Cisco WAE 6.3 System Administration Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- December 10, 2015
Chapter: LDAP Configuration
LDAP Configuration
Overview
Cisco WAE supports authentication and authorization of foreign users using the LDAP protocol. The embedded directory service within the WAE system is based upon Java Enterprise Directory libraries that are linked with the Tomcat server instance. The objective of the LDAP module is to allow customers to map multiple LDAP user groups to privilege level roles in the WAE system.
Pre-Installation Steps
Step 1![]() Install the ldapsearch binary.
Install the ldapsearch binary.

Note![]() The ldapsearch binary is not required for the normal operation of LDAP with a WAE server. It is only necessary to discover the correct formatting of the LDAP schema required to configure the LDAP server settings. If necessary, the ldapsearch binary can be installed on an alternative machine. We recommend installing the binary on the WAE server as it can assist in troubleshooting LDAP protocol connection issues with the LDAP servers.
The ldapsearch binary is not required for the normal operation of LDAP with a WAE server. It is only necessary to discover the correct formatting of the LDAP schema required to configure the LDAP server settings. If necessary, the ldapsearch binary can be installed on an alternative machine. We recommend installing the binary on the WAE server as it can assist in troubleshooting LDAP protocol connection issues with the LDAP servers.
sudo yum install openld ap-clients
sudo apt-get install ldap-utils openssl libpam-ldap
Step 2![]() Gather LDAP server information. See Table 4-1 for a list of information required and the variables that are used throughout this chapter to represent this information.
Gather LDAP server information. See Table 4-1 for a list of information required and the variables that are used throughout this chapter to represent this information.
Step 3![]() Retrieve the LDAP schema from the LDAP server.
Retrieve the LDAP schema from the LDAP server.
ldapsearch -x -v -W -LLL -a always -h <ldap-server> -b <ldap-base-ou> -D <admin-user-dn>
This command assumes that the LDAP server does not use certificates or SSL encryption.
Note If you are dealing with a large LDAP dataset we recommend you use command line filters and/or pipe the output to a file.
This example uses parameters from a fictitious company:
ldapsearch -x -v -W -LLL -a always -h ldap-server.company.com -b "dc=company, dc=com" -D "cn=admin,dc=company,dc=com"
ldap_initialize( ldap://ldap-server.company.com)
Enter LDAP Password: <admin-password>
Step 4![]() Review the LDAP schema.
Review the LDAP schema.
Example 4-1shows a trimmed down version of an LDAP schema. Bold text denotes information that is required later for LDAP authentication and authorization.
Example 4-1 Trimmed Example of LDAP Schema
(These are Organization Units containing other LDAP objects)
Table 4-1 LDAP Server Information Needed for Configuration
Configuring LDAP
You must have administrator privileges to configure LDAP.
Step 1![]() From the WAE UI, select System > LDAP Server.
From the WAE UI, select System > LDAP Server.
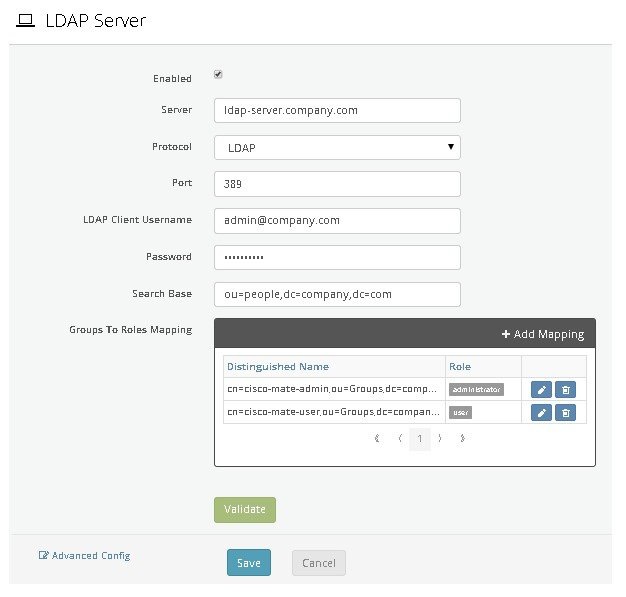
Step 2![]() Enter the information needed for all fields, except within the Groups To Roles Mapping area. Leave the Groups To Roles Mapping area blank. For field descriptions, see Table 4-2 .
Enter the information needed for all fields, except within the Groups To Roles Mapping area. Leave the Groups To Roles Mapping area blank. For field descriptions, see Table 4-2 .
|
|
|
|---|---|
Select to enable use of the LDAP server for user authentication. This must be selected to use the LDAP server for authentication. |
|
LDAP server IP address or FQDN, which is the server’s hostname with the DNS domain name appended to the end. |
|
Applicable only if LDAPS is selected as the protocol. Use this option if you do not expect the LDAP server to have a valid SSL certificate for establishing encrypted communication with this system. If this option is not selected, the communication cannot be established unless the certificate used by the LDAP server to establish communication is valid. |
|
Port used to reach the LDAP server. For unencrypted authentication the default is TCP 389. For encrypted authentication the default is TCP 636. |
|
The DN for the LDAP user login which requires minimum read only access to the necessary sections of the LDAP Tree schema. This should be in the DN format: "cn=admin,dc=company,dc=com" This information was collected in Pre-Installation Steps. |
|
| This information was collected in Pre-Installation Steps. |
|
This is the Distinguished Name of the base search OU for all user accounts that should have permission to login to the WAE Server. This information was collected in Pre-Installation Steps. |
Step 3![]() Click Validate to test the LDAP configuration you have entered. A window displaying test results appears.
Click Validate to test the LDAP configuration you have entered. A window displaying test results appears.

