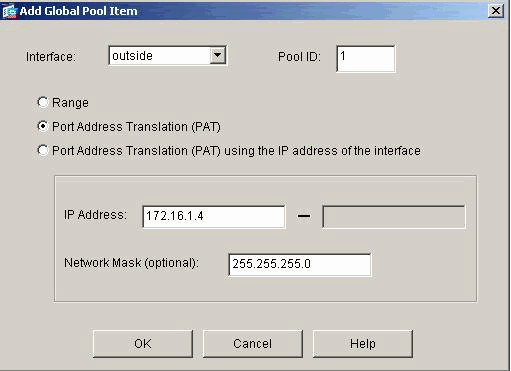
Choose Manage Pools in order to configure your PAT address.
-
Choose Outside > Add and click Port Address Translation (PAT) in order to configure a single address for PAT.
-
Enter an address, a Pool ID, and click OK.
-
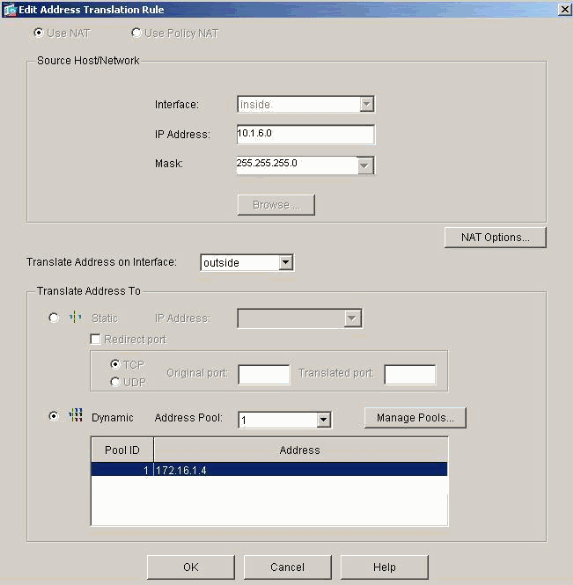
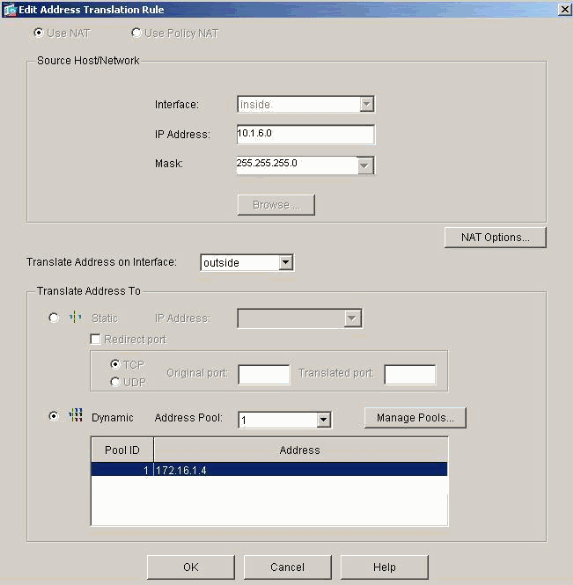
Choose Configuration > Features > NAT > Translation Rules in order to create the translation rule.
-
Select inside as the source interface, and enter the addresses you want to NAT.
-
For Translate Address on Interface, select outside, choose Dynamic, and select the Address Pool you just configured. Click OK.
-
The translation appears in the Translation Rules at Configuration > Features > NAT > Translation Rules.
There are a few things to consider when you use PAT.
-
The IP addresses you specify for PAT cannot be in another global address pool.
-
PAT does not work with H.323 applications, caching nameservers, and Point-to-Point Tunneling Protocol (PPTP). PAT works with Domain Name Service (DNS), FTP and passive FTP, HTTP, mail, remote-procedure call (RPC), rshell, Telnet, URL filtering, and outbound traceroute.
-
Do not use PAT when you need to run multimedia applications through the firewall. Multimedia applications can conflict with port mappings that PAT provides.
-
In PIX software release 4.2(2), the PAT feature does not work with IP data packets that arrive in reverse order. PIX software release 4.2(3) corrects this problem.
-
IP addresses in the pool of global addresses specified with the global command require reverse DNS entries in order to ensure that all external network addresses are accessible through the PIX. In order to create reverse DNS mappings, use a DNS Pointer (PTR) record in the address-to-name mapping file for each global address. Without the PTR entries, sites can experience slow or intermittent Internet connectivity and FTP requests fail consistently.
For example, if a global IP address is 192.168.1.3 and the domain name for the PIX Security Appliance is pix.caguana.com, the PTR record is:
3.1.1.175.in-addr.arpa. IN PTR pix3.caguana.com 4.1.1.175.in-addr.arpa. IN PTR pix4.caguana.com & so on.
