Restrictions for Cisco TrustSec
-
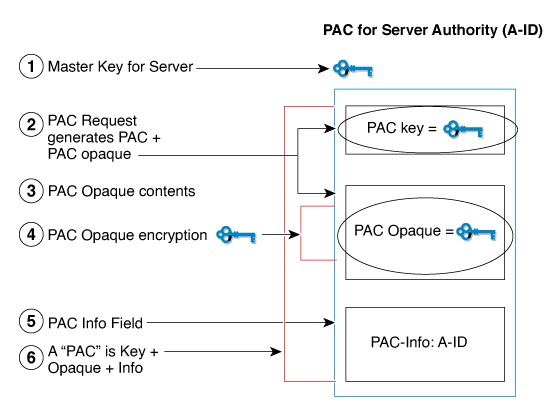
Protected access credential (PAC) provisioning fails and remains in hung state, when an invalid device ID is specified. Even after clearing the PAC, and configuring the correct device ID and password, PAC still fails.
As a workaround, in the Cisco Identity Services Engine (ISE), uncheck the Suppress Anomalous Clients option in the Administration> System> Settings> Protocols> Radius menu for PAC to work.
-
Cisco TrustSec is not supported in FIPS mode when PAC is enabled.
-
Cisco TrustSec over Radsec is not supported.
Restrictions for configuring Cisco TrustSec in PAC-less mode:
-
PAC-less mode is only supported on ISE 3.4.x and later.
-
When the device is in PAC-less mode, all servers within the server group must be configured with the PAC-Less configuration (key ). Mixing configurations, such as having one server with a PAC key configuration and another with PAC-less configuration, is not allowed.
-
In PAC-less mode, the Cisco TrustSec credential command with the device ID is the only parameterneeded to download environment data. However, SGACL requests do not require any credential information.
-
Device in PAC-Less mode can be identified by “cts-pac-less” attribute by radius debug.
-
IPv6 support for PAC-less is not available.
-
Multi-ISE support is limited to up to 2 ISEs.

 Feedback
Feedback