透過內部報告模式對Catalyst SD-WAN Manager上的許可證同步進行故障排除
下載選項
無偏見用語
本產品的文件集力求使用無偏見用語。針對本文件集的目的,無偏見係定義為未根據年齡、身心障礙、性別、種族身分、民族身分、性別傾向、社會經濟地位及交織性表示歧視的用語。由於本產品軟體使用者介面中硬式編碼的語言、根據 RFP 文件使用的語言,或引用第三方產品的語言,因此本文件中可能會出現例外狀況。深入瞭解思科如何使用包容性用語。
關於此翻譯
思科已使用電腦和人工技術翻譯本文件,讓全世界的使用者能夠以自己的語言理解支援內容。請注意,即使是最佳機器翻譯,也不如專業譯者翻譯的內容準確。Cisco Systems, Inc. 對這些翻譯的準確度概不負責,並建議一律查看原始英文文件(提供連結)。
簡介
本文檔介紹如何對透過內部報告模式在Catalyst SD-WAN Manager上同步許可證時遇到錯誤進行故障排除。
需求
對於Catalyst SD-WAN Manager未直接連線到網際網路的情況,使用代理伺服器可以提供對基於網際網路的服務(例如Cisco SSM)或本地內部SSM的訪問。
最低版本:Catalyst SD-WAN Manager版本20.9.1
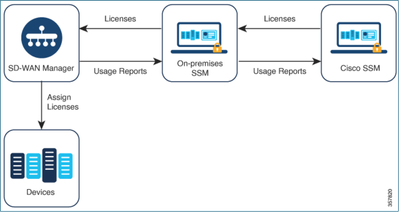
思科智慧軟體管理器內部部署(SSM on-prem)是思科智慧許可解決方案,使您能夠從本地伺服器管理許可證,而無需直接連線到思科SSM。該解決方案包括設定思科SSM內部許可證伺服器,該伺服器定期將其許可證資料庫與思科SSM同步,其功能與思科SSM類似,同時可在本地運行。
Catalyst SD-WAN Manager支援使用思科SSM內部伺服器管理許可證,使用一種稱為內部模式。內部模式對於使用思科SSM內部模式的組織非常有用,因為這種模式支援不允許網路裝置透過直接網際網路連線與思科SSM通訊的嚴格安全策略。
在內部模式下運行時,Catalyst SD-WAN Manager每24小時將許可證資訊與Cisco SSM內部許可證伺服器同步。在此同步過程中,Catalyst SD-WAN Manager接收對可用許可證的任何更新,並將許可證使用情況報告傳送到思科SSM內部許可證伺服器。您可以隨時同步許可證。
使用Cisco Smart Software Manager的優勢
如果組織的安全策略或其他情況要求Catalyst SD-WAN Manager不能連線到網際網路,則可以使用以下兩個選項來管理智慧許可證使用策略的許可證:
- 使用離線模式,這需要在Catalyst SD-WAN Manager和Cisco SSM之間手動傳輸檔案。
- 使用可透過到Catalyst SD-WAN Manager的本地連線訪問的Cisco SSM內部伺服器。
這兩種方法都解決了在Cisco SSM和Catalyst SD-WAN Manager之間傳輸許可證資訊的需要。只要可以使用預置模式,此模式便具有顯著優勢,可降低在Catalyst SD-WAN Manager和Cisco SSM之間手動傳輸檔案的維護開銷(這是離線模式所必需的)。
錯誤
從Catalyst SD-WAN Manager GUI同步智慧憑證時,我們會收到以下錯誤:
Failed to authenticate Smart Account credentials.: Failed to authenticate user - 'admin'. {"error":"invalid_client","error_message":"Grant not found. Ensure that the given grant details are correct."}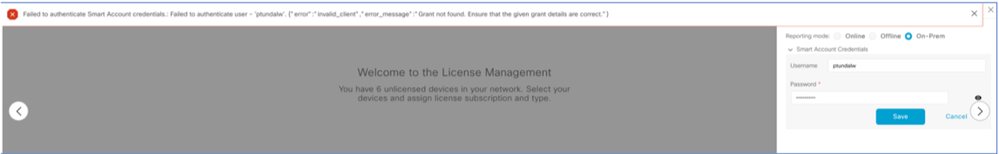
疑難排解方法
- vManage必須位於代碼20.9.1或更高版本上。
- 在Catalyst SD-WAN Manager許可證管理部分放置智慧帳戶憑證時,檢查Catalyst SD-WAN Manager (vmanage-server.logs)上的日誌。
- 確保內部SSM團隊共用的客戶端ID和金鑰正確。
- CSSM伺服器IP的vManage上的TCPDUMP
- 驗證Catalyst SD-WAN Manager上的DNS配置是否正確且能夠ping通cloudsso.cisco.com
- 讓內部SSM團隊參與,並請求SSM團隊在內部伺服器端進行調試。
Catalyst SD-WAN Manager IP:10.66.76.81/192.168.10.1
CSSM伺服器IP:10.106.66.55
SSM伺服器IP的vManage上的TCPDump:
um8_vManage# tcpdump vpn 0 interface eth0 options "host 10.106.66.55 -nn -vv"
tcpdump -p -i eth0 -s 128 host 10.106.66.55 -nn -vv in VPN 0
tcpdump: listening on eth0, link-type EN10MB (Ethernet), capture size 128 bytes
12:15:06.407513 IP (tos 0x0, ttl 64, id 24618, offset 0, flags [DF], proto TCP (6), length 52)