Restrict Inside Hosts Access to Outside Networks
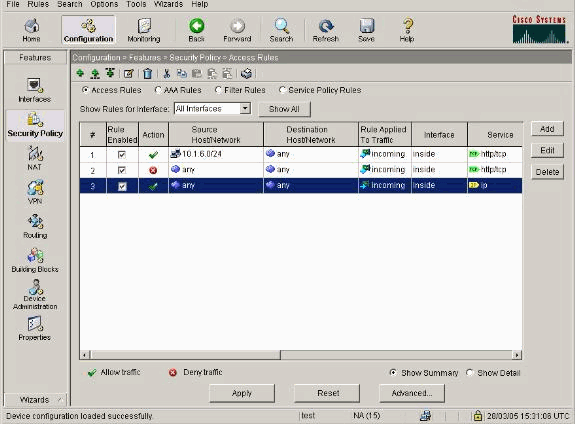
If there is a valid translation method defined for the source host, and no ACL defined for the source PIX interface, then the outbound connection is allowed by default. However, in some cases it is necessary to restrict outbound access based on source, destination, protocol, and/or port. In order to accomplish this, configure an ACL with the access-list command and apply it to the connection source PIX interface with the access-group command. You can apply PIX 7.0 ACLs in both inbound and outbound directions. This procedure is an example that allows outbound HTTP access for one subnet, but denies all other hosts HTTP access to the outside, while allowing all other IP traffic for everyone.
-
Define the ACL.
access-list acl_outbound permit tcp 10.1.6.0 255.255.255.0 any eq www access-list acl_outbound deny tcp any any eq www access-list acl_outbound permit ip any any
Note: PIX ACLs differ from ACLs on Cisco IOS® routers in that the PIX does not use a wildcard mask like Cisco IOS. It uses a regular subnet mask in the ACL definition. As with Cisco IOS routers, the PIX ACL has an implicit "deny all" at the end of the ACL.
Note: New access-list entries will be appended to the end of the existing ACEs. If you need a specific ACE processed first, you can use the line keyword in the access-list. This is an example command summary:
access-list acl_outbound line 1 extended permit tcp host 10.1.10.225 any
-
Apply the ACL to the inside interface.
access-group acl_outbound in interface inside
-
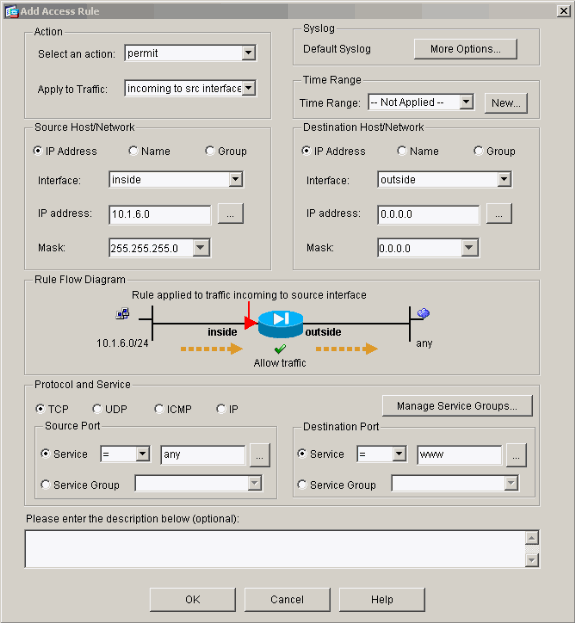
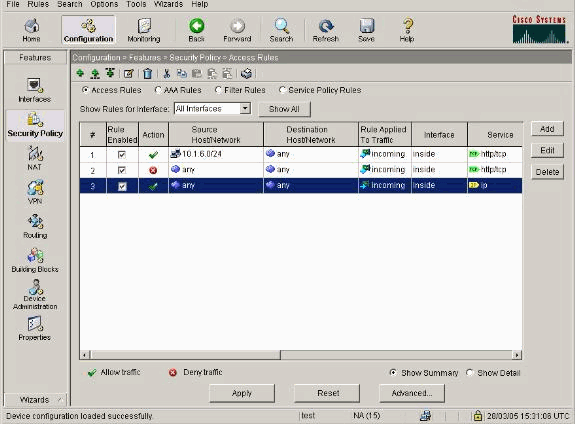
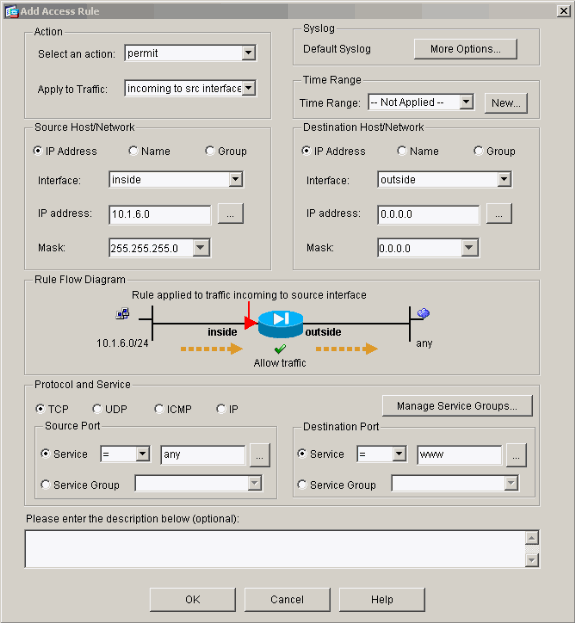
Use ASDM in order to configure the first access-list entry in step 1 to allow HTTP traffic from 10.1.6.0/24. Choose Configuration > Features > Security Policy > Access Rules.
-
Click Add, enter the information as this window shows, and click OK.
-
Once you enter the three access-list entries, choose Configuration > Feature > Security Policy > Access Rules in order to display these rules.
Allow Untrusted Hosts Access to Hosts on Your Trusted Network
Most organizations need to allow untrusted hosts access to resources in their trusted network. A common example is an internal web server. By default, the PIX denies connections from outside hosts to inside hosts. In order to allow this connection in NAT control mode, use the static command, with access-list and access-group commands. If NAT control is disabled, only the access-list and access-group commands are required, if no translation is performed.
Apply ACLs to interfaces with an access-group command. This command associates the ACL with the interface to examine traffic that flows in a particular direction.
In contrast to the nat and global commands which allow inside hosts out, the static command creates a two-way translation that allows inside hosts out and outside hosts in if you add the proper ACLs/groups.
In the PAT configuration examples shown in this document, if an outside host tries to connect to the global address, it can be used by thousands of inside hosts. The static command creates a one-to-one mapping. The access-list command defines what type of connection is allowed to an inside host and is always required when a lower security host connects to a higher security host. The access-list command is based on both port and protocol and can be very permissive or very restrictive, based on what the system administrator wants to achieve.
The network diagram in this document illustrates the use of these commands in order to configure the PIX to allow any untrusted hosts to connect to the inside web server, and allow untrusted host 192.168.1.1 access to an FTP service on the same machine.
