Cisco Nexus 1000V for KVM Security Configuration Guide, Release 5.x
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- November 21, 2014
Chapter: Configuring AAA
Configuring AAA
This chapter contains the following sections:
- Information about AAA
- Prerequisites for AAA
- Guidelines and Limitations
- AAA Default Settings
- Configuring AAA
- Verifying the AAA Configuration
- Configuration Examples for AAA
- Feature History for AAA
Information about AAA
AAA Security Services
Based on a user ID and password combination, authentication, authorization, and accounting (AAA) is used to authenticate and authorize users. A key secures communication with AAA servers.
In many circumstances, AAA uses protocols such as RADIUS or TACACS+ to administer its security functions. If your router or access server is acting as a network access server, AAA is the means through which you establish communication between your network access server and your RADIUS or TACACS+ security server.
Although AAA is the primary (and recommended) method for access control, additional features for simple access control are available outside the scope of AAA, such as local username authentication, line password authentication, and enable password authentication. However, these features do not provide the same degree of access control that is possible by using AAA.
Separate AAA configurations are made for the following services:
-
User Telnet or Secure Shell (SSH) login authentication
-
Console login authentication
-
User management session accounting
The following table provides the authentication commands:
|
AAA Service Configuration Option |
Related Command |
|---|---|
|
Telnet or SSH login |
aaa authentication login default |
|
Console login |
aaa authentication login console |
Authentication
Authentication provides the method of identifying users, including login and password dialog, challenge and response, messaging support, and, depending on the security protocol that you select, encryption. Authentication is the way a user is identified prior to being allowed access to the network and network services. You configure AAA authentication by defining a named list of authentication methods and then applying that list to various interfaces.
Authentication is accomplished as follows:
|
Authentication Method |
Description |
|---|---|
|
Local database |
Authenticates the following with a local lookup database of usernames or passwords: |
|
Remote RADIUS or TACACS+ server |
Authenticates the following with a local lookup database of usernames or passwords: |
|
None |
Authenticates the following with only a username: |
The following figure shows a flowchart of the authentication process.
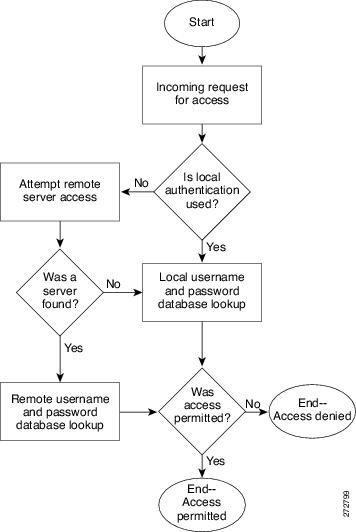
 Note | This diagram is applicable only to username password SSH authentication. It does not apply to public key SSH authentication. All username password SSH authentication goes through AAA. |
Authorization
Authorization restricts the actions that a user is allowed to perform. It provides the method for remote access control, including one-time authorization or authorization for each service, per-user account list and profile, user group support, and support of IP, IPX, ARA, and Telnet.
Remote security servers, such as RADIUS and TACACS+, authorize users for specific rights by associating attribute-value (AV) pairs, which define those rights, with the appropriate user. AAA authorization works by assembling a set of attributes that describe what the user is authorized to perform. These attributes are compared with the information contained in a database for a given user, and the result is returned to AAA to determine the user’s actual capabilities and restrictions.
Accounting
Accounting provides the method for collecting and sending security server information used for billing, auditing, and reporting, such as user identities, start and stop times, executed commands (such as PPP), number of packets, and number of bytes. Accounting enables you to track the services that users are accessing, as well as the amount of network resources that they are consuming.
Accounting tracks and maintains a log of every SVS management session. You can use this information to generate reports for troubleshooting and auditing purposes. You can store accounting logs locally or send them to remote AAA servers.
AAA Server Groups
Remote AAA server groups can provide failovers if one remote AAA server fails to respond, which means that if the first server in the group fails, the next server in the group is tried until a server responds. Multiple server groups can provide failovers for each other in this same way.
If all remote server groups fail, the local database is used for authentication.
