- Using Ethernet Operations Administration and Maintenance
- Configuring IEEE Standard-Compliant Ethernet CFM in a Service Provider Network
- Configuring ITU-T Y.1731 Fault Management Functions in IEEE CFM
- CFM CCM Extensions to Support the NSN Microwave 1+1 Hot Standby Protocol
- IEEE-Compliant CFM MIB
- Configuring Ethernet Connectivity Fault Management in a Service Provider Network
- Ethernet Performance Monitoring on Untagged EFPs
- Syslog Support for Ethernet Connectivity Fault Management
- Dynamic Ethernet Service Activation
- Layer 2 Access Control Lists on EVCs
- Static MAC Address Support on Service Instances and Pseudowires
- IEEE 802.1s on Bridge Domains
- IEEE 802.1ah on Provider Backbone Bridges
- Enabling Ethernet Local Management Interface
- Configuring Remote Port Shutdown
- Configuring Ethernet Local Management Interface at a Provider Edge
- Configuring IEEE 802.3ad Link Bundling and Load Balancing
- Multichassis LACP
- ICCP Multichassis VLAN Redundancy
- ITU-T G.8032 Ethernet Ring Protection Switching
- Configuring IP SLAs Metro-Ethernet 3.0 (ITU-T Y.1731) Operations
- IPSLA Y1731 On-Demand and Concurrent Operations
- Finding Feature Information
- Prerequisites for Configuring ITU-T G.8032 Ethernet Ring Protection Switching
- About ITU-T G.8032 Ethernet Ring Protection Switching
- Ring Protection Links
- ITU-T G.8032 Ethernet Ring Protection Switching Functionality
- R-APS Control Messages
- CFM Protocols and Link Failures
- G.8032 Ring-Supported Commands and Functionality
- G.8032 ERP Timers
- Protection Switching Functionality in a Single Link Failure and Recovery
- Ethernet Flow Points
- Service Instances and Associated EFPs
- How to Configure ITU-T G.8032 Ethernet Ring Protection Switching
- Configuring the Ethernet Ring Profile
- Configuring Ethernet CFM MEPs
- Enabling Ethernet Fault Detection for a Service
- Configuring the Ethernet Protection Ring
- Configuring Topology Change Notification Propagation
- Configuring a Service Instance
- Verifying the Ethernet Ring Protection (ERP) Switching Configuration
- Configuration Examples for ITU-T G.8032 Ethernet Ring Protection Switching
- Additional References for ITU-T G.8032 Ethernet Ring Protection Switching
- Feature Information For ITU-T G.8032 Ethernet Ring Protection Switching
ITU-T G.8032 Ethernet Ring Protection Switching
The ITU-T G.8032 Ethernet Ring Protection Switching feature implements protection switching mechanisms for Ethernet layer ring topologies. This feature uses the G.8032 Ethernet Ring Protection (ERP) protocol, defined in ITU-T G.8032, to provide protection for Ethernet traffic in a ring topology, while ensuring that no loops are within the ring at the Ethernet layer. The loops are prevented by blocking traffic on either a predetermined link or a failed link.
- Finding Feature Information
- Prerequisites for Configuring ITU-T G.8032 Ethernet Ring Protection Switching
- About ITU-T G.8032 Ethernet Ring Protection Switching
- How to Configure ITU-T G.8032 Ethernet Ring Protection Switching
- Configuration Examples for ITU-T G.8032 Ethernet Ring Protection Switching
- Additional References for ITU-T G.8032 Ethernet Ring Protection Switching
- Feature Information For ITU-T G.8032 Ethernet Ring Protection Switching
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest caveats and feature information, see Bug Search Tool and the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the feature information table at the end of this module.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
Prerequisites for Configuring ITU-T G.8032 Ethernet Ring Protection Switching
About ITU-T G.8032 Ethernet Ring Protection Switching
- Ring Protection Links
- ITU-T G.8032 Ethernet Ring Protection Switching Functionality
- R-APS Control Messages
- CFM Protocols and Link Failures
- G.8032 Ring-Supported Commands and Functionality
- G.8032 ERP Timers
- Protection Switching Functionality in a Single Link Failure and Recovery
- Ethernet Flow Points
- Service Instances and Associated EFPs
Ring Protection Links
An Ethernet ring consists of multiple Ethernet ring nodes. Each Ethernet ring node is connected to adjacent Ethernet ring nodes using two independent ring links. A ring link prohibits formation of loops that affect the network. The Ethernet ring uses a specific link to protect the entire Ethernet ring. This specific link is called the Ring Protection Link (RPL). A ring link is bound by two adjacent Ethernet ring nodes and a port for a ring link (also known as a ring port). There must be at least two Ethernet ring nodes in a Ethernet ring.
ITU-T G.8032 Ethernet Ring Protection Switching Functionality
The Ethernet ring protection functionality includes the following:
Loop avoidance in an Ethernet ring is achieved by ensuring that, at any time, traffic flows on all but the Ring Protection Link (RPL).
The following is a list of RPL types (or RPL nodes) and their functions:
RPL owner—Responsible for blocking traffic over the RPL so that no loops are formed in the Ethernet traffic. There can be only one RPL owner in a ring.
RPL neighbor node—An Ethernet ring node adjacent to the RPL. It is responsible for blocking its end of the RPL under normal conditions. This node type is optional and prevents RPL usage when protected.
RPL next-neighbor node—Next-neighbor node is an Ethernet ring node adjacent to an RPL owner node or RPL neighbor node. It is mainly used for FDB flush optimization on the ring. This node is also optional.
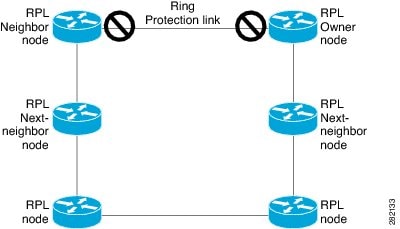
The following figure illustrates the G.8032 Ethernet ring topology.
R-APS Control Messages
Nodes on the ring use control messages called Ring Automatic Protection Switching (R-APS) messages to coordinate the activities of switching the ring protection link (RPL) on and off. Any failure along the ring triggers a R-APS Signal Failure (R-APS SF) message in both directions of the nodes adjacent to the failed link, after the nodes have blocked the port facing the failed link. On obtaining this message, the RPL owner unblocks the RPL port.
 Note | A single link failure in the ring ensures a loop-free topology. |
CFM Protocols and Link Failures
Connectivity Fault Management (CFM) and line status messages are used to detect ring link and node failure. During the recovery phase, when the failed link is restored, the nodes adjacent to the restored link send Ring Automatic Protection Switching (R-APS) No Request (R-APS NR) messages. On obtaining this message, the ring protection link (RPL) owner blocks the RPL port and sends R-APS NR and R-APS RPL (R-APS NR, RB) messages. These messages cause all other nodes, other than the RPL owner in the ring, to unblock all blocked ports. The Ethernet Ring Protection (ERP) protocol works for both unidirectional failure and multiple link failure scenarios in a ring topology.
 Note | The G.8032 Ethernet Ring Protection (ERP) protocol uses CFM Continuity Check Messages (CCMs) at an interval of 3.3 milliseconds (ms). At this interval (which is supported only on selected platforms), SONET-like switching time performance and loop-free traffic can be achieved. |
G.8032 Ring-Supported Commands and Functionality
A G.8032 ring supports these basic operator administrative commands:
Force switch (FS)—Allows the operator to forcefully block a particular ring port. Note the following points about FS commands: Manual switch (MS)—Allows the operator to manually block a particular ring port. Note the following points about MS commands: Clear—Cancels an existing FS or MS command on the ring port. The Clear command is used at the ring protection link (RPL) owner to clear a nonrevertive mode condition.
A G.8032 ring can support multiple instances. An instance is a logical ring running over a physical ring. Such instances are used for various reasons, such as load-balancing VLANs over a ring. For example, odd-numbered VLANs may go in one direction of the ring, and even-numbered VLANs may go in the other direction. Specific VLANs can be configured under only one instance. They cannot overlap multiple instances. Otherwise, data traffic or Ring Automatic Protection Switching (R-APS) messages may cross logical rings, which is not desirable.
G.8032 ERP Timers
The G.8032 Ethernet Ring Protection (ERP) protocol specifies the use of different timers to avoid race conditions and unnecessary switching operations:
Delay timers—Used by the Ring Protection Link (RPL) owner to verify that the network has stabilized before blocking the RPL. Note the following points about delay timers. - After a signal failure (SF) condition, a Wait-to-Restore (WTR) timer is used to verify that the SF is not intermittent.
- The WTR timer can be configured by the operator. The default time interval is 5 minutes; the time interval ranges from 1 to 12 minutes.