Use ACLs on PIX Versions 7.0 and Later
Complete these steps for PIX software versions 7.0 and later with the use of ACLs.
-
If NAT control is enabled, define a static address translation for the inside web server to an outside/global address.
static (inside, outside) 172.16.1.16 10.16.1.16
-
Define which hosts can connect on which ports to your web/FTP server.
access-list 101 permit tcp any host 172.16.1.16 eq www access-list 101 permit tcp host 192.168.1.1 host 172.16.1.16 eq ftp
-
Apply the ACL to the outside interface.
access-group 101 in interface outside
-
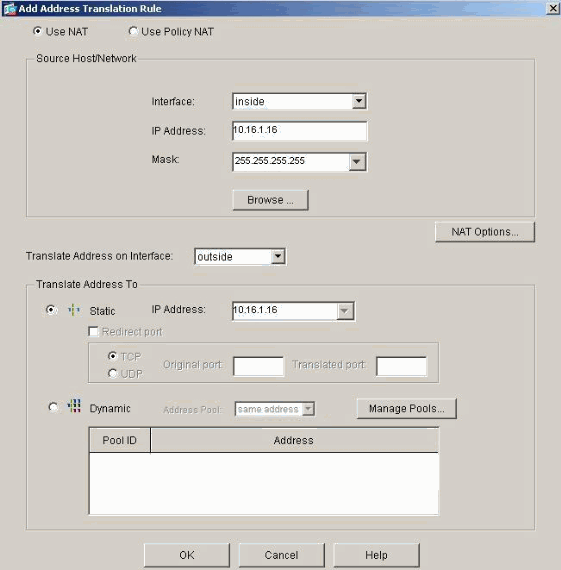
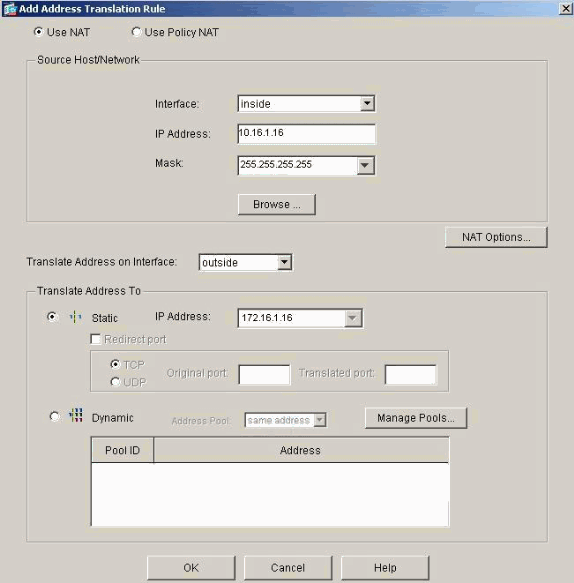
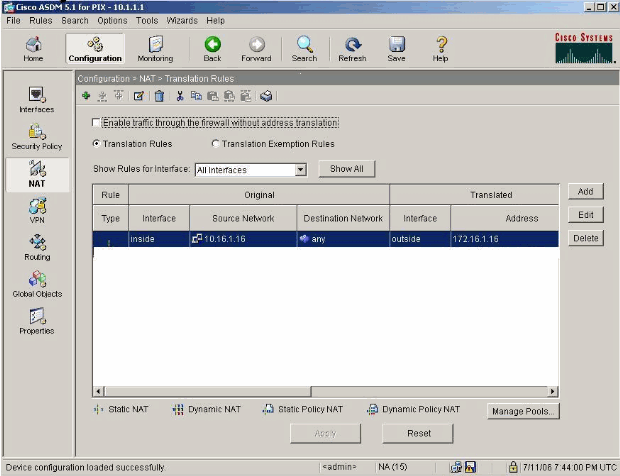
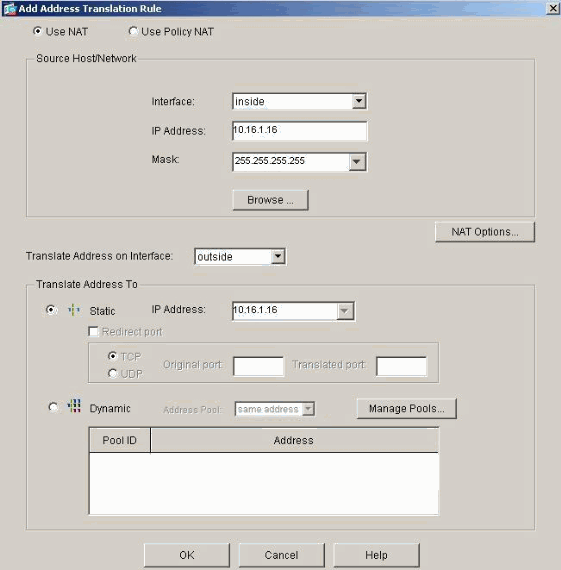
Choose Configuration > Features > NAT and click Add in order to create this static translation with the use of ASDM.
-
Select inside as the source interface, and enter the internal address for which you want to create a static translation.
-
Choose Static and enter the outside address you want to translate to in the IP address field. Click OK.
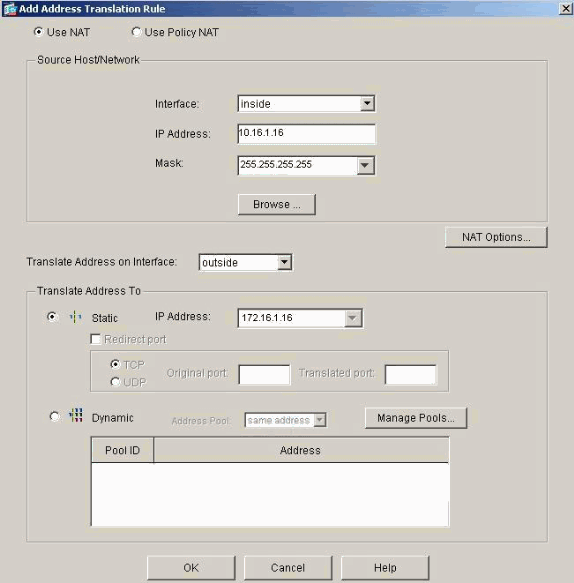
-
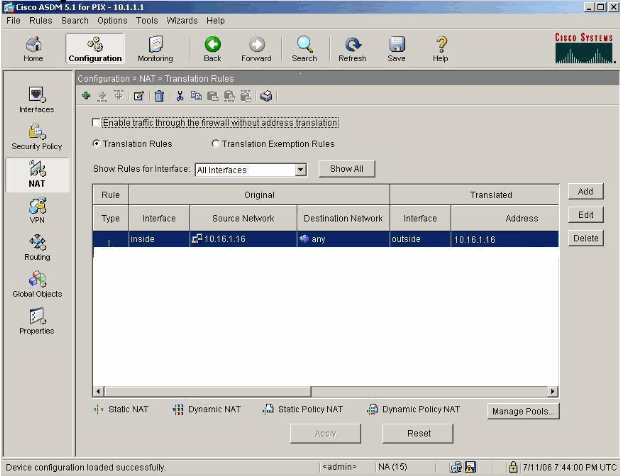
The translation appears in the Translation Rules when you choose Configuration > Features > NAT > Translation Rules.
-
Use the Restrict Inside Hosts Access to Outside Networks procedure in order to enter the access-list entries.
Note: Be careful when you implement these commands. If you implement the access-list 101 permit ip any any command, any host on the untrusted network can access any host on the trusted network with the use of IP as long as there is an active translation.
Disable NAT for Specific Hosts/Networks
If you use NAT control and have some public addresses on the inside network, and you want those specific inside hosts to go out to the outside without translation, you can disable NAT for those hosts, with nat 0 or static commands.
