Feature Information for Cisco Umbrella Integration
The following table provides release information about the feature or features described in this module. This table lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to www.cisco.com/go/cfn. An account on Cisco.com is not required.
|
Feature Name |
Releases |
Feature Information |
|---|---|---|
|
Cisco Umbrella Integration |
Cisco IOS XE Everest Release 16.6.1 |
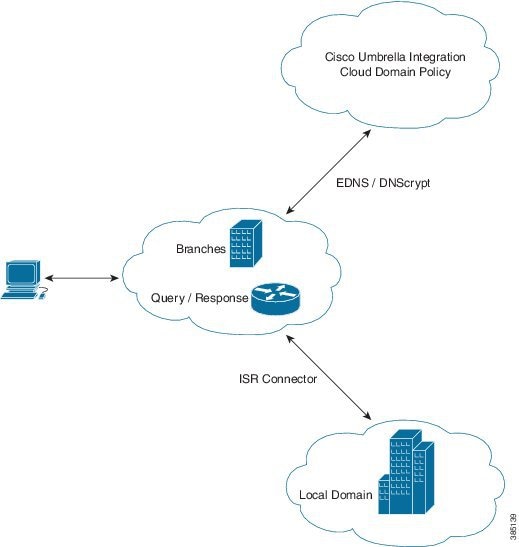
The Cisco Umbrella Integration feature enables cloud-based security service by inspecting the DNS query that is sent to the DNS server through Cisco 1000 Series Integrated Services Routers (ISR). The security administrator configures policies on the Umbrella cloud to either allow or deny traffic towards the fully qualified domain name (FQDN). |

 Feedback
Feedback