Restrictions for Cisco Umbrella Integration
-
If an application or host uses IP address directly instead of DNS to query domain names, policy enforcement is not applied.
-
When the client is connected to a web proxy, the DNS query does not pass through the Cisco device. In this case, the connector does not detect any DNS request and the connection to the web server bypasses any policy from the Cisco Umbrella portal.
-
When the Cisco Umbrella Integration policy blocks a DNS query, the client is redirected to a Cisco Umbrella block page. HTTPS servers provide these block pages and the IP address range of these block pages is defined by the Cisco Umbrella portal.
-
User authentication and identity is not supported in this release.
-
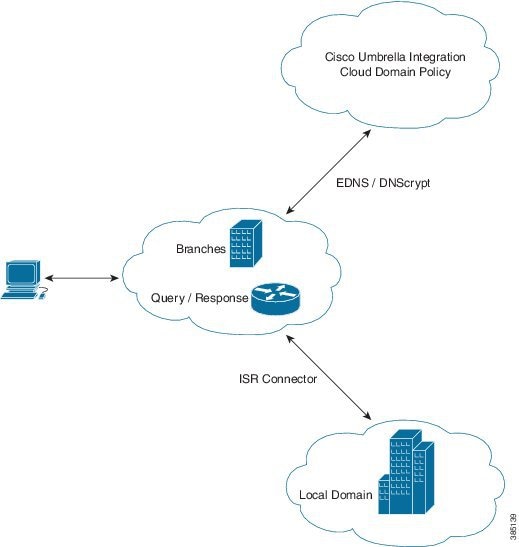
The type A, AAAA, and TXT queries are the only records that are redirected. Other types of query bypasses the connector. Cisco Umbrella Connector maintains a list of IP address that is known for malicious traffic. When the Cisco Umbrella roaming client detects the destination of packets to those addresses, it forwards those addresses to Cisco Umbrella cloud for further inspection.
-
Only the IPv4 address of the host is conveyed in the EDNS option.
-
A maximum of 64 local domains can be configured, and the allowed domain name length is 100 characters.

 Feedback
Feedback