This is an example of the nat command:
nat (inside) 0 10.1.6.0 255.255.255.0
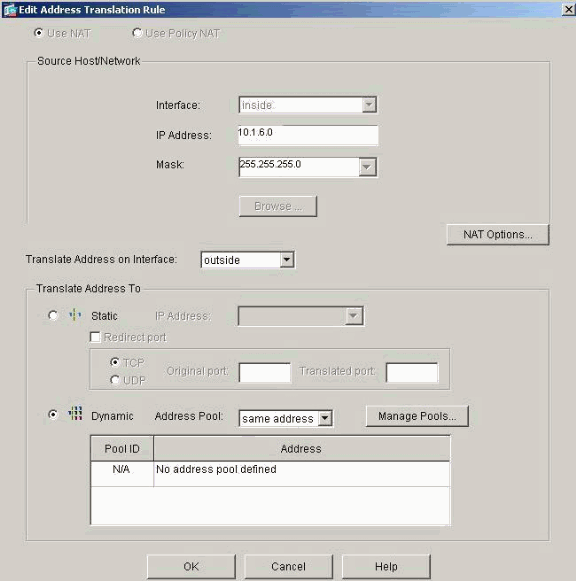
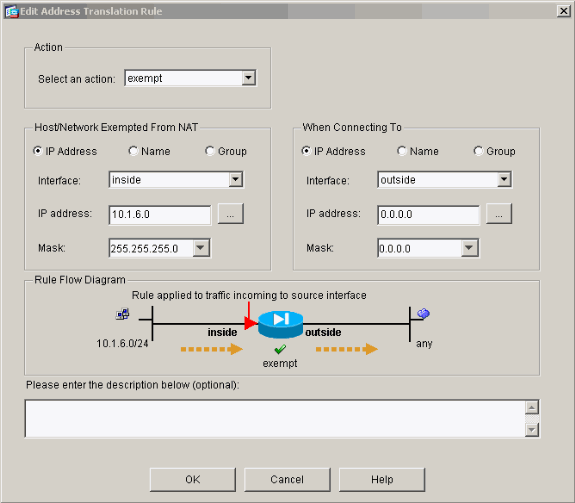
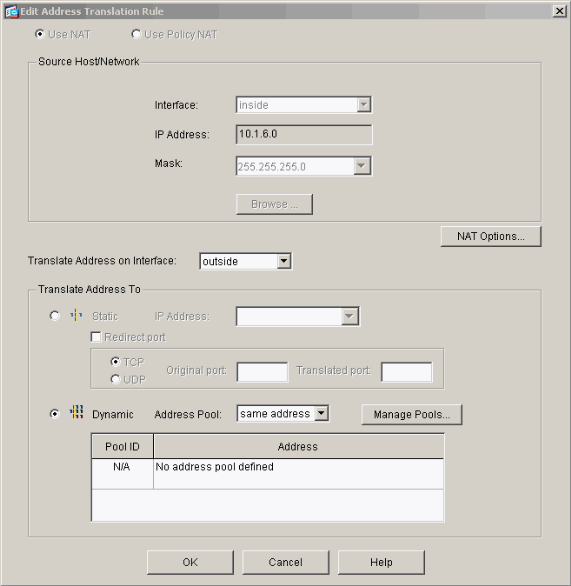
Complete these steps in order to disable NAT for specific hosts/networks with the use of ASDM.
-
Choose Configuration > Features > NAT and click Add.
-
Choose inside as the source interface, and enter the internal address/network for which you want to create a static translation.
-
Choose Dynamic and select the same address for Address Pool. Click OK.
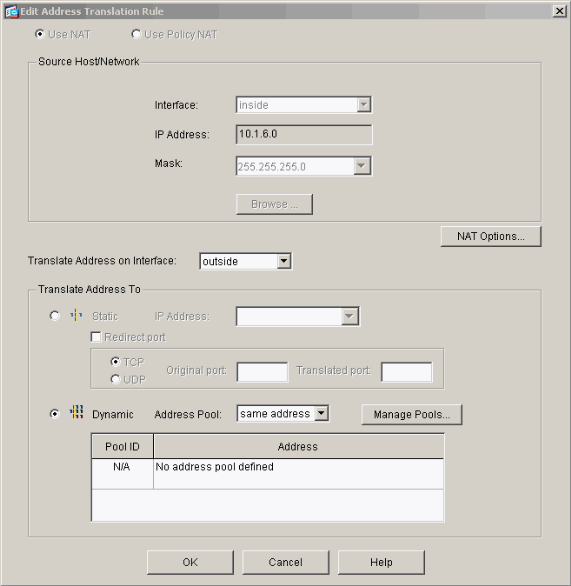
-
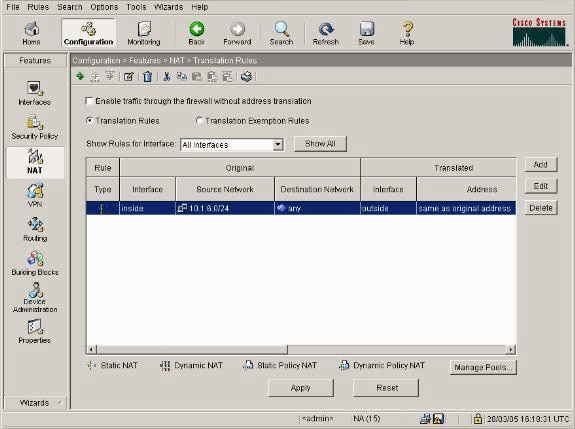
The new rule appears in the Translation Rules when you choose Configuration > Features > NAT > Translation Rules.