192.168.10.1.57886 > 10.106.66.55.8443: Flags [S], cksum 0xfadb (incorrect -> 0xdf91), seq 746386211, win 29200, options [mss 1460,nop,nop,sackOK,nop,wscale 7], length 0
12:15:06.651698 IP (tos 0x20, ttl 44, id 0, offset 0, flags [DF], proto TCP (6), length 52)
10.106.66.55.8443 > 192.168.10.1.57886: Flags [S.], cksum 0x1b34 (correct), seq 2758352947, ack 746386212, win 29200, options [mss 1380,nop,nop,sackOK,nop,wscale 7], length 0
12:15:06.651768 IP (tos 0x0, ttl 64, id 24619, offset 0, flags [DF], proto TCP (6), length 40)
192.168.10.1.57886 > 10.106.66.55.8443: Flags [.], cksum 0xfacf (incorrect -> 0xcce1), seq 1, ack 1, win 229, length 0
12:15:06.654592 IP (tos 0x0, ttl 64, id 24620, offset 0, flags [DF], proto TCP (6), length 212)
192.168.10.1.57886 > 10.106.66.55.8443: Flags [P.], seq 1:173, ack 1, win 229, length 172
12:15:06.899695 IP (tos 0x0, ttl 41, id 44470, offset 0, flags [DF], proto TCP (6), length 40)
10.106.66.55.8443 > 192.168.10.1.57886: Flags [.], cksum 0xcc2d (correct), seq 1, ack 173, win 237, length 0
12:15:06.911484 IP (tos 0x0, ttl 41, id 44471, offset 0, flags [DF], proto TCP (6), length 1420)
10.106.66.55.8443 > 192.168.10.1.57886: Flags [.], seq 1:1381, ack 173, win 237, length 1380
12:15:06.911542 IP (tos 0x0, ttl 41, id 44472, offset 0, flags [DF], proto TCP (6), length 254)
10.106.66.55.8443 > 192.168.10.1.57886: Flags [P.], seq 1381:1595, ack 173, win 237, length 214
12:15:06.911573 IP (tos 0x0, ttl 64, id 24621, offset 0, flags [DF], proto TCP (6), length 40)
192.168.10.1.57886 > 10.106.66.55.8443: Flags [.], cksum 0xfacf (incorrect -> 0xc6bb), seq 173, ack 1381, win 251, length 0
12:15:06.911598 IP (tos 0x0, ttl 64, id 24622, offset 0, flags [DF], proto TCP (6), length 40)
192.168.10.1.57886 > 10.106.66.55.8443: Flags [.], cksum 0xfacf (incorrect -> 0xc5cf), seq 173, ack 1595, win 273, length 0
12:15:06.923929 IP (tos 0x0, ttl 64, id 24623, offset 0, flags [DF], proto TCP (6), length 234)
192.168.10.1.57886 > 10.106.66.55.8443: Flags [P.], seq 173:367, ack 1595, win 273, length 194
內部伺服器日誌:
[root@SSM-On-Prem log]# tail -f messages
Jan 13 11:13:36 SSM-On-Prem chronyd[1319]: Source 172.20.226.229https://172.20.226.229 replaced with 172.30.5.123https://172.30.5.123
Jan 13 11:14:09 SSM-On-Prem b09c1e3b5d81: 1:M 13 Jan 2023 11:14:09.049 * 100 changes in 300 seconds. Saving...
