ASDM Book 2: Cisco ASA Series Firewall ASDM Configuration Guide, 7.2
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- March 17, 2014
Chapter: Inspection of Basic Internet Protocols
Inspection of Basic Internet Protocols
This chapter describes how to configure application layer protocol inspection. Inspection engines are required for services that embed IP addressing information in the user data packet or that open secondary channels on dynamically assigned ports. These protocols require the ASA to do a deep packet inspection instead of passing the packet through the fast path. As a result, inspection engines can affect overall throughput.
Several common inspection engines are enabled on the ASA by default, but you might need to enable others depending on your network.
DNS Inspection
This section describes DNS application inspection. This section includes the following topics:
- Information About DNS Inspection
- Default Settings for DNS Inspection
- (Optional) Configuring a DNS Inspection Policy Map and Class Map
- Configuring DNS Inspection
Information About DNS Inspection
General Information About DNS
A single connection is created for multiple DNS sessions, as long as they are between the same two hosts, and the sessions have the same 5-tuple (source/destination IP address, source/destination port, and protocol). DNS identification is tracked by app_id, and the idle timer for each app_id runs independently. Because the app_id expires independently, a legitimate DNS response can only pass through the ASA within a limited period of time and there is no resource build-up.
DNS Inspection Actions
DNS inspection is enabled by default. You can customize DNS inspection to perform many tasks:
- Translate the DNS record based on the NAT configuration. For more information, see DNS and NAT.
- Enforce message length, domain-name length, and label length.
- Verify the integrity of the domain-name referred to by the pointer if compression pointers are encountered in the DNS message.
- Check to see if a compression pointer loop exists.
- Inspect packets based on the DNS header, type, class and more.
Default Settings for DNS Inspection
DNS inspection is enabled by default, using the preset_dns_map inspection class map:
- The maximum DNS message length is 512 bytes.
- The maximum client DNS message length is automatically set to match the Resource Record.
- DNS Guard is enabled, so the ASA tears down the DNS session associated with a DNS query as soon as the DNS reply is forwarded by the ASA. The ASA also monitors the message exchange to ensure that the ID of the DNS reply matches the ID of the DNS query.
- Translation of the DNS record based on the NAT configuration is enabled.
- Protocol enforcement is enabled, which enables DNS message format check, including domain name length of no more than 255 characters, label length of 63 characters, compression, and looped pointer check.
(Optional) Configuring a DNS Inspection Policy Map and Class Map
To match DNS packets with certain characteristics and perform special actions, create a DNS inspection policy map. You can also configure a DNS inspection class map to group multiple match criteria for reference within the inspection policy map. You can then apply the inspection policy map when you enable DNS inspection.
Prerequisites
If you want to match a DNS message domain name list, then create a regular expression using one of the methods below:
Detailed Steps
Step 1![]() Choose Configuration > Firewall > Objects > Inspect Maps > DNS.
Choose Configuration > Firewall > Objects > Inspect Maps > DNS.
The Configure DNS Maps pane appears.
The Add IPv6 Inspection Map dialog box appears.
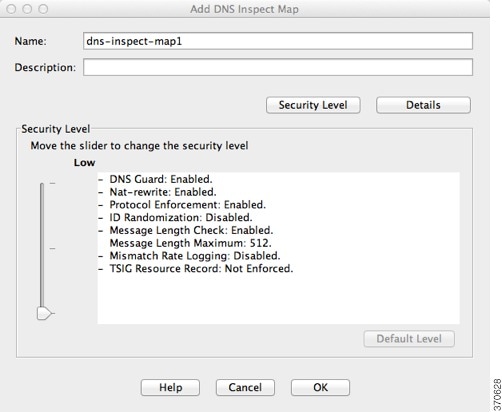
Step 3![]() In the Name field, name the inspection policy map.
In the Name field, name the inspection policy map.
Step 4![]() (Optional) In the Description field, add a description.
(Optional) In the Description field, add a description.
Step 5![]() Do one of the following:
Do one of the following:
Detailed Steps—Protocol Conformance
Step 1![]() Configure the following Protocol Conformance parameters:
Configure the following Protocol Conformance parameters:

Step 2![]() Enable DNS guard function —Enables DNS Guard. The ASA tears down the DNS session associated with a DNS query as soon as the DNS reply is forwarded by the ASA. The ASA also monitors the message exchange to ensure that the ID of the DNS reply matches the ID of the DNS query.
Enable DNS guard function —Enables DNS Guard. The ASA tears down the DNS session associated with a DNS query as soon as the DNS reply is forwarded by the ASA. The ASA also monitors the message exchange to ensure that the ID of the DNS reply matches the ID of the DNS query.
Step 3![]() Enable NAT re-write function —Translates the DNS record based on the NAT configuration.
Enable NAT re-write function —Translates the DNS record based on the NAT configuration.
Step 4![]() Enable protocol enforcement —Enables DNS message format check, including domain name length of no more than 255 characters, label length of 63 characters, compression, and looped pointer check.
Enable protocol enforcement —Enables DNS message format check, including domain name length of no more than 255 characters, label length of 63 characters, compression, and looped pointer check.
Step 5![]() Randomize the DNS identifier for DNS query —Randomizes the DNS identifier for a DNS query.
Randomize the DNS identifier for DNS query —Randomizes the DNS identifier for a DNS query.
Step 6![]() Enforce TSIG resource record to be present in DNS message —Requires a TSIG resource record to be present. Actions include:
Enforce TSIG resource record to be present in DNS message —Requires a TSIG resource record to be present. Actions include:
- Action: Drop packet or Log —Drop or log a non-conforming packet.
- Log: Enable or Disable —If you selected Drop packet, you can also enable logging.
Detailed Steps—Filtering
Step 1![]() Click the Filtering tab.
Click the Filtering tab.

Step 2![]() Global Settings: Drop packets that exceed specified maximum length (global) —Sets the maximum DNS message length, from 512 to 65535 bytes.
Global Settings: Drop packets that exceed specified maximum length (global) —Sets the maximum DNS message length, from 512 to 65535 bytes.
Step 3![]() Server Settings: Drop packets that exceed specified maximum length and Drop packets sent to server that exceed length indicated by the RR —Sets the maximum server DNS message length, from 512 to 65535 bytes, or sets the maximum length to the value in the Resource Record. If you enable both settings, the lower value is used.
Server Settings: Drop packets that exceed specified maximum length and Drop packets sent to server that exceed length indicated by the RR —Sets the maximum server DNS message length, from 512 to 65535 bytes, or sets the maximum length to the value in the Resource Record. If you enable both settings, the lower value is used.
Step 4![]() Client Settings: Drop packets that exceed specified maximum length and Drop packets sent to server that exceed length indicated by the RR —Sets the maximum client DNS message length, from 512 to 65535 bytes, or sets the maximum length to the value in the Resource Record. If you enable both settings, the lower value is used.
Client Settings: Drop packets that exceed specified maximum length and Drop packets sent to server that exceed length indicated by the RR —Sets the maximum client DNS message length, from 512 to 65535 bytes, or sets the maximum length to the value in the Resource Record. If you enable both settings, the lower value is used.
Detailed Steps—Mismatch Rate
Step 1![]() Click the Mismatch Rate tab.
Click the Mismatch Rate tab.

Step 2![]() Enable logging when DNS ID mismatch rate exceeds specified rate —Enables logging for excessive DNS ID mismatches, where the Mismatch Instance Threshold and Time Interval fields specify the maximum number of mismatch instances per x seconds before a system
Enable logging when DNS ID mismatch rate exceeds specified rate —Enables logging for excessive DNS ID mismatches, where the Mismatch Instance Threshold and Time Interval fields specify the maximum number of mismatch instances per x seconds before a system![]() message log is sent.
message log is sent.
Detailed Steps—Inspections
Step 1![]() Click the Inspections tab.
Click the Inspections tab.

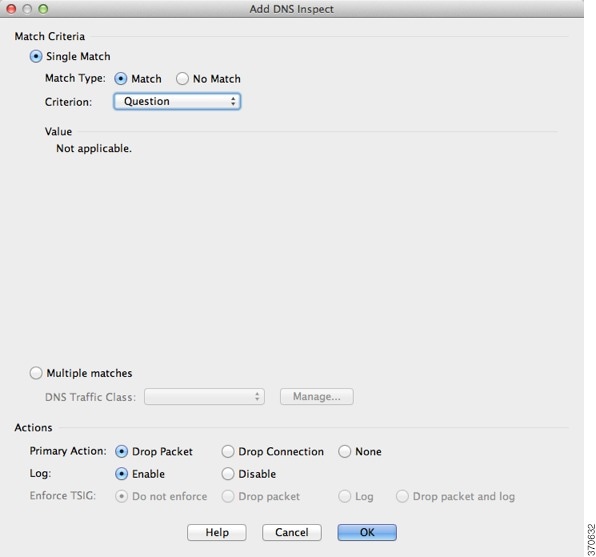
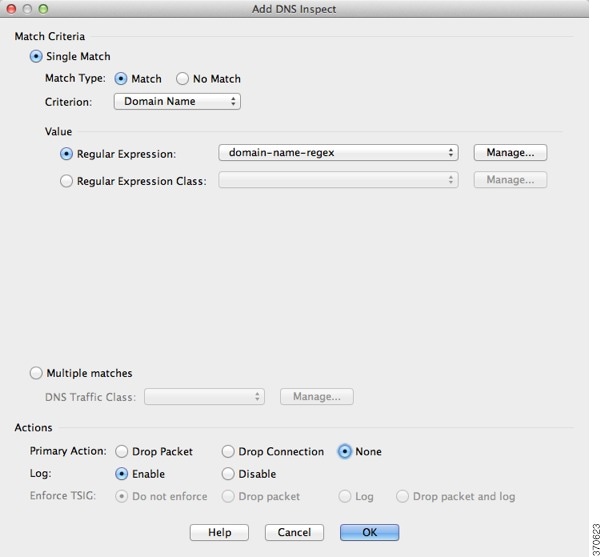
The Add DNS Inspect dialog box appears.

Step 3![]() You can configure DNS inspections using the following methods:
You can configure DNS inspections using the following methods:
The difference between creating a class map and defining the traffic match directly in the inspection policy map is that the class map lets you create more complex match criteria, and you can reuse class maps. If you want different actions for each criteria, use the single match option; you can only set one action for the entire class map.
You can add multiple class maps and single matches in the same policy map.
Actions for each Single Match, or for a Multiple match class map include:
Not all combinations are valid for all matching criteria. For example, you can configure both Mask and Enforce TSIG together only for the Criterion: Header Flag option.
Step 4![]() For Multiple matches, if you predefined a class map on the Configuration > Firewall > Objects > Class Maps > DNS pane, you can select it from the drop-down list, set the Actions, and click OK.
For Multiple matches, if you predefined a class map on the Configuration > Firewall > Objects > Class Maps > DNS pane, you can select it from the drop-down list, set the Actions, and click OK.
The Manage DNS Class Maps dialog box appears
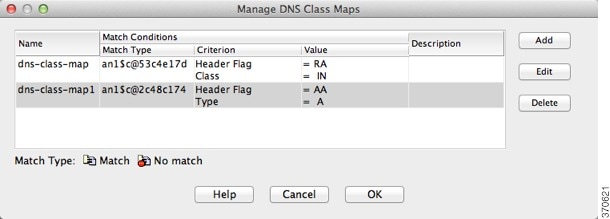
The Add DNS Traffic Class Map dialog box appears.

The Add DNS Match Criterion dialog box appears.
The match criteria are the same for a class map or for single matches; the following steps apply to both methods. The only difference is that you do not set an Action for each criterion in a class map.
Step 5![]() From the Criterion drop-down list, choose one of the following criteria:
From the Criterion drop-down list, choose one of the following criteria:

Set the following Value parameters:
–![]() Match Option: Equals or Contains. If you choose Header Flag Name, and check multiple flags, you can set the ASA to match a packet only if all flags are present (Equals) or if any one of the flags is present (Contains).
Match Option: Equals or Contains. If you choose Header Flag Name, and check multiple flags, you can set the ASA to match a packet only if all flags are present (Equals) or if any one of the flags is present (Contains).
–![]() Match Value: Header Flag Name or Header Flag Value. If you click Header Flag Name, you can check one or more well-known flag values. If you want to specify a hex value, click the Header Flag Value radio button, and enter the hex value in the field.
Match Value: Header Flag Name or Header Flag Value. If you click Header Flag Name, you can check one or more well-known flag values. If you want to specify a hex value, click the Header Flag Value radio button, and enter the hex value in the field.

Set the following Value parameters:
–![]() DNS Type Field Name —Lists the DNS types to select.
DNS Type Field Name —Lists the DNS types to select.
IXFR —Incremental (zone) transfer
SOA —Start of a zone of authority
Value —Lets you enter a value between 0 and 65535 to match.
Range —Lets you enter a range match. Both values between 0 and 65535.

Set the following Value parameters:
–![]() DNS Class Field Name: Internet —Internet is the only option.
DNS Class Field Name: Internet —Internet is the only option.
Value —Lets you enter a value between 0 and 65535.
Range —Lets you enter a range match. Both values between 0 and 65535.
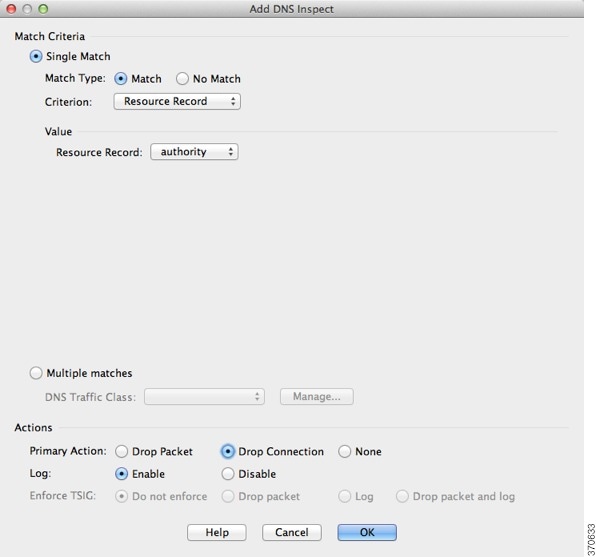
Set the following Value parameters:
additional —DNS additional resource record
answer —DNS answer resource record
authority —DNS authority resource record
Set the following Value parameters:
–![]() Regular Expression —Choose an existing regular expression from the drop-down menu, or click Manage to add a new one. See the general operations configuration guide.
Regular Expression —Choose an existing regular expression from the drop-down menu, or click Manage to add a new one. See the general operations configuration guide.
–![]() Regular Expression Class —Choose an existing regular expression class map from the drop-down menu, or click Manage to add a new one. See the general operations configuration guide.
Regular Expression Class —Choose an existing regular expression class map from the drop-down menu, or click Manage to add a new one. See the general operations configuration guide.
a.![]() Click OK to add the match to the map.
Click OK to add the match to the map.
b.![]() Add more matches as desired.
Add more matches as desired.
c.![]() Click OK to finish the class map.
Click OK to finish the class map.
d.![]() Click OK to return to the Add DNS Inspect Map dialog box.
Click OK to return to the Add DNS Inspect Map dialog box.
Step 7![]() Set the action for the Single Match, or for the Multiple matches class map; see Step 3 for actions.
Set the action for the Single Match, or for the Multiple matches class map; see Step 3 for actions.
Step 8![]() Click OK to return to the Add DNS Inspect dialog box.
Click OK to return to the Add DNS Inspect dialog box.
Step 9![]() In some cases when you have more than one match in the inspection policy map, you can order the matches using the Move Up and Move Down buttons. Generally, the order is determined by internal ASA rules, so these buttons are not available for most entries. However, if you have a direct match and a class map that have the same match, then the order in the configuration determines which match is used, so these buttons are enabled. See Guidelines and Limitations for more information.
In some cases when you have more than one match in the inspection policy map, you can order the matches using the Move Up and Move Down buttons. Generally, the order is determined by internal ASA rules, so these buttons are not available for most entries. However, if you have a direct match and a class map that have the same match, then the order in the configuration determines which match is used, so these buttons are enabled. See Guidelines and Limitations for more information.
Step 10![]() Click OK to save the DNS inspect map.
Click OK to save the DNS inspect map.
Configuring DNS Inspection
The default ASA configuration includes many default inspections on default ports applied globally on all interfaces. A common method for customizing the inspection configuration is to customize the default global policy. The steps in this section show how to edit the default global policy, but you can alternatively create a new service policy as desired, for example, an interface-specific policy.
Detailed Steps
Step 1![]() Configure a service policy on the Configuration > Firewall > Service Policy Rules pane according to Chapter1, “Service Policy”
Configure a service policy on the Configuration > Firewall > Service Policy Rules pane according to Chapter1, “Service Policy”
You can configure DNS inspection as part of a new service policy rule, or you can edit an existing service policy.
Step 2![]() On the Rule Actions dialog box, click the Protocol Inspections tab.
On the Rule Actions dialog box, click the Protocol Inspections tab.
Step 3![]() (To change an in-use policy) If you are editing any in-use policy to use a different DNS inspection policy map, you must disable the DNS inspection, and then re-enable it with the new DNS inspection policy map name:
(To change an in-use policy) If you are editing any in-use policy to use a different DNS inspection policy map, you must disable the DNS inspection, and then re-enable it with the new DNS inspection policy map name:
d.![]() Repeat these steps to return to the Protocol Inspections tab.
Repeat these steps to return to the Protocol Inspections tab.
Step 4![]() Check the DNS check box.
Check the DNS check box.
The Select DNS Inspect Map dialog appears.
Step 6![]() Choose the inspection map:
Choose the inspection map:
- To use the default map, click Use the default DNS inspection map (preset_dns_map).
- To use a DNS inspection policy map that you configured in the (Optional) Configuring a DNS Inspection Policy Map and Class Map, select the map name.
- To add a new map, click Add. See (Optional) Configuring a DNS Inspection Policy Map and Class Map for more information.
Step 7![]() If you use the Botnet Traffic Filter, click Enable Botnet traffic filter DNS snooping. Botnet Traffic Filter snooping compares the domain name with those on the dynamic database or static database, and adds the name and IP address to the Botnet Traffic Filter DNS reverse lookup cache. This cache is then used by the Botnet Traffic Filter when connections are made to the suspicious address. We suggest that you enable DNS snooping only on interfaces where external DNS requests are going. Enabling DNS snooping on all UDP DNS traffic, including that going to an internal DNS server, creates unnecessary load on the ASA. For example, if the DNS server is on the outside interface, you should enable DNS inspection with snooping for all UDP DNS traffic on the outside interface. See Enabling DNS Snooping.
If you use the Botnet Traffic Filter, click Enable Botnet traffic filter DNS snooping. Botnet Traffic Filter snooping compares the domain name with those on the dynamic database or static database, and adds the name and IP address to the Botnet Traffic Filter DNS reverse lookup cache. This cache is then used by the Botnet Traffic Filter when connections are made to the suspicious address. We suggest that you enable DNS snooping only on interfaces where external DNS requests are going. Enabling DNS snooping on all UDP DNS traffic, including that going to an internal DNS server, creates unnecessary load on the ASA. For example, if the DNS server is on the outside interface, you should enable DNS inspection with snooping for all UDP DNS traffic on the outside interface. See Enabling DNS Snooping.
Step 8![]() Click OK to return to the Protocol Inspections tab.
Click OK to return to the Protocol Inspections tab.
Step 9![]() Click OK to finish editing the service policy.
Click OK to finish editing the service policy.
FTP Inspection
This section describes the FTP inspection engine. This section includes the following topics:
- FTP Inspection Overview
- Using Strict FTP
- Select FTP Map
- FTP Class Map
- Add/Edit FTP Traffic Class Map
- Add/Edit FTP Match Criterion
- FTP Inspect Map
FTP Inspection Overview
The FTP application inspection inspects the FTP sessions and performs four tasks:
- Prepares dynamic secondary data connection
- Tracks the FTP command-response sequence
- Generates an audit trail
- Translates the embedded IP address
FTP application inspection prepares secondary channels for FTP data transfer. Ports for these channels are negotiated through PORT or PASV commands. The channels are allocated in response to a file upload, a file download, or a directory listing event.

Note![]() If you disable FTP inspection engines with the no inspect ftp command, outbound users can start connections only in passive mode, and all inbound FTP is disabled.
If you disable FTP inspection engines with the no inspect ftp command, outbound users can start connections only in passive mode, and all inbound FTP is disabled.
Using Strict FTP
Using strict FTP increases the security of protected networks by preventing web browsers from sending embedded commands in FTP requests. To enable strict FTP, click the Configure button next to FTP on the Configuration > Firewall > Service Policy Rules > Edit Service Policy Rule > Rule Actions > Protocol Inspection tab.
After you enable the strict option on an interface, FTP inspection enforces the following behavior:
- An FTP command must be acknowledged before the ASA allows a new command.
- The ASA drops connections that send embedded commands.
- The 227 and PORT commands are checked to ensure they do not appear in an error string.

If the strict option is enabled, each FTP command and response sequence is tracked for the following anomalous activity:
- Truncated command—Number of commas in the PORT and PASV reply command is checked to see if it is five. If it is not five, then the PORT command is assumed to be truncated and the TCP connection is closed.
- Incorrect command—Checks the FTP command to see if it ends with <CR><LF> characters, as required by the RFC. If it does not, the connection is closed.
- Size of RETR and STOR commands—These are checked against a fixed constant. If the size is greater, then an error message is logged and the connection is closed.
- Command spoofing—The PORT command should always be sent from the client. The TCP connection is denied if a PORT command is sent from the server.
- Reply spoofing—PASV reply command (227) should always be sent from the server. The TCP connection is denied if a PASV reply command is sent from the client. This prevents the security hole when the user executes “227 xxxxx a1, a2, a3, a4, p1, p2.”
- TCP stream editing—The ASA closes the connection if it detects TCP stream editing.
- Invalid port negotiation—The negotiated dynamic port value is checked to see if it is less than 1024. As port numbers in the range from 1 to 1024 are reserved for well-known connections, if the negotiated port falls in this range, then the TCP connection is freed.
- Command pipelining—The number of characters present after the port numbers in the PORT and PASV reply command is cross checked with a constant value of 8. If it is more than 8, then the TCP connection is closed.
- The ASA replaces the FTP server response to the SYST command with a series of Xs. to prevent the server from revealing its system type to FTP clients. To override this default behavior, use the no mask-syst-reply command in the FTP map.
Select FTP Map
The Select FTP Map dialog box is accessible as follows:
Add/Edit Service Policy Rule Wizard > Rule Actions > Protocol Inspection Tab > Select FTP Map
The Select FTP Map dialog box lets you enable strict FTP application inspection, select an FTP map, or create a new FTP map. An FTP map lets you change the configuration values used for FTP application inspection.The Select FTP Map table provides a list of previously configured maps that you can select for application inspection.
- FTP Strict (prevent web browsers from sending embedded commands in FTP requests) — Enables strict FTP application inspection, which causes the ASA to drop the connection when an embedded command is included in an FTP request.
- Use the default FTP inspection map—Specifies to use the default FTP map.
- Select an FTP map for fine control over inspection — Lets you select a defined application inspection map or add a new one.
- Add—Opens the Add Policy Map dialog box for the inspection.
FTP Class Map
The FTP Class Map dialog box is accessible as follows:
Configuration > Global Objects > Class Maps > FTP
The FTP Class Map pane lets you configure FTP class maps for FTP inspection.
An inspection class map matches application traffic with criteria specific to the application. You then identify the class map in the inspect map and enable actions. The difference between creating a class map and defining the traffic match directly in the inspect map is that you can create more complex match criteria and you can reuse class maps. The applications that support inspection class maps are DNS, FTP, H.323, HTTP, IM, and SIP.
- Name—Shows the FTP class map name.
- Match Conditions—Shows the type, match criterion, and value in the class map.
–![]() Match Type—Shows the match type, which can be a positive or negative match.
Match Type—Shows the match type, which can be a positive or negative match.
Add/Edit FTP Traffic Class Map
The Add/Edit FTP Traffic Class Map dialog box is accessible as follows:
Configuration > Global Objects > Class Maps > FTP > Add/Edit FTP Traffic Class Map
The Add/Edit FTP Traffic Class Map dialog box lets you define a FTP class map.
Add/Edit FTP Match Criterion
The Add/Edit FTP Match Criterion dialog box is accessible as follows:
Configuration > Global Objects > Class Maps > FTP > Add/Edit FTP Traffic Class Map > Add/Edit FTP Match Criterion
The Add/Edit FTP Match Criterion dialog box lets you define the match criterion and value for the FTP class map.
- Match Type—Specifies whether the class map includes traffic that matches the criterion, or traffic that does not match the criterion.
For example, if No Match is selected on the string “example.com,” then any traffic that contains “example.com” is excluded from the class map.
–![]() Request-Command—Match an FTP request command.
Request-Command—Match an FTP request command.
–![]() File Name—Match a filename for FTP transfer.
File Name—Match a filename for FTP transfer.
–![]() File Type—Match a file type for FTP transfer.
File Type—Match a file type for FTP transfer.
–![]() User Name—Match an FTP user.
User Name—Match an FTP user.
–![]() Request Command—Lets you select one or more request commands to match.
Request Command—Lets you select one or more request commands to match.
CDUP—Change to the parent of the current directory.
DELE—Delete a file at the server site.
GET—FTP client command for the retr (retrieve a file) command.
HELP—Help information from the server.
PUT—FTP client command for the stor (store a file) command.
SITE—Specify a server specific command.
STOU—Store a file with a unique name.
–![]() Regular Expression—Lists the defined regular expressions to match.
Regular Expression—Lists the defined regular expressions to match.
–![]() Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
–![]() Regular Expression Class—Lists the defined regular expression classes to match.
Regular Expression Class—Lists the defined regular expression classes to match.
–![]() Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Regular Expression—Lists the defined regular expressions to match.
Regular Expression—Lists the defined regular expressions to match.
–![]() Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
–![]() Regular Expression Class—Lists the defined regular expression classes to match.
Regular Expression Class—Lists the defined regular expression classes to match.
–![]() Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Regular Expression—Lists the defined regular expressions to match.
Regular Expression—Lists the defined regular expressions to match.
–![]() Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
–![]() Regular Expression Class—Lists the defined regular expression classes to match.
Regular Expression Class—Lists the defined regular expression classes to match.
–![]() Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Regular Expression—Lists the defined regular expressions to match.
Regular Expression—Lists the defined regular expressions to match.
–![]() Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
–![]() Regular Expression Class—Lists the defined regular expression classes to match.
Regular Expression Class—Lists the defined regular expression classes to match.
–![]() Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
FTP Inspect Map
The FTP Inspect Map dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > FTP
The FTP pane lets you view previously configured FTP application inspection maps. An FTP map lets you change the default configuration values used for FTP application inspection.
FTP command filtering and security checks are provided using strict FTP inspection for improved security and control. Protocol conformance includes packet length checks, delimiters and packet format checks, command terminator checks, and command validation.
Blocking FTP based on user values is also supported so that it is possible for FTP sites to post files for download, but restrict access to certain users. You can block FTP connections based on file type, server name, and other attributes. System message logs are generated if an FTP connection is denied after inspection.
- FTP Inspect Maps—Table that lists the defined FTP inspect maps.
- Add—Configures a new FTP inspect map. To edit an FTP inspect map, choose the FTP entry in the FTP Inspect Maps table and click Customize.
- Delete—Deletes the inspect map selected in the FTP Inspect Maps table.
- Security Level—Select the security level (medium or low).
–![]() File Type Filtering—Opens the Type Filtering dialog box to configure file type filters.
File Type Filtering—Opens the Type Filtering dialog box to configure file type filters.
–![]() Customize—Opens the Add/Edit FTP Policy Map dialog box for additional settings.
Customize—Opens the Add/Edit FTP Policy Map dialog box for additional settings.
–![]() Default Level—Sets the security level back to the default level of Medium.
Default Level—Sets the security level back to the default level of Medium.
File Type Filtering
The File Type Filtering dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > FTP > MIME File Type Filtering
The File Type Filtering dialog box lets you configure the settings for a file type filter.
- Match Type—Shows the match type, which can be a positive or negative match.
- Criterion—Shows the criterion of the inspection.
- Value—Shows the value to match in the inspection.
- Action—Shows the action if the match condition is met.
- Log—Shows the log state.
- Add—Opens the Add File Type Filter dialog box to add a file type filter.
- Edit—Opens the Edit File Type Filter dialog box to edit a file type filter.
- Delete—Deletes a file type filter.
- Move Up—Moves an entry up in the list.
- Move Down—Moves an entry down in the list.
Add/Edit FTP Policy Map (Security Level)
The Add/Edit FTP Policy Map dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > FTP > FTP Inspect Map > Basic View
The Add/Edit FTP Policy Map pane lets you configure the security level and additional settings for FTP application inspection maps.
- Name—When adding an FTP map, enter the name of the FTP map. When editing an FTP map, the name of the previously configured FTP map is shown.
- Description—Enter the description of the FTP map, up to 200 characters in length.
- Security Level—Select the security level (medium or low).
–![]() File Type Filtering—Opens the Type Filtering dialog box to configure file type filters.
File Type Filtering—Opens the Type Filtering dialog box to configure file type filters.
–![]() Default Level—Sets the security level back to the default level of Medium.
Default Level—Sets the security level back to the default level of Medium.
Add/Edit FTP Policy Map (Details)
The Add/Edit FTP Policy Map (Details) dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > FTP > FTP Inspect Map > Advanced View
The Add/Edit FTP Policy Map pane lets you configure the security level and additional settings for FTP application inspection maps.
- Name—When adding an FTP map, enter the name of the FTP map. When editing an FTP map, the name of the previously configured FTP map is shown.
- Description—Enter the description of the FTP map, up to 200 characters in length.
- Security Level—Shows the security level and file type filtering settings to configure.
- Parameters—Tab that lets you configure the parameters for the FTP inspect map.
–![]() Mask greeting banner from the server—Masks the greeting banner from the FTP server to prevent the client from discovering server information.
Mask greeting banner from the server—Masks the greeting banner from the FTP server to prevent the client from discovering server information.
–![]() Mask reply to SYST command—Masks the reply to the syst command to prevent the client from discovering server information.
Mask reply to SYST command—Masks the reply to the syst command to prevent the client from discovering server information.
–![]() Match Type—Shows the match type, which can be a positive or negative match.
Match Type—Shows the match type, which can be a positive or negative match.
–![]() Criterion—Shows the criterion of the FTP inspection.
Criterion—Shows the criterion of the FTP inspection.
–![]() Value—Shows the value to match in the FTP inspection.
Value—Shows the value to match in the FTP inspection.
–![]() Action—Shows the action if the match condition is met.
Action—Shows the action if the match condition is met.
–![]() Add—Opens the Add FTP Inspect dialog box to add an FTP inspection.
Add—Opens the Add FTP Inspect dialog box to add an FTP inspection.
–![]() Edit—Opens the Edit FTP Inspect dialog box to edit an FTP inspection.
Edit—Opens the Edit FTP Inspect dialog box to edit an FTP inspection.
–![]() Delete—Deletes an FTP inspection.
Delete—Deletes an FTP inspection.
Add/Edit FTP Map
The Add/Edit FTP Map dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > FTP > FTP Inspect Map > Advanced View > Add/Edit FTP Inspect
The Add/Edit FTP Inspect dialog box lets you define the match criterion and value for the FTP inspect map.
- Single Match—Specifies that the FTP inspect has only one match statement.
- Match Type—Specifies whether traffic should match or not match the values.
For example, if No Match is selected on the string “example.com,” then any traffic that contains “example.com” is excluded from the class map.
–![]() Request Command—Match an FTP request command.
Request Command—Match an FTP request command.
–![]() File Name—Match a filename for FTP transfer.
File Name—Match a filename for FTP transfer.
–![]() File Type—Match a file type for FTP transfer.
File Type—Match a file type for FTP transfer.
–![]() User Name—Match an FTP user.
User Name—Match an FTP user.
APPE—Command that appends to a file.
CDUP—Command that changes to the parent directory of the current working directory.
DELE—Command that deletes a file.
HELP—Command that provides help information.
MKD—Command that creates a directory.
PUT—Command that sends a file.
RMD—Command that deletes a directory.
RNFR—Command that specifies rename-from filename.
RNTO—Command that specifies rename-to filename.
SITE—Commands that are specific to the server system. Usually used for remote administration.
STOU—Command that stores a file using a unique filename.
–![]() Regular Expression—Lists the defined regular expressions to match.
Regular Expression—Lists the defined regular expressions to match.
–![]() Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
–![]() Regular Expression Class—Lists the defined regular expression classes to match.
Regular Expression Class—Lists the defined regular expression classes to match.
–![]() Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Regular Expression—Lists the defined regular expressions to match.
Regular Expression—Lists the defined regular expressions to match.
–![]() Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
–![]() Regular Expression Class—Lists the defined regular expression classes to match.
Regular Expression Class—Lists the defined regular expression classes to match.
–![]() Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Regular Expression—Lists the defined regular expressions to match.
Regular Expression—Lists the defined regular expressions to match.
–![]() Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
–![]() Regular Expression Class—Lists the defined regular expression classes to match.
Regular Expression Class—Lists the defined regular expression classes to match.
–![]() Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Regular Expression—Lists the defined regular expressions to match.
Regular Expression—Lists the defined regular expressions to match.
–![]() Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
–![]() Regular Expression Class—Lists the defined regular expression classes to match.
Regular Expression Class—Lists the defined regular expression classes to match.
–![]() Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() FTP Traffic Class—Specifies the FTP traffic class match.
FTP Traffic Class—Specifies the FTP traffic class match.
–![]() Manage—Opens the Manage FTP Class Maps dialog box to add, edit, or delete FTP Class Maps.
Manage—Opens the Manage FTP Class Maps dialog box to add, edit, or delete FTP Class Maps.
Verifying and Monitoring FTP Inspection
FTP application inspection generates the following log messages:
- An Audit record 303002 is generated for each file that is retrieved or uploaded.
- The FTP command is checked to see if it is RETR or STOR and the retrieve and store commands are logged.
- The username is obtained by looking up a table providing the IP address.
- The username, source IP address, destination IP address, NAT address, and the file operation are logged.
- Audit record 201005 is generated if the secondary dynamic channel preparation failed due to memory shortage.
In conjunction with NAT, the FTP application inspection translates the IP address within the application payload. This is described in detail in RFC 959.
HTTP Inspection
This section describes the HTTP inspection engine. This section includes the following topics:
- HTTP Inspection Overview
- Select HTTP Map
- HTTP Class Map
- Add/Edit HTTP Traffic Class Map
- Add/Edit HTTP Match Criterion
- HTTP Inspect Map
- URI Filtering
- Add/Edit HTTP Policy Map (Security Level)
- Add/Edit HTTP Policy Map (Details)
- Add/Edit HTTP Map
HTTP Inspection Overview
Use the HTTP inspection engine to protect against specific attacks and other threats that are associated with HTTP traffic. The latter two features are configured in conjunction with Filter rules.
The enhanced HTTP inspection feature, which is also known as an application firewall and is available when you configure an HTTP map, can help prevent attackers from using HTTP messages for circumventing network security policy. It verifies the following for all HTTP messages:
Select HTTP Map
The Select HTTP Map dialog box is accessible as follows:
Add/Edit Service Policy Rule Wizard > Rule Actions > Protocol Inspection Tab > Select HTTP Map
The Select HTTP Map dialog box lets you select or create a new HTTP map. An HTTP map lets you change the configuration values used for HTTP application inspection. The Select HTTP Map table provides a list of previously configured maps that you can select for application inspection.
HTTP Class Map
The HTTP Class Map dialog box is accessible as follows:
Configuration > Global Objects > Class Maps > HTTP
The HTTP Class Map pane lets you configure HTTP class maps for HTTP inspection.
An inspection class map matches application traffic with criteria specific to the application. You then identify the class map in the inspect map and enable actions. The difference between creating a class map and defining the traffic match directly in the inspect map is that you can create more complex match criteria and you can reuse class maps. The applications that support inspection class maps are DNS, FTP, H.323, HTTP, IM, and SIP.
- Name—Shows the HTTP class map name.
- Match Conditions—Shows the type, match criterion, and value in the class map.
–![]() Match Type—Shows the match type, which can be a positive or negative match.
Match Type—Shows the match type, which can be a positive or negative match.
Add/Edit HTTP Traffic Class Map
The Add/Edit HTTP Traffic Class Map dialog box is accessible as follows:
Configuration > Global Objects > Class Maps > HTTP > Add/Edit HTTP Traffic Class Map
The Add/Edit HTTP Traffic Class Map dialog box lets you define a HTTP class map.
Add/Edit HTTP Match Criterion
The Add/Edit HTTP Match Criterion dialog box is accessible as follows:
Configuration > Global Objects > Class Maps > HTTP > Add/Edit HTTP Traffic Class Map > Add/Edit HTTP Match Criterion
The Add/Edit HTTP Match Criterion dialog box lets you define the match criterion and value for the HTTP class map.
- Match Type—Specifies whether the class map includes traffic that matches the criterion, or traffic that does not match the criterion.
For example, if No Match is selected on the string “example.com,” then any traffic that contains “example.com” is excluded from the class map.
–![]() Request/Response Content Type Mismatch—Specifies that the content type in the response must match one of the MIME types in the accept field of the request.
Request/Response Content Type Mismatch—Specifies that the content type in the response must match one of the MIME types in the accept field of the request.
–![]() Request Arguments—Applies the regular expression match to the arguments of the request.
Request Arguments—Applies the regular expression match to the arguments of the request.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Request Body Length—Applies the regular expression match to the body of the request with field length greater than the bytes specified.
Request Body Length—Applies the regular expression match to the body of the request with field length greater than the bytes specified.
Greater Than Length—Enter a field length value in bytes that request field lengths will be matched against.
–![]() Request Body—Applies the regular expression match to the body of the request.
Request Body—Applies the regular expression match to the body of the request.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Request Header Field Count—Applies the regular expression match to the header of the request with a maximum number of header fields.
Request Header Field Count—Applies the regular expression match to the header of the request with a maximum number of header fields.
Predefined—Specifies the request header fields: accept, accept-charset, accept-encoding, accept-language, allow, authorization, cache-control, connection, content-encoding, content-language, content-length, content-location, content-md5, content-range, content-type, cookie, date, expect, expires, from, host, if-match, if-modified-since, if-none-match, if-range, if-unmodified-since, last-modified, max-forwards, pragma, proxy-authorization, range, referer, te, trailer, transfer-encoding, upgrade, user-agent, via, warning.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Greater Than Count—Enter the maximum number of header fields.
–![]() Request Header Field Length—Applies the regular expression match to the header of the request with field length greater than the bytes specified.
Request Header Field Length—Applies the regular expression match to the header of the request with field length greater than the bytes specified.
Predefined—Specifies the request header fields: accept, accept-charset, accept-encoding, accept-language, allow, authorization, cache-control, connection, content-encoding, content-language, content-length, content-location, content-md5, content-range, content-type, cookie, date, expect, expires, from, host, if-match, if-modified-since, if-none-match, if-range, if-unmodified-since, last-modified, max-forwards, pragma, proxy-authorization, range, referer, te, trailer, transfer-encoding, upgrade, user-agent, via, warning.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Greater Than Length—Enter a field length value in bytes that request field lengths will be matched against.
–![]() Request Header Field—Applies the regular expression match to the header of the request.
Request Header Field—Applies the regular expression match to the header of the request.
Predefined—Specifies the request header fields: accept, accept-charset, accept-encoding, accept-language, allow, authorization, cache-control, connection, content-encoding, content-language, content-length, content-location, content-md5, content-range, content-type, cookie, date, expect, expires, from, host, if-match, if-modified-since, if-none-match, if-range, if-unmodified-since, last-modified, max-forwards, pragma, proxy-authorization, range, referer, te, trailer, transfer-encoding, upgrade, user-agent, via, warning.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Request Header Count—Applies the regular expression match to the header of the request with a maximum number of headers.
Request Header Count—Applies the regular expression match to the header of the request with a maximum number of headers.
Greater Than Count—Enter the maximum number of headers.
–![]() Request Header Length—Applies the regular expression match to the header of the request with length greater than the bytes specified.
Request Header Length—Applies the regular expression match to the header of the request with length greater than the bytes specified.
Greater Than Length—Enter a header length value in bytes.
–![]() Request Header non-ASCII—Matches non-ASCII characters in the header of the request.
Request Header non-ASCII—Matches non-ASCII characters in the header of the request.
–![]() Request Method—Applies the regular expression match to the method of the request.
Request Method—Applies the regular expression match to the method of the request.
Method—Specifies to match on a request method: bcopy, bdelete, bmove, bpropfind, bproppatch, connect, copy, delete, edit, get, getattribute, getattributenames, getproperties, head, index, lock, mkcol, mkdir, move, notify, options, poll, post, propfind, proppatch, put, revadd, revlabel, revlog, revnum, save, search, setattribute, startrev, stoprev, subscribe, trace, unedit, unlock, unsubscribe.
Regular Expression—Specifies to match on a regular expression.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Request URI Length—Applies the regular expression match to the URI of the request with length greater than the bytes specified.
Request URI Length—Applies the regular expression match to the URI of the request with length greater than the bytes specified.
Greater Than Length—Enter a URI length value in bytes.
–![]() Request URI—Applies the regular expression match to the URI of the request.
Request URI—Applies the regular expression match to the URI of the request.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Response Body—Applies the regex match to the body of the response.
Response Body—Applies the regex match to the body of the response.
ActiveX—Specifies to match on ActiveX.
Java Applet—Specifies to match on a Java Applet.
Regular Expression—Specifies to match on a regular expression.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Response Body Length—Applies the regular expression match to the body of the response with field length greater than the bytes specified.
Response Body Length—Applies the regular expression match to the body of the response with field length greater than the bytes specified.
Greater Than Length—Enter a field length value in bytes that response field lengths will be matched against.
–![]() Response Header Field Count—Applies the regular expression match to the header of the response with a maximum number of header fields.
Response Header Field Count—Applies the regular expression match to the header of the response with a maximum number of header fields.
Predefined—Specifies the response header fields: accept-ranges, age, allow, cache-control, connection, content-encoding, content-language, content-length, content-location, content-md5, content-range, content-type, date, etag, expires, last-modified, location, pragma, proxy-authenticate, retry-after, server, set-cookie, trailer, transfer-encoding, upgrade, vary, via, warning, www-authenticate.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Greater Than Count—Enter the maximum number of header fields.
–![]() Response Header Field Length—Applies the regular expression match to the header of the response with field length greater than the bytes specified.
Response Header Field Length—Applies the regular expression match to the header of the response with field length greater than the bytes specified.
Predefined—Specifies the response header fields: accept-ranges, age, allow, cache-control, connection, content-encoding, content-language, content-length, content-location, content-md5, content-range, content-type, date, etag, expires, last-modified, location, pragma, proxy-authenticate, retry-after, server, set-cookie, trailer, transfer-encoding, upgrade, vary, via, warning, www-authenticate.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Greater Than Length—Enter a field length value in bytes that response field lengths will be matched against.
–![]() Response Header Field—Applies the regular expression match to the header of the response.
Response Header Field—Applies the regular expression match to the header of the response.
Predefined—Specifies the response header fields: accept-ranges, age, allow, cache-control, connection, content-encoding, content-language, content-length, content-location, content-md5, content-range, content-type, date, etag, expires, last-modified, location, pragma, proxy-authenticate, retry-after, server, set-cookie, trailer, transfer-encoding, upgrade, vary, via, warning, www-authenticate.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Response Header Count—Applies the regular expression match to the header of the response with a maximum number of headers.
Response Header Count—Applies the regular expression match to the header of the response with a maximum number of headers.
Greater Than Count—Enter the maximum number of headers.
–![]() Response Header Length—Applies the regular expression match to the header of the response with length greater than the bytes specified.
Response Header Length—Applies the regular expression match to the header of the response with length greater than the bytes specified.
Greater Than Length—Enter a header length value in bytes.
–![]() Response Header non-ASCII—Matches non-ASCII characters in the header of the response.
Response Header non-ASCII—Matches non-ASCII characters in the header of the response.
–![]() Response Status Line—Applies the regular expression match to the status line.
Response Status Line—Applies the regular expression match to the status line.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
HTTP Inspect Map
The HTTP Inspect Map dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > HTTP
The HTTP pane lets you view previously configured HTTP application inspection maps. An HTTP map lets you change the default configuration values used for HTTP application inspection.
HTTP application inspection scans HTTP headers and body, and performs various checks on the data. These checks prevent various HTTP constructs, content types, and tunneling and messaging protocols from traversing the security appliance.
HTTP application inspection can block tunneled applications and non-ASCII characters in HTTP requests and responses, preventing malicious content from reaching the web server. Size limiting of various elements in HTTP request and response headers, URL blocking, and HTTP server header type spoofing are also supported.
- HTTP Inspect Maps—Table that lists the defined HTTP inspect maps.
- Add—Configures a new HTTP inspect map. To edit an HTTP inspect map, choose the HTTP entry in the HTTP Inspect Maps table and click Customize.
- Delete—Deletes the inspect map selected in the HTTP Inspect Maps table.
- Security Level—Select the security level (low, medium, or high).
Protocol violation action: Drop connection
Drop connections for unsafe methods: Disabled
Drop connections for requests with non-ASCII headers: Disabled
Advanced inspections: Not configured
Protocol violation action: Drop connection
Drop connections for unsafe methods: Allow only GET, HEAD, and POST
Drop connections for requests with non-ASCII headers: Disabled
Advanced inspections: Not configured
Protocol violation action: Drop connection and log
Drop connections for unsafe methods: Allow only GET and HEAD.
Drop connections for requests with non-ASCII headers: Enabled
Advanced inspections: Not configured
–![]() URI Filtering—Opens the URI Filtering dialog box to configure URI filters.
URI Filtering—Opens the URI Filtering dialog box to configure URI filters.
–![]() Customize—Opens the Edit HTTP Policy Map dialog box for additional settings.
Customize—Opens the Edit HTTP Policy Map dialog box for additional settings.
–![]() Default Level—Sets the security level back to the default level of Medium.
Default Level—Sets the security level back to the default level of Medium.
URI Filtering
The URI Filtering dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > HTTP > URI Filtering
The URI Filtering dialog box lets you configure the settings for an URI filter.
- Match Type—Shows the match type, which can be a positive or negative match.
- Criterion—Shows the criterion of the inspection.
- Value—Shows the value to match in the inspection.
- Action—Shows the action if the match condition is met.
- Log—Shows the log state.
- Add—Opens the Add URI Filtering dialog box to add a URI filter.
- Edit—Opens the Edit URI Filtering dialog box to edit a URI filter.
- Delete—Deletes an URI filter.
- Move Up—Moves an entry up in the list.
- Move Down—Moves an entry down in the list.
Add/Edit HTTP Policy Map (Security Level)
The Add/Edit HTTP Policy Map (Security Level) dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > HTTP > HTTP Inspect Map > Basic View
The Add/Edit HTTP Policy Map pane lets you configure the security level and additional settings for HTTP application inspection maps.
- Name—When adding an HTTP map, enter the name of the HTTP map. When editing an HTTP map, the name of the previously configured HTTP map is shown.
- Description—Enter the description of the HTTP map, up to 200 characters in length.
- Security Level—Select the security level (low, medium, or high).
Protocol violation action: Drop connection
Drop connections for unsafe methods: Disabled
Drop connections for requests with non-ASCII headers: Disabled
Advanced inspections: Not configured
Protocol violation action: Drop connection
Drop connections for unsafe methods: Allow only GET, HEAD, and POST
Drop connections for requests with non-ASCII headers: Disabled
Advanced inspections: Not configured
Protocol violation action: Drop connection and log
Drop connections for unsafe methods: Allow only GET and HEAD.
Drop connections for requests with non-ASCII headers: Enabled
Advanced inspections: Not configured
–![]() URI Filtering—Opens the URI Filtering dialog box which lets you configure the settings for an URI filter.
URI Filtering—Opens the URI Filtering dialog box which lets you configure the settings for an URI filter.
–![]() Default Level—Sets the security level back to the default.
Default Level—Sets the security level back to the default.
Add/Edit HTTP Policy Map (Details)
The Add/Edit HTTP Policy Map (Details) dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > HTTP > HTTP Inspect Map > Advanced View
The Add/Edit HTTP Policy Map pane lets you configure the security level and additional settings for HTTP application inspection maps.
- Name—When adding an HTTP map, enter the name of the HTTP map. When editing an HTTP map, the name of the previously configured HTTP map is shown.
- Description—Enter the description of the HTTP map, up to 200 characters in length.
- Security Level—Shows the security level and URI filtering settings to configure.
- Parameters—Tab that lets you configure the parameters for the HTTP inspect map.
–![]() Check for protocol violations—Checks for HTTP protocol violations.
Check for protocol violations—Checks for HTTP protocol violations.
Action—Drop Connection, Reset, Log.
–![]() Spoof server string—Replaces the server HTTP header value with the specified string.
Spoof server string—Replaces the server HTTP header value with the specified string.
Spoof String—Enter a string to substitute for the server header field. Maximum is 82 characters.
–![]() Body Match Maximum—The maximum number of characters in the body of an HTTP message that should be searched in a body match. Default is 200 bytes. A large number will have a significant impact on performance.
Body Match Maximum—The maximum number of characters in the body of an HTTP message that should be searched in a body match. Default is 200 bytes. A large number will have a significant impact on performance.
–![]() Match Type—Shows the match type, which can be a positive or negative match.
Match Type—Shows the match type, which can be a positive or negative match.
–![]() Criterion—Shows the criterion of the HTTP inspection.
Criterion—Shows the criterion of the HTTP inspection.
–![]() Value—Shows the value to match in the HTTP inspection.
Value—Shows the value to match in the HTTP inspection.
–![]() Action—Shows the action if the match condition is met.
Action—Shows the action if the match condition is met.
–![]() Add—Opens the Add HTTP Inspect dialog box to add an HTTP inspection.
Add—Opens the Add HTTP Inspect dialog box to add an HTTP inspection.
–![]() Edit—Opens the Edit HTTP Inspect dialog box to edit an HTTP inspection.
Edit—Opens the Edit HTTP Inspect dialog box to edit an HTTP inspection.
–![]() Delete—Deletes an HTTP inspection.
Delete—Deletes an HTTP inspection.
Add/Edit HTTP Map
The Add/Edit HTTP Map dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > HTTP > HTTP Inspect Map > Advanced View > Add/Edit HTTP Inspect
The Add/Edit HTTP Inspect dialog box lets you define the match criterion and value for the HTTP inspect map.
- Single Match—Specifies that the HTTP inspect has only one match statement.
- Match Type—Specifies whether traffic should match or not match the values.
For example, if No Match is selected on the string “example.com,” then any traffic that contains “example.com” is excluded from the class map.
–![]() Request/Response Content Type Mismatch—Specifies that the content type in the response must match one of the MIME types in the accept field of the request.