Note![]() If there are failures, you may have entered an incorrect server address or the LDAP user login is invalid. To resolve these issues, contact your LDAP system administrator.
If there are failures, you may have entered an incorrect server address or the LDAP user login is invalid. To resolve these issues, contact your LDAP system administrator.
Step 4![]() Configure LDAP group to roles mapping.
Configure LDAP group to roles mapping.
WAE mappings defaults to support Microsoft's Active Directory LDAP Schema.If you are using Active Directory you will not need to perform any advanced configurations.
The WAE LDAP system supports only one of the following mappings (cannot be mixed):
- LDAP Administrative Groups to Mate/WAE Groups in a Many : One relationship
- LDAP Specific Users to Mate/WAE Groups in a Many : One relationship

Note![]() To configure LDAP specific users group mappings, contact your support representative.
To configure LDAP specific users group mappings, contact your support representative.
a.![]() From the LDAP schema that you downloaded in Pre-Installation Steps, identify the LDAP administrative groups (see Example 4-1). Locate the DN for the LDAP group objects that contain the LDAP attribute objectClass: groupOfUniqueNames.
From the LDAP schema that you downloaded in Pre-Installation Steps, identify the LDAP administrative groups (see Example 4-1). Locate the DN for the LDAP group objects that contain the LDAP attribute objectClass: groupOfUniqueNames.
c.![]() Enter the Distinguished Name. For example, cn=cisco-mate-admin,ou=Groups,dc=company,dc=com.
Enter the Distinguished Name. For example, cn=cisco-mate-admin,ou=Groups,dc=company,dc=com.
d.![]() Check either the User or Administrator Role check box.
Check either the User or Administrator Role check box.
e.![]() Repeat these steps to add more mappings.
Repeat these steps to add more mappings.
Figure 4-1 shows an example of an LDAP Server page with populated fields.
Figure 4-1 Example of LDAP Server Page With Populated Fields
Step 5![]() Click the Advanced Configuration link located at the bottom left of the LDAP Server page. The Edit System Object window appears.
Click the Advanced Configuration link located at the bottom left of the LDAP Server page. The Edit System Object window appears.
Step 6![]() View Table 4-3 and determine if lines 7 and 8 must be edited, then click Save.
View Table 4-3 and determine if lines 7 and 8 must be edited, then click Save.
|
|
|
|---|---|
Default : The The From the LDAP schema (Example 4-1), use the User Unique Attribute The WAE server will search all objects under the LDAP search base tree for: Common alternatives include |
|
Default : There are 2 options available here: The WAE server will look for Group based searches locates the membership of each administrative group that a particular user is a member of. Administrative Groups are based on From the LDAP schema, find the unique attribute that lists the user association to the Group of Unique Names. In Example 4-1, this is |
Table 4-4 lists configuration examples that were based on tested default installations of the LDAP servers with default LDAP schema that were provided by the software vendor.
Step 7![]() From the LDAP Server page, click Save.
From the LDAP Server page, click Save.
Step 8![]() To validate configuration, log off and log on to the WAE UI with a valid LDAP user account.
To validate configuration, log off and log on to the WAE UI with a valid LDAP user account.

Note If you are experience issues, we recommend the following:
–![]() $CARIDEN_HOME/lib/web/apache-tomcat-6.0.37/logs/catalina.
$CARIDEN_HOME/lib/web/apache-tomcat-6.0.37/logs/catalina.
–![]() $CARIDEN_HOME/lib/web/apache-tomcat-6.0.37/logs/catalina.out
$CARIDEN_HOME/lib/web/apache-tomcat-6.0.37/logs/catalina.out
–![]() $CARIDEN_HOME/lib/web/apache-tomcat-6.0.37/logs/mate_live.log
$CARIDEN_HOME/lib/web/apache-tomcat-6.0.37/logs/mate_live.log
–![]() $CARIDEN_HOME/lib/web/apache-tomcat-6.0.37/logs/user_manager.log
$CARIDEN_HOME/lib/web/apache-tomcat-6.0.37/logs/user_manager.log
Table 4-4 Advanced Configurations Tested on Default LDAP Server Installations With Default LDAP Schema
|
|
|
|
|---|---|---|
 Feedback
Feedback