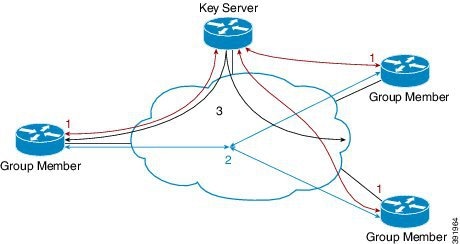
Over a period of time, you may want to upgrade and migrate your key
servers and group members to G-IKEv2. Migration from GDOI to G-IKEv2 for an
entire GETVPN group requires careful planning. You cannot migrate all your
group members at the same time. The migration entails allowing GDOI group
members and G-IKEv2 group members to communicate using the same traffic
encryption key (TEK) while using different control plane protocols—GDOI and
G-IKEv2. A GDOI to G-IKEv2 migration sequence includes the following:
-
Backward compatibility—The new Cisco IOS software image containing
the GETVPN G-IKEv2 feature must support existing GDOI features and must be
consistent with for earlier releases of GDOI features for Cisco IOS software.
-
Service upgrade—The recommended sequence for changing the Cisco IOS
software image is secondary key server, primary key server, and group member.
-
Service downgrade—The recommended sequence for changing the Cisco
IOS software image is group member, secondary key server, and primary key
server.
Service Upgrade Procedure
-
Save the existing key server and group member GDOI configurations.
For more information, see the “Configuration Replace and Configuration
Rollback” feature module in the
Managing Configuration Files Configuration Guide.
-
Configure a key encryption key (KEK) and a traffic encryption key
(TEK) lifetime on all key servers to avoid network split and merge during the
migration of the key servers. Use the crypto gdoi ks rekey command to configure
the new lifetimes.
-
Upgrade key server to the new Cisco IOS software images. Follow
the sequence mentioned above—start with the secondary key server followed by
the primary key server. All existing configurations that use the keyword
gdoi will be converted to the keyword
gkm . For example, the global
configuration command
crypto gdoi group will be converted to
crypto gkm group command. However, the
groups continue to use GDOI for registration and rekey.
-
On key server, execute the
gikev2 command in the server local
command for groups that support GDOI and G-IKEv2 group members.
-
Upgrade group members to the new Cisco IOS software image. All
existing configurations that use the keyword "gdoi "
will be converted to the keyword
gkm . For example, the global
configuration commands
crypto gdoi group and
crypto map gdoi will be converted to
"crypto gkm group " and
crypto map gkm respectively. These groups
continue to use GDOI for registration and rekey and include the
client protocol gdoi command.
-
Configure the
client protocol gikev2 command to use
G-IKEv2 on group member.
-
Configure the
no gdoi command in the server local
command, to stop servicing GDOI group members.
For a group member to use GDOI after upgrading to G-IKEv2, configure
the
client protocol gdoi command in the group
member group configuration. Group member registers again with key server using
GDOI instead of G-IKEv2.

Note
|
Before you convert group member, ensure that key server to which
group member is registered is configured with the gdoi command in GDOI local
server configuration mode.
|
Service Downgrade Procedure
Use the previously saved GDOI configurations (saved before upgrade
procedure) and downgrade the Cisco IOS software for each group member. Next,
downgrade the key server; beginning with the secondary key server followed by
primary key server. For more information, see the “Configuration Replace and
Configuration Rollback” feature module in the
Managing Configuration Files Configuration Guide.
Migration Examples
This section provides examples on GDOI to G-IKEv2 migration. The
following examples show how the GDOI group g1 is converted to a GKM group after
upgrading to a G-IKEv2 Cisco IOS software image. The following is a sample key
server configuration before Cisco IOS software upgrade.
crypto gdoi group g1
identity 1111
server local
.
.
.
sa ipsec 1
profile getvpn_profile
match address getvpn_acl
.
.
.
redundancy
.
.
.
The following is a sample key server configuration after Cisco IOS
software upgrade. In this example, the commands
gdoi ,
no gikev2 , and
gikev2 are automatically added. The
gikev2 command starts accepting G-IKEv2
registrations.
crypto gkm group g1
identity 1111
server local
gdoi
no gikev2
gikev2 ikev2_profile1
.
.
.
sa ipsec 1
profile getvpn_profile
match address getvpn_acl
.
.
.
redundancy
.
.
.
The following is a sample group member configuration before Cisco IOS
software upgrade.
crypto gdoi group g1
identity 1111
server address ipv4 ks1
server address ipv4 ks2
crypto map GETVPN_CM 10 gdoi
set group g1
interface g0/0/0
crypto map GETVPN_CM
The following is a sample group member configuration after Cisco IOS
software upgrade. In this example, the commands
client protocol gdoi and
client protocol gikev2 are automatically
added. The
client protocol gikev2 command starts using
G-IKEv2.
crypto gkm group g1
identity 1111
server address ipv4 ks1
server address ipv4 ks2
client protocol gdoi
client protocol gikev2 ikev2_profile1 ] – Configure this to start using G-IKEv2
crypto map GETVPN_CM 10 gdoi
set group g1
interface g0/0/0
crypto map GETVPN_CM


 Feedback
Feedback