-
If you use ACLs, which allow more precise control of traffic that you should not translate (based on source/destination), use these commands.
access-list 103 permit ip 10.1.6.0 255.255.255.0 any nat (inside) 0 access-list 103
-
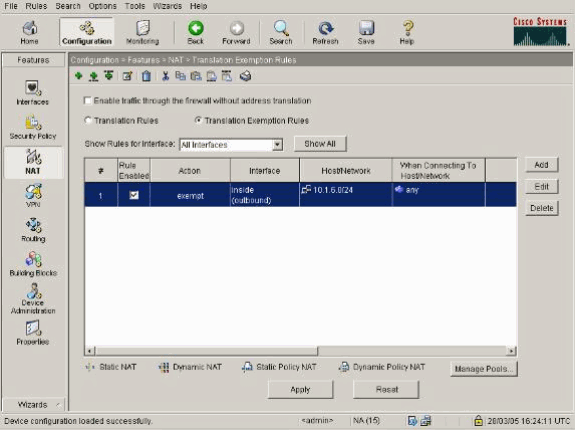
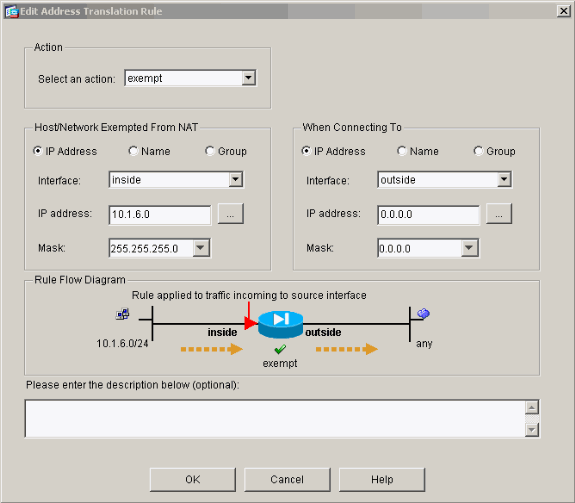
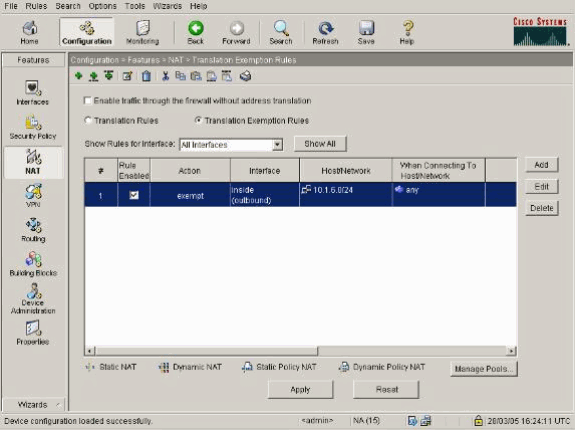
Use ASDM and choose Configuration > Features > NAT > Translation Rules.
-
Choose Translation Exemption Rules and click Add.
This example shows how to exempt traffic from the 10.1.6.0/24 network to anywhere from being translated.
-
Choose Configuration > Features > NAT > Translation Exemption Rules in order to display the new rules.
-
The static command for the web server changes as this example shows.
static (inside, outside) 10.16.1.16 10.16.1.16
-
From ASDM, choose Configuration > Features > NAT > Translation Rules.
-
Select Translation Rules and click Add. Enter the source address information, and select Static. Enter the same address in the IP Address field.
-
The translation appears in the Translation Rules when you choose Configuration > Features > NAT > Translation Rules.
-
If you use ACLs, use these commands.
access-list 102 permit tcp any host 10.16.1.16 eq www access-group 102 in interface outside
See the Restrict Inside Hosts Access to Outside Networks section of this document for additional information on the configuration of ACLs in ASDM.
Note the difference between when you use nat 0 when you specify network/mask as opposed to when you use an ACL that uses a network/mask that permits the initiation of connections from inside only. The use of ACLs with nat 0 permits the initiation of connections by inbound or outbound traffic. The PIX interfaces need to be in different subnets in order to avoid reachability issues.
Port Redirection(Forwarding) with Statics
In PIX 6.0, the Port Redirection(Forwarding) feature was added in order to allow outside users to connect to a particular IP address/port and have the PIX redirect the traffic to the appropriate inside server/port. The static command was modified. The shared address can be a unique address, a shared outbound PAT address, or shared with the external interface. This feature is available in PIX 7.0.
Note: Due to space limitations, commands are shown on two lines.
static [(internal_if_name, external_if_name)] {global_ip|interface}local_ip [netmask mask] [max_conns [emb_limit [norandomseq]]] static [(internal_if_name, external_if_name)] {tcp|udp} {global_ip|interface} global_port local_ip local_port [netmask mask] [max_conns [emb_limit [norandomseq]]]
Note: If the static NAT uses the outside IP (global_IP) address to translate, then this might cause a translation. Therefore, use the keyword interface instead of the IP address in the static translation.
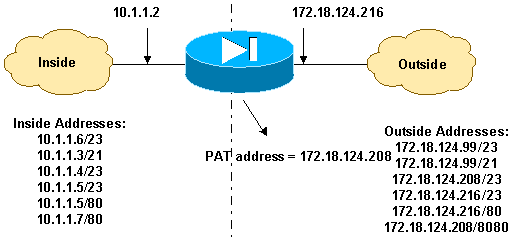
These Port Redirections(Forwardings) are in this network example:
-
External users direct Telnet requests to unique IP address 172.18.124.99, which the PIX redirects to 10.1.1.6.
-
External users direct FTP requests to unique IP address 172.18.124.99, which the PIX redirects to 10.1.1.3.
-
External users direct Telnet requests to PAT address 172.18.124.208, which the PIX redirects to 10.1.1.4.
-
External users direct Telnet request to PIX outside IP address 172.18.124.216, which the PIX redirects to 10.1.1.5.
-
External users direct HTTP request to PIX outside IP address 172.18.124.216, which the PIX redirects to 10.1.1.5.
-
External users direct HTTP port 8080 requests to PAT address 172.18.124.208, which the PIX redirects to 10.1.1.7 port 80.
This example also blocks the access of some users from inside to outside with ACL 100. This step is optional. All traffic is permitted outbound without the ACL in place.
Network Diagram - Port Redirection(Forwarding)
Partial PIX Configuration - Port Redirection
This partial configuration illustrates the use of Static Port Redirection(Forwarding). See the Port Redirection(Forwarding) network diagram.
| Partial PIX 7.x Configuration - Port Redirection(Forwarding) |
|---|
fixup protocol ftp 21 !--- Use of an outbound ACL is optional. access-list 100 permit tcp 10.1.1.0 255.255.255.128 any eq www access-list 100 deny tcp any any eq www access-list 100 permit tcp 10.0.0.0 255.0.0.0 any access-list 100 permit udp 10.0.0.0 255.0.0.0 host 172.18.124.100 eq domain access-list 101 permit tcp any host 172.18.124.99 eq telnet access-list 101 permit tcp any host 172.18.124.99 eq ftp access-list 101 permit tcp any host 172.18.124.208 eq telnet access-list 101 permit tcp any host 172.18.124.216 eq telnet access-list 101 permit tcp any host 172.18.124.216 eq www access-list 101 permit tcp any host 172.18.124.208 eq 8080 interface Ethernet0 nameif outside security-level 0 ip address 172.18.124.216 255.255.255.0 ! interface Ethernet1 nameif inside security-level 100 ip address 10.1.1.2 255.255.255.0 ! global (outside) 1 172.18.124.208 nat (inside) 1 0.0.0.0 0.0.0.0 0 0 static (inside,outside) tcp 172.18.124.99 telnet 10.1.1.6 telnet netmask 255.255.255.255 0 0 static (inside,outside) tcp 172.18.124.99 ftp 10.1.1.3 ftp netmask 255.255.255.255 0 0 static (inside,outside) tcp 172.18.124.208 telnet 10.1.1.4 telnet netmask 255.255.255.255 0 0 static (inside,outside) tcp interface telnet 10.1.1.5 telnet netmask 255.255.255.255 0 0 static (inside,outside) tcp interface www 10.1.1.5 www netmask 255.255.255.255 0 0 static (inside,outside) tcp 172.18.124.208 8080 10.1.1.7 www netmask 255.255.255.255 0 0 !--- Use of an outbound ACL is optional. access-group 100 in interface inside access-group 101 in interface outside |
Note: If PIX/ASA is configured with the sysopt noproxyarp outside command, then it does not allow the firewall to do the proxyarp and static NAT translations in PIX/ASA. In order to resolve this, remove the sysopt noproxyarp outside command in the PIX/ASA configuration and then update the ARP entries by using gratuitous ARP. This allows static NAT entries to work fine.
This procedure is an example of how to configure the Port Redirection(Forwarding) which allows external users direct Telnet requests to unique IP address 172.18.124.99, which the PIX redirects to 10.1.1.6.
-
Use ASDM and choose Configuration > Features > NAT > Translation Rules.
-
Select Translation Rules and click Add.
-
For Source Host/Network, enter the information for the inside IP address.
-
For Translate Address To, select Static, enter the outside IP address and check Redirect port.
-
Enter the pre-translation and post-translation port information (this example maintains port 23). Click OK.