Jan 13 11:14:09 SSM-On-Prem b09c1e3b5d81: 1:M 13 Jan 2023 11:14:09.050 * Background saving started by pid 4617
Jan 13 11:14:09 SSM-On-Prem b09c1e3b5d81: 4617:C 13 Jan 2023 11:14:09.052 * DB saved on disk
Jan 13 11:14:09 SSM-On-Prem b09c1e3b5d81: 4617:C 13 Jan 2023 11:14:09.053 * RDB: 0 MB of memory used by copy-on-write
Jan 13 11:14:09 SSM-On-Prem b09c1e3b5d81: 1:M 13 Jan 2023 11:14:09.150 * Background saving terminated with success
Jan 13 11:14:46 SSM-On-Prem 1a1fca641d0a: Redis#exists(key) will return an Integer in redis-rb 4.3. exists? returns a boolean, you should use it instead. To opt-in to the new behavior now you can set Redis.exists_returns_integer = true. To disable this message and keep the current (boolean) behaviour of 'exists' you can set Redis.exists_returns_integer = false, but this option will be removed in 5.0. (/usr/local/lib/ruby/gems/2.6.0/gems/redis-session-store-0.11.1/lib/redis-session-store.rb:70:in `session_exists?')
Jan 13 11:14:46 SSM-On-Prem 1a1fca641d0a: [active_model_serializers] Rendered UserSerializer with ActiveModelSerializers::Adapter::Attributes (3.0ms)
Jan 13 11:14:46 SSM-On-Prem 1a1fca641d0a: method=GET path=/sessions/get_user format=json controller=SessionsController action=get_user status=200 duration=24.86 view=3.23 db=7.98 params={"controller"=>"sessions", "action"=>"get_user", "session"=>{}} session_id=[FILTERED] uid=admin time=2023-07-13T11:14:46Z http_referer=https://172.20.85.137:8443/admin/ client_ip=10.110.35.124https://10.110.35.124 user_agent=Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/10.120.0.0 Safari/537.36
Jan 13 11:14:46 SSM-On-Prem 504f06c0d581: 10.110.35.124https://10.110.35.124 - - [13/Jan/2023:11:14:46 +0000] "GET /backend/sessions/get_user HTTP/1.1" 200 271 https://172.20.85.137:8443/admin/ "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/10.120.0.0 Safari/537.36" "-"
Jan 13 11:17:01 SSM-On-Prem 504f06c0d581: 2023/07/13 11:17:01 [error] 47#47: *1576 connect() failed (111: Connection refused) while connecting to upstream, client: 10.66.76.85, server: , request: "POST /backend/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=admin&password=CiscoLab%21234567 HTTP/1.1", upstream: http://[fd00:dead:beef::5]:3000/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=admin&password=CiscoLab%21234567, host: "172.20.85.137:8443"
Jan 13 11:17:01 SSM-On-Prem 504f06c0d581: 2023/07/13 11:17:01 [warn] 47#47: *1576 upstream server temporarily disabled while connecting to upstream, client: 10.66.76.85, server: , request: "POST /backend/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=admin&password=CiscoLab%21234567 HTTP/1.1", upstream: http://[fd00:dead:beef::5]:3000/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=admin&password=CiscoLab%21234567, host: "172.20.85.137:8443"
Jan 13 11:17:01 SSM-On-Prem 1a1fca641d0a: [active_model_serializers] Rendered ActiveModel::Serializer::Null with Hash (0.09ms)
Jan 13 11:17:01 SSM-On-Prem 1a1fca641d0a: method=POST path=/oauth/token format=json controller=Doorkeeper::OauthTokensController action=create status=403 duration=4.21 view=0.53 db=1.12
