Controlling Encrypted Traffic with Network-Based Conditions
License: Any
SSL rules within SSL policies exert granular control over encrypted traffic logging and handling. Network-based conditions allow you to manage which encrypted traffic can traverse your network, using one or more of the following criteria:
-
source and destination security zones
-
source and destination IP addresses or geographical locations
-
source and destination port
You can combine network-based conditions with each other and with other types of conditions to create an SSL rule. These SSL rules can be simple or complex, matching and inspecting traffic using multiple conditions. For detailed information on SSL rules, see Getting Started with SSL Rules.
Controlling Encrypted Traffic by Network Zone
License: Any
Zone conditions in SSL rules allow you to control encrypted traffic by its source and destination security zones.
A security zone is a grouping of one or more interfaces. An option you choose during a device’s initial setup, called its detection mode , determines how the ASA FirePOWER module initially configures the device’s interfaces, and whether those interfaces belong to a security zone.
As a simple example, when you register a device with an Inline detection mode, the ASA FirePOWER module creates two zones: Internal and External, and assigns the first pair of interfaces on the device to those zones. Hosts connected to the network on the Internal side represent your protected assets.
 Tip |
You are not required to group all internal (or external) interfaces into a single zone. Choose the grouping that makes sense for your deployment and security policies. For more information on creating zones, see Working with Security Zones. |
In this deployment, you may decide that although you want these hosts to have unrestricted access to the Internet, you nevertheless want to protect them by decrypting and inspecting incoming encrypted traffic.
To accomplish this with SSL inspection, configure an SSL rule with a zone condition where the Destination Zone is set to Internal. This simple SSL rule matches traffic that leaves the device from any interface in the Internal zone.
If you want to build a more complex rule, you can add a maximum of 50 zones to each of the Sources Zones and Destination Zones in a single zone condition:
-
To match encrypted traffic leaving the device from an interface in the zone, add that zone to the Destination Zones.
Because devices deployed passively do not transmit traffic, you cannot use a zone comprised of passive interfaces in a Destination Zone condition.
-
To match encrypted traffic entering the device from an interface in the zone, add that zone to the Source Zones.
If you add both source and destination zone conditions to a rule, matching traffic must originate from one of the specified source zones and egress through one of the destination zones.
Note that just as all interfaces in a zone must be of the same type (all inline, all passive, all switched, or all routed), all zones used in a zone condition for an SSL rule must be of the same type. That is, you cannot write a single rule that matches encrypted traffic to or from zones of different types.
Warning icons indicate invalid configurations, such as zones that contain no interfaces. For details, hover your pointer over the icon.
To control encrypted traffic by zone:
Procedure
| Step 1 |
In the SSL policy where you want to control encrypted traffic by zone, create a new SSL rule or edit an existing rule. For detailed instructions, see Getting Started with SSL Rules. |
| Step 2 |
In the SSL rule editor, select the Zones tab. The Zones tab appears. |
| Step 3 |
Find and select the zones you want to add from the Available Zones. To search for zones to add, click the Search by name prompt above the Available Zones list, then type a zone name. The list updates as you type to display matching zones. Click to select a zone. To select multiple zones, use the Shift and Ctrl keys, or right-click and then select Select All. |
| Step 4 |
Click Add to Source or Add to Destination to add the selected zones to the appropriate list. You can also drag and drop selected zones. |
| Step 5 |
Save or continue editing the rule. You must apply the access control policy associated with the SSL policy for your changes to take effect; see Deploying Configuration Changes. |
Controlling Encrypted Traffic by Network or Geographical Location
License: Any
Network conditions in SSL rules allow you to control and decrypt encrypted traffic by its source and destination IP address. You can either:
-
explicitly specify the source and destination IP addresses for the encrypted traffic you want to control, or
-
use the geolocation feature, which associates IP addresses with geographical locations, to control encrypted traffic based on its source or destination country or continent
When you build a network-based SSL rule condition, you can manually specify IP address and geographical locations. Alternately, you can configure network conditions with network and geolocation objects , which are reusable and associate a name with one or more IP addresses, address blocks, countries, continents, and so on.
 Tip |
After you create a network or geolocation object, you can use it not only to build SSL rules, but also to represent IP addresses in various other places in the module interface. You can create these objects using the object manager; you can also create network objects on-the-fly while you are configuring SSL rules. For more information, see Managing Reusable Objects. |
Note that if you want to write rules to control traffic by geographical location, to ensure you are using up-to-date geolocation data to filter your traffic, Cisco strongly recommends you regularly update the geolocation database (GeoDB) on your ASA FirePOWER module; see Updating the Geolocation Database.
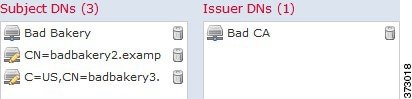
The following graphic shows the network condition for an SSL rule that blocks encrypted connections originating from your
internal network and attempting to access resources either in the Cayman Islands or an offshore holding corporation server
at 182.16.0.3. 
The example manually specifies the offshore holding corporation’s server IP address, and uses a ASA FirePOWER module-provided Cayman Islands geolocation object to represent Cayman Island IP addresses.
You can add a maximum of 50 items to each of the Source Networks and Destination Networks in a single network condition, and you can mix network and geolocation-based configurations:
-
To match encrypted traffic from an IP address or geographical location, configure the Source Networks.
-
To match encrypted traffic to an IP address or geographical location, configure the Destination Networks.
If you add both source and destination network conditions to a rule, matching encrypted traffic must originate from one of the specified IP addresses and be destined for one of the destination IP addresses.
When building a network condition, warning icons indicate invalid configurations. For details, hover your pointer over the icon.
To control traffic by network or geographical location:
Access: Admin/Access Admin/Network Admin
Procedure
| Step 1 |
In the SSL policy where you want to control encrypted traffic by network, create a new SSL rule or edit an existing rule. For detailed instructions, see Understanding and Creating SSL Rules. |
| Step 2 |
In the SSL rule editor, select the Networks tab. The Networks tab appears. |
| Step 3 |
Find and select the networks you want to add from the Available Networks, as follows:
To select an object, click it. To select multiple objects, use the Shift and Ctrl keys, or right-click and then select Select All. |
| Step 4 |
Click Add to Source or Add to Destination to add the selected objects to the appropriate list. You can also drag and drop selected objects. |
| Step 5 |
Add any source or destination IP addresses or address blocks that you want to specify manually. Click the Enter an IP address prompt below the Source Networks or Destination Networks list; then type an IP address or address block and click Add. |
| Step 6 |
Save or continue editing the rule. You must apply the access control policy associated with the SSL policy for your changes to take effect; see Deploying Configuration Changes. |
Controlling Encrypted Traffic by Port
License: Any
Port conditions in SSL rules allow you to control encrypted traffic by its source and destination TCP port. When you build a port-based SSL rule condition, you can manually specify TCP ports. Alternately, you can configure port conditions with port objects , which are reusable and associate a name with one or more ports.
 Tip |
After you create a port object, you can use it not only to build SSL rules, but also to represent ports in various other places in the module interface. You can create port objects either using the object manager or on-the-fly while you are configuring SSL rules. For more information, see Working with Port Objects. |
You can add a maximum of 50 items to each of the Selected Source Ports and Selected Destination Ports lists in a single network condition:
-
To match encrypted traffic from a TCP port, configure the Selected Source Ports.
-
To match encrypted traffic to a TCP port, configure the Selected Destination Ports.
-
To match encrypted traffic both originating from TCP Selected Source Ports and destined for TCP Selected Destination Ports, configure both.
You can only configure the Selected Source Ports and Selected Destination Ports lists with TCP ports. Port objects containing non-TCP ports are greyed out in the Available Ports list.
When building a port condition, warning icons indicate invalid configurations. For example, you can use the object manager to edit in-use port objects so that the rules that use those object groups become invalid. For details, hover your pointer over the icon.
To control traffic by port:
Procedure
| Step 1 |
In the SSL policy where you want to control encrypted traffic by TCP port, create a new SSL rule or edit an existing rule. For detailed instructions, see Understanding and Creating SSL Rules. |
| Step 2 |
In the SSL rule editor, select the Ports tab. The Ports tab appears. |
| Step 3 |
Find and select the TCP ports you want to add from the Available Ports, as follows:
To select a TCP-based port object, click it. To select multiple TCP-based port objects, use the Shift and Ctrl keys, or right-click and then select Select All. If the object includes non-TCP-based ports, you cannot add it to your port condition. |
| Step 4 |
Click Add to Source or Add to Destination to add the selected objects to the appropriate list. You can also drag and drop selected objects. |
| Step 5 |
Enter a Port under the Selected Source Ports or Selected Destination Ports list to manually specify source or destination ports. You can specify a single port with a value from 0 to 65535. |
| Step 6 |
Click Add. Note that the ASA FirePOWER module will not add a port to a rule condition that results in an invalid configuration. |
| Step 7 |
Save or continue editing the rule. You must apply the access control policy associated with the SSL policy for your changes to take effect; see Deploying Configuration Changes. |

 ) above the Available Networks list; see
) above the Available Networks list; see 
 ) next to an application.
) next to an application.

 ) next to the SSL policy you want to configure.
) next to the SSL policy you want to configure.


 6>
6>
 Feedback
Feedback