|
Certificate(s) will be used for
|
Choose the service for which you are going to use the certificate:
Cisco ISE Identity Certificates
-
Multi-Use: Used for multiple services (Admin, EAP-TLS Authentication, pxGrid). Multi-use certificates use both client and server key
usages. The certificate template on the signing CA is often called a Computer or Machine certificate template. This template
has the following properties:
-
Admin: Used for server authentication (to secure communication with the Admin portal and between ISE-PIC nodes in a deployment). The certificate template on the signing CA is often called a Web Server certificate template. This
template has the following properties:
-
pxGrid: Used for both client and server authentication (to secure communication between the pxGrid client and server). The certificate
template on the signing CA is often called a Computer or Machine certificate template. This template has the following properties:
-
SAML: Server certificate used to secure communication with the SAML Identity Provider (IdP). A certificate designated for SAML
use cannot be used for any other service such as Admin, EAP authentication, and so on.
| Note
|
We recommend that you do not use a certificate that contains the value of 2.5.29.37.0 for the Any Purpose object identifier
in the Extended Key Usage attribute. If you use a certificate that contains the value of 2.5.29.37.0 for the Any Purpose object
identifier in the Extended Key Usage attribute, the certificate is considered invalid and the following error message is displayed:
source=local ; type=fatal ; message="unsupported certificate"
|
Cisco ISE Certificate Authority Certificates
-
ISE Root CA: (Applicable only for the internal CA service ) Used for regenerating the entire internal CA certificate chain including
the root CA on the Primary PAN and subordinate CAs on the PSNs.
-
ISE Intermediate CA: (Applicable only for the internal CA service when ISE-PIC acts as an intermediate CA of an external PKI) Used to generate an intermediate CA certificate on the Primary PAN and subordinate
CA certificates on the PSNs. The certificate template on the signing CA is often called a Subordinate Certificate Authority.
This template has the following properties:
-
Basic Constraints: Critical, Is a Certificate Authority
-
Key Usage: Certificate Signing, Digital Signature
-
Extended Key Usage: OCSP Signing (1.3.6.1.5.5.7.3.9)
-
Renew ISE OCSP Responder Certificates: (Applicable only for the internal CA service) Used to renew the ISE-PIC OCSP responder certificate for the entire deployment (and is not a certificate signing request). For security reasons, we
recommend that you renew the ISE-PIC OCSP responder certificates every six months.
|
|
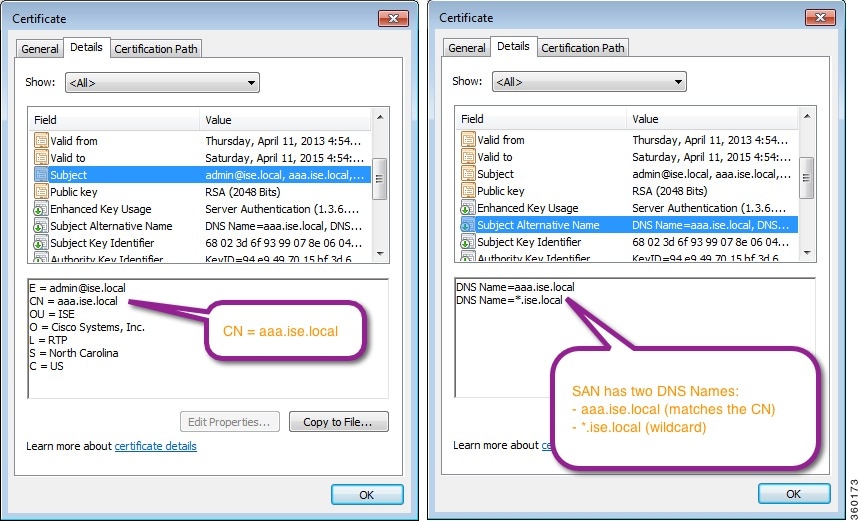
Allow Wildcard Certificates
|
Check this check box to use a wildcard character (*) in the CN and/or the DNS name in the SAN field of the certificate. If
you check this check box, all the nodes in the deployment are selected automatically. You must use the asterisk (*) wildcard
character in the left-most label position. If you use wildcard certificates, we recommend that you partition your domain space
for greater security. For example, instead of *.example.com, you can partition it as *.amer.example.com. If you do not partition
your domain, it might lead to security issues.
|
|
Generate CSRs for these Nodes
|
Check the check boxes next to the nodes for which you want to generate the certificate. To generate a CSR for select nodes
in the deployment, you must uncheck the Allow Wildcard Certificates option.
|
|
Common Name (CN)
|
By default, the common name is the FQDN of the ISE-PIC node for which you are generating the certificate signing request. $FQDN$ denotes the FQDN of the ISE-PIC node. When you generate certificate signing requests for multiple nodes in the deployment, the Common Name field in the certificate
signing requests is replaced with the FQDN of the respective ISE nodes.
|
|
Organizational Unit (OU)
|
Organizational Unit name. For example, Engineering.
|
|
Organization (O)
|
Organization name. For example, Cisco.
|
|
City (L)
|
(Do not abbreviate) City name. For example, San Jose.
|
|
State (ST)
|
(Do not abbreviate) State name. For example, California.
|
|
Country (C)
|
Country name. You must enter the two-letter ISO country code. For example, US.
|
|
Subject Alternative Name (SAN)
|
An IP address, DNS name, Uniform Resource Identifier (URI), or Directory Name that is associated with the certificate.
-
DNS Name: If you choose the DNS name, enter the fully qualified domain name of the ISE-PIC node. If you have enabled the Allow Wildcard Certificates option, specify the wildcard notation (an asterisk and a period
before the domain name). For example, *.amer.example.com.
-
IP Address: IP address of the ISE-PIC node to be associated with the certificate.
-
Uniform Resource Identifier: A URI that you want to associate with the certificate.
-
Directory Name: A string representation of distinguished name(s) (DNs) defined per RFC 2253. Use a comma (,) to separate the DNs. For “dnQualifier”
RDN, escape the comma and use backslash-comma “\,” as separator. For example, CN=AAA,dnQualifier=O=Example\,DC=COM,C=IL
|
|
Key Type
|
Specify the algorithm to be used for creating the public key: RSA or ECDSA.
|
|
Key Length
|
Specify the bit size for the public key.
The following options are available for RSA:
The following options are available for ECDSA:
| Note
|
RSA and ECDSA public keys might have different key length for the same security level.
|
Choose 2048 or greater if you plan to get a public CA-signed certificate.
|
|
Digest to Sign With
|
Choose one of the following hashing algorithm: SHA-1 or SHA-256.
|
|
Certificate Policies
|
Enter the certificate policy OID or list of OIDs that the certificate should conform to. Use comma or space to separate the
OIDs.
|

 Feedback
Feedback