Jan 13 11:17:01 SSM-On-Prem 504f06c0d581: 10.66.76.85https://10.66.76.85 - - [13/Jan/2023:11:17:01 +0000] "POST /backend/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=admin&password=CiscoLab%21234567 HTTP/1.1" 403 121 "-" "Apache-HttpClient/4.5.11 (Java/11.0.7)" "-"
Jan 13 11:17:14 SSM-On-Prem 1a1fca641d0a: [INFO] Session expiring outcome=success將智慧帳戶詳細資訊放入vManage許可證管理部分時登入vManage:
13-Jan-2023 17:29:02,775 IST INFO [um8_vManage] [SmartLicensingIntegrationManager] (default task-24) |default| user is using in On Prem mode
13-Jan-2023 17:29:02,776 IST INFO [um8_vManage] [SmartLicensingIntegrationManager] (default task-24) |default| Authenticating on-prem server
13-Jan-2023 17:29:02,780 IST INFO [um8_vManage] [AbstractSettingsManager] (default task-24) |default| Found smart licensing mode is onprem
13-Jan-2023 17:29:02,781 IST INFO [um8_vManage] [SmartLicensingUtil] (default task-24) |default| intializing client Map {clientUrl=172.20.85.137https://172.20.85.137, client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx, client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf}
13-Jan-2023 17:29:02,781 IST INFO [um8_vManage] [SmartLicensingUtil] (default task-24) |default| Getting onPrem server details
13-Jan-2023 17:29:02,793 IST INFO [um8_vManage] [RestAPIClient] (default task-24) |default| RestAPI proxy host
13-Jan-2023 17:29:02,793 IST INFO [um8_vManage] [RestAPIClient] (default task-24) |default| RestAPI proxy port
13-Jan-2023 17:29:02,798 IST INFO [um8_vManage] [SmartLicensingUtil] (default task-24) |default| URL backend/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=ptundalw&password=Carnation%2321
13-Jan-2023 17:29:02,798 IST INFO [um8_vManage] [SmartLicensingUtil] (default task-24) |default| Query Smart Account: backend/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=ptundalw&password=*******
13-Jan-2023 17:29:03,490 IST ERROR [um8_vManage] [RestAPIClient] (default task-24) |default| Failed to process POST request uri: backend/oauth/token?grant_type=password&client_id=jF6qntGFm429n2B7tlgJPNHueoyjjn8p6zAn7BhYLUhjAY5BZlTUV9Q0r_Zk7uBf&client_secret=d1b_ZV4QWs4UzB00_YYHz0Ek_qxcvywN4d2GD40LQOyKfMOV6MoKmVchUBX3GsGx&username=ptundalw&password=******* . Code: 403 Message: {"error":"invalid_client","error_message":"Grant not found. Ensure that the given grant details are correct."}
13-Jan-2023 17:29:03,491 IST ERROR [um8_vManage] [SmartLicensingUtil] (default task-24) |default| Failed to authenticate user - 'ptundalw'.
13-Jan-2023 17:29:03,491 IST ERROR [um8_vManage] [SmartLicensingIntegrationRestfulResource] (default task-24) |default| Smart Account User Authentication failed.注意:從vManage GUI同步智慧帳戶時出現錯誤403,表示伺服器理解該請求,但拒絕對其進行授權。
因應措施
- 登入Prem伺服器。
- 導覽至API Tool Kit。
- 選取「資源擁有者授權」,輸入名稱並儲存。
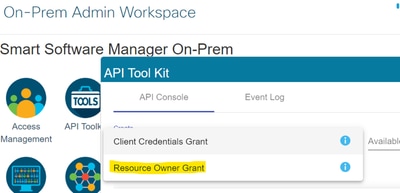
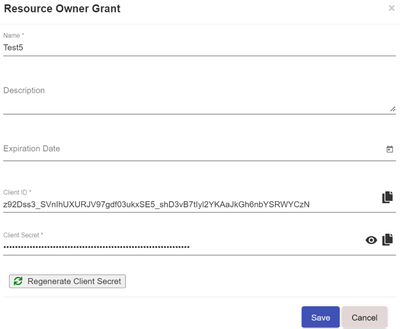
- 選擇儲存的記錄(在以前的快照中提到)並選中「客戶端ID」和「客戶端密碼」。
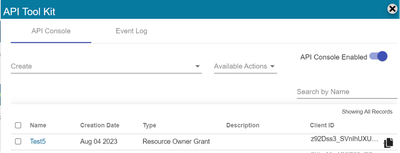
- 在Catalyst SD-WAN Manager門戶中共用並輸入共用客戶端ID和客戶端密碼。
- 轉到vManage中的「同步許可證和重新整理裝置」,並使用您登入的相同內部憑證來生成客戶端ID和客戶端密碼。
修訂記錄
| 修訂 | 發佈日期 | 意見 |
|---|---|---|
1.0 |
11-Jul-2024 |
初始版本 |
 意見
意見