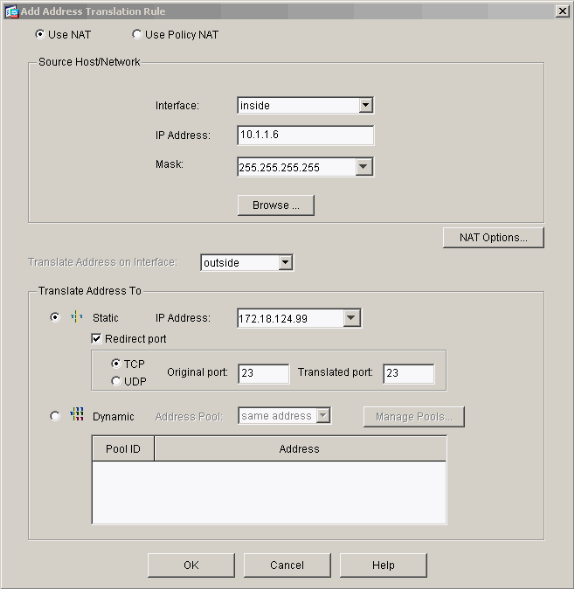
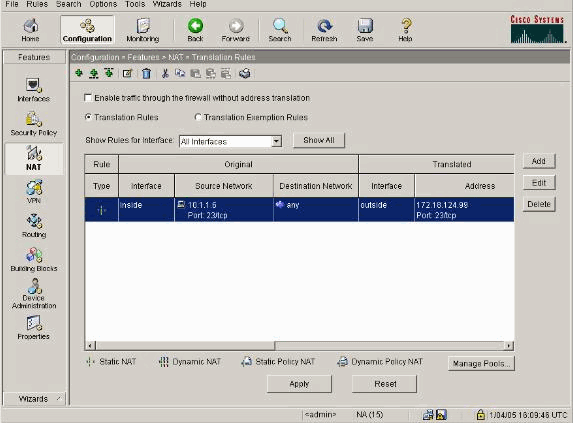
The translation appears in the Translation Rules when you choose Configuration > Features > NAT > Translation Rules.
Limit TCP/UDP Session using Static
If you want to limit the TCP or UDP sessions to the internal server placed in PIX/ASA, then use the static command.
Specifies the maximum number of simultaneous TCP and UDP connections for the entire subnet. The default is 0, which means unlimited connections (Idle connections are closed after the idle timeout specified by the timeout conn command.). This option does not apply to outside NAT. The security appliance only tracks connections from a higher security interface to a lower security interface.
Limiting the number of embryonic connections protects you from a DoS attack. The security appliance uses the embryonic limit to trigger TCP Intercept, which protects inside systems from a DoS attack perpetrated by flooding an interface with TCP SYN packets. An embryonic connection is a connection request that has not finished the necessary handshake between source and destination. This option does not apply to outside NAT. The TCP intercept feature applies only to hosts or servers on a higher security level. If you set the embryonic limit for outside NAT, the embryonic limit is ignored.
For example:
ASA(config)#static (inside,outside) tcp 10.1.1.1 www 10.2.2.2 www tcp 500 100 !--- The maximum number of simultaneous tcp connections the local IP !--- hosts are to allow is 500, default is 0 which means unlimited !--- connections. Idle connections are closed after the time specified !--- by the timeout conn command !--- The maximum number of embryonic connections per host is 100.
%PIX-3-201002: Too many connections on {static|xlate} global_address! econns nconns
This is a connection-related message. This message is logged when the maximum number of connections to the specified static address was exceeded. The econns variable is the maximum number of embryonic connections and nconns is the maximum number of connections permitted for the static or xlate.
The recommended action is to use the show static command in order to check the limit imposed on connections to a static address. The limit is configurable.
%ASA-3-201011: Connection limit exceeded 1000/1000 for inbound packet from 10.1.26.51/2393 to 10.0.86.155/135 on interface Outside
This error message is due to Cisco bug ID CSCsg52106 (registered customers only) . Refer to this bug for more information.
Time Based Access List
The creation of a time range does not restrict access to the device. The time-range command defines the time range only. After a time range is defined, you can attach it to traffic rules or an action.
In order to implement a time-based ACL, use the time-range command to define specific times of the day and week. Then use the with the access-list extended time-range command to bind the time range to an ACL.
The time range relies on the system clock of the security appliance. However, the feature works best with NTP synchronization.
After you have created a time range and entered time-range configuration mode, you can define time range parameters with the absolute and periodic commands. In order to restore default settings for the time-range command absolute and periodic keywords, use the default command in time-range configuration mode.
In order to implement a time-based ACL, use the time-range command to define specific times of the day and week. Then use the with the access-list extended command to bind the time range to an ACL. The next example binds an ACL named "Sales" to a time range named "New York Minute":
This example creates a time range named "New York Minute" and enters time-range configuration mode:
hostname(config)#time-range New_York_Minute hostname(config-time-range)#periodic weekdays 07:00 to 19:00 hostname(config)#access-list Sales line 1 extended deny ip any any time-range New_York_Minute hostname(config)#access-group Sales in interface inside
Information to Collect if You Open a Technical Support Case
| If you still need assistance and want to open a case with Cisco Technical Support, be sure to include this information for troubleshooting your PIX Security Appliance. |
|---|
|
Related Information
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback