- Index
- Preface
- Product Overview
- Command-line Interfaces
- Configuring the Switch for the First Time
- Administering the Switch
- Configuring the Cisco IOS In Service Software Upgrade Process
- Configuring Interfaces
- Checking Port Status and Connectivity
- Configuring Supervisor Engine Redundancy Using RPR and SSO
- Configuring Cisco NSF with SSO Supervisor Engine Redundancy
- Environmental Monitoring and Power Management
- Configuring Power over Ethernet
- Configuring Energy Wise
- Configuring the Catalyst 4500 Series Switch with Cisco Network Assistant
- Configuring VLANs, VTP, and VMPS
- Configuring IP Unnumbered Interface
- Configuring Layer 2 Ethernet Interfaces
- Configuring SmartPort Macros
- Auto SmartPort Macro
- Configuring STP and MST
- Configuring Flex Links and the MAC Address-Table Move Update Feature
- Configuring Resilient Ethernet Protocol
- Configuring Optional STP Features
- Configuring EtherChannels
- Configuring IGMP Snooping and Filtering
- Configuring IPv6 MLD Snooping
- Configuring 802.1Q and Layer 2 Protocol Tunneling
- Configuring CDP
- Configuring LLDP and LLDP-MED
- Configuring UDLD
- Configuring Unidirectional Ethernet
- Configuring Layer 3 Interfaces
- Configuring Cisco Express Forwarding
- Configuring Unicast Reverse Path Forwarding
- Configuring IP Multicast
- Configuring ANCP Client
- Configuring Policy-Based Routing
- Configuring VRF-lite
- Configuring Quality of Service
- Configuring Voice Interfaces
- Configuring Private VLANs
- Configuring 802.1X Port-Based Authentication
- Configuring PPPoE Intermediate Agent
- Configuring Web-Based Authentication
- Configuring Port Security
- Configuring Control Plane Policing
- Configuring DHCP Snooping, IP Source Guard, and IPSG for Static Hosts
- Configuring Dynamic ARP Inspection
- Configuring Network Security with ACLs
- IPv6
- Port Unicast and Multicast Flood Blocking
- Configuring Storm Control
- Configuring SPAN and RSPAN
- Configuring System Message Logging
- Configuring SNMP
- Configuring NetFlow
- Configuring Ethernet CFM and OAM
- Configuring Y.1731 (AIS and RDI)
- Configuring Call Home
- Configuring Cisco IOS IP SLAs Operations
- Configuring RMON
- Performing Diagnostics
- Configuring WCCP Version 2 Services
- ROM Monitor
- Configuring MIB Support
- Acronyms
- About EtherChannel
- EtherChannel Configuration Guidelines and Restrictions
- Configuring EtherChannel
- Displaying EtherChannel to a Virtual Switch System
- Understanding Link-State Tracking
- Configuring Link-State Tracking
Configuring EtherChannel and Link State Tracking
This chapter describes how to use the command-line interface (CLI) to configure EtherChannel on the Catalyst 4500 series switch Layer 2 or Layer 3 interfaces. It also provides guidelines, procedures, and configuration examples.
EtherChannel provides automatic recovery for the loss of a link by redistributing the load across the remaining links. If a link fails, EtherChannel redirects traffic from the failed link to the remaining links in the channel without intervention. This chapter also describes how to configure link-state tracking.
This chapter includes the following major sections:
- About EtherChannel
- EtherChannel Configuration Guidelines and Restrictions
- Configuring EtherChannel
- Displaying EtherChannel to a Virtual Switch System
- Understanding Link-State Tracking
- Configuring Link-State Tracking

Note![]() The commands in the following sections can be used on all Ethernet interfaces on a Catalyst 4500 series switch, including the uplink ports on the supervisor engine.
The commands in the following sections can be used on all Ethernet interfaces on a Catalyst 4500 series switch, including the uplink ports on the supervisor engine.

Note![]() For complete syntax and usage information for the switch commands used in this chapter, look at the Cisco Catalyst 4500 Series Switch Command Reference and related publications at this location:
For complete syntax and usage information for the switch commands used in this chapter, look at the Cisco Catalyst 4500 Series Switch Command Reference and related publications at this location:
http://www.cisco.com/en/US/products/hw/switches/ps4324/index.html
If the command is not found in the Catalyst 4500 Command Reference, it is located in the larger Cisco IOS library. Refer to the Cisco IOS Command Reference and related publications at this location:
http://www.cisco.com/en/US/products/ps6350/index.html
About EtherChannel
EtherChannel bundles up to eight individual Ethernet links into a single logical ink that provides an aggregate bandwidth of up to 800 Mbps (Fast EtherChannel), 8 Gbps (Gigabit EtherChannel), or 80 Gbps (10 Gigabit EtherChannel) between a Catalyst 4500 or 4500X series switch and another switch or host.

Note![]() Because some linecards have a maximum bandwidth capacity toward the backplane, they can limit the aggregate bandwidth of an EtherChannel when all the EtherChannel members belong to the same linecard.
Because some linecards have a maximum bandwidth capacity toward the backplane, they can limit the aggregate bandwidth of an EtherChannel when all the EtherChannel members belong to the same linecard.
A Catalyst 4500 series switch supports a maximum of 64 EtherChannels. You can form an EtherChannel with up to eight compatibly configured Ethernet interfaces across modules in a Catalyst 4500 series switch. All interfaces in each EtherChannel must be the same speed and must be configured as either Layer 2 or Layer 3 interfaces.

Note![]() The network device to which a Catalyst 4500 series switch is connected may impose its own limits on the number of interfaces in an EtherChannel.
The network device to which a Catalyst 4500 series switch is connected may impose its own limits on the number of interfaces in an EtherChannel.
If a segment within an EtherChannel fails, traffic previously carried over the failed link switches to the remaining segments within the EtherChannel. When the segment fails, an SNMP trap is sent, identifying the switch, the EtherChannel, and the failed link. Inbound broadcast and multicast packets on one segment in an EtherChannel are blocked from returning on any other segment of the EtherChannel.

Note![]() The port channel link failure switchover for the Catalyst 4500 series switch was measured at 50 miliseconds, which provides SONET-like link failure switchover time.
The port channel link failure switchover for the Catalyst 4500 series switch was measured at 50 miliseconds, which provides SONET-like link failure switchover time.
These subsections describe how EtherChannel works:
Port Channel Interfaces
Each EtherChannel has a numbered port channel interface. A configuration applied to the port channel interface affects all physical interfaces assigned to that interface.

Note![]() QoS does not propagate to members. The defaults, QoS cos = 0 and QoS dscp = 0, apply on the port channel. Input or output policies applied on individual interfaces are ignored.
QoS does not propagate to members. The defaults, QoS cos = 0 and QoS dscp = 0, apply on the port channel. Input or output policies applied on individual interfaces are ignored.
After you configure an EtherChannel, the configuration that you apply to the port channel interface affects the EtherChannel; the configuration that you apply to the physical interfaces affects only the interface where you apply the configuration. To change the parameters of all ports in an EtherChannel, apply configuration commands to the port channel interface (such commands can be STP commands or commands to configure a Layer 2 EtherChannel as a trunk).
Configuring EtherChannels
These subsections describe how EtherChannels are configured:
EtherChannel Configuration Overview
You can configure EtherChannels manually or use the Port Aggregation Control Protocol (PAgP) or the Link Aggregation Control Protocol (LACP) (Cisco IOS Release 12.2(25)EWA and later), to form EtherChannels. The EtherChannel protocols allow ports with similar characteristics to form an EtherChannel through dynamic negotiation with connected network devices. PAgP is a Cisco-proprietary protocol and LACP is defined in IEEE 802.3ad.
PAgP and LACP do not interoperate. Ports configured to use PAgP cannot form EtherChannels with ports configured to use LACP and vice versa.
Table 22-1 lists the user-configurable EtherChannel modes.
Manual EtherChannel Configuration
Manually configured EtherChannel ports do not exchange EtherChannel protocol packets. A manually configured EtherChannel forms only when you configure all ports compatibly in the EtherChannel.
PAgP EtherChannel Configuration
PAgP supports the automatic creation of EtherChannels by exchanging PAgP packets between LAN ports. PAgP packets are exchanged only between ports in auto and desirable modes.
The protocol learns the capabilities of LAN port groups dynamically and informs the other LAN ports. Once PAgP identifies correctly matched Ethernet links, it facilitates grouping the links into an EtherChannel. The EtherChannel is then added to the spanning tree as a single bridge port.
Both the auto and desirable modes allow PAgP to negotiate between LAN ports to determine if they can form an EtherChannel, based on criteria such as port speed and trunking state. Layer 2 EtherChannels also use VLAN numbers.
LAN ports can form an EtherChannel when they are in different PAgP modes if the modes are compatible. For example:
- A LAN port in desirable mode can form an EtherChannel successfully with another LAN port that is in desirable mode.
- A LAN port in desirable mode can form an EtherChannel with another LAN port in auto mode.
- A LAN port in auto mode cannot form an EtherChannel with another LAN port that is also in auto mode because neither port initiates negotiation.
IEEE 802.3ad LACP EtherChannel Configuration
Cisco IOS Release 12.2(25)EWA and later releases support IEEE 802.3ad LACP EtherChannels. LACP supports the automatic creation of EtherChannels by exchanging LACP packets between LAN ports. LACP packets are exchanged only between ports in passive and active modes.
The protocol learns the capabilities of LAN port groups dynamically and informs the other LAN ports. Once LACP identifies correctly matched Ethernet links, it facilitates grouping the links into an EtherChannel. The EtherChannel is then added to the spanning tree as a single bridge port.
Both the passive and active modes allow LACP to negotiate between LAN ports to determine if they can form an EtherChannel, based on criteria such as port speed and trunking state. Layer 2 EtherChannels also use VLAN numbers.
LAN ports can form an EtherChannel when they are in different LACP modes as long as the modes are compatible. For example:
- A LAN port in active mode can form an EtherChannel successfully with another LAN port that is in active mode.
- A LAN port in active mode can form an EtherChannel with another LAN port in passive mode.
- A LAN port in passive mode cannot form an EtherChannel with another LAN port that is also in passive mode, because neither port initiates negotiation.
LACP uses the following parameters:
- LACP system priority—You may configure an LACP system priority on each switch running LACP. The system priority can be configured automatically or through the CLI. See the “Configuring the LACP System Priority and System ID” section. LACP uses the system priority with the switch MAC address to form the system ID and also during negotiation with other systems.

Note![]() The LACP system ID is the combination of the LACP system priority value and the MAC address of the switch.
The LACP system ID is the combination of the LACP system priority value and the MAC address of the switch.
- LACP port priority—You must configure an LACP port priority on each port configured to use LACP. The port priority can be configured automatically or through the CLI. See the “Configuring Layer 2 EtherChannels” section. LACP uses the port priority with the port number to form the port identifier.
- LACP administrative key—LACP automatically configures an administrative key value equal to the channel group identification number on each port configured to use LACP. The administrative key defines the ability of a port to aggregate with other ports. A port’s ability to aggregate with other ports is determined by these factors:
–![]() Port physical characteristics, such as data rate, duplex capability, and point-to-point or shared medium
Port physical characteristics, such as data rate, duplex capability, and point-to-point or shared medium
–![]() Configuration restrictions that you establish
Configuration restrictions that you establish
LACP tries to configure the maximum number of compatible ports in an EtherChannel up to the maximum allowed by the hardware (eight ports). If a port cannot be actively included in a channel, it is not included automatically if a channelled port fails.

Note![]() Standby and “sub-channeling” are not supported in LACP and PAgP.
Standby and “sub-channeling” are not supported in LACP and PAgP.
Load Balancing
EtherChannel can balance the traffic load across the links in the channel by reducing part of the binary pattern formed from the addresses or ports in the frame to a numerical value that selects one of the links in the channel. To balance the load, EtherChannel uses MAC addresses, IP addresses, or Layer 4 port numbers, and either the message source or message destination, or both.
Use the option that provides the greatest variety in your configuration. For example, if the traffic on a channel is going only to a single MAC address, using the destination MAC address always chooses the same link in the channel; using source addresses or IP addresses might result in better load balancing.

Note![]() Load balancing can only be configured globally. As a result, all channels (manually configured, PagP, or LACP) use the same load-balancing method.
Load balancing can only be configured globally. As a result, all channels (manually configured, PagP, or LACP) use the same load-balancing method.
For additional information on load balancing, see the “Configuring EtherChannel Load Balancing” section.
EtherChannel Configuration Guidelines and Restrictions
If improperly configured, some EtherChannel interfaces are disabled automatically to avoid network loops and other problems. Follow these guidelines and restrictions to avoid configuration problems:
- All Ethernet interfaces on all modules support EtherChannel (maximum of eight interfaces) with no requirement that interfaces be physically contiguous or on the same module.
- Configure all interfaces in an EtherChannel to operate at the same speed and duplex mode.
- Enable all interfaces in an EtherChannel. Disabling an interface in an EtherChannel is treated as a link failure, and its traffic is transferred to one of the remaining interfaces in the EtherChannel.
- An EtherChannel does not form if one of the interfaces is a Switched Port Analyzer (SPAN) destination port.
- For Layer 3 EtherChannels:
–![]() Assign Layer 3 addresses to the port channel logical interface, not to the physical interfaces in the channel.
Assign Layer 3 addresses to the port channel logical interface, not to the physical interfaces in the channel.
–![]() Assign all interfaces in the EtherChannel to the same VLAN, or configure them as trunks.
Assign all interfaces in the EtherChannel to the same VLAN, or configure them as trunks.
–![]() If you configure an EtherChannel from trunk interfaces, verify that the trunking mode and the native VLAN is the same on all the trunks. Interfaces in an EtherChannel with different trunk modes or different native VLANs can have unexpected results.
If you configure an EtherChannel from trunk interfaces, verify that the trunking mode and the native VLAN is the same on all the trunks. Interfaces in an EtherChannel with different trunk modes or different native VLANs can have unexpected results.
–![]() An EtherChannel supports the same allowed range of VLANs on all the interfaces in a trunking Layer 2 EtherChannel. If the allowed ranges differ for selected interface differ, they do not form an EtherChannel.
An EtherChannel supports the same allowed range of VLANs on all the interfaces in a trunking Layer 2 EtherChannel. If the allowed ranges differ for selected interface differ, they do not form an EtherChannel.
–![]() Interfaces with different Spanning Tree Protocol (STP) port path costs can form an EtherChannel as long they are otherwise compatibly configured. Setting different STP port path costs does not make interfaces incompatible for the formation of an EtherChannel.
Interfaces with different Spanning Tree Protocol (STP) port path costs can form an EtherChannel as long they are otherwise compatibly configured. Setting different STP port path costs does not make interfaces incompatible for the formation of an EtherChannel.
- After you configure an EtherChannel, any configuration that you apply to the port channel interface affects the EtherChannel; any configuration that you apply to the physical interfaces affects only the interface you configure.
Storm Control is an exception to this rule. For example, you cannot configure Storm Control on some of the members of an EtherChannel; Storm Control must be configured on all or none of the ports. If you configure Storm Control on only some of the ports, those ports are dropped from the EtherChannel interface (put in suspended state). You should configure Storm Control at the port channel interface level, and not at the physical interface level.
Configuring EtherChannel
These sections describe how to configure EtherChannel:
- Configuring Layer 3 EtherChannels
- Configuring Layer 2 EtherChannels
- Configuring the LACP System Priority and System ID
- Configuring EtherChannel Load Balancing
- Removing an Interface from an EtherChannel
- Removing an EtherChannel

Note![]() Ensure that the interfaces are configured correctly. See the “EtherChannel Configuration Guidelines and Restrictions” section.
Ensure that the interfaces are configured correctly. See the “EtherChannel Configuration Guidelines and Restrictions” section.
Configuring Layer 3 EtherChannels
To configure Layer 3 EtherChannels, create the port channel logical interface and then put the Ethernet interfaces into the port channel.
Creating Port Channel Logical Interfaces

Note![]() To move an IP address from a physical interface to an EtherChannel, you must delete the IP address from the physical interface before configuring it on the port channel interface.
To move an IP address from a physical interface to an EtherChannel, you must delete the IP address from the physical interface before configuring it on the port channel interface.
To create a port channel interface for a Layer 3 EtherChannel, perform this task:
This example shows how to create port channel interface 1:
This example shows how to verify the configuration of port channel interface 1:
Configuring Physical Interfaces as Layer 3 EtherChannels
To configure physical interfaces as Layer 3 EtherChannels, perform this task for each interface:
This example shows how to configure Fast Ethernet interfaces 5/4 and 5/5 into port channel 1 with PAgP mode desirable :

Note![]() See the “Configuring a Range of Interfaces” section for information about the range keyword.
See the “Configuring a Range of Interfaces” section for information about the range keyword.
The following two examples show how to verify the configuration of Fast Ethernet interface 5/4:
This example shows how to verify the configuration of port channel interface 1 after the interfaces have been configured:
Configuring Layer 2 EtherChannels
To configure Layer 2 EtherChannels, configure the Ethernet interfaces with the channel-group command. This operation creates the port channel logical interface.

Note![]() Cisco IOS software creates port channel interfaces for Layer 2 EtherChannels when you configure Layer 2 Ethernet interfaces with the channel-group command.
Cisco IOS software creates port channel interfaces for Layer 2 EtherChannels when you configure Layer 2 Ethernet interfaces with the channel-group command.
To configure Layer 2 Ethernet interfaces as Layer 2 EtherChannels, perform this task for each interface:
This example shows how to configure Fast Ethernet interfaces 5/6 and 5/7 into port channel 2 with PAgP mode desirable :

Note![]() See the “Configuring a Range of Interfaces” section for information about the range keyword.
See the “Configuring a Range of Interfaces” section for information about the range keyword.
This example shows how to verify the configuration of port channel interface 2:
The following two examples show how to verify the configuration of Fast Ethernet interface 5/6:
This example shows how to verify the configuration of port channel interface 2 after the interfaces have been configured:
Configuring the LACP System Priority and System ID
The LACP system ID is the LACP system priority value combined with the MAC address of the switch.
To configure the LACP system priority and system ID, perform this task:
This example shows how to configure the LACP system priority:
This example shows how to verify the configuration:
The system priority is displayed first, followed by the MAC address of the switch.
Configuring EtherChannel Load Balancing

Note![]() Load balancing can only be configured globally. As a result, all channels (manually configured, PagP, or LACP) use the same load-balancing method.
Load balancing can only be configured globally. As a result, all channels (manually configured, PagP, or LACP) use the same load-balancing method.
To configure EtherChannel load balancing, perform this task:
The load-balancing keywords indicate these values:
- src-mac —Source MAC addresses
- dst-mac —Destination MAC addresses
- src-dst-mac —Source and destination MAC addresses
- src-ip —Source IP addresses
- dst-ip —Destination IP addresses
- src-dst-ip —Source and destination IP addresses (Default)
- src-port —Source Layer 4 port
- dst-port —Destination Layer 4 port
- src-dst-port —Source and destination Layer 4 port
This example shows how to configure EtherChannel to use source and destination IP addresses:
This example shows how to verify the configuration:
Removing an Interface from an EtherChannel
To remove an Ethernet interface from an EtherChannel, perform this task:
This example shows how to remove Fast Ethernet interfaces 5/4 and 5/5 from port channel 1:
Removing an EtherChannel
If you remove an EtherChannel, the member ports are shut down and removed from the channel group.

Note![]() If you want to change an EtherChannel from Layer 2 to Layer 3, or Layer 3 to Layer 2, you must remove the EtherChannel and recreate it in the desired configuration.
If you want to change an EtherChannel from Layer 2 to Layer 3, or Layer 3 to Layer 2, you must remove the EtherChannel and recreate it in the desired configuration.
To remove an EtherChannel, perform this task:
|
|
|
|
|---|---|---|
|
|
||
|
|
||
|
|
This example shows how to remove port channel 1:
Displaying EtherChannel to a Virtual Switch System
Catalyst 4500 series switches support enhanced PAgP. If a Catalyst 4500 series switch is connected to a Catalyst 6500 series Virtual Switch System (VSS) by using a PAgP EtherChannel, the Catalyst 4500 series switch automatically serve as a VSS client, using enhanced PAgP on this EtherChannel for dual-active detection. This VSS client feature has no impact on the performance of Catalyst 4500 series switch and does not require any user configuration.
This section includes these topics:
Understanding VSS Client
Virtual Switch System
The Cisco Catalyst 6500 Series VSS 1440 allows for the combination of two Cisco Catalyst 6500 Series switches into a single, logical network entity from the network control-plane and management perspectives. Within the Cisco VSS, one chassis is designated as the active virtual switch, acting as the single management point of the entire system, and the other is designated as the standby virtual switch. There two chassis are bound together by a special link, called Virtual Switch Link (VSL), which carries the internal signaling and control information between them.
Dual-Active Scenarios
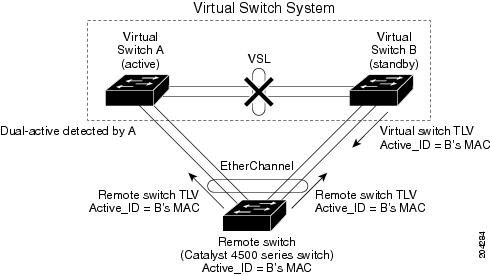
One of the failure scenarios in a VSS is called dual-active, which occurs when the VSL fails completely. Neither virtual switch knows of the other's status. From the perspective of the active virtual switch, the standby chassis is lost. The standby virtual switch also views the active chassis as failed and transitions to active state by using an SSO switchover. Two active virtual switches exist in the network with identical configurations, causing duplicate IP addresses and bridge identifiers. This scenario has adverse effects on the network topology and traffic if it persists.
Dual-Active Detection Using Enhanced PAgP
One method for detecting a dual-active scenario is based on enhanced PAgP (PAgP+). Specifically, the VSS sends regularly scheduled PAgP messages with Type-Length-Values (TLVs) containing the ID of the current active virtual switch ( Figure 22-1). When the VSL fails completely, the standby virtual switch immediately sends asynchronous PAgP messages with TLVs containing its own ID on all port channels enabled for enhanced PAgP dual-active detection (Figure 22-2). The remote switch
(the VSS client) connected to both VSS components by using EtherChannel links, compares every received active ID with its stored active ID. If they match, the remote switch sends TLVs containing its stored active ID back to the VSS in its regularly scheduled PAgP messages. If they do not match, the remote switch stores the new active ID and immediately transmits asynchronous PAgP messages with TLVs containing the new active ID. Upon receiving the new active ID from the remote switch, the original active virtual switch detects the dual-active scenario and takes appropriate actions.
Figure 22-1 Enhanced PAgP in VSS Normal Operation
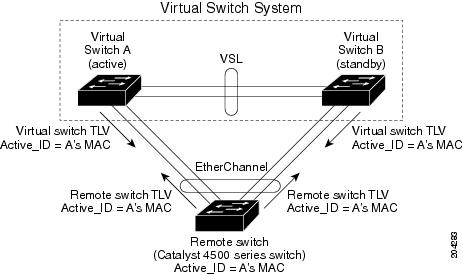
Figure 22-2 Enhanced PAgP in VSS Dual-active Scenario
As a remote switch, the Catalyst 4500 series switch supports stateful VSS client. In particular, the ID of the current active virtual switch is synchronized from the active supervisor engine to the redundant supervisor engine of the Catalyst 4500 series switch. This ensures that dual-active detection is not disrupted even when the active supervisor engine switches over to the redundant supervisor engine.
Displaying EtherChannel Links to VSS
To display the dual-active detection capability of a configured PAgP port channel, enter the
show pagp port_channel_number dual-active command.
The command provides the following information:
You should always see Yes after PAgP dual-active diction enabled on a Catalyst 4500 switch.
You see N/A below Partner Version if this EtherChannel is not connected to a VSS. Otherwise, you see the version of enhanced PAgP dual-active detection implemented in the VSS.
You see Yes below Dual-Active Detect Capable if and only if the configured EtherChannel is connected to a Catalyst 6500 series VSS that uses the same version of enhanced PAgP dual-active detection.

Note![]() You can also see the name of the neighboring switch (Partner Name) and the ports to which this EtherChannel is connected (Partner Port).
You can also see the name of the neighboring switch (Partner Name) and the ports to which this EtherChannel is connected (Partner Port).
If a Catalyst 4500 switch is connected to a Catalyst 6500 series VSS with the same version of enhanced PAgP dual-active detection, the switch can detect a dual-active scenario:
If a Catalyst 4500 switch is not connected to a Catalyst 6500 series VSS, the switch cannot detect a dual-active scenario:
Understanding Link-State Tracking
Link-state tracking, also known as trunk failover, is a feature that binds the link state of multiple interfaces. For example, link-state tracking provides redundancy in the network when used with server NIC adapter teaming. When server network adapters are configured in a primary or secondary relationship known as teaming, if the link is lost on the primary interface, connectivity is transparently changed to the secondary interface.
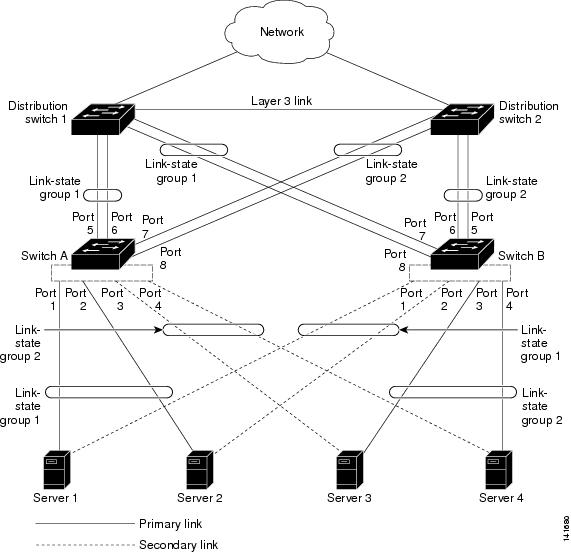
Figure 22-3 shows a network configured with link-state tracking. To enable link-state tracking, create a link-state group, and specify the interfaces that are assigned to the link-state group. An interface can be an aggregation of ports (an EtherChannel), a single physical port in access or trunk mode, or a routed port. In a link-state group, these interfaces are bundled together. The downstream interfaces are bound to the upstream interfaces. Interfaces connected to servers are referred to as downstream interfaces, and interfaces connected to distribution switches and network devices are referred to as upstream interfaces.
The configuration in Figure 22-3 ensures that the network traffic flow is balanced as follows:
–![]() Server 1 and server 2 use switch A for primary links and switch B for secondary links.
Server 1 and server 2 use switch A for primary links and switch B for secondary links.
–![]() Server 3 and server 4 use switch B for primary links and switch A for secondary links.
Server 3 and server 4 use switch B for primary links and switch A for secondary links.
–![]() Switch A provides primary links to server 1 and server 2 through link-state group 1. Port 1 is connected to server 1, and port 2 is connected to server 2. Port 1 and port 2 are the downstream interfaces in link-state group 1.
Switch A provides primary links to server 1 and server 2 through link-state group 1. Port 1 is connected to server 1, and port 2 is connected to server 2. Port 1 and port 2 are the downstream interfaces in link-state group 1.
–![]() Port 5 and port 6 are connected to distribution switch 1 through link-state group 1. Port 5 and port 6 are the upstream interfaces in link-state group 1.
Port 5 and port 6 are connected to distribution switch 1 through link-state group 1. Port 5 and port 6 are the upstream interfaces in link-state group 1.
–![]() Switch A provides secondary links to server 3 and server 4 through link-state group 2. Port 3 is connected to server 3, and port 4 is connected to server 4. Port 3 and port 4 are the downstream interfaces in link-state group 2.
Switch A provides secondary links to server 3 and server 4 through link-state group 2. Port 3 is connected to server 3, and port 4 is connected to server 4. Port 3 and port 4 are the downstream interfaces in link-state group 2.
–![]() Port 7 and port 8 are connected to distribution switch 2 through link-state group 2. Port 7 and port 8 are the upstream interfaces in link-state group 2.
Port 7 and port 8 are connected to distribution switch 2 through link-state group 2. Port 7 and port 8 are the upstream interfaces in link-state group 2.
–![]() Switch B provides primary links to server 3 and server 4 through link-state group 2. Port 3 is connected to server 3, and port 4 is connected to server 4. Port 3 and port 4 are the downstream interfaces in link-state group 2.
Switch B provides primary links to server 3 and server 4 through link-state group 2. Port 3 is connected to server 3, and port 4 is connected to server 4. Port 3 and port 4 are the downstream interfaces in link-state group 2.
–![]() Port 5 and port 6 are connected to distribution switch 2 through link-state group 2. Port 5 and port 6 are the upstream interfaces in link-state group 2.
Port 5 and port 6 are connected to distribution switch 2 through link-state group 2. Port 5 and port 6 are the upstream interfaces in link-state group 2.
–![]() Switch B provides secondary links to server 1 and server 2 through link-state group 1. Port 1 is connected to server 1, and port 2 is connected to server 2. Port 1 and port 2 are the downstream interfaces in link-state group 1.
Switch B provides secondary links to server 1 and server 2 through link-state group 1. Port 1 is connected to server 1, and port 2 is connected to server 2. Port 1 and port 2 are the downstream interfaces in link-state group 1.
–![]() Port 7 and port 8 are connected to distribution switch 1 through link-state group 1. Port 7 and port 8 are the upstream interfaces in link-state group 1.
Port 7 and port 8 are connected to distribution switch 1 through link-state group 1. Port 7 and port 8 are the upstream interfaces in link-state group 1.
In a link-state group, the upstream ports can become unavailable or lose connectivity because the distribution switch or router fails, the cables are disconnected, or the link is lost. These are the interactions between the downstream and upstream interfaces when link-state tracking is enabled:
- If any of the upstream interfaces are in the link-up state, the downstream interfaces can change to or remain in the link-up state.
- If all of the upstream interfaces become unavailable, link-state tracking automatically puts the downstream interfaces in the error-disabled state. Connectivity to and from the servers is automatically changed from the primary server interface to the secondary server interface.
As an example of a connectivity change from link-state group 1 to link-state group 2 on switch A, see Figure 22-3. If the upstream link for port 6 is lost, the link states of downstream ports 1 and 2 do not change. However, if the link for upstream port 5 is also lost, the link state of the downstream ports changes to the link-down state. Connectivity to server 1 and server 2 is then changed from link-state group1 to link-state group 2. The downstream ports 3 and 4 do not change state because they are in link-group 2.
- If the link-state group is configured, link-state tracking is disabled, and the upstream interfaces lose connectivity, the link states of the downstream interfaces remain unchanged. The server does not recognize that upstream connectivity has been lost and does not failover to the secondary interface.
You can recover a downstream interface link-down condition by removing the failed downstream port from the link-state group. To recover multiple downstream interfaces, disable the link-state group.
Figure 22-3 Typical Link-State Tracking Configuration
Configuring Link-State Tracking
These sections describe how to configure link-state tracking ports:
- Default Link-State Tracking Configuration
- Link-State Tracking Configuration Guidelines
- Configuring Link-State Tracking
- Displaying Link-State Tracking Status
Default Link-State Tracking Configuration
No link-state groups are defined, and link-state tracking is not enabled for any group.
Link-State Tracking Configuration Guidelines
Follow these guidelines to avoid configuration problems:
- An interface that is defined as an upstream interface cannot also be defined as a downstream interface in the same or different link-state group. The reverse is also true.
- We recommend that you add the upstream interfaces to the link state group before adding the downstream interfaces. it is because when a downstream interface is added to a link state group without an upstream interface, the downstream interface is put in error-disabled state until an upstream interfaces is added to the group.
- An interface cannot be a member of more than one link-state group.
- You can configure up to ten link-state groups per switch.
- If a SPAN destination port is configured as a downstream interface, it is error disabled when all upstream interfaces in its group are down. When an upstream interface is configured as a SPAN destination port, it is considered as a link down event on the interface.
Configuring Link-State Tracking
To configure a link-state group and to assign an interface to a group, perform this task beginning in privileged EXEC mode:
This example shows how to create a link-state group and configure the interfaces:
To disable a link-state group, use the no link state track number global configuration command.
Displaying Link-State Tracking Status
To display the link-state group information, enter the show link state group command. Enter this command without keywords to display information about all link-state groups.
Enter the group number to display information specific to the group. Enter the detail keyword to display detailed information about the group.
it is an example of output from the show link state group 1 command:
it is an example of output from the show link state group detail command:
 Feedback
Feedback