Request/Response Content Type Mismatch—Specifies that the content type in the response must match one of the MIME types in the accept field of the request.
–![]() Request Arguments—Applies the regular expression match to the arguments of the request.
Request Arguments—Applies the regular expression match to the arguments of the request.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Request Body Length—Applies the regular expression match to the body of the request with field length greater than the bytes specified.
Request Body Length—Applies the regular expression match to the body of the request with field length greater than the bytes specified.
Greater Than Length—Enter a field length value in bytes that request field lengths will be matched against.
–![]() Request Body—Applies the regular expression match to the body of the request.
Request Body—Applies the regular expression match to the body of the request.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Request Header Field Count—Applies the regular expression match to the header of the request with a maximum number of header fields.
Request Header Field Count—Applies the regular expression match to the header of the request with a maximum number of header fields.
Predefined—Specifies the request header fields: accept, accept-charset, accept-encoding, accept-language, allow, authorization, cache-control, connection, content-encoding, content-language, content-length, content-location, content-md5, content-range, content-type, cookie, date, expect, expires, from, host, if-match, if-modified-since, if-none-match, if-range, if-unmodified-since, last-modified, max-forwards, pragma, proxy-authorization, range, referer, te, trailer, transfer-encoding, upgrade, user-agent, via, warning.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Greater Than Count—Enter the maximum number of header fields.
–![]() Request Header Field Length—Applies the regular expression match to the header of the request with field length greater than the bytes specified.
Request Header Field Length—Applies the regular expression match to the header of the request with field length greater than the bytes specified.
Predefined—Specifies the request header fields: accept, accept-charset, accept-encoding, accept-language, allow, authorization, cache-control, connection, content-encoding, content-language, content-length, content-location, content-md5, content-range, content-type, cookie, date, expect, expires, from, host, if-match, if-modified-since, if-none-match, if-range, if-unmodified-since, last-modified, max-forwards, pragma, proxy-authorization, range, referer, te, trailer, transfer-encoding, upgrade, user-agent, via, warning.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Greater Than Length—Enter a field length value in bytes that request field lengths will be matched against.
–![]() Request Header Field—Applies the regular expression match to the header of the request.
Request Header Field—Applies the regular expression match to the header of the request.
Predefined—Specifies the request header fields: accept, accept-charset, accept-encoding, accept-language, allow, authorization, cache-control, connection, content-encoding, content-language, content-length, content-location, content-md5, content-range, content-type, cookie, date, expect, expires, from, host, if-match, if-modified-since, if-none-match, if-range, if-unmodified-since, last-modified, max-forwards, pragma, proxy-authorization, range, referer, te, trailer, transfer-encoding, upgrade, user-agent, via, warning.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Request Header Count—Applies the regular expression match to the header of the request with a maximum number of headers.
Request Header Count—Applies the regular expression match to the header of the request with a maximum number of headers.
Greater Than Count—Enter the maximum number of headers.
–![]() Request Header Length—Applies the regular expression match to the header of the request with length greater than the bytes specified.
Request Header Length—Applies the regular expression match to the header of the request with length greater than the bytes specified.
Greater Than Length—Enter a header length value in bytes.
–![]() Request Header non-ASCII—Matches non-ASCII characters in the header of the request.
Request Header non-ASCII—Matches non-ASCII characters in the header of the request.
–![]() Request Method—Applies the regular expression match to the method of the request.
Request Method—Applies the regular expression match to the method of the request.
Method—Specifies to match on a request method: bcopy, bdelete, bmove, bpropfind, bproppatch, connect, copy, delete, edit, get, getattribute, getattributenames, getproperties, head, index, lock, mkcol, mkdir, move, notify, options, poll, post, propfind, proppatch, put, revadd, revlabel, revlog, revnum, save, search, setattribute, startrev, stoprev, subscribe, trace, unedit, unlock, unsubscribe.
Regular Expression—Specifies to match on a regular expression.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Request URI Length—Applies the regular expression match to the URI of the request with length greater than the bytes specified.
Request URI Length—Applies the regular expression match to the URI of the request with length greater than the bytes specified.
Greater Than Length—Enter a URI length value in bytes.
–![]() Request URI—Applies the regular expression match to the URI of the request.
Request URI—Applies the regular expression match to the URI of the request.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Response Body—Applies the regex match to the body of the response.
Response Body—Applies the regex match to the body of the response.
ActiveX—Specifies to match on ActiveX.
Java Applet—Specifies to match on a Java Applet.
Regular Expression—Specifies to match on a regular expression.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Response Body Length—Applies the regular expression match to the body of the response with field length greater than the bytes specified.
Response Body Length—Applies the regular expression match to the body of the response with field length greater than the bytes specified.
Greater Than Length—Enter a field length value in bytes that response field lengths will be matched against.
–![]() Response Header Field Count—Applies the regular expression match to the header of the response with a maximum number of header fields.
Response Header Field Count—Applies the regular expression match to the header of the response with a maximum number of header fields.
Predefined—Specifies the response header fields: accept-ranges, age, allow, cache-control, connection, content-encoding, content-language, content-length, content-location, content-md5, content-range, content-type, date, etag, expires, last-modified, location, pragma, proxy-authenticate, retry-after, server, set-cookie, trailer, transfer-encoding, upgrade, vary, via, warning, www-authenticate.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Greater Than Count—Enter the maximum number of header fields.
–![]() Response Header Field Length—Applies the regular expression match to the header of the response with field length greater than the bytes specified.
Response Header Field Length—Applies the regular expression match to the header of the response with field length greater than the bytes specified.
Predefined—Specifies the response header fields: accept-ranges, age, allow, cache-control, connection, content-encoding, content-language, content-length, content-location, content-md5, content-range, content-type, date, etag, expires, last-modified, location, pragma, proxy-authenticate, retry-after, server, set-cookie, trailer, transfer-encoding, upgrade, vary, via, warning, www-authenticate.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Greater Than Length—Enter a field length value in bytes that response field lengths will be matched against.
–![]() Response Header Field—Applies the regular expression match to the header of the response.
Response Header Field—Applies the regular expression match to the header of the response.
Predefined—Specifies the response header fields: accept-ranges, age, allow, cache-control, connection, content-encoding, content-language, content-length, content-location, content-md5, content-range, content-type, date, etag, expires, last-modified, location, pragma, proxy-authenticate, retry-after, server, set-cookie, trailer, transfer-encoding, upgrade, vary, via, warning, www-authenticate.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Response Header Count—Applies the regular expression match to the header of the response with a maximum number of headers.
Response Header Count—Applies the regular expression match to the header of the response with a maximum number of headers.
Greater Than Count—Enter the maximum number of headers.
–![]() Response Header Length—Applies the regular expression match to the header of the response with length greater than the bytes specified.
Response Header Length—Applies the regular expression match to the header of the response with length greater than the bytes specified.
Greater Than Length—Enter a header length value in bytes.
–![]() Response Header non-ASCII—Matches non-ASCII characters in the header of the response.
Response Header non-ASCII—Matches non-ASCII characters in the header of the response.
–![]() Response Status Line—Applies the regular expression match to the status line.
Response Status Line—Applies the regular expression match to the status line.
Regular Expression—Lists the defined regular expressions to match.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Regular Expression Class—Lists the defined regular expression classes to match.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() H323 Traffic Class—Specifies the HTTP traffic class match.
H323 Traffic Class—Specifies the HTTP traffic class match.
–![]() Manage—Opens the Manage HTTP Class Maps dialog box to add, edit, or delete HTTP Class Maps.
Manage—Opens the Manage HTTP Class Maps dialog box to add, edit, or delete HTTP Class Maps.
ICMP Inspection
The ICMP inspection engine allows ICMP traffic to have a “session” so it can be inspected like TCP and UDP traffic. Without the ICMP inspection engine, we recommend that you do not allow ICMP through the ASA in an ACL. Without stateful inspection, ICMP can be used to attack your network. The ICMP inspection engine ensures that there is only one response for each request, and that the sequence number is correct.
ICMP Error Inspection
When this feature is enabled, the ASA creates translation sessions for intermediate hops that send ICMP error messages, based on the NAT configuration. The ASA overwrites the packet with the translated IP addresses.
When disabled, the ASA does not create translation sessions for intermediate nodes that generate ICMP error messages. ICMP error messages generated by the intermediate nodes between the inside host and the ASA reach the outside host without consuming any additional NAT resource. This is undesirable when an outside host uses the traceroute command to trace the hops to the destination on the inside of the ASA. When the ASA does not translate the intermediate hops, all the intermediate hops appear with the mapped destination IP address.
The ICMP payload is scanned to retrieve the five-tuple from the original packet. Using the retrieved five-tuple, a lookup is performed to determine the original address of the client. The ICMP error inspection engine makes the following changes to the ICMP packet:
- In the IP Header, the mapped IP is changed to the real IP (Destination Address) and the IP checksum is modified.
- In the ICMP Header, the ICMP checksum is modified due to the changes in the ICMP packet.
- In the Payload, the following changes are made:
–![]() Original packet mapped IP is changed to the real IP
Original packet mapped IP is changed to the real IP
Instant Messaging Inspection
This section describes the IM inspection engine. This section includes the following topics:
IM Inspection Overview
The IM inspect engine lets you apply fine grained controls on the IM application to control the network usage and stop leakage of confidential data, propagation of worms, and other threats to the corporate network.
Adding a Class Map for IM Inspection
Use the Add Service Policy Rule Wizard - Rule Actions dialog box to configure IP Options inspection.
This wizard is available from the Configuration > Firewall > Service Policy Rules > Add > Add Service Policy Rule Wizard - Rule Actions dialog box.
Step 1![]() Choose Configuration > Firewall > Objects > Class Maps > Instant Messaging (IM). The table displaying the configured class maps for Instant Messaging Inspection appears.
Choose Configuration > Firewall > Objects > Class Maps > Instant Messaging (IM). The table displaying the configured class maps for Instant Messaging Inspection appears.
Step 2![]() To add a new class map, click Add. The Add Instant Messaging (IM) Traffic Class Map dialog box appears.
To add a new class map, click Add. The Add Instant Messaging (IM) Traffic Class Map dialog box appears.
Step 3![]() Enter a name for the class map.
Enter a name for the class map.
Step 4![]() (Optional) Enter a description for the class map. The description can contain up to 200 characters.
(Optional) Enter a description for the class map. The description can contain up to 200 characters.
Step 5![]() In the Match Option field, click an option for the class map:
In the Match Option field, click an option for the class map:
Step 6![]() Click Add to add a match criteria for the class map. The Add Instant Messaging (IM) Match Criterion dialog box appears.
Click Add to add a match criteria for the class map. The Add Instant Messaging (IM) Match Criterion dialog box appears.
Step 7![]() In the Match Type field, click the Match or No Match radio button.
In the Match Type field, click the Match or No Match radio button.
Step 8![]() In the Criterion drop-down list, select one of the following options and specify the criteria value. Depending on which option you select, the Value fields dynamically refresh to display the appropriate values for that criteria.
In the Criterion drop-down list, select one of the following options and specify the criteria value. Depending on which option you select, the Value fields dynamically refresh to display the appropriate values for that criteria.
- Protocol—Select to match traffic of a specific IM protocol, such as Yahoo Messenger or MSN Messenger.
- Service—Select to match a specific IM service, such as chat, file-transfer, webcam, voice-chat, conference, or games.
- Version—Select to match the version of the IM message. In the Value fields, click the Regular Expression or Regular Expression Class option and select an expression from the drop-down list.
- Client Login Name—Select to match the source login name of the IM message. In the Value fields, click the Regular Expression or Regular Expression Class option and select an expression from the drop-down list.
- Client Peer Login Name—Select to match the destination login name of the IM message. In the Value fields, click the Regular Expression or Regular Expression Class option and select an expression from the drop-down list.
- Source IP Address—Select to match the source IP address of the IM message. In the Value fields, enter the IP address and netmask of the message source.
- Destination IP Address—Select to match the destination IP address of the IM message. In the Value fields, enter the IP address and netmask of the message destination.
- Filename—Select to match the filename of the IM message. In the Value fields, click the Regular Expression or Regular Expression Class option and select an expression from the drop-down list.
Step 9![]() Click OK to save the criteria. The Add Instant Messaging (IM) Match Criterion dialog box closes and the criteria appears in the Match Criterion table.
Click OK to save the criteria. The Add Instant Messaging (IM) Match Criterion dialog box closes and the criteria appears in the Match Criterion table.
Step 10![]() Click OK to save the class map.
Click OK to save the class map.
Select IM Map
The Select IM Map dialog box is accessible as follows:
Add/Edit Service Policy Rule Wizard > Rule Actions > Protocol Inspection Tab > Select IM Map
The Select IM Map dialog box lets you select or create a new IM map. An IM map lets you change the configuration values used for IM application inspection. The Select IM Map table provides a list of previously configured maps that you can select for application inspection.
IP Options Inspection
This section describes the IP Options inspection engine. This section includes the following topics:
- IP Options Inspection Overview
- Configuring IP Options Inspection
- Select IP Options Inspect Map
- IP Options Inspect Map
- Add/Edit IP Options Inspect Map
IP Options Inspection Overview
Each IP packet contains an IP header with the Options field. The Options field, commonly referred to as IP Options, provide for control functions that are required in some situations but unnecessary for most common communications. In particular, IP Options include provisions for time stamps, security, and special routing. Use of IP Options is optional, and the field can contain zero, one, or more options.
You can configure IP Options inspection to control which IP packets with specific IP options are allowed through the ASA. Configuring this inspection instructs the ASA to allow a packet to pass or to clear the specified IP options and then allow the packet to pass.
IP Options inspection can check for the following three IP options in a packet:
- End of Options List (EOOL) or IP Option 0—This option, which contains just a single zero byte, appears at the end of all options to mark the end of a list of options. This might not coincide with the end of the header according to the header length.
- No Operation (NOP) or IP Option 1—The Options field in the IP header can contain zero, one, or more options, which makes the total length of the field variable. However, the IP header must be a multiple of 32 bits. If the number of bits of all options is not a multiple of 32 bits, the NOP option is used as “internal padding” to align the options on a 32-bit boundary.
- Router Alert (RTRALT) or IP Option 20—This option notifies transit routers to inspect the contents of the packet even when the packet is not destined for that router. This inspection is valuable when implementing RSVP and similar protocols require relatively complex processing from the routers along the packets delivery path.

Note![]() IP Options inspection is included by default in the global inspection policy. Therefore, the ASA allows RSVP traffic that contains packets with the Router Alert option (option 20) when the ASA is in routed mode.
IP Options inspection is included by default in the global inspection policy. Therefore, the ASA allows RSVP traffic that contains packets with the Router Alert option (option 20) when the ASA is in routed mode.
Dropping RSVP packets containing the Router Alert option can cause problems in VoIP implementations.
When you configure the ASA to clear the Router Alert option from IP headers, the IP header changes in the following ways:
- The Options field is padded so that the field ends on a 32 bit boundary.
- Internet header length (IHL) changes.
- The total length of the packet changes.
- The checksum is recomputed.
If an IP header contains additional options other than EOOL, NOP, or RTRALT, regardless of whether the ASA is configured to allow these options, the ASA will drop the packet.
Configuring IP Options Inspection
Use the Add Service Policy Rule Wizard - Rule Actions dialog box to configure IP Options inspection.
This wizard is available from the Configuration > Firewall > Service Policy Rules > Add > Add Service Policy Rule Wizard - Rule Actions dialog box.
Step 1![]() Open the Add Service Policy Rule Wizard by selecting Configuration > Firewall > Service Policy Rules > Add.
Open the Add Service Policy Rule Wizard by selecting Configuration > Firewall > Service Policy Rules > Add.
Perform the steps to complete the Service Policy, Traffic Classification Criteria, and Traffic Match - Destination Port pages of the wizard. See Adding a Service Policy Rule for Through Traffic.
The Add Service Policy Rule Wizard - Rule Actions dialog box opens.
Step 2![]() Check the IP-Options check box.
Check the IP-Options check box.
The Select IP Options Inspect Map dialog box opens.
Step 4![]() Perform one of the following:
Perform one of the following:
- Click the Use the default IP-Options inspection map radio button to use the default IP Options map. The default map drops packets containing all the inspected IP options, namely End of Options List (EOOL), No Operation (NOP), and Router Alert (RTRALT).
- Click the Select an IP-Options inspect map for fine control over inspection radio button to select a defined application inspection map.
- Click Add to open the Add IP-Options Inspect Map dialog box and create a new inspection map.
Step 5![]() (Optional) If you clicked Add to create a new inspection map, define the following values for IP Options Inspection:
(Optional) If you clicked Add to create a new inspection map, define the following values for IP Options Inspection:
a.![]() Enter a name for the inspection map.
Enter a name for the inspection map.
b.![]() Enter a description for the inspection map, up to 200 characters long.
Enter a description for the inspection map, up to 200 characters long.
c.![]() From the Parameters area, select which IP options you want to pass through the ASA or clear and then pass through the ASA:
From the Parameters area, select which IP options you want to pass through the ASA or clear and then pass through the ASA:
–![]() Allow packets with the End of Options List (EOOL) option
Allow packets with the End of Options List (EOOL) option
This option, which contains just a single zero byte, appears at the end of all options to mark the end of a list of options. This might not coincide with the end of the header according to the header length.
–![]() Allow packets with the No Operation (NOP) option
Allow packets with the No Operation (NOP) option
The Options field in the IP header can contain zero, one, or more options, which makes the total length of the field variable. However, the IP header must be a multiple of 32 bits. If the number of bits of all options is not a multiple of 32 bits, the NOP option is used as “internal padding” to align the options on a 32-bit boundary.
–![]() Allow packets with the Router Alert (RTRALT) option
Allow packets with the Router Alert (RTRALT) option
This option notifies transit routers to inspect the contents of the packet even when the packet is not destined for that router. This inspection is valuable when implementing RSVP and similar protocols require relatively complex processing from the routers along the packets delivery path.
–![]() Clear the option value from the packets
Clear the option value from the packets
When an option is checked, the Clear the option value from the packets check box becomes available for that option. Select the Clear the option value from the packets check box to clear the option from the packet before allowing the packet through the ASA.
Select IP Options Inspect Map
The Select IP Options Inspect Map dialog box is accessible as follows:
Add/Edit Service Policy Rule Wizard > Rule Actions > Protocol Inspection Tab > Select IM Map
The Select IP-Options Inspect Map dialog box lets you select or create a new IP Options inspection map. Use this inspection map to control whether the ASA drops, passes, or clears IP packets containing the following IP options—End of Options List, No Operations, and Router Alert.
- Use the default IP-Options inspection map—Specifies to use the default IP Options map. The default map drops packets containing all the inspected IP options, namely End of Options List (EOOL), No Operation (NOP), and Router Alert (RTRALT).
- Select an IP-Options map for fine control over inspection — Lets you select a defined application inspection map or add a new one.
- Add—Opens the Add IP Options Inspect Map dialog box for the inspection.
IP Options Inspect Map
The IP Options Inspect Maps pane lets you view previously configured IP Options inspection maps. An IP Options inspection map lets you change the default configuration values used for IP Option inspection.
You can configure IP Options inspection to control which IP packets with specific IP options are allowed through the security appliance. Configuring this inspection instructs the security appliance to allow a packet to pass or to clear the specified IP options and then allow the packet to pass.
In particular, you can control whether the security appliance drops, clears, or passes packets containing the Router Alert (RTRALT) option. Dropping RSVP packets containing the Router Alert option can cause problems in VoIP implementations. Therefore, you can create IP Options inspection maps to pass packets containing the RTRALT option.
IP Options Inspect Maps—Table that lists the defined IP Options inspect maps.
Add—Configures a new IP Options inspect map.
Edit—Edits an existing IP Options inspect map. To edit an IP Options inspect map, choose the entry in the table and click Edit.
Delete—Deletes the inspect map selected in the IP Options Inspect Maps table.
Add/Edit IP Options Inspect Map
The Add/Edit IP Options Inspect Map lets you configure the settings for IP Options inspection maps.
- Name—When adding an IP Options inspection map, enter the name of the map. When editing a map, the name of the previously configured map is shown.
- Description—Enter the description of the IP Options inspection map, up to 200 characters in length.
- Parameters—Select which IP options you want to pass through the ASA or clear and then pass through the ASA:
–![]() Allow packets with the End of Options List (EOOL) option
Allow packets with the End of Options List (EOOL) option
This option, which contains just a single zero byte, appears at the end of all options to mark the end of a list of options. This might not coincide with the end of the header according to the header length.
–![]() Allow packets with the No Operation (NOP) option
Allow packets with the No Operation (NOP) option
The Options field in the IP header can contain zero, one, or more options, which makes the total length of the field variable. However, the IP header must be a multiple of 32 bits. If the number of bits of all options is not a multiple of 32 bits, the NOP option is used as “internal padding” to align the options on a 32-bit boundary.
–![]() Allow packets with the Router Alert (RTRALT) option
Allow packets with the Router Alert (RTRALT) option
This option notifies transit routers to inspect the contents of the packet even when the packet is not destined for that router. This inspection is valuable when implementing RSVP and similar protocols require relatively complex processing from the routers along the packets delivery path.
–![]() Clear the option value from the packets
Clear the option value from the packets
When an option is checked, the Clear the option value from the packets check box becomes available for that option. Select the Clear the option value from the packets check box to clear the option from the packet before allowing the packet through the ASA.
IPsec Pass Through Inspection
This section describes the IPsec Pass Through inspection engine. This section includes the following topics:
- IPsec Pass Through Inspection Overview
- Select IPsec-Pass-Thru Map
- IPsec Pass Through Inspect Map
- Add/Edit IPsec Pass Thru Policy Map (Security Level)
- Add/Edit IPsec Pass Thru Policy Map (Details)
IPsec Pass Through Inspection Overview
Internet Protocol Security (IPsec) is a protocol suite for securing IP communications by authenticating and encrypting each IP packet of a data stream. IPsec also includes protocols for establishing mutual authentication between agents at the beginning of the session and negotiation of cryptographic keys to be used during the session. IPsec can be used to protect data flows between a pair of hosts (for example, computer users or servers), between a pair of security gateways (such as routers or firewalls), or between a security gateway and a host.
IPsec Pass Through application inspection provides convenient traversal of ESP (IP protocol 50) and AH (IP protocol 51) traffic associated with an IKE UDP port 500 connection. It avoids lengthy ACL configuration to permit ESP and AH traffic and also provides security using timeout and max connections.
Specify IPsec Pass Through inspection parameters to identify a specific map to use for defining the parameters for the inspection. Configure a policy map for Specify IPsec Pass Through inspection to access the parameters configuration, which lets you specify the restrictions for ESP or AH traffic. You can set the per client max connections and the idle timeout in parameters configuration.
NAT and non-NAT traffic is permitted. However, PAT is not supported.
Select IPsec-Pass-Thru Map
The Select IPsec-Pass-Thru Map dialog box is accessible as follows:
Add/Edit Service Policy Rule Wizard > Rule Actions > Protocol Inspection Tab > Select IPsec-Pass-Thru Map
The Select IPsec-Pass-Thru dialog box lets you select or create a new IPsec map. An IPsec map lets you change the configuration values used for IPsec application inspection. The Select IPsec Map table provides a list of previously configured maps that you can select for application inspection.
IPsec Pass Through Inspect Map
The IPsec Pass Through Inspect Map dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > IPsec Pass Through
The IPsec Pass Through pane lets you view previously configured IPsec Pass Through application inspection maps. An IPsec Pass Through map lets you change the default configuration values used for IPsec Pass Through application inspection. You can use an IPsec Pass Through map to permit certain flows without using an ACL.
- IPsec Pass Through Inspect Maps—Table that lists the defined IPsec Pass Through inspect maps.
- Add—Configures a new IPsec Pass Through inspect map. To edit an IPsec Pass Through inspect map, select the IPsec Pass Through entry in the IPsec Pass Through Inspect Maps table and click Customize.
- Delete—Deletes the inspect map selected in the IPsec Pass Through Inspect Maps table.
- Security Level—Select the security level (high or low).
Maximum ESP flows per client: Unlimited.
Maximum AH flows per client: Unlimited.
Maximum ESP flows per client:10.
Maximum AH flows per client: 10.
–![]() Customize—Opens the Add/Edit IPsec Pass Thru Policy Map dialog box for additional settings.
Customize—Opens the Add/Edit IPsec Pass Thru Policy Map dialog box for additional settings.
–![]() Default Level—Sets the security level back to the default level of Low.
Default Level—Sets the security level back to the default level of Low.
Add/Edit IPsec Pass Thru Policy Map (Security Level)
The Add/Edit IPsec Pass Thru Policy Map (Security Level) dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > IPsec Pass Through> IPsec Pass Through Inspect Map > Basic View
The Add/Edit IPsec Pass Thru Policy Map pane lets you configure the security level and additional settings for IPsec Pass Thru application inspection maps.
- Name—When adding an IPsec Pass Thru map, enter the name of the IPsec Pass Thru map. When editing an IPsec Pass Thru map, the name of the previously configured IPsec Pass Thru map is shown.
- Security Level—Select the security level (high or low).
Maximum ESP flows per client: Unlimited.
Maximum AH flows per client: Unlimited.
Maximum ESP flows per client:10.
Maximum AH flows per client: 10.
–![]() Default Level—Sets the security level back to the default level of Low.
Default Level—Sets the security level back to the default level of Low.
Add/Edit IPsec Pass Thru Policy Map (Details)
The Add/Edit IPsec Pass Thru Policy Map (Details) dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps >IPsec Pass Through > IPsec Pass Through Inspect Map > Advanced View
The Add/Edit IPsec Pass Thru Policy Map pane lets you configure the security level and additional settings for IPsec Pass Thru application inspection maps.
- Name—When adding an IPsec Pass Thru map, enter the name of the IPsec Pass Thru map. When editing an IPsec Pass Thru map, the name of the previously configured IPsec Pass Thru map is shown.
- Description—Enter the description of the IPsec Pass Through map, up to 200 characters in length.
- Security Level—Shows the security level settings to configure.
- Parameters—Configures ESP and AH parameter settings.
–![]() Limit ESP flows per client—Limits ESP flows per client.
Limit ESP flows per client—Limits ESP flows per client.
Maximum—Specify maximum limit.
–![]() Apply ESP idle timeout—Applies ESP idle timeout.
Apply ESP idle timeout—Applies ESP idle timeout.
–![]() Limit AH flows per client—Limits AH flows per client.
Limit AH flows per client—Limits AH flows per client.
Maximum—Specify maximum limit.
IPv6 Inspection
- Information about IPv6 Inspection
- Default Settings for IPv6 Inspection
- (Optional) Configuring an IPv6 Inspection Policy Map
- Configuring IPv6 Inspection
Information about IPv6 Inspection
IPv6 inspection lets you selectively log or drop IPv6 traffic based on the extension header. In addition, IPv6 inspection can check conformance to RFC 2460 for type and order of extension headers in IPv6 packets.
Default Settings for IPv6 Inspection
If you enable IPv6 inspection and do not specify an inspection policy map, then the default IPv6 inspection policy map is used, and the following actions are taken:
- Allows only known IPv6 extension headers
- Enforces the order of IPv6 extension headers as defined in the RFC 2460 specification
If you create an inspection policy map, the above actions are taken by default unless you explicitly disable them.
(Optional) Configuring an IPv6 Inspection Policy Map
To identify extension headers to drop or log, and/or to disable packet verification, create an IPv6 inspection policy map to be used by the service policy.
Detailed Steps
Step 1![]() Choose Configuration > Firewall > Objects > Inspect Maps > IPv6. The Configure IPv6 Maps pane appears.
Choose Configuration > Firewall > Objects > Inspect Maps > IPv6. The Configure IPv6 Maps pane appears.
Step 2![]() Click Add. The Add IPv6 Inspection Map dialog box appears.
Click Add. The Add IPv6 Inspection Map dialog box appears.
Step 3![]() Enter a name and description for the inspection map.
Enter a name and description for the inspection map.
By default, the Enforcement tab is selected and the following options are selected:
When Permit only known extension headers is selected, the ASA verifies the IPv6 extension header.
When Enforce extension header order is selected, the order of IPv6 extension headers as defined in the RFC 2460 Specification is enforced.
When these options are specified and an error is detected, the ASA drops the packet and logs the action.
Step 4![]() To configure matching in the extension header, click the Header Matches tab.
To configure matching in the extension header, click the Header Matches tab.
Step 5![]() Click Add to add a match. The Add IPv6 Inspect dialog box appears.
Click Add to add a match. The Add IPv6 Inspect dialog box appears.
a.![]() Select a criterion for the match.
Select a criterion for the match.
When you select any of the following criteria, you can configure to the ASA to drop or log when an IPv6 packet arrives matching the criterion:
–![]() Encapsulating Security Payload (ESP) header
Encapsulating Security Payload (ESP) header
–![]() Routing header—When Routing header is selected and an IPv6 routing extension header is detected, the ASA takes the specified action when the routing type is matched or a number when the specified routing type range is matched.
Routing header—When Routing header is selected and an IPv6 routing extension header is detected, the ASA takes the specified action when the routing type is matched or a number when the specified routing type range is matched.
–![]() Header count—When Header count is selected and an IPv6 routing extension header is detected, the ASA takes the specified action when number of IPv6 extension headers in the packet is more than the specified value.
Header count—When Header count is selected and an IPv6 routing extension header is detected, the ASA takes the specified action when number of IPv6 extension headers in the packet is more than the specified value.
–![]() Routing header address count—When Routing header address count is selected, and an IPv6 routing extension header is detected, the ASA takes the specified action when the number of addresses in the type 0 routing header is more than the value you configure.
Routing header address count—When Routing header address count is selected, and an IPv6 routing extension header is detected, the ASA takes the specified action when the number of addresses in the type 0 routing header is more than the value you configure.
b.![]() Click OK to save the match criterion.
Click OK to save the match criterion.
Step 6![]() Repeat Step 5 for each header you want to match.
Repeat Step 5 for each header you want to match.
Step 7![]() Click OK to save the IPv6 inspect map.
Click OK to save the IPv6 inspect map.
Configuring IPv6 Inspection
Detailed Steps
Step 1![]() Configure a service policy on the Configuration > Firewall > Service Policy Rules pane according to Chapter1, “Service Policy”
Configure a service policy on the Configuration > Firewall > Service Policy Rules pane according to Chapter1, “Service Policy”
You can configure IPv6 inspection as part of a new service policy rule, or you can edit an existing service policy.
Step 2![]() On the Rule Actions dialog box, click the Protocol Inspections tab.
On the Rule Actions dialog box, click the Protocol Inspections tab.
Step 3![]() Check the IPv6 check box.
Check the IPv6 check box.
Step 4![]() (Optional) To add an IPv6 inspection policy map that you configured in the (Optional) Configuring an IPv6 Inspection Policy Map:
(Optional) To add an IPv6 inspection policy map that you configured in the (Optional) Configuring an IPv6 Inspection Policy Map:
The Select IPv6 Inspect Map dialog box appears.
b.![]() Select the map name, and click OK.
Select the map name, and click OK.
Alternatively, you can click the Add button to add a new inspection policy map.
NetBIOS Inspection
This section describes the IM inspection engine. This section includes the following topics:
NetBIOS Inspection Overview
NetBIOS inspection is enabled by default. The NetBios inspection engine translates IP addresses in the NetBios name service (NBNS) packets according to the ASA NAT configuration.
Select NETBIOS Map
The Select NETBIOS Map dialog box is accessible as follows:
Add/Edit Service Policy Rule Wizard > Rule Actions > Protocol Inspection Tab > Select NetBIOS Map
The Select NETBIOS Map dialog box lets you select or create a new NetBIOS map. A NetBIOS map lets you change the configuration values used for NetBIOS application inspection. The Select NetBIOS Map table provides a list of previously configured maps that you can select for application inspection.
NetBIOS Inspect Map
The NetBIOS Inspect Map dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > NetBIOS
The NetBIOS pane lets you view previously configured NetBIOS application inspection maps. A NetBIOS map lets you change the default configuration values used for NetBIOS application inspection.
NetBIOS application inspection performs NAT for the embedded IP address in the NetBIOS name service packets and NetBIOS datagram services packets. It also enforces protocol conformance, checking the various count and length fields for consistency.
Add/Edit NetBIOS Policy Map
The Add/Edit NetBIOS Policy Map dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > NetBIOS > NetBIOS Inspect Map > View
The Add/Edit NetBIOS Policy Map pane lets you configure the protocol violation settings for NetBIOS application inspection maps.
- Name—When adding a NetBIOS map, enter the name of the NetBIOS map. When editing an NetBIOS map, the name of the previously configured NetBIOS map is shown.
- Description—Enter the description of the NetBIOS map, up to 200 characters in length.
- Check for protocol violations—Checks for protocol violations and executes specified action.
PPTP Inspection
PPTP is a protocol for tunneling PPP traffic. A PPTP session is composed of one TCP channel and usually two PPTP GRE tunnels. The TCP channel is the control channel used for negotiating and managing the PPTP GRE tunnels. The GRE tunnels carries PPP sessions between the two hosts.
When enabled, PPTP application inspection inspects PPTP protocol packets and dynamically creates the GRE connections and xlates necessary to permit PPTP traffic. Only Version 1, as defined in RFC 2637, is supported.
PAT is only performed for the modified version of GRE [RFC 2637] when negotiated over the PPTP TCP control channel. Port Address Translation is not performed for the unmodified version of GRE [RFC 1701, RFC 1702].
Specifically, the ASA inspects the PPTP version announcements and the outgoing call request/response sequence. Only PPTP Version 1, as defined in RFC 2637, is inspected. Further inspection on the TCP control channel is disabled if the version announced by either side is not Version 1. In addition, the outgoing-call request and reply sequence are tracked. Connections and xlates are dynamic allocated as necessary to permit subsequent secondary GRE data traffic.
The PPTP inspection engine must be enabled for PPTP traffic to be translated by PAT. Additionally, PAT is only performed for a modified version of GRE (RFC2637) and only if it is negotiated over the PPTP TCP control channel. PAT is not performed for the unmodified version of GRE (RFC 1701 and RFC 1702).
As described in RFC 2637, the PPTP protocol is mainly used for the tunneling of PPP sessions initiated from a modem bank PAC (PPTP Access Concentrator) to the headend PNS (PPTP Network Server). When used this way, the PAC is the remote client and the PNS is the server.
However, when used for VPN by Windows, the interaction is inverted. The PNS is a remote single-user PC that initiates connection to the head-end PAC to gain access to a central network.
SMTP and Extended SMTP Inspection
This section describes the IM inspection engine. This section includes the following topics:
- SMTP and ESMTP Inspection Overview
- Select ESMTP Map
- ESMTP Inspect Map
- MIME File Type Filtering
- Add/Edit ESMTP Policy Map (Security Level)
- Add/Edit ESMTP Policy Map (Details)
- Add/Edit ESMTP Inspect
SMTP and ESMTP Inspection Overview
ESMTP application inspection provides improved protection against SMTP-based attacks by restricting the types of SMTP commands that can pass through the ASA and by adding monitoring capabilities.
ESMTP is an enhancement to the SMTP protocol and is similar is most respects to SMTP. For convenience, the term SMTP is used in this document to refer to both SMTP and ESMTP. The application inspection process for extended SMTP is similar to SMTP application inspection and includes support for SMTP sessions. Most commands used in an extended SMTP session are the same as those used in an SMTP session but an ESMTP session is considerably faster and offers more options related to reliability and security, such as delivery status notification.
Extended SMTP application inspection adds support for these extended SMTP commands, including AUTH, EHLO, ETRN, HELP, SAML, SEND, SOML, STARTTLS, and VRFY. Along with the support for seven RFC 821 commands (DATA, HELO, MAIL, NOOP, QUIT, RCPT, RSET), the ASA supports a total of fifteen SMTP commands.
Other extended SMTP commands, such as ATRN, ONEX, VERB, CHUNKING, and private extensions and are not supported. Unsupported commands are translated into Xs, which are rejected by the internal server. This results in a message such as “500 Command unknown: 'XXX'.” Incomplete commands are discarded.
The ESMTP inspection engine changes the characters in the server SMTP banner to asterisks except for the “2”, “0”, “0” characters. Carriage return (CR) and linefeed (LF) characters are ignored.
With SMTP inspection enabled, a Telnet session used for interactive SMTP may hang if the following rules are not observed: SMTP commands must be at least four characters in length; must be terminated with carriage return and line feed; and must wait for a response before issuing the next reply.
An SMTP server responds to client requests with numeric reply codes and optional human-readable strings. SMTP application inspection controls and reduces the commands that the user can use as well as the messages that the server returns. SMTP inspection performs three primary tasks:
- Restricts SMTP requests to seven basic SMTP commands and eight extended commands.
- Monitors the SMTP command-response sequence.
- Generates an audit trail—Audit record 108002 is generated when invalid character embedded in the mail address is replaced. For more information, see RFC 821.
SMTP inspection monitors the command and response sequence for the following anomalous signatures:
- Truncated commands.
- Incorrect command termination (not terminated with <CR><LR>).
- The MAIL and RCPT commands specify who are the sender and the receiver of the mail. Mail addresses are scanned for strange characters. The pipeline character (|) is deleted (changed to a blank space) and “<” ‚”>” are only allowed if they are used to define a mail address (“>” must be preceded by “<”).
- Unexpected transition by the SMTP server.
- For unknown commands, the ASA changes all the characters in the packet to X. In this case, the server generates an error code to the client. Because of the change in the packed, the TCP checksum has to be recalculated or adjusted.
- TCP stream editing.
- Command pipelining.
Select ESMTP Map
The Select ESMTP Map dialog box is accessible as follows:
Add/Edit Service Policy Rule Wizard > Rule Actions > Protocol Inspection Tab >Select ESMTP Map
The Select ESMTP Map dialog box lets you select or create a new ESMTP map. An ESMTP map lets you change the configuration values used for ESMTP application inspection. The Select ESMTP Map table provides a list of previously configured maps that you can select for application inspection.
ESMTP Inspect Map
The ESMTP Inspect Map dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > ESMTP
The ESMTP pane lets you view previously configured ESMTP application inspection maps. An ESMTP map lets you change the default configuration values used for ESMTP application inspection.
Since ESMTP traffic can be a main source of attack from spam, phising, malformed messages, buffer overflows, and buffer underflows, detailed packet inspection and control of ESMTP traffic are supported. Application security and protocol conformance enforce the sanity of the ESMTP message as well as detect several attacks, block senders and receivers, and block mail relay.
- ESMTP Inspect Maps—Table that lists the defined ESMTP inspect maps.
- Add—Configures a new ESMTP inspect map. To edit an ESMTP inspect map, choose the ESMTP entry in the ESMTP Inspect Maps table and click Customize.
- Delete—Deletes the inspect map selected in the ESMTP Inspect Maps table.
- Security Level—Select the security level (high, medium, or low).
Log if command line length is greater than 512
Log if command recipient count is greater than 100
Log if body line length is greater than 1000
Log if sender address length is greater than 320
Log if MIME file name length is greater than 255
Drop Connections if command line length is greater than 512
Drop Connections if command recipient count is greater than 100
Drop Connections if body line length is greater than 1000
Drop Connections if sender address length is greater than 320
Drop Connections if MIME file name length is greater than 255
Drop Connections if command line length is greater than 512
Drop Connections if command recipient count is greater than 100
Drop Connections if body line length is greater than 1000
Drop Connections and log if sender address length is greater than 320
Drop Connections and log if MIME file name length is greater than 255
–![]() MIME File Type Filtering—Opens the MIME Type Filtering dialog box to configure MIME file type filters.
MIME File Type Filtering—Opens the MIME Type Filtering dialog box to configure MIME file type filters.
–![]() Customize—Opens the Add/Edit ESMTP Policy Map dialog box for additional settings.
Customize—Opens the Add/Edit ESMTP Policy Map dialog box for additional settings.
–![]() Default Level—Sets the security level back to the default level of Low.
Default Level—Sets the security level back to the default level of Low.
MIME File Type Filtering
The MIME File Type Filtering dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > ESMTP > MIME File Type Filtering
The MIME File Type Filtering dialog box lets you configure the settings for a MIME file type filter.
- Match Type—Shows the match type, which can be a positive or negative match.
- Criterion—Shows the criterion of the inspection.
- Value—Shows the value to match in the inspection.
- Action—Shows the action if the match condition is met.
- Log—Shows the log state.
- Add—Opens the Add MIME File Type Filter dialog box to add a MIME file type filter.
- Edit—Opens the Edit MIME File Type Filter dialog box to edit a MIME file type filter.
- Delete—Deletes a MIME file type filter.
- Move Up—Moves an entry up in the list.
- Move Down—Moves an entry down in the list.
Add/Edit ESMTP Policy Map (Security Level)
The Add/Edit ESMTP Policy Map (Security Level) dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > ESMTP > ESMTP Inspect Map > Basic View
The Add/Edit ESMTP Policy Map pane lets you configure the security level and additional settings for ESMTP application inspection maps.
- Name—When adding an ESMTP map, enter the name of the ESMTP map. When editing an ESMTP map, the name of the previously configured ESMTPS map is shown.
- Description—Enter the description of the ESMTP map, up to 200 characters in length.
- Security Level—Select the security level (high, medium, or low).
Log if command line length is greater than 512
Log if command recipient count is greater than 100
Log if body line length is greater than 1000
Log if sender address length is greater than 320
Log if MIME file name length is greater than 255
Drop Connections if command line length is greater than 512
Drop Connections if command recipient count is greater than 100
Drop Connections if body line length is greater than 1000
Drop Connections if sender address length is greater than 320
Drop Connections if MIME file name length is greater than 255
Drop Connections if command line length is greater than 512
Drop Connections if command recipient count is greater than 100
Drop Connections if body line length is greater than 1000
Drop Connections and log if sender address length is greater than 320
Drop Connections and log if MIME file name length is greater than 255
–![]() MIME File Type Filtering—Opens the MIME Type Filtering dialog box to configure MIME file type filters.
MIME File Type Filtering—Opens the MIME Type Filtering dialog box to configure MIME file type filters.
–![]() Default Level—Sets the security level back to the default level of Low.
Default Level—Sets the security level back to the default level of Low.
Add/Edit ESMTP Policy Map (Details)
The Add/Edit ESMTP Policy Map (Details) dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > ESMTP > ESMTP Inspect Map > Advanced View
The Add/Edit ESMTP Policy Map pane lets you configure the security level and additional settings for ESMTP application inspection maps.
- Name—When adding an ESMTP map, enter the name of the ESMTP map. When editing an ESMTP map, the name of the previously configured ESMTP map is shown.
- Description—Enter the description of the ESMTP map, up to 200 characters in length.
- Security Level—Shows the security level and mime file type filtering settings to configure.
- Parameters—Tab that lets you configure the parameters for the ESMTP inspect map.
–![]() Mask server banner—Enforces banner obfuscation.
Mask server banner—Enforces banner obfuscation.
–![]() Configure Mail Relay—Enables ESMTP mail relay.
Configure Mail Relay—Enables ESMTP mail relay.
Domain Name—Specifies a local domain.
Action—Drop connection or log.
–![]() Match Type—Shows the match type, which can be a positive or negative match.
Match Type—Shows the match type, which can be a positive or negative match.
–![]() Criterion—Shows the criterion of the ESMTP inspection.
Criterion—Shows the criterion of the ESMTP inspection.
–![]() Value—Shows the value to match in the ESMTP inspection.
Value—Shows the value to match in the ESMTP inspection.
–![]() Action—Shows the action if the match condition is met.
Action—Shows the action if the match condition is met.
–![]() Add—Opens the Add ESMTP Inspect dialog box to add an ESMTP inspection.
Add—Opens the Add ESMTP Inspect dialog box to add an ESMTP inspection.
–![]() Edit—Opens the Edit ESMTP Inspect dialog box to edit an ESMTP inspection.
Edit—Opens the Edit ESMTP Inspect dialog box to edit an ESMTP inspection.
–![]() Delete—Deletes an ESMTP inspection.
Delete—Deletes an ESMTP inspection.
Add/Edit ESMTP Inspect
The Add/Edit ESMTP Inspect dialog box is accessible as follows:
Configuration > Global Objects > Inspect Maps > ESMTP > ESMTP Inspect Map > Advanced View > Add/Edit ESMTP Inspect
The Add/Edit ESMTP Inspect dialog box lets you define the match criterion and value for the ESMTP inspect map.
For example, if No Match is selected on the string “example.com,” then any traffic that contains “example.com” is excluded from the class map.
–![]() Body Length—Match body length at specified length in bytes.
Body Length—Match body length at specified length in bytes.
–![]() Body Line Length—Match body line length matching at specified length in bytes.
Body Line Length—Match body line length matching at specified length in bytes.
–![]() Commands—Match commands exchanged in the ESMTP protocol.
Commands—Match commands exchanged in the ESMTP protocol.
–![]() Command Recipient Count—Match command recipient count greater than number specified.
Command Recipient Count—Match command recipient count greater than number specified.
–![]() Command Line Length—Match command line length greater than length specified in bytes.
Command Line Length—Match command line length greater than length specified in bytes.
–![]() EHLO Reply Parameters—Match an ESMTP ehlo reply parameter.
EHLO Reply Parameters—Match an ESMTP ehlo reply parameter.
–![]() Header Length—Match header length at length specified in bytes.
Header Length—Match header length at length specified in bytes.
–![]() Header To Fields Count—Match header To fields count greater than number specified.
Header To Fields Count—Match header To fields count greater than number specified.
–![]() Invalid Recipients Count—Match invalid recipients count greater than number specified.
Invalid Recipients Count—Match invalid recipients count greater than number specified.
–![]() MIME File Type—Match MIME file type.
MIME File Type—Match MIME file type.
–![]() MIME Filename Length—Match MIME filename.
MIME Filename Length—Match MIME filename.
–![]() MIME Encoding—Match MIME encoding.
MIME Encoding—Match MIME encoding.
–![]() Sender Address—Match sender email address.
Sender Address—Match sender email address.
–![]() Sender Address Length—Match sender email address length.
Sender Address Length—Match sender email address length.
–![]() Greater Than Length—Body length in bytes.
Greater Than Length—Body length in bytes.
–![]() Action—Reset, drop connection, log.
Action—Reset, drop connection, log.
–![]() Greater Than Length—Body line length in bytes.
Greater Than Length—Body line length in bytes.
–![]() Action—Reset, drop connection, log.
Action—Reset, drop connection, log.
–![]() Add—Adds the selected command from the Available Commands table to the Selected Commands table.
Add—Adds the selected command from the Available Commands table to the Selected Commands table.
–![]() Remove—Removes the selected command from the Selected Commands table.
Remove—Removes the selected command from the Selected Commands table.
–![]() Primary Action—Mask, Reset, Drop Connection, None, Limit Rate (pps).
Primary Action—Mask, Reset, Drop Connection, None, Limit Rate (pps).
–![]() Rate Limit—Do not limit rate, Limit Rate (pps).
Rate Limit—Do not limit rate, Limit Rate (pps).
- Command Recipient Count Criterion Values—Specifies the value details for command recipient count match.
–![]() Greater Than Count—Specify command recipient count.
Greater Than Count—Specify command recipient count.
–![]() Action—Reset, drop connection, log.
Action—Reset, drop connection, log.
–![]() Greater Than Length—Command line length in bytes.
Greater Than Length—Command line length in bytes.
–![]() Action—Reset, drop connection, log.
Action—Reset, drop connection, log.
–![]() Add—Adds the selected parameter from the Available Parameters table to the Selected Parameters table.
Add—Adds the selected parameter from the Available Parameters table to the Selected Parameters table.
–![]() Remove—Removes the selected command from the Selected Commands table.
Remove—Removes the selected command from the Selected Commands table.
–![]() Action—Reset, Drop Connection, Mask, Log.
Action—Reset, Drop Connection, Mask, Log.
–![]() Greater Than Length—Header length in bytes.
Greater Than Length—Header length in bytes.
–![]() Action—Reset, Drop Connection, Mask, Log.
Action—Reset, Drop Connection, Mask, Log.
- Header To Fields Count Criterion Values—Specifies the value details for header To fields count match.
–![]() Greater Than Count—Specify command recipient count.
Greater Than Count—Specify command recipient count.
–![]() Action—Reset, drop connection, log.
Action—Reset, drop connection, log.
- Invalid Recipients Count Criterion Values—Specifies the value details for invalid recipients count match.
–![]() Greater Than Count—Specify command recipient count.
Greater Than Count—Specify command recipient count.
–![]() Action—Reset, drop connection, log.
Action—Reset, drop connection, log.
–![]() Regular Expression—Lists the defined regular expressions to match.
Regular Expression—Lists the defined regular expressions to match.
–![]() Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
–![]() Regular Expression Class—Lists the defined regular expression classes to match.
Regular Expression Class—Lists the defined regular expression classes to match.
–![]() Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Action—Reset, drop connection, log.
Action—Reset, drop connection, log.
–![]() Greater Than Length—MIME filename length in bytes.
Greater Than Length—MIME filename length in bytes.
–![]() Action—Reset, Drop Connection, Log.
Action—Reset, Drop Connection, Log.
–![]() Add—Adds the selected parameter from the Available Encodings table to the Selected Encodings table.
Add—Adds the selected parameter from the Available Encodings table to the Selected Encodings table.
–![]() Remove—Removes the selected command from the Selected Commands table.
Remove—Removes the selected command from the Selected Commands table.
–![]() Action—Reset, Drop Connection, Log.
Action—Reset, Drop Connection, Log.
–![]() Regular Expression—Lists the defined regular expressions to match.
Regular Expression—Lists the defined regular expressions to match.
–![]() Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
Manage—Opens the Manage Regular Expressions dialog box, which lets you configure regular expressions.
–![]() Regular Expression Class—Lists the defined regular expression classes to match.
Regular Expression Class—Lists the defined regular expression classes to match.
–![]() Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
Manage—Opens the Manage Regular Expression Class dialog box, which lets you configure regular expression class maps.
–![]() Action—Reset, Drop Connection, Log.
Action—Reset, Drop Connection, Log.
–![]() Greater Than Length—Sender address length in bytes.
Greater Than Length—Sender address length in bytes.
TFTP Inspection
TFTP inspection is enabled by default.
TFTP, described in RFC 1350, is a simple protocol to read and write files between a TFTP server and client.
The ASA inspects TFTP traffic and dynamically creates connections and translations, if necessary, to permit file transfer between a TFTP client and server. Specifically, the inspection engine inspects TFTP read request (RRQ), write request (WRQ), and error notification (ERROR).
A dynamic secondary channel and a PAT translation, if necessary, are allocated on a reception of a valid read (RRQ) or write (WRQ) request. This secondary channel is subsequently used by TFTP for file transfer or error notification.
Only the TFTP server can initiate traffic over the secondary channel, and at most one incomplete secondary channel can exist between the TFTP client and server. An error notification from the server closes the secondary channel.
TFTP inspection must be enabled if static PAT is used to redirect TFTP traffic.
 Feedback
Feedback