Security Cloud Control Command Line Interface
Security Cloud Control provides users with a command line interface (CLI) for managing , SSH-managed, devices. Users can send commands to a single device or to multiple devices simultaneously.
Using the Command Line Interface
Procedure
|
Step 1 |
In the left pane, click . |
||
|
Step 2 |
Click the Devices tab. |
||
|
Step 3 |
Use the device tabs and filter button to find the device you want to manage using the command line interface (CLI). |
||
|
Step 4 |
Select the device. |
||
|
Step 5 |
In the Device Actions pane, click >_Command Line Interface. |
||
|
Step 6 |
Click the Command Line Interface tab. |
||
|
Step 7 |
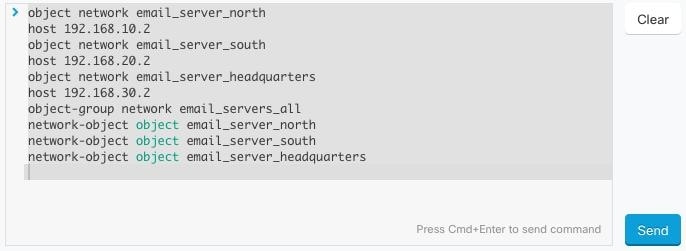
Enter your command, or commands, in the command pane and click Send. The device's response to the command(s) are displayed below in the "response pane."
|
Entering Commands in the Command Line Interface
Work with Command History
After you send a CLI command, Security Cloud Control records that command in the history pane on the Command Line Interface page. You can rerun the commands saved in the history pane or use the commands as a template:
Procedure
|
Step 1 |
In the left pane, click page. |
||
|
Step 2 |
Click the Devices tab to locate the device. |
||
|
Step 3 |
Click the appropriate device type tab. |
||
|
Step 4 |
Click >_Command Line Interface. |
||
|
Step 5 |
Click the clock icon |
||
|
Step 6 |
Select the command in the history pane that you want to modify or resend. |
||
|
Step 7 |
Reuse the command as it is or edit it in the command pane and click Send. Security Cloud Control displays the results of the command in the response pane.
|
 to expand the history pane if it is not already expanded.
to expand the history pane if it is not already expanded.





 to see what macros already exist.
to see what macros already exist.
 .
.
 . The command is now the basis for a new CLI macro.
. The command is now the basis for a new CLI macro.



 in the CLI macro label.
in the CLI macro label.
 .
.
 . The devices affected by these changes show the status "Not Synced" in the Devices and
. The devices affected by these changes show the status "Not Synced" in the Devices and  on the details pane. Review any warnings and click
on the details pane. Review any warnings and click  in the navigation bar to view the results of the bulk deploy.
in the navigation bar to view the results of the bulk deploy.




 Feedback
Feedback