Prerequisites for AAA
Guidelines and Limitations
The Cisco Nexus 1000V does not support usernames that have all numeric characters and does not create local usernames that have all numeric characters. If a username that has all numeric characters already exists on an AAA server and is entered during login, the Cisco Nexus 1000V does not authenticate the user.
AAA Default Settings
Parameters |
Default |
|---|---|
Console authentication method |
local |
Default authentication method |
local |
Login authentication failure messages |
Disabled |
Configuring AAA
Configuring a Login Authentication Method
Log in to the CLI in EXEC mode.
If authenticate with TACACS+ server groups, you must have already added the groups.
1. switch# configure terminal
2. switch(config)# aaa authentication login {console | default} {group group-list [none] | local | none}
3. switch(config)# exit
4. (Optional) switch# show aaa authentication
5. (Optional) switch# copy running-config startup-config
DETAILED STEPS
The following example shows how to configure a local authentication method:
switch# configure terminal
switch(config)# aaa authentication login console group tacgroup
switch(config)# exit
switch# show aaa authentication
default: group tacgroup
console: group tacgroup
switch# copy running-config startup-config
switch#
switch# configure terminal switch(config)# aaa authentication login default group tacacs switch(config)# aaa authentication login console group tacacs
Enabling Login Authentication Failure Messages
You can enable the login authentication failure message to display if the remote AAA servers do not respond.
The following is the login authentication failure message:
Remote AAA servers unreachable; local authentication done. Remote AAA servers unreachable; local authentication failed.
Log in to the CLI in EXEC mode.
1. switch# configure terminal
2. switch(config)# aaa authentication login error-enable
3. switch(config)# exit
4. (Optional) switch# show aaa authentication login error-enable
5. (Optional) switch# copy running-config startup-config
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | switch# configure terminal |
Enters global configuration mode. |
| Step 2 | switch(config)# aaa authentication login error-enable |
Enables the login authentication failure message. The default is disabled. |
| Step 3 | switch(config)# exit |
Exits global configuration mode and returns you to EXEC mode. |
| Step 4 | switch# show aaa authentication login error-enable | (Optional)
Displays the login failure message configuration. |
| Step 5 | switch# copy running-config startup-config | (Optional)
Copies the running configuration to the startup configuration. |
The following example shows how to enable the login authentication failure message:
switch# configure terminal switch(config)# aaa authentication login error-enable switch(config)# exit switch# show aaa authentication login error-enable enabled
Verifying the AAA Configuration
Use one of the following commands to verify the configuration:
|
Command |
Purpose |
|---|---|
|
show aaa authentication [login {error-enable | mschap}] |
Displays AAA authentication information. |
|
show aaa groups |
Displays the AAA server group configuration. |
|
show running-config aaa [all] |
Displays the AAA configuration in the running configuration. |
|
show startup-config aaa |
Displays the AAA configuration in the startup configuration. |
Example 1: show aaa authentication
switch# show aaa authentication login error-enable disabled switch#
Example 2: show aaa groups
switch# show aaa groups radius switch#
Example 3: show running config aaa
switch# show running-config aaa all !Time: Fri Nov 15 11:22:13 2013 version 5.2(1)SK1(2.1) aaa authentication login default local aaa authorization ssh-publickey default local aaa authorization ssh-certificate default local aaa accounting default local aaa user default-role aaa authentication login default fallback error local aaa authentication login console fallback error local no aaa authentication login error-enable no aaa authentication login mschap enable no aaa authentication login mschapv2 enable no aaa authentication login chap enable no aaa authentication login ascii-authentication no radius-server directed-request switch#
Example 4: show startup-config aaa
switch# show startup-config aaa !Command: show startup-config aaa !Time: Fri Nov 15 11:19:57 2013 !Startup config saved at: Tue Jun 25 05:23:10 2013 version 5.2(1)SK1(2.1) switch#
Configuration Examples for AAA
The following example configures AAA:
switch# show aaa authentication login default group tacacs switch# show aaa authentication login console group tacacs
Feature History for AAA
|
Feature Name |
Releases |
Feature Information |
|---|---|---|
|
AAA |
Release 5.2(1)SK1(2.1) |
This feature was introduced. |
 Feedback
Feedback