Use OpenAPI to Retrieve ISE Certificate Information on ISE 3.3
Available Languages
Download Options
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
Contents
Introduction
This document describes the procedure for utilizing openAPI to manage Cisco Identity Services Engine (ISE) certificate.
Background
In the face of growing complexity in enterprise network security and management, Cisco ISE 3.1 introduces OpenAPI-formatted APIs that streamline certificate lifecycle management, offering a standardized and automated interface for efficient and secure certificate operations, helping administrators enforce strong security practices and maintain network compliance.
Prerequisites
Requirements
Cisco recommends that you have knowledge of these topics:
- Cisco Identity Services Engine (ISE)
- REST API
- Python
Components Used
- ISE 3.3
- Python 3.10.0
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command.
Configure
Network Diagram
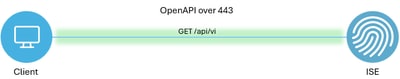 Topology
Topology
Configuration on ISE
Step 1: Add an Open API admin account
To add an API admin, navigate toAdministration > System > Admin Access > Administrators > Admin Users > Add.
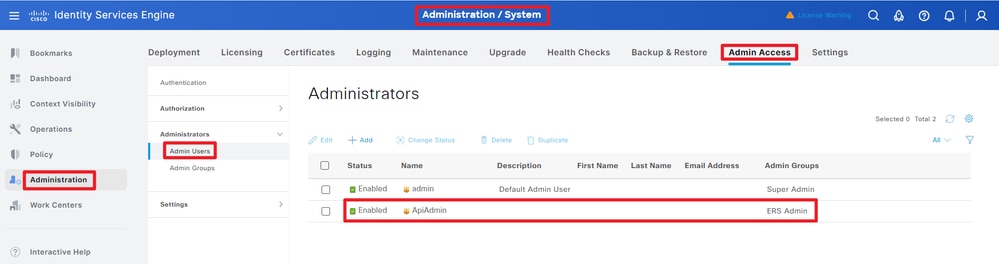 API Admin
API Admin
Step 2: Enable Open API on ISE
Open API is disabled by default on ISE. To enable it, navigate to Administration > System > Settings > API Settings > API Service Settings. Toggle the Open API options. Click Save.
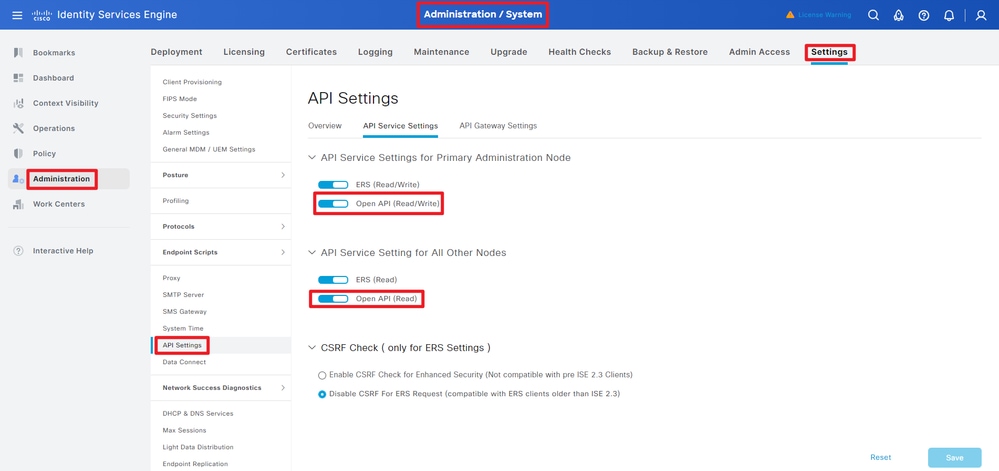 Enable OpenAPI
Enable OpenAPI
Step 3: Explore ISE open API
navigate to Administration > System > Settings > API Settings > Overview. Click open API visit link.
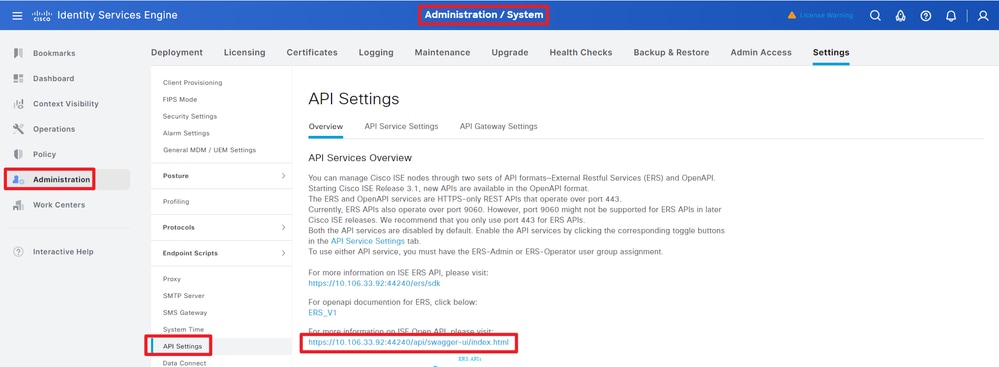 Visit OpenAPI
Visit OpenAPI
Python Examples
Get All System Certificates Of A Particular Node
The API lists all the certificates of a particular ISE node.
Step 1: Required information for an API call.
| Method | GET |
| URL |
https://<ISE-PAN-IP>/api/v1/certs/system-certificate/<ISE-Node-Hostname>
|
| Credentials | Use Open API account credentials |
| Headers |
Accept: application/json
Content-Type: application/json
|
Step 2: Locate the URL that is utilized to retrieve certificates of a particular ISE node.
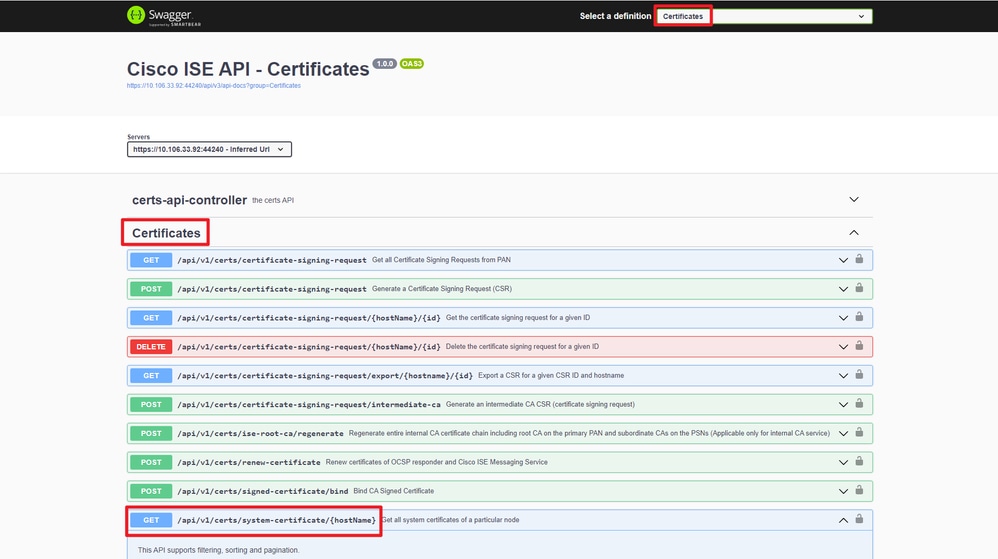 API URI
API URI
Step 3: Here is the example of Python Code. Copy and paste the content. Replace the ISE IP, username, password. Save as a python file to execute.
Ensure the good connectivity between ISE and the device running the python code example.
from requests.auth import HTTPBasicAuth
import requests
requests.packages.urllib3.disable_warnings()
if __name__ == "__main__":
url = "https://10.106.33.92/api/v1/certs/system-certificate/ISE-DLC-CFME02-PSN"
headers = {"Accept": "application/json", "Content-Type": "application/json"}
basicAuth = HTTPBasicAuth("ApiAdmin", "Admin123")
response = requests.get(url=url, auth=basicAuth, headers=headers, verify=False)
print("Return Code:")
print(response.status_code)
print("Expected Outputs:")
print(response.json())Here is the example of expected outputs.
Return Code:
200
Expected Outputs:
{'response': [{'id': '5b5b28e4-2a51-495c-8413-610190e1070b', 'friendlyName': 'Default self-signed saml server certificate - CN=SAML_ISE-DLC-CFME02-PSN.cisco.com', 'serialNumberDecimalFormat': '171164606212827159112166844026', 'issuedTo': 'SAML_ISE-DLC-CFME02-PSN.cisco.com', 'issuedBy': 'SAML_ISE-DLC-CFME02-PSN.cisco.com', 'validFrom': 'Fri Mar 29 01:14:22 CST 2024', 'expirationDate': 'Wed Mar 28 01:14:22 CST 2029', 'usedBy': 'Not in use', 'keySize': 4096, 'groupTag': '', 'selfSigned': True, 'signatureAlgorithm': 'SHA384withRSA', 'portalsUsingTheTag': '', 'sha256Fingerprint': '42ad8eeec643fce00605ac34aaf88ca5d687117591a2a4431b656dad8ce9616b', 'link': {'rel': 'self', 'href': 'https://10.106.33.92/api/v1/certs/system-certificate/ISE-DLC-CFME02-PSN/5b5b28e4-2a51-495c-8413-610190e1070b', 'type': 'application/json'}}, {'id': '8460950e-fd02-43f6-b1ea-abfa592cb641', 'friendlyName': 'CN=ISE-DLC-CFME02-PSN.cisco.com, OU=Certificate Services System Certificate#Certificate Services Endpoint Sub CA - ISE-DLC-CFME02-PSN#00003', 'serialNumberDecimalFormat': '27546245129667566853665077095037707664', 'issuedTo': 'ISE-DLC-CFME02-PSN.cisco.com', 'issuedBy': 'Certificate Services Endpoint Sub CA - ISE-DLC-CFME02-PSN', 'validFrom': 'Thu Mar 28 16:24:11 CST 2024', 'expirationDate': 'Thu Mar 29 16:24:11 CST 2029', 'usedBy': 'pxGrid', 'keySize': 4096, 'groupTag': '', 'selfSigned': False, 'signatureAlgorithm': 'SHA256withRSA', 'portalsUsingTheTag': '', 'sha256Fingerprint': 'a3c67ea007db0fd5672b471ea614a33c57f1ec55182b436cd0b386ebd88a141c', 'link': {'rel': 'self', 'href': 'https://10.106.33.92/api/v1/certs/system-certificate/ISE-DLC-CFME02-PSN/8460950e-fd02-43f6-b1ea-abfa592cb641', 'type': 'application/json'}}, {'id': 'ee5a1a18-4bba-49b5-960b-eabb4418ab5a', 'friendlyName': 'CN=ISE-DLC-CFME02-PSN.cisco.com, OU=ISE Messaging Service#Certificate Services Endpoint Sub CA - ISE-DLC-CFME02-PSN#00004', 'serialNumberDecimalFormat': '108100957755910846563764359601813445413', 'issuedTo': 'ISE-DLC-CFME02-PSN.cisco.com', 'issuedBy': 'Certificate Services Endpoint Sub CA - ISE-DLC-CFME02-PSN', 'validFrom': 'Thu Mar 28 16:24:12 CST 2024', 'expirationDate': 'Thu Mar 29 16:24:12 CST 2029', 'usedBy': 'ISE Messaging Service', 'keySize': 4096, 'groupTag': '', 'selfSigned': False, 'signatureAlgorithm': 'SHA256withRSA', 'portalsUsingTheTag': '', 'sha256Fingerprint': '3cf23d21cdae3bb412a24d3949a4e1e36666b7188fba24f15161be205c2de84a', 'link': {'rel': 'self', 'href': 'https://10.106.33.92/api/v1/certs/system-certificate/ISE-DLC-CFME02-PSN/ee5a1a18-4bba-49b5-960b-eabb4418ab5a', 'type': 'application/json'}}, {'id': '06024b57-e21d-44f7-ade9-f27835f825cd', 'friendlyName': 'CN=ISE-DLC-CFME02-PSN.cisco.com, OU=ISE Messaging Service#Certificate Services Endpoint Sub CA - ISE-DLC-CFME02-PSN#00001', 'serialNumberDecimalFormat': '161050984501207870146216443017020239440', 'issuedTo': 'ISE-DLC-CFME02-PSN.cisco.com', 'issuedBy': 'Certificate Services Endpoint Sub CA - ISE-DLC-CFME02-PSN', 'validFrom': 'Thu Mar 28 01:32:39 CST 2024', 'expirationDate': 'Thu Mar 29 01:32:39 CST 2029', 'usedBy': 'Not in use', 'keySize': 4096, 'groupTag': '', 'selfSigned': False, 'signatureAlgorithm': 'SHA256withRSA', 'portalsUsingTheTag': '', 'sha256Fingerprint': '53ebe08309e787d503a484538efe7631c89c6faa34371807cd98fd22a0ea3f4a', 'link': {'rel': 'self', 'href': 'https://10.106.33.92/api/v1/certs/system-certificate/ISE-DLC-CFME02-PSN/06024b57-e21d-44f7-ade9-f27835f825cd', 'type': 'application/json'}}, {'id': 'ba0833e1-d1b6-4080-bcf8-ef088cdcd2c8', 'friendlyName': 'CN=ISE-DLC-CFME02-PSN.cisco.com, OU=Certificate Services System Certificate#Certificate Services Endpoint Sub CA - ISE-DLC-CFME02-PSN#00002', 'serialNumberDecimalFormat': '47010535375030235417054492045580827528', 'issuedTo': 'ISE-DLC-CFME02-PSN.cisco.com', 'issuedBy': 'Certificate Services Endpoint Sub CA - ISE-DLC-CFME02-PSN', 'validFrom': 'Thu Mar 28 01:32:29 CST 2024', 'expirationDate': 'Thu Mar 29 01:32:29 CST 2029', 'usedBy': 'Not in use', 'keySize': 4096, 'groupTag': '', 'selfSigned': False, 'signatureAlgorithm': 'SHA256withRSA', 'portalsUsingTheTag': '', 'sha256Fingerprint': '656866d5143561929466b68d0bd207b67b3ae62cc69746fcef20a25000737d1c', 'link': {'rel': 'self', 'href': 'https://10.106.33.92/api/v1/certs/system-certificate/ISE-DLC-CFME02-PSN/ba0833e1-d1b6-4080-bcf8-ef088cdcd2c8', 'type': 'application/json'}}, {'id': '6c9c6d94-e693-4864-82cb-85ea37fd9527', 'friendlyName': 'Default self-signed saml server certificate - CN=SAML_ISE-BGL-CFME01-PAN.cisco.com', 'serialNumberDecimalFormat': '17112682887682578269840298717', 'issuedTo': 'SAML_ISE-BGL-CFME01-PAN.cisco.com', 'issuedBy': 'SAML_ISE-BGL-CFME01-PAN.cisco.com', 'validFrom': 'Sun Mar 24 16:18:08 CST 2024', 'expirationDate': 'Fri Mar 23 16:18:08 CST 2029', 'usedBy': 'SAML', 'keySize': 4096, 'groupTag': '', 'selfSigned': True, 'signatureAlgorithm': 'SHA384withRSA', 'portalsUsingTheTag': '', 'sha256Fingerprint': '010365518c6282e7fe54aa0b593433a2ae912000a3c76e0b2763b866bc7304e9', 'link': {'rel': 'self', 'href': 'https://10.106.33.92/api/v1/certs/system-certificate/ISE-DLC-CFME02-PSN/6c9c6d94-e693-4864-82cb-85ea37fd9527', 'type': 'application/json'}}, {'id': '9a7751ba-d630-43f2-b43d-bcf431dffa97', 'friendlyName': 'Default self-signed server certificate', 'serialNumberDecimalFormat': '17116455823360843797526070457', 'issuedTo': 'ISE-DLC-CFME02-PSN.cisco.com', 'issuedBy': 'ISE-DLC-CFME02-PSN.cisco.com', 'validFrom': 'Fri Mar 29 01:06:22 CST 2024', 'expirationDate': 'Sun Mar 29 01:06:22 CST 2026', 'usedBy': 'EAP Authentication, Admin, Portal, RADIUS DTLS', 'keySize': 4096, 'groupTag': 'Default Portal Certificate Group', 'selfSigned': True, 'signatureAlgorithm': 'SHA384withRSA', 'portalsUsingTheTag': 'BYOD Portal (default), Blocked List Portal (default), Certificate Provisioning Portal (default), Client Provisioning Portal (default), Hotspot Guest Portal (default), ISE Portal (default), MDM Portal (default), My Devices Portal (default), Self-Registered Guest Portal (default), Sponsor Portal (default), Sponsored Guest Portal (default)', 'sha256Fingerprint': 'f498da0b64fac68318f1f8f195e915c1000265d8950f610ec3bb9c75822739bd', 'link': {'rel': 'self', 'href': 'https://10.106.33.92/api/v1/certs/system-certificate/ISE-DLC-CFME02-PSN/9a7751ba-d630-43f2-b43d-bcf431dffa97', 'type': 'application/json'}}], 'nextPage': None, 'previousPage': None, 'version': '1.0.1'}Get System Certificate Of A Particular Node By ID
This API provides details of a system certificate of a particular node based on given hostname and ID.
Step 1: Required information for an API call.
| Method | GET |
| URL |
https://<ISE-PAN-IP>/api/v1/certs/system-certificate/<ISE-Node-Hostname>/<ID-Of-Certificate>
|
| Credentials | Use Open API account credentials |
| Headers |
Accept: application/json
Content-Type: application/json
|
Step 2: Locate the URL that is utilized to retrieve the certificate of a particular node based on given hostname and ID.
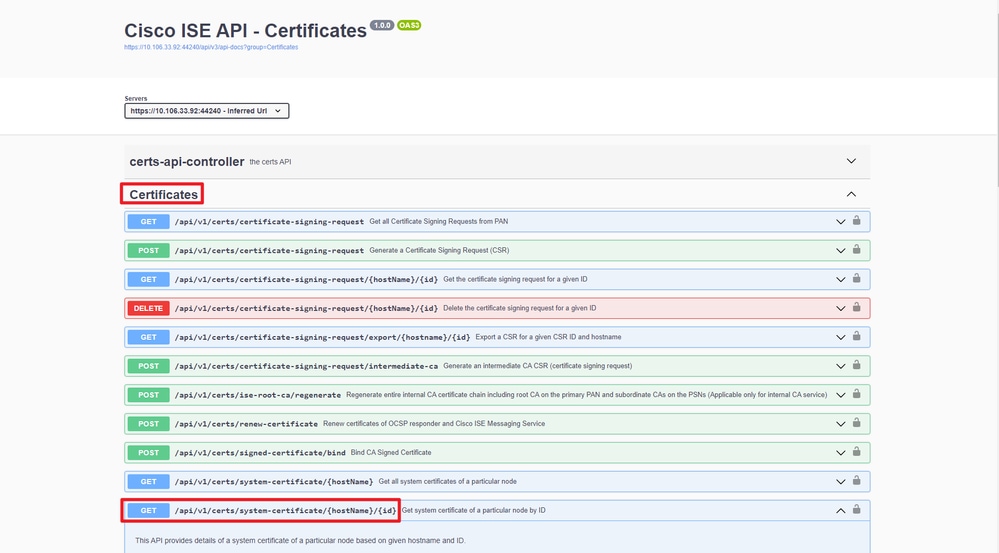 API URI
API URI
Step 3: Here is the example of Python Code. Copy and paste the content. Replace the ISE IP, username, password. Save as a python file to execute.
Ensure the good connectivity between ISE and the device running the python code example.
from requests.auth import HTTPBasicAuth
import requests
requests.packages.urllib3.disable_warnings()
if __name__ == "__main__":
url = "https://10.106.33.92/api/v1/certs/system-certificate/ISE-DLC-CFME02-PSN/5b5b28e4-2a51-495c-8413-610190e1070b"
headers = {"Accept": "application/json", "Content-Type": "application/json"}
basicAuth = HTTPBasicAuth("ApiAdmin", "Admin123")
response = requests.get(url=url, auth=basicAuth, headers=headers, verify=False)
print("Return Code:")
print(response.status_code)
print("Expected Outputs:")
print(response.json())
Note: The ID is from API outputs in step 3 of "Get All System Certificates Of A Particular Node", for example, 5b5b28e4-2a51-495c-8413-610190e1070b is "Default self-signed saml server certificate - CN=SAML_ISE-DLC-CFME02-PSN.cisco.com".
Here is the example of expected outputs.
Return Code:
200
Expected Outputs:
{'response': {'id': '5b5b28e4-2a51-495c-8413-610190e1070b', 'friendlyName': 'Default self-signed saml server certificate - CN=SAML_ISE-DLC-CFME02-PSN.cisco.com', 'serialNumberDecimalFormat': '171164606212827159112166844026', 'issuedTo': 'SAML_ISE-DLC-CFME02-PSN.cisco.com', 'issuedBy': 'SAML_ISE-DLC-CFME02-PSN.cisco.com', 'validFrom': 'Fri Mar 29 01:14:22 CST 2024', 'expirationDate': 'Wed Mar 28 01:14:22 CST 2029', 'usedBy': 'Not in use', 'keySize': 4096, 'groupTag': '', 'selfSigned': True, 'signatureAlgorithm': 'SHA384withRSA', 'portalsUsingTheTag': '', 'sha256Fingerprint': '42ad8eeec643fce00605ac34aaf88ca5d687117591a2a4431b656dad8ce9616b', 'link': {'rel': 'self', 'href': 'https://10.106.33.92/api/v1/certs/system-certificate/ISE-DLC-CFME02-PSN/5b5b28e4-2a51-495c-8413-610190e1070b', 'type': 'application/json'}}, 'version': '1.0.1'}Get List Of All Trusted Certificates
The API lists all the trusted certificates of ISE cluster.
Step 1: Required information for an API call.
| Method | GET |
| URL |
https://<ISE-PAN-IP>/api/v1/certs/trusted-certificate
|
| Credentials | Use Open API account credentials |
| Headers |
Accept: application/json
Content-Type: application/json
|
Step 2: Locate the URL that is utilized to retrieve trusted certificates.
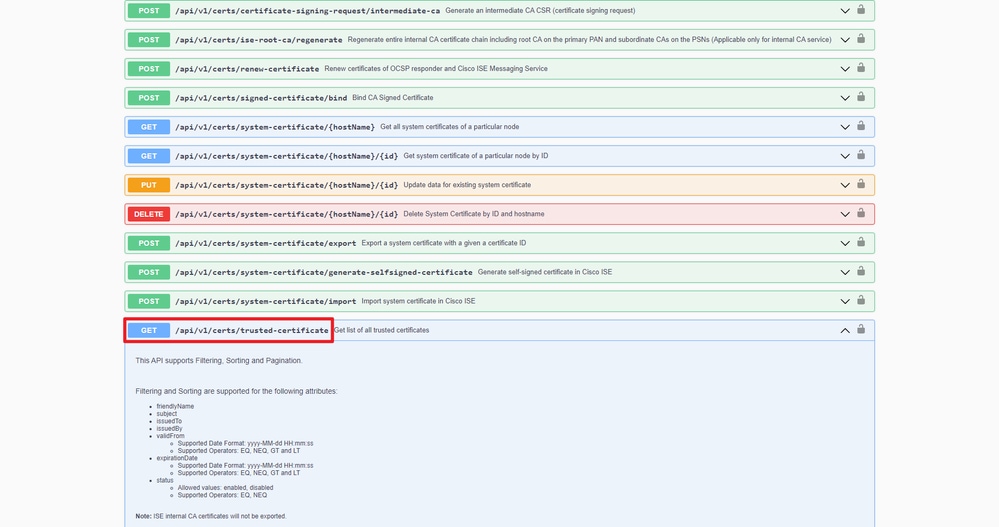 API URI
API URI
Step 3: Here is the example of Python Code. Copy and paste the content. Replace the ISE IP, username, password. Save as a python file to execute.
Ensure the good connectivity between ISE and the device running the python code example.
from requests.auth import HTTPBasicAuth
import requests
requests.packages.urllib3.disable_warnings()
if __name__ == "__main__":
url = "https://10.106.33.92/api/v1/certs/trusted-certificate"
headers = {"Accept": "application/json", "Content-Type": "application/json"}
basicAuth = HTTPBasicAuth("ApiAdmin", "Admin123")
response = requests.get(url=url, auth=basicAuth, headers=headers, verify=False)
print("Return Code:")
print(response.status_code)
print("Expected Outputs:")
print(response.json())Here is the example of expected outputs.(Omitted)
Return Code:
200
Expected Outputs:
{'response': [{'id': '147d97cc-6ce9-43d7-9928-8cd0fa83e140', 'friendlyName': 'VeriSign Class 3 Public Primary Certification Authority', 'subject': 'CN=VeriSign Class 3 Public Primary Certification Authority - G5,OU=(c) 2006 VeriSign\\, Inc. - For authorized use only,OU=VeriSign Trust Network,O=VeriSign\\, Inc.,C=US', 'issuedTo': 'VeriSign Class 3 Public Primary Certification Authority - G5', 'issuedBy': 'VeriSign Class 3 Public Primary Certification Authority - G5', 'keySize': '2048', 'signatureAlgorithm': 'SHA1withRSA', 'validFrom': 'Wed Nov 08 08:00:00 CST 2006', 'expirationDate': 'Thu Jul 17 07:59:59 CST 2036', 'serialNumberDecimalFormat': '33037644167568058970164719475676101450', 'description': 'Auto imported for secure connection to cisco.com/perfigo.com', 'status': 'Enabled', 'trustedFor': 'Cisco Services', 'internalCA': False, 'downloadCRL': 'off', 'crlDistributionUrl': None, 'automaticCRLUpdate': 'on', 'automaticCRLUpdatePeriod': '5', 'automaticCRLUpdateUnits': 'Minutes', 'nonAutomaticCRLUpdatePeriod': '1', 'nonAutomaticCRLUpdateUnits': 'Hours', 'crlDownloadFailureRetries': '10', 'crlDownloadFailureRetriesUnits': 'Minutes', 'authenticateBeforeCRLReceived': 'off', 'ignoreCRLExpiration': 'off', 'enableServerIdentityCheck': 'off', 'enableOCSPValidation': 'off', 'selectedOCSPService': '', 'rejectIfNoStatusFromOCSP': 'off', 'rejectIfUnreachableFromOCSP': 'off', 'sha256Fingerprint': '9acfab7e43c8d880d06b262a94deeee4b4659989c3d0caf19baf6405e41ab7df', 'link': {'rel': 'self', 'href': 'https://10.106.33.92/api/v1/certs/trusted-certificate/147d97cc-6ce9-43d7-9928-8cd0fa83e140', 'type': 'application/json'}},{'id': '2ed8db2d-a93c-45a7-b0de-4ee52978bf36', 'friendlyName': 'Certificate Services Endpoint Sub CA - ISE-RTP-CFME02-MNT#00026', 'subject': 'CN=Certificate Services Endpoint Sub CA - ISE-RTP-CFME02-MNT', 'issuedTo': 'Certificate Services Endpoint Sub CA - ISE-RTP-CFME02-MNT', 'issuedBy': 'Certificate Services Node CA - ISE-BGL-CFME01-PAN', 'keySize': '4096', 'signatureAlgorithm': 'SHA256withRSA', 'validFrom': 'Fri Jul 05 11:14:45 CST 2024', 'expirationDate': 'Fri Mar 24 16:19:21 CST 2034', 'serialNumberDecimalFormat': '32567431426291188219902826022164975182', 'description': "Auto import of trust certificate from PSN's CA server", 'status': 'Enabled', 'trustedFor': 'Infrastructure,Endpoints', 'internalCA': True, 'downloadCRL': 'off', 'crlDistributionUrl': None, 'automaticCRLUpdate': 'on', 'automaticCRLUpdatePeriod': '5', 'automaticCRLUpdateUnits': 'Minutes', 'nonAutomaticCRLUpdatePeriod': '1', 'nonAutomaticCRLUpdateUnits': 'Hours', 'crlDownloadFailureRetries': '10', 'crlDownloadFailureRetriesUnits': 'Minutes', 'authenticateBeforeCRLReceived': 'off', 'ignoreCRLExpiration': 'off', 'enableServerIdentityCheck': 'off', 'enableOCSPValidation': 'on', 'selectedOCSPService': 'Internal_OCSP_Service', 'rejectIfNoStatusFromOCSP': 'on', 'rejectIfUnreachableFromOCSP': 'off', 'sha256Fingerprint': '6162311dcf7a2517a6bb454b9e7e46ad64cbf4be1fcfc73680730304c94e28f7', 'link': {'rel': 'self', 'href': 'https://10.106.33.92/api/v1/certs/trusted-certificate/2ed8db2d-a93c-45a7-b0de-4ee52978bf36', 'type': 'application/json'}},{'id': '34ae5495-f892-422b-b27e-4e48246b54cc', 'friendlyName': 'Certificate Services OCSP Responder - ISE-RTP-CFME02-MNT#00027', 'subject': 'CN=Certificate Services OCSP Responder - ISE-RTP-CFME02-MNT', 'issuedTo': 'Certificate Services OCSP Responder - ISE-RTP-CFME02-MNT', 'issuedBy': 'Certificate Services Endpoint Sub CA - ISE-RTP-CFME02-MNT', 'keySize': '2048', 'signatureAlgorithm': 'SHA256withRSA', 'validFrom': 'Fri Jul 05 11:16:34 CST 2024', 'expirationDate': 'Fri Jul 06 11:16:34 CST 2029', 'serialNumberDecimalFormat': '32318639486615740757657486695632971049', 'description': "Auto import of trust certificate from PSN's CA server", 'status': 'Enabled', 'trustedFor': 'Infrastructure,Endpoints', 'internalCA': True, 'downloadCRL': 'off', 'crlDistributionUrl': None, 'automaticCRLUpdate': 'on', 'automaticCRLUpdatePeriod': '5', 'automaticCRLUpdateUnits': 'Minutes', 'nonAutomaticCRLUpdatePeriod': '1', 'nonAutomaticCRLUpdateUnits': 'Hours', 'crlDownloadFailureRetries': '10', 'crlDownloadFailureRetriesUnits': 'Minutes', 'authenticateBeforeCRLReceived': 'off', 'ignoreCRLExpiration': 'off', 'enableServerIdentityCheck': 'off', 'enableOCSPValidation': 'off', 'selectedOCSPService': '', 'rejectIfNoStatusFromOCSP': 'off', 'rejectIfUnreachableFromOCSP': 'off', 'sha256Fingerprint': 'bae344121c6fd3b9cfe43c4853406595f450b5d90c474419e8d692e0098a1200', 'link': {'rel': 'self', 'href': 'https://10.106.33.92/api/v1/certs/trusted-certificate/34ae5495-f892-422b-b27e-4e48246b54cc', 'type': 'application/json'}}], 'nextPage': None, 'previousPage': None, 'version': '1.0.1'}Get Trust Certificate By ID
This API can displays details of a Trust Certificate based on a given ID.
Step 1: Required information for an API call.
| Method | GET |
| URL |
https://<ISE-PAN-IP>/api/v1/certs/trusted-certificate/<ID-Of-Certificate>
|
| Credentials | Use Open API account credentials |
| Headers |
Accept: application/json
Content-Type: application/json
|
Step 2: Locate the URL that is utilized to retrieve deployment information.
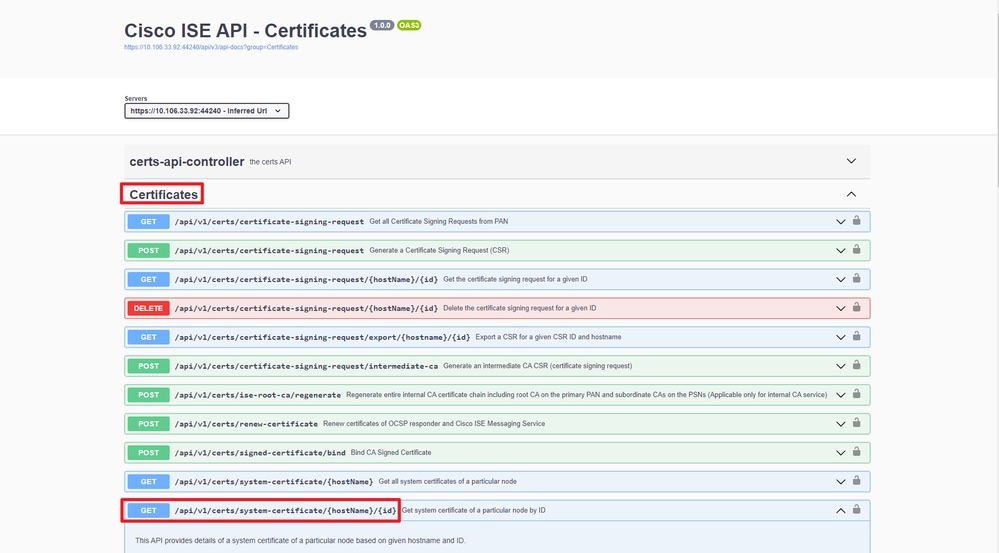 API URI
API URI
Step 3: Here is the example of Python Code. Copy and paste the content. Replace the ISE IP, username, password. Save as a python file to execute.
Ensure the good connectivity between ISE and the device running the python code example.
from requests.auth import HTTPBasicAuth
import requests
requests.packages.urllib3.disable_warnings()
if __name__ == "__main__":
url = "https://10.106.33.92/api/v1/certs/trusted-certificate/147d97cc-6ce9-43d7-9928-8cd0fa83e140"
headers = {"Accept": "application/json", "Content-Type": "application/json"}
basicAuth = HTTPBasicAuth("ApiAdmin", "Admin123")
response = requests.get(url=url, auth=basicAuth, headers=headers, verify=False)
print("Return Code:")
print(response.status_code)
print("Expected Outputs:")
print(response.json())
Note: The ID is from API outputs in step 3 of "Get List Of All Trusted Certificates", for example, 147d97cc-6ce9-43d7-9928-8cd0fa83e140 is "VeriSign Class 3 Public Primary Certification Authority".
Here is the example of expected outputs.
Return Code:
200
Expected Outputs:
{'response': {'id': '147d97cc-6ce9-43d7-9928-8cd0fa83e140', 'friendlyName': 'VeriSign Class 3 Public Primary Certification Authority', 'subject': 'CN=VeriSign Class 3 Public Primary Certification Authority - G5,OU=(c) 2006 VeriSign\\, Inc. - For authorized use only,OU=VeriSign Trust Network,O=VeriSign\\, Inc.,C=US', 'issuedTo': 'VeriSign Class 3 Public Primary Certification Authority - G5', 'issuedBy': 'VeriSign Class 3 Public Primary Certification Authority - G5', 'keySize': '2048', 'signatureAlgorithm': 'SHA1withRSA', 'validFrom': 'Wed Nov 08 08:00:00 CST 2006', 'expirationDate': 'Thu Jul 17 07:59:59 CST 2036', 'serialNumberDecimalFormat': '33037644167568058970164719475676101450', 'description': 'Auto imported for secure connection to cisco.com/perfigo.com', 'status': 'Enabled', 'trustedFor': 'Cisco Services', 'internalCA': False, 'downloadCRL': 'off', 'crlDistributionUrl': None, 'automaticCRLUpdate': 'on', 'automaticCRLUpdatePeriod': '5', 'automaticCRLUpdateUnits': 'Minutes', 'nonAutomaticCRLUpdatePeriod': '1', 'nonAutomaticCRLUpdateUnits': 'Hours', 'crlDownloadFailureRetries': '10', 'crlDownloadFailureRetriesUnits': 'Minutes', 'authenticateBeforeCRLReceived': 'off', 'ignoreCRLExpiration': 'off', 'enableServerIdentityCheck': 'off', 'enableOCSPValidation': 'off', 'selectedOCSPService': '', 'rejectIfNoStatusFromOCSP': 'off', 'rejectIfUnreachableFromOCSP': 'off', 'sha256Fingerprint': '9acfab7e43c8d880d06b262a94deeee4b4659989c3d0caf19baf6405e41ab7df', 'link': {'rel': 'self', 'href': 'https://10.106.33.92/api/v1/certs/trusted-certificate/147d97cc-6ce9-43d7-9928-8cd0fa83e140', 'type': 'application/json'}, 'isReferredInPolicy': False}, 'version': '1.0.1'}Troubleshoot
To troubleshoot issues that are related to the Open APIs, set theLog Levelfor theapiservicecomponent toDEBUGin theDebug Log Configurationwindow.
To enable debug, Navigate to Operations > Troubleshoot > Debug Wizard > Debug Log Configuration > ISE Node > apiservice.
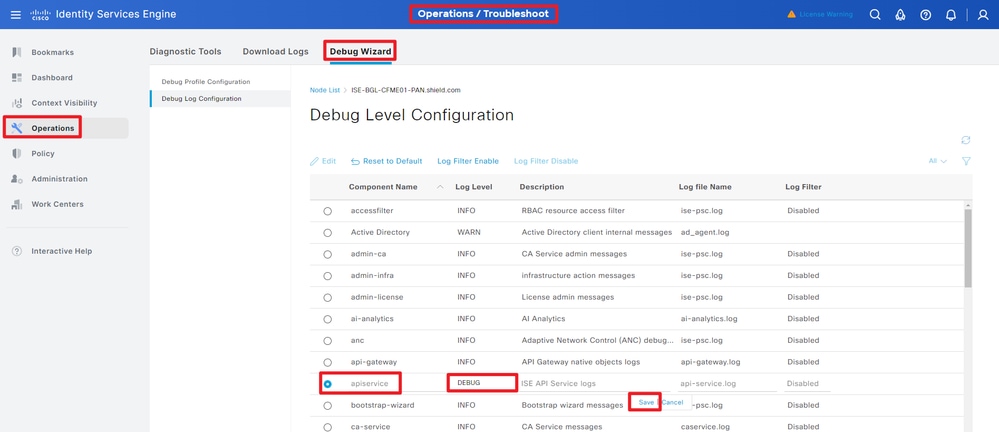 API Service Debug
API Service Debug
To download debug logs, Navigate to Operations > Troubleshoot > Downlaod Logs > ISE PAN Node > Debug Logs.
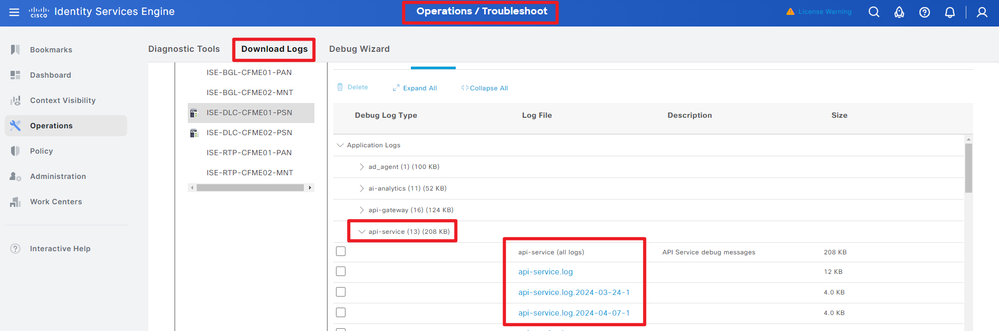 Download Debug Logs
Download Debug Logs
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
2.0 |
25-Jul-2024 |
Initial Release |
1.0 |
24-Jul-2024 |
Initial Release |
Contributed by Cisco Engineers
- Bo PangTechnical Consulting Engineer
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback