Restrictions for IPv4 Access Control Lists
General Network Security
The following are restrictions for configuring network security with ACLs:
-
Not all commands that accept a numbered ACL accept a named ACL. ACLs for packet filters and route filters on interfaces can use a name. VLAN maps also accept a name.
-
A standard ACL and an extended ACL cannot have the same name.
-
Though visible in the command-line help strings, appletalk is not supported as a matching condition for the deny and permit MAC access-list configuration mode commands.
-
ACL wildcard is not supported in downstream client policy.
-
ACLs cannot be configured on management ports.
-
When you apply a scale ACL to an interface that does not program TCAM for a protocol and the ACLs that have been unloaded, it can impact the existing normal movement of traffic for other protocols. The restriction is applicable to IPv6 and MAC address traffic.
-
Router ACL is enforced on all types of traffic, including CPU generated traffic.
-
ACL logging in the egress direction are not supported for packets that are generated from the control plane of the device.
-
Time-to-live (TTL) classification is not supported on ACLs.
-
If a downloadable ACL contains any type of duplicate entries, the entries are not auto merged. As a result, the 802.1X session authorization fails. Ensure that the downloadable ACL is optimized without any duplicate entries, for example port-based and name-based entries for the same port.
-
Egress ACL lookup is not supported for injected traffic that is forwarded by the software.
IPv4 ACL Network Interfaces
The following restrictions apply to IPv4 ACLs to network interfaces:
-
When controlling access to an interface, you can use a named or numbered ACL.
-
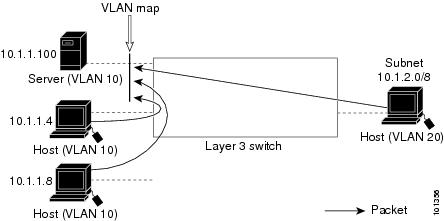
If you apply an ACL to a Layer 2 interface that is a member of a VLAN, the Layer 2 (port) ACL takes precedence over an input Layer 3 ACL applied to the VLAN interface or a VLAN map applied to the VLAN.
-
If you apply an ACL to a Layer 3 interface and routing is not enabled on the switch, the ACL only filters packets that are intended for the CPU, such as SNMP, Telnet, or web traffic.
-
If the preauth_ipv4_acl ACL is configured to filter packets, the ACL is removed after authentication.
-
You do not have to enable routing to apply ACLs to Layer 2 interfaces.
MAC ACLs on a Layer 2 Interface
After you create a MAC ACL, you can apply it to a Layer 2 interface to filter non-IP traffic coming in that interface. When you apply the MAC ACL, consider these guidelines:
-
You can apply no more than one IP access list and one MAC access list to the same Layer 2 interface. The IP access list filters only IP packets, and the MAC access list filters non-IP packets.
-
A Layer 2 interface can have only one MAC access list. If you apply a MAC access list to a Layer 2 interface that has a MAC ACL configured, the new ACL replaces the previously configured one.
 Note |
The mac access-group interface configuration command is only valid when applied to a physical Layer 2 interface. You cannot use the command on EtherChannel port channels. |
IP Access List Entry Sequence Numbering
-
This feature does not support dynamic, reflexive, or firewall access lists.
Fully Qualified Domain Name (FQDN) ACLs
-
FQDN ACLs can be used only as redirect ACLs, as part of central web authentication.
-
FQDN ACL resolution is supported on per session-based snooping only.
-
FQDN ACLs can be used only for the names in Domain Name System (DNS) response on the client session.
-
FQDN ACLs are supported on the Catalyst 9300 Series Switches that are configured as standalone, and the Catalyst 9400 Series Switches configured as dual-SUP with no SVL.
-
FQDN ACLs do not support encrypted DNS packets.
-
FQDN ACLs are not supported for IPv6.
-
FQDN ACLs do not support the Yang model.
-
FQDN ACLs are not supported with the Cisco Umbrella feature.
-
Each access control entry (ACE) can have FQDN for either source or destination entries, but not for both in the same ACE.
-
A maximum of 1000 unique policies are supported.
-
DNS over TCP is not supported.
-
DNS responses more than 512 bytes are not supported.
-
An extended ACL cannot be created with the same name as an existing FQDN ACL.
-
FQDN ACLs are not supported with Security Group access control lists (SGACL) on the same port.
-
FQDN ACLs are not supported with SPAN monitoring session on the same interface.
 Feedback
Feedback