- After a force switch (FS) or a manual switch (MS) command is issued, a Wait-to-Block (WTB) timer is used to verify that no background condition exists.
 Note | The WTB timer interval may be shorter than the WTR timer interval. |
Guard timer—Used by all nodes when changing state; the guard timer blocks latent outdated messages from causing unnecessary state changes. The guard timer can be configured. The default time interval is 500 ms; the time interval ranges from 10 to 2000 ms.
Hold-off timers—Used by the underlying Ethernet layer to filter out intermittent link faults. The hold-off timer can be configured. The default time interval is 0 seconds; the time interval ranges from 0 to 10 seconds. Faults are reported to the ring protection mechanism only if this timer expires.
Protection Switching Functionality in a Single Link Failure and Recovery
The following figure illustrates protection switching functionality in a single-link failure.
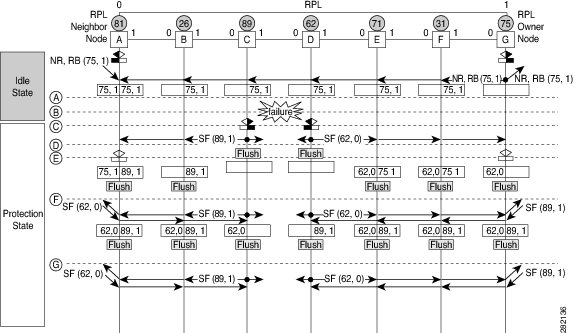

The figure represents an Ethernet ring topology consisting of seven Ethernet ring nodes. The ring protection link (RPL) is the ring link between Ethernet ring nodes A and G. In this topology, both ends of the RPL are blocked. Ethernet ring node G is the RPL owner node, and Ethernet ring node A is the RPL neighbor node.
The following sequence describes the steps followed in the single-link failure:
A link operates in the normal condition.
A failure occurs.
Ethernet ring nodes C and D detect a local signal failure (SF) condition and after the hold-off time interval, block the failed ring port and perform the FDB flush.
Ethernet ring nodes C and D start sending Ring Automatic Protection Switching (R-APS) SF messages periodically along with the (node ID and bidirectional path-protected ring (BPR) identifier pair) on both ring ports while the SF condition persists.
All Ethernet ring nodes receiving an R-APS SF message perform the FDB flush. When the RPL owner node G and RPL neighbor node A receive an R-APS SF message, the Ethernet ring node unblocks its end of the RPL and performs the FDB flush.
All Ethernet ring nodes receiving a second R-APS SF message perform the FDB flush again; the additional FDB flush is because of the node ID and BPR-based configuration.
R-APS SF messages are detected on the Ethernet Ring indicating a stable SF condition. Further R-APS SF messages trigger no further action.
The following figure illustrates the steps taken in a revertive operation in a single-link failure.
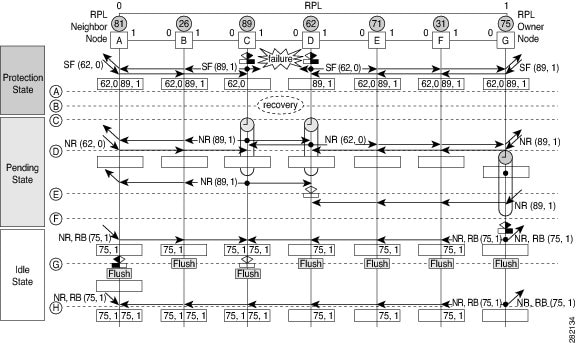
The following sequence describes the steps followed in the single-link failure revertive (recovery) operation:
A link operates in the stable SF condition.
Recovery of link failure occurs.
Ethernet ring nodes C and D detect clearing of the SF condition, start the guard timer, and initiate periodic transmission of the R-APS No Request (NR) messages on both ring ports. (The guard timer prevents the reception of R-APS messages.)
When the Ethernet ring nodes receive an R-APS NR message, the node ID and BPR identifier pair of a receiving ring port is deleted and the RPL owner node starts the Wait-to-Restore (WTR) timer.
When the guard timer expires on Ethernet ring nodes C and D, the nodes may accept the new R-APS messages, if any. Ethernet ring node D receives an R-APS NR message with a higher node ID from Ethernet ring node C, and unblocks its nonfailed ring port.
When the WTR timer expires, the RPL owner node blocks its end of the RPL, sends R-APS (NR or route blocked [RB]) message with the (node ID and BPR identifier pair), and performs the FDB flush.
When Ethernet ring node C receives an R-APS (NR or RB) message, the node removes the block on its blocked ring ports, and stops sending R-APS NR messages. On the other hand, when the RPL neighbor node A receives an R-APS NR or RB message, the node blocks its end of the RPL. In addition, Ethernet ring nodes A to F perform the FDB flush when receiving an RAPS NR or RB message because of the node ID and BPR-based configuration.
Ethernet Flow Points
An Ethernet flow point (EFP) is a forwarding decision point in the provider edge (PE) router, which gives network designers flexibility to make many Layer 2 flow decisions within the interface. Many EFPs can be configured on a single physical port. (The number varies from one device to another.) EFPs are the logical demarcation points of an Ethernet virtual connection (EVC) on an interface. An EVC that uses two or more user network interfaces (UNIs) requires an EFP on the associated ingress and egress interfaces of every device that the EVC passes through.
EFPs can be configured on any Layer 2 traffic port; however, they are usually configured on UNI ports. The following parameters (matching criteria) can be configured on the EFP:
A frame passes each configured match criterion until the correct matching point is found. If a frame does not fit any of the matching criteria, it is dropped. Default criteria can be configured to avoid dropping frames.
The following types of commands can be used in an EFP:
Service Instances and Associated EFPs
Configuring a service instance on a Layer 2 port creates a pseudoport or EFP on which you configure EVC features. Each service instance has a unique number per interface, but you can use the same number on different interfaces because service instances on different ports are not related.
An EFP classifies frames from the same physical port to one of the multiple service instances associated with that port, based on user-defined criteria. Each EFP can be associated with different forwarding actions and behavior.
When an EFP is created, the initial state is UP. The state changes to DOWN under the following circumstances:
The EFP is explicitly shut down by a user.
The main interface to which the EFP is associated is down or removed.
If the EFP belongs to a bridge domain, the bridge domain is down.
The EFP is forced down as an error-prevention measure of certain features.
Use the service instance ethernet interface configuration command to create an EFP on a Layer 2 interface and to enter service instance configuration mode. Service instance configuration mode is used to configure all management and control data plane attributes and parameters that apply to the service instance on a per-interface basis. The service instance number is the EFP identifier.
After the device enters service instance configuration mode, you can configure these options:
default--Sets a command to its defaults
description--Adds a service instance-specific description
encapsulation--Configures Ethernet frame match criteria
exit--Exits from service instance configuration mode
no--Negates a command or sets its defaults
shutdown--Takes the service instance out of service
How to Configure ITU-T G.8032 Ethernet Ring Protection Switching
- Configuring the Ethernet Ring Profile
- Configuring Ethernet CFM MEPs
- Enabling Ethernet Fault Detection for a Service
- Configuring the Ethernet Protection Ring
- Configuring Topology Change Notification Propagation
- Configuring a Service Instance
- Verifying the Ethernet Ring Protection (ERP) Switching Configuration
Configuring the Ethernet Ring Profile
To configure the Ethernet ring profile, complete the following steps.
1.
enable
2.
configure
terminal
3.
ethernet
ring
g8032
profile
profile-name
4.
timer
{guard
seconds |
hold-off
seconds |
wtr
minutes}
5.
non-revertive
6.
end
DETAILED STEPS
Configuring Ethernet CFM MEPs
Configuring Ethernet Connectivity Fault Management (CFM) maintenance endpoints (MEPs) is optional although recommended for fast failure detection and CFM monitoring. When CFM monitoring is configured, note the following points:
Enabling Ethernet Fault Detection for a Service
To enable Ethernet Fault Detection (EFD) for a service to achieve fast convergence, complete the following steps
1.
enable
2.
configure
terminal
3.
ethernet
cfm
global
4.
link-protection enable
5.
link-protection
group management vlan vlan-id
6.
link-protection
group group-number pccm vlan vlan-id
7.
ethernet
cfm domaindomain-name level level-id [direction outward]
8.
service {ma-name | ma-num | vlan-id vlan-id | vpn-id vpn-id} [port | vlan vlan-id [direction down]]
9.
continuity-check
[interval time | loss-threshold threshold | static rmep]
10.
efd notify g8032
11.
end
DETAILED STEPS
Configuring the Ethernet Protection Ring
To configure the Ethernet Protection Ring (EPR), complete the following steps.
1.
enable
2.
configure
terminal
3.
ethernet
ring
g8032
ring-name
4.
port0
interface
type
number
5.
monitor
service
instance
instance-id
6.
exit
7.
port1
{interfacetype
number |
none}
8.
monitor
service
instance
instance-id
9.
exit
10.
exclusion-list
vlan-ids
vlan-id
11.
open-ring
12.
instance
instance-id
13.
description
descriptive-name
14.
profile
profile-name
15.
rpl
{port0 |
port1} {owner |
neighbor |
next-neighbor
}
16.
inclusion-list
vlan-ids
vlan-id
17.
aps-channel
18.
level
level-value
19.
port0
service
instance
instance-id
20.
port1
service
instance
{instance-id
| none
}
21.
end
DETAILED STEPS
Configuring Topology Change Notification Propagation
To configure topology change notification (TCN) propagation, complete the following steps.
1.
enable
2.
configure
terminal
3.
ethernet
tcn-propagation
G8032 to {REP | G8032}
4.
end
DETAILED STEPS
Configuring a Service Instance
To configure a service instance, complete the following steps.
1.
enable
2.
configure
terminal
3.
interface
type
number
4.
service
instance
instance-id
ethernet
[evc-id]
5.
encapsulation
dot1q
vlan-id
[native]
6.
bridge-domain
bridge-id
[split-horizon [group
group-id]]
7.
end
DETAILED STEPS
Verifying the Ethernet Ring Protection (ERP) Switching Configuration
To verify the ERP switching configuration, use one or more of the following commands in any order.
1.
enable
2.
show
ethernet
ring
g8032
status [ring-name] [instance [instance-id]]
3.
show
ethernet
ring
g8032
brief [ring-name] [instance [instance-id]]
4.
show
ethernet
ring
g8032
summary
5.
show
ethernet
ring
g8032
statistics [ring-name] [instance [instance-id]]
6.
show
ethernet
ring
g8032
profile [profile-name]
7.
show
ethernet
ring
g8032
port
status
interface [type number]
8.
show
ethernet
ring
g8032
configuration [ring-name]
instance [instance-id]
9.
show
ethernet
ring
g8032
trace {ctrl [ring-name
instance
instance-id] |
sm}
10.
end
DETAILED STEPS
Configuration Examples for ITU-T G.8032 Ethernet Ring Protection Switching
- Example: Configuring Ethernet Ring Protection Switching
- Example: Enabling Ethernet Fault Detection for a Service
- Example: Verifying the Ethernet Ring Protection Configuration
Example: Configuring Ethernet Ring Protection Switching
The following is an example of an Ethernet Ring Protection (ERP) switching configuration:
ethernet ring g8032 profile profile_ABC timer wtr 1 timer guard 100 timer hold-off 1 ethernet ring g8032 major_ring_ABC exclusion-list vlan-ids 1000 port0 interface FastEthernet 0/0/0 monitor service instance 103 port1 interface FastEthernet 0/1/0 monitor service instance 102 instance 1 profile profile_ABC rpl port0 owner inclusion-list vlan-ids 100 aps-channel port0 service instance 100 port1 service instance 100 ! interface FastEthernet 0/0/0 no ip address service instance 100 ethernet encapsulation dot1q 100 bridge-domain 100 service instance 200 ethernet encapsulation dot1q 200 bridge-domain 200 ! ! interface FastEthernet 0/1/1 no ip address service instance 100 ethernet encapsulation dot1q 100 bridge-domain 100 service instance 200 ethernet encapsulation dot1q 200 bridge-domain 200 ! !
Example: Enabling Ethernet Fault Detection for a Service
ethernet cfm domain G8032 level 4 service 8032_service evc 8032-evc vlan 1001 direction down continuity-check continuity-check interval 3.3ms offload sampling 1000 efd notify g8032 ethernet ring g8032 profile TEST timer wtr 1 timer guard 100 ethernet ring g8032 open open-ring port0 interface GigabitEthernet0/1/3 monitor service instance 1001 port1 none instance 1 profile TEST inclusion-list vlan-ids 2-500,1001 aps-channel port0 service instance 1001 port1 none ! ! instance 2 profile TEST rpl port0 owner inclusion-list vlan-ids 1002,1005-2005 aps-channel port0 service instance 1002 port1 none ! interface GigabitEthernet0/1/3 no ip address load-interval 30 shutdown negotiation auto storm-control broadcast level 10.00 storm-control multicast level 10.00 storm-control unicast level 90.00 service instance 1 ethernet encapsulation untagged l2protocol peer lldp bridge-domain 1 ! service instance trunk 10 ethernet encapsulation dot1q 2-500,1005-2005 rewrite ingress tag pop 1 symmetric bridge-domain from-encapsulation ! service instance 1001 ethernet 8032-evc encapsulation dot1q 1001 rewrite ingress tag pop 1 symmetric bridge-domain 1001 cfm mep domain G8032 mpid 20 ! service instance 1002 ethernet 8032-evc-1 encapsulation dot1q 1002 rewrite ingress tag pop 1 symmetric bridge-domain 1002 ! End
Example: Verifying the Ethernet Ring Protection Configuration
The following is sample output from the show ethernet ring g8032 configuration command. Use this command to verify if the configuration entered is valid and to check for any missing configuration parameters.
Device# show ethernet ring g8032 configuration ethernet ring ring0 Port0: GigabitEthernet0/0/0 (Monitor: GigabitEthernet0/0/0) Port1: GigabitEthernet0/0/4 (Monitor: GigabitEthernet0/0/4) Exclusion-list VLAN IDs: 4001-4050 Open-ring: no Instance 1 Description: Profile: opp RPL: Inclusion-list VLAN IDs: 2,10-500 APS channel Level: 7 Port0: Service Instance 1 Port1: Service Instance 1 State: configuration resolved
Additional References for ITU-T G.8032 Ethernet Ring Protection Switching
Related Documents
|
Related Topic |
Document Title |
|---|---|
|
Ethernet Connectivity Fault Management (CFM) |
Configuring Ethernet Connectivity Fault Management in a Service Provider Network |
|
G.8032 Ethernet Ring Protection (ERP) administrative procedures |
|
|
Carrier Ethernet commands: complete command syntax, command mode, command history, defaults, usage guidelines, and examples |
Cisco IOS Carrier Ethernet Command Reference |
|
Cisco IOS commands: master list of commands with complete command syntax, command mode, command history, defaults, usage guidelines, and examples |
Standards
|
Standard |
Title |
|---|---|
|
ITU-T |
ITU-T Y.1731 OAM Mechanisms for Ethernet-Based Networks |
Technical Assistance
|
Description |
Link |
|---|---|
|
The Cisco Support and Documentation website provides online resources to download documentation, software, and tools. Use these resources to install and configure the software and to troubleshoot and resolve technical issues with Cisco products and technologies. Access to most tools on the Cisco Support and Documentation website requires a Cisco.com user ID and password. |
Feature Information For ITU-T G.8032 Ethernet Ring Protection Switching
The following table provides release information about the feature or features described in this module. This table lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
|
Feature Name |
Releases |
Feature Information |
|---|---|---|
|
ITU-T G.8032 Ethernet Ring Protection Switching |
15.2(4)S 15.3(1)S |
The ITU-T G.8032 Ethernet Ring Protection Switching feature implements protection switching mechanisms for Ethernet layer ring topologies. This feature uses the G.8032 Ethernet Ring Protection (ERP) protocol, defined in ITU-T G.8032, to provide protection for Ethernet traffic in a ring topology, while ensuring that no loops are within the ring at the Ethernet layer. The loops are prevented by blocking traffic on either a predetermined link or a failed link. The following commands were introduced or modified: aps-channel, clear ethernet ring g8032 statistics, debug ethernet ring g8032 errors, debug ethernet ring g8032 events, debug ethernet ring g8032 fsm, debug ethernet ring g8032 packets, description (Ethernet ring), ethernet ring g8032, ethernet ring g8032 profile, ethernet tcn-propagation, exclusion-list, inclusion-list, instance (Ethernet ring), level, monitor service instancenon-revertiveopen-ring, port0, port0 service instance, port1, port1 service instance, profile, rpl, show ethernet cfm domain, show ethernet cfm errors,show ethernet cfm maintenance-points remote, show ethernet cfm maintenance-points remote crosscheck, show ethernet ring g8032 brief, show ethernet ring g8032 configuration, show ethernet ring g8032 port status, show ethernet ring g8032 profile, show ethernet ring g8032 statistics, show ethernet ring g8032 status, show ethernet ring g8032 summary , show ethernet ring g8032 trace,show ethernet service instance and timer (Ethernet ring). |
 Feedback
Feedback