- About This Guide
-
- Information about AAA
- Configuring the Local Database for AAA
- Configuring RADIUS Servers for AAA
- Configuring TACACS+ Servers for AAA
- Configuring LDAP Servers for AAA
- Configuring Windows NT Servers for AAA
- Configuring the Identity Firewall
- Configuring the ASA to Integrate with Cisco TrustSec
- Configuring Digital Certificates
- Index
ASDM Book 1: Cisco ASA Series General Operations ASDM Configuration Guide, 7.1
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- August 21, 2014
Chapter: Getting Started
- Accessing the Appliance Command-Line Interface
- Accessing the ASA Services Module Command-Line Interface
- Configuring ASDM Access for Appliances
- Configuring ASDM Access for the ASA Services Module
- Starting ASDM
- Installing an Identity Certificate for ASDM
- Factory Default Configurations
- Getting Started with the Configuration
- Using the Command Line Interface Tool in ASDM
- Applying Configuration Changes to Connections
Getting Started
This chapter describes how to get started with your ASA. This chapter includes the following sections:
- Accessing the Appliance Command-Line Interface
- Accessing the ASA Services Module Command-Line Interface
- Configuring ASDM Access for Appliances
- Configuring ASDM Access for the ASA Services Module
- Starting ASDM
- Installing an Identity Certificate for ASDM
- Factory Default Configurations
- Getting Started with the Configuration
- Using the Command Line Interface Tool in ASDM
- Applying Configuration Changes to Connections
Accessing the Appliance Command-Line Interface
In some cases, you may need to use the CLI to configure basic settings for ASDM access. See the “Configuring ASDM Access for Appliances” section to determine if you need to use the CLI.
For initial configuration, access the CLI directly from the console port. Later, you can configure remote access using Telnet or SSH according to Chapter45, “Configuring Management Access” If your system is already in multiple context mode, then accessing the console port places you in the system execution space. See “Configuring Multiple Context Mode,” for more information about multiple context mode.
Detailed Steps
Step 1![]() Connect a PC to the console port using the provided console cable, and connect to the console using a terminal emulator set for 9600 baud, 8 data bits, no parity, 1 stop bit, no flow control.
Connect a PC to the console port using the provided console cable, and connect to the console using a terminal emulator set for 9600 baud, 8 data bits, no parity, 1 stop bit, no flow control.
See the hardware guide for your ASA for more information about the console cable.
Step 2![]() Press the Enter key to see the following prompt:
Press the Enter key to see the following prompt:
This prompt indicates that you are in user EXEC mode. Only basic commands are available from user EXEC mode.
Step 3![]() To access privileged EXEC mode, enter the following command:
To access privileged EXEC mode, enter the following command:
All non-configuration commands are available in privileged EXEC mode. You can also enter configuration mode from privileged EXEC mode.
Step 4![]() Enter the enable password at the prompt.
Enter the enable password at the prompt.
By default, the password is blank, and you can press the Enter key to continue. See the “Configuring the Hostname, Domain Name, and Passwords” section to change the enable password.
To exit privileged mode, enter the disable , exit , or quit command.
Step 5![]() To access global configuration mode, enter the following command:
To access global configuration mode, enter the following command:
The prompt changes to the following:
You can begin to configure the ASA from global configuration mode. To exit global configuration mode, enter the exit , quit , or end command.
Accessing the ASA Services Module Command-Line Interface
For initial configuration, access the command-line interface by connecting to the switch (either to the console port or remotely using Telnet or SSH) and then connecting to the ASASM. The ASASM does not include a factory default configuration, so you must perform some configuration at the CLI before you can access it using ASDM. This section describes how to access the ASASM CLI, and includes the following sections:
- Logging Into the ASA Services Module
- Logging Out of a Console Session
- Logging Out of a Telnet Session
Logging Into the ASA Services Module
For initial configuration, access the command-line interface by connecting to the switch (either to the switch console port or remotely using Telnet or SSH) and then connecting to the ASASM.
If your system is already in multiple context mode, then accessing the ASASM from the switch places you in the system execution space. See “Configuring Multiple Context Mode,” for more information about multiple context mode.
Later, you can configure remote access directly to the ASASM using Telnet or SSH according to the “Configuring ASA Access for ASDM, Telnet, or SSH” section.
Information About Connection Methods
From the switch CLI, you can use two methods to connect to the ASASM:
- Virtual console connection—Using the service-module session command, you create a virtual console connection to the ASASM, with all the benefits and limitations of an actual console connection.
–![]() The connection is persistent across reloads and does not time out.
The connection is persistent across reloads and does not time out.
–![]() You can stay connected through ASASM reloads and view startup messages.
You can stay connected through ASASM reloads and view startup messages.
–![]() You can access ROMMON if the ASASM cannot load the image.
You can access ROMMON if the ASASM cannot load the image.
–![]() No initial password configuration is required.
No initial password configuration is required.
–![]() The connection is slow (9600 baud).
The connection is slow (9600 baud).
–![]() You can only have one console connection active at a time.
You can only have one console connection active at a time.
–![]() You cannot use this command in conjunction with a terminal server where Ctrl-Shift-6 , x is the escape sequence to return to the terminal server prompt. Ctrl-Shift-6 , x is also the sequence to escape the ASASM console and return to the switch prompt. Therefore, if you try to exit the ASASM console in this situation, you instead exit all the way to the terminal server prompt. If you reconnect the terminal server to the switch, the ASASM console session is still active; you can never exit to the switch prompt. You must use a direct serial connection to return the console to the switch prompt. In this case, either change the terminal server or switch escape character in Cisco IOS, or use the Telnet session command instead.
You cannot use this command in conjunction with a terminal server where Ctrl-Shift-6 , x is the escape sequence to return to the terminal server prompt. Ctrl-Shift-6 , x is also the sequence to escape the ASASM console and return to the switch prompt. Therefore, if you try to exit the ASASM console in this situation, you instead exit all the way to the terminal server prompt. If you reconnect the terminal server to the switch, the ASASM console session is still active; you can never exit to the switch prompt. You must use a direct serial connection to return the console to the switch prompt. In this case, either change the terminal server or switch escape character in Cisco IOS, or use the Telnet session command instead.

Note Because of the persistence of the console connection, if you do not properly log out of the ASASM, the connection may exist longer than intended. If someone else wants to log in, they will need to kill the existing connection. See the “Logging Out of a Console Session” section for more information.

Note You cannot connect using this method for a new ASASM; this method requires you to configure a Telnet login password on the ASASM (there is no default password). After you set a password using the passwd command, you can use this method.
–![]() You can have multiple sessions to the ASASM at the same time.
You can have multiple sessions to the ASASM at the same time.
–![]() The Telnet session is a fast connection.
The Telnet session is a fast connection.
–![]() The Telnet session is terminated when the ASASM reloads, and can time out.
The Telnet session is terminated when the ASASM reloads, and can time out.
–![]() You cannot access the ASASM until it completely loads; you cannot access ROMMON.
You cannot access the ASASM until it completely loads; you cannot access ROMMON.
–![]() You must first set a Telnet login password; there is no default password.
You must first set a Telnet login password; there is no default password.
Logging In
Perform the following steps to log into the ASASM and access global configuration mode.
Detailed Steps
|
|
|
|
|---|---|---|
(Available for initial access.) service-module session [ switch { 1 | 2 }] slot number |
From the switch CLI, enter this command to gain console access to the ASASM. For a switch in a VSS, enter the switch argument. To view the module slot numbers, enter the show module command at the switch prompt. |
|
(Available after you configure a login password.) You are prompted for the login password: |
From the switch CLI, enter this command to Telnet to the ASASM over the backplane. For a switch in a VSS, enter the switch argument. Note The session slot processor 0 command, which is supported on other services modules, is not supported on the ASASM; the ASASM does not have a processor 0. To view the module slot numbers, enter the show module command at the switch prompt. Enter the login password to the ASASM. Set the password using the passwd command. 9.1(1): The default password is “cisco.” 9.1(2) and later: There is no default password. |
|
|
|
Accesses privileged EXEC mode, which is the highest privilege level. Enter the enable password at the prompt. By default, the password is blank. To change the enable password, see the “Configuring the Hostname, Domain Name, and Passwords” section. To exit privileged EXEC mode, enter the disable , exit , or quit command. |
|
|
|
Accesses global configuration mode. To exit global configuration mode, enter the disable , exit , or quit command. |
|
Logging Out of a Console Session
Logging Out
If you do not log out of the ASASM, the console connection persists; there is no timeout. To end the ASASM console session and access the switch CLI, perform the following steps.
To kill another user’s active connection, which may have been unintentionally left open, see the “Killing an Active Console Connection” section.
Detailed Steps
Step 1![]() To return to the switch CLI, type the following:
To return to the switch CLI, type the following:
You return to the switch prompt:

Note Shift-6 on US and UK keyboards issues the caret (^) character. If you have a different keyboard and cannot issue the caret (^) character as a standalone character, you can temporarily or permanently change the escape character to a different character. Use the terminal escape-character ascii_number command (to change for this session) or the default escape-character ascii_number command (to change permanently). For example, to change the sequence for the current session to Ctrl-w, x, enter terminal escape-character 23.
Killing an Active Console Connection
Because of the persistence of a console connection, if you do not properly log out of the ASASM, the connection may exist longer than intended. If someone else wants to log in, they will need to kill the existing connection.
Detailed Steps
Step 1![]() From the switch CLI, show the connected users using the show users command. A console user is called “con”. The Host address shown is 127.0.0. slot 0, where slot is the slot number of the module.
From the switch CLI, show the connected users using the show users command. A console user is called “con”. The Host address shown is 127.0.0. slot 0, where slot is the slot number of the module.
For example, the following command output shows a user “con” on line 0 on a module in slot 2:
Step 2![]() To clear the line with the console connection, enter the following command:
To clear the line with the console connection, enter the following command:
Logging Out of a Telnet Session
To end the Telnet session and access the switch CLI, perform the following steps.
Detailed Steps
Step 1![]() To return to the switch CLI, type exit from the ASASM privileged or user EXEC mode. If you are in a configuration mode, enter exit repeatedly until you exit the Telnet session.
To return to the switch CLI, type exit from the ASASM privileged or user EXEC mode. If you are in a configuration mode, enter exit repeatedly until you exit the Telnet session.
You return to the switch prompt:

Note You can alternatively escape the Telnet session using the escape sequence Ctrl-Shift-6, x; this escape sequence lets you resume the Telnet session by pressing the Enter key at the switch prompt. To disconnect your Telnet session from the switch, enter disconnect at the switch CLI. If you do not disconnect the session, it will eventually time out according to the ASASM configuration.
Configuring ASDM Access for Appliances
ASDM access requires some minimal configuration so you can communicate over the network with a management interface. This section includes the following topics:
- Using the Pre-login Banner in ASDM
- Accessing ASDM Using the Factory Default Configuration
- Customizing ASDM Access (ASA 5505)
- Customizing ASDM Access (ASA 5510 and Higher)
Using the Pre-login Banner in ASDM
When you first log in to ASDM, a message may appear even if you have not entered the device IP address, your username, and password. Administrators can create a message that appears before users log into ASDM, which is called a pre-login banner. For example:
Click OK to close the dialog box that includes the message. Then re-enter the device IP address, your username, and password to open ASDM.
Accessing ASDM Using the Factory Default Configuration
With a factory default configuration (see the “Factory Default Configurations” section), ASDM connectivity is pre-configured with default network settings. Connect to ASDM using the following interface and network settings:
–![]() ASA 5505—The switch port to which you connect to ASDM can be any port, except for Ethernet 0/0.
ASA 5505—The switch port to which you connect to ASDM can be any port, except for Ethernet 0/0.
–![]() ASA 5510 and higher—The interface to which you connect to ASDM is Management 0/0.
ASA 5510 and higher—The interface to which you connect to ASDM is Management 0/0.
- The default management address is 192.168.1.1.
- The clients allowed to access ASDM must be on the 192.168.1.0/24 network. The default configuration enables DHCP so your management station can be assigned an IP address in this range.
To launch ASDM, see the “Starting ASDM” section.

Note![]() To change to multiple context mode, see the “Enabling or Disabling Multiple Context Mode” section. After changing to multiple context mode, you can access ASDM from the admin context using the network settings above.
To change to multiple context mode, see the “Enabling or Disabling Multiple Context Mode” section. After changing to multiple context mode, you can access ASDM from the admin context using the network settings above.
Customizing ASDM Access (ASA 5505)
Use this procedure if one or more of the following conditions applies:
See also the sample configurations in the “ASA 5505 Default Configuration” section.

Note![]() For routed mode, for quick and easy ASDM access, we recommend applying the factory default configuration with the option to set your own management IP address (see the “Restoring the Factory Default Configuration” section). Use the procedure in this section only if you have special needs such as setting transparent mode, or if you have other configuration that you need to preserve.
For routed mode, for quick and easy ASDM access, we recommend applying the factory default configuration with the option to set your own management IP address (see the “Restoring the Factory Default Configuration” section). Use the procedure in this section only if you have special needs such as setting transparent mode, or if you have other configuration that you need to preserve.
Prerequisites
Access the CLI at the console port according to the “Accessing the Appliance Command-Line Interface” section.
Detailed Steps
|
|
|
|
|---|---|---|
|
|
Enables transparent firewall mode. This command clears your configuration. See the “Setting the Firewall Mode (Single Mode)” section for more information. |
|
| Do one of the following to configure a management interface, depending on your mode: |
||
| ip address ip_address [ mask ] ciscoasa(config)# interface vlan 1 ciscoasa(config-if)# nameif inside |
Configures an interface in routed mode. The security-level is a number between 1 and 100, where 100 is the most secure. |
|
| ip address ip_address [ mask ] ciscoasa(config)# interface bvi 1 ciscoasa(config-if)# ip address 192.168.1.1 255.255.255.0 ciscoasa(config)# interface vlan 1 ciscoasa(config-if)# bridge-group 1 |
Configures a bridge virtual interface and assigns a management VLAN to the bridge group. The security-level is a number between 1 and 100, where 100 is the most secure. |
|
|
ciscoasa(config)# interface ethernet 0/1 |
Enables the management switchport and assigns it to the management VLAN. |
|
dhcpd address ip_address - ip_address ciscoasa(config)# dhcpd address 192.168.1.5-192.168.1.254 inside |
Sets the DHCP pool for the management network. Make sure you do not include the VLAN interface address in the range. Note By default, the IPS module, if installed, uses 192.168.1.2 for its internal management address, so be sure not to use this address in the DHCP range. You can later change the IPS module management address using the ASA if required. |
|
|
|
||
http ip_address mask interface_name |
||
|
|
||
To launch ASDM, see the “Starting ASDM” section. |
||
Examples
The following configuration converts the firewall mode to transparent mode, configures the VLAN 1 interface and assigns it to BVI 1, enables a switchport, and enables ASDM for a management host:
dhcpd address 192.168.1.5-192.168.1.254 inside
Customizing ASDM Access (ASA 5510 and Higher)
Use this procedure if one or more of the following conditions applies:
- You do not have a factory default configuration
- You want to change to transparent firewall mode
- You want to change to multiple context mode

Note![]() For routed, single mode, for quick and easy ASDM access, we recommend applying the factory default configuration with the option to set your own management IP address (see the “Restoring the Factory Default Configuration” section). Use the procedure in this section only if you have special needs such as setting transparent or multiple context mode, or if you have other configuration that you need to preserve.
For routed, single mode, for quick and easy ASDM access, we recommend applying the factory default configuration with the option to set your own management IP address (see the “Restoring the Factory Default Configuration” section). Use the procedure in this section only if you have special needs such as setting transparent or multiple context mode, or if you have other configuration that you need to preserve.
Prerequisites
Access the CLI at the console port according to the “Accessing the Appliance Command-Line Interface” section.
Detailed Steps
|
|
|
|
|---|---|---|
|
|
Enables transparent firewall mode. This command clears your configuration. See the “Setting the Firewall Mode (Single Mode)” section for more information. |
|
|
ciscoasa(config)# interface management 0/0 ciscoasa(config-if)# nameif management ciscoasa(config-if)# security-level 100 |
Configures the Management 0/0 interface. The security-level is a number between 1 and 100, where 100 is the most secure. |
|
dhcpd address ip_address - ip_address ciscoasa(config)# dhcpd address 192.168.1.2-192.168.1.254 management |
Sets the DHCP pool for the management network. Make sure you do not include the Management 0/0 address in the range. |
|
| route management_ifc management_host_ip mask gateway_ip 1 ciscoasa(config)# route management 10.1.1.0 255.255.255.0 192.168.1.50 |
||
|
|
||
http ip_address mask interface_name |
||
|
|
||
|
|
Sets the mode to multiple mode. When prompted, confirm that you want to convert the existing configuration to be the admin context. You are then prompted to reload the ASASM. See “Configuring Multiple Context Mode,” for more information. |
|
To launch ASDM, see the “Starting ASDM” section. |
Examples
The following configuration converts the firewall mode to transparent mode, configures the Management 0/0 interface, and enables ASDM for a management host:
dhcpd address 192.168.1.2-192.168.1.254 management
Configuring ASDM Access for the ASA Services Module
Because the ASASM does not have physical interfaces, it does not come pre-configured for ASDM access; you must configure ASDM access using the CLI on the ASASM. To configure the ASASM for ASDM access, perform the following steps.
Prerequisites
- Assign a VLAN interface to the ASASM according to the “Assigning VLANs to the ASA Services Module” section.
- Connect to the ASASM and access global configuration mode according to the “Accessing the ASA Services Module Command-Line Interface” section.
Detailed Steps
|
|
|
|
|---|---|---|
|
|
Enables transparent firewall mode. This command clears your configuration. See the “Setting the Firewall Mode (Single Mode)” section for more information. |
|
| Do one of the following to configure a management interface, depending on your mode: |
||
| ip address ip_address [ mask ] ciscoasa(config)# interface vlan 1 ciscoasa(config-if)# ip address 192.168.1.1 255.255.255.0 |
Configures an interface in routed mode. The security-level is a number between 1 and 100, where 100 is the most secure. |
|
| ip address ip_address [ mask ] ciscoasa(config)# interface bvi 1 ciscoasa(config-if)# ip address 192.168.1.1 255.255.255.0 ciscoasa(config)# interface vlan 1 ciscoasa(config-if)# bridge-group 1 |
Configures a bridge virtual interface and assigns a management VLAN to the bridge group. The security-level is a number between 1 and 100, where 100 is the most secure. |
|
(For directly-connected management hosts) dhcpd address ip_address - ip_address ciscoasa(config)# dhcpd address 192.168.1.2-192.168.1.254 inside |
Enables DHCP for the management host on the management interface network. Make sure you do not include the management address in the range. |
|
| route management_ifc management_host_ip mask gateway_ip 1 ciscoasa(config)# route management 10.1.1.0 255.255.255.0 192.168.1.50 |
||
|
|
||
http ip_address mask interface_name |
||
|
|
||
|
|
Sets the mode to multiple mode. When prompted, confirm that you want to convert the existing configuration to be the admin context. You are then prompted to reload the ASASM. See “Configuring Multiple Context Mode,” for more information. |
|
To launch ASDM, see the “Starting ASDM” section. |
||
Examples
The following routed mode configuration configures the VLAN 1 interface and enables ASDM for a management host:
dhcpd address 192.168.1.3-192.168.1.254 inside
http 192.168.1.0 255.255.255.0 inside
The following configuration converts the firewall mode to transparent mode, configures the VLAN 1 interface and assigns it to BVI 1, and enables ASDM for a management host:
dhcpd address 192.168.1.3-192.168.1.254 inside
Starting ASDM
You can start ASDM using two methods:
- ASDM-IDM Launcher—The Launcher is an application downloaded from the ASA using a web browser that you can use to connect to any ASA IP address. You do not need to re-download the launcher if you want to connect to other ASAs. The Launcher also lets you run a virtual ASDM in Demo mode using files downloaded locally.
- Java Web Start—For each ASA that you manage, you need to connect with a web browser and then save or launch the Java Web Start application. You can optionally save the application to your PC; however you need separate applications for each ASA IP address.

Note![]() Within ASDM, you can choose a different ASA IP address to manage; the difference between the Launcher and Java Web Start application functionality rests primarily in how you initially connect to the ASA and launch ASDM.
Within ASDM, you can choose a different ASA IP address to manage; the difference between the Launcher and Java Web Start application functionality rests primarily in how you initially connect to the ASA and launch ASDM.
This section describes how to connect to ASDM initially, and then launch ASDM using the Launcher or the Java Web Start application. This section includes the following topics:
- Connecting to ASDM for the First Time
- Starting ASDM from the ASDM-IDM Launcher
- Starting ASDM from the Java Web Start Application
- Using ASDM in Demo Mode

Note![]() ASDM allows multiple PCs or workstations to each have one browser session open with the same ASA software. A single ASA can support up to five concurrent ASDM sessions in single, routed mode. Only one session per browser per PC or workstation is supported for a specified ASA. In multiple context mode, five concurrent ASDM sessions are supported per context, up to a maximum of 32 total connections for each ASA.
ASDM allows multiple PCs or workstations to each have one browser session open with the same ASA software. A single ASA can support up to five concurrent ASDM sessions in single, routed mode. Only one session per browser per PC or workstation is supported for a specified ASA. In multiple context mode, five concurrent ASDM sessions are supported per context, up to a maximum of 32 total connections for each ASA.
Connecting to ASDM for the First Time
To connect to ASDM for the first time to download the ASDM-IDM Launcher or Java Web Start application, perform the following steps:
Step 1![]() From a supported web browser on the ASA network, enter the following URL:
From a supported web browser on the ASA network, enter the following URL:
Where interface_ip_address is the management IP address of the ASA, by default 192.168.1.2. See the “Configuring ASDM Access for Appliances” section or the “Configuring ASDM Access for the ASA Services Module” section for more information about management access.
See the ASDM release notes for your release for the requirements to run ASDM.
The ASDM launch page appears with the following buttons:
Step 2![]() To download the Launcher:
To download the Launcher:
a.![]() Click Install ASDM Launcher and Run ASDM .
Click Install ASDM Launcher and Run ASDM .
b.![]() Enter the username and password, and click OK . For a factory default configuration, leave these fields empty. With no HTTPS authentication configured, you can gain access to ASDM with no username and the enable password, which is blank by default. With HTTPS authentication enabled, enter your username and associated password.
Enter the username and password, and click OK . For a factory default configuration, leave these fields empty. With no HTTPS authentication configured, you can gain access to ASDM with no username and the enable password, which is blank by default. With HTTPS authentication enabled, enter your username and associated password.
c.![]() Save the installer to your PC, and then start the installer. The ASDM-IDM Launcher opens automatically after installation is complete.
Save the installer to your PC, and then start the installer. The ASDM-IDM Launcher opens automatically after installation is complete.
d.![]() See the “Starting ASDM from the ASDM-IDM Launcher” section to use the Launcher to connect to ASDM.
See the “Starting ASDM from the ASDM-IDM Launcher” section to use the Launcher to connect to ASDM.
Step 3![]() To use the Java Web Start application:
To use the Java Web Start application:
a.![]() Click Run ASDM or Run Startup Wizard .
Click Run ASDM or Run Startup Wizard .
b.![]() Save the application to your PC when prompted. You can optionally open it instead of saving it.
Save the application to your PC when prompted. You can optionally open it instead of saving it.
c.![]() See the “Starting ASDM from the Java Web Start Application” section to use the Java Web Start application to connect to ASDM.
See the “Starting ASDM from the Java Web Start Application” section to use the Java Web Start application to connect to ASDM.
Starting ASDM from the ASDM-IDM Launcher
To start ASDM from the ASDM-IDM Launcher, perform the following steps.
Prerequisites
Download the ASDM-IDM Launcher according to the “Connecting to ASDM for the First Time” section.
Detailed Steps
Step 1![]() Start the ASDM-IDM Launcher application.
Start the ASDM-IDM Launcher application.
Step 2![]() Enter or choose the ASA IP address or hostname to which you want to connect. To clear the list of IP addresses, click the trash can icon next to the Device/IP Address/Name field.
Enter or choose the ASA IP address or hostname to which you want to connect. To clear the list of IP addresses, click the trash can icon next to the Device/IP Address/Name field.
Step 3![]() Enter your username and your password, and then click OK .
Enter your username and your password, and then click OK .
For a factory default configuration, leave these fields empty. With no HTTPS authentication configured, you can gain access to ASDM with no username and the enable password, which is blank by default. With HTTPS authentication enabled, enter your username and associated password.
If there is a new version of ASDM on the ASA, the ASDM Launcher automatically downloads the new version and requests that you update the current version before starting ASDM.
Starting ASDM from the Java Web Start Application
To start ASDM from the Java Web Start application, perform the following steps.
Prerequisites
Download the Java Web Start application according to the “Connecting to ASDM for the First Time” section.
Detailed Steps
Step 1![]() Start the Java Web Start application.
Start the Java Web Start application.
Step 2![]() Accept any certificates according to the dialog boxes that appear. The Cisco ASDM-IDM Launcher appears.
Accept any certificates according to the dialog boxes that appear. The Cisco ASDM-IDM Launcher appears.
Step 3![]() Enter the username and password, and click OK . For a factory default configuration, leave these fields empty. With no HTTPS authentication configured, you can gain access to ASDM with no username and the enable password, which is blank by default. With HTTPS authentication enabled, enter your username and associated password.
Enter the username and password, and click OK . For a factory default configuration, leave these fields empty. With no HTTPS authentication configured, you can gain access to ASDM with no username and the enable password, which is blank by default. With HTTPS authentication enabled, enter your username and associated password.
Using ASDM in Demo Mode
The ASDM Demo Mode, a separately installed application, lets you run ASDM without having a live device available. In this mode, you can do the following:
- Perform configuration and selected monitoring tasks via ASDM as though you were interacting with a real device.
- Demonstrate ASDM or ASA features using the ASDM interface.
- Perform configuration and monitoring tasks with the CSC SSM.
- Obtain simulated monitoring and logging data, including real-time syslog messages. The data shown is randomly generated; however, the experience is identical to what you would see when you are connected to a real device.
This mode has been updated to support the following features:
- For global policies, an ASA in single, routed mode and intrusion prevention
- For object NAT, an ASA in single, routed mode and a firewall DMZ.
- For the Botnet Traffic Filter, an ASA in single, routed mode and security contexts.
- Site-to-Site VPN with IPv6 (Clientless SSL VPN and IPsec VPN)
- Promiscuous IDS (intrusion prevention)
- Unified Communication Wizard
This mode does not support the following:
- Saving changes made to the configuration that appear in the GUI.
- File or disk operations.
- Historical monitoring data.
- Non-administrative users.
- These features:
Save Running Configuration to Flash
Save Running Configuration to TFTP Server
Save Running Configuration to Standby Unit
Save Internal Log Buffer to Flash
–![]() Configuration > Interface > Edit Interface > Renew DHCP Lease
Configuration > Interface > Edit Interface > Renew DHCP Lease
–![]() Configuring a standby device after failover
Configuring a standby device after failover
- Operations that cause a rereading of the configuration, in which the GUI reverts to the original configuration:
–![]() Making changes in the Interface pane
Making changes in the Interface pane
To run ASDM in Demo Mode, perform the following steps:
Step 1![]() Download the ASDM Demo Mode installer, asdm-demo- version .msi, from the following location: http://www.cisco.com/cisco/web/download/index.html.
Download the ASDM Demo Mode installer, asdm-demo- version .msi, from the following location: http://www.cisco.com/cisco/web/download/index.html.
Step 2![]() Double-click the installer to install the software.
Double-click the installer to install the software.
Step 3![]() Double-click the Cisco ASDM Launcher shortcut on your desktop, or open it from the Start menu.
Double-click the Cisco ASDM Launcher shortcut on your desktop, or open it from the Start menu.
Step 4![]() Check the Run in Demo Mode check box.
Check the Run in Demo Mode check box.
Installing an Identity Certificate for ASDM
When using Java 7 update 51 and later, the ASDM Launcher requires a trusted certificate. An easy approach to fulfill the certificate requirements is to install a self-signed identity certificate. You can use Java Web Start to launch ASDM until you install a certificate.
See the following document to install a self-signed identity certificate on the ASA for use with ASDM, and to register the certificate with Java.
Factory Default Configurations
The factory default configuration is the configuration applied by Cisco to new ASAs.
- ASA 5505—The factory default configuration configures interfaces and NAT so that the ASA is ready to use in your network immediately.
- ASA 5510 and higher—The factory default configuration configures an interface for management so you can connect to it using ASDM, with which you can then complete your configuration.
The factory default configuration is available only for routed firewall mode and single context mode. See “Configuring Multiple Context Mode,” for more information about multiple context mode. See “Configuring the Transparent or Routed Firewall,” for more information about routed and transparent firewall mode. For the ASA 5505, a sample transparent mode configuration is provided in this section.

Note![]() In addition to the image files and the (hidden) default configuration, the following folders and files are standard in flash memory: log/, crypto_archive/, and coredumpinfo/coredump.cfg. The date on these files may not match the date of the image files in flash memory. These files aid in potential troubleshooting; they do not indicate that a failure has occurred.
In addition to the image files and the (hidden) default configuration, the following folders and files are standard in flash memory: log/, crypto_archive/, and coredumpinfo/coredump.cfg. The date on these files may not match the date of the image files in flash memory. These files aid in potential troubleshooting; they do not indicate that a failure has occurred.
This section includes the following topics:
- Restoring the Factory Default Configuration
- ASA 5505 Default Configuration
- ASA 5510 and Higher Default Configuration
Restoring the Factory Default Configuration
This section describes how to restore the factory default configuration.

Note![]() On the ASASM, restoring the factory default configuration simply erases the configuration; there is no factory default configuration.
On the ASASM, restoring the factory default configuration simply erases the configuration; there is no factory default configuration.
Limitations
This feature is available only in routed firewall mode; transparent mode does not support IP addresses for interfaces. In addition, this feature is available only in single context mode; an ASA with a cleared configuration does not have any defined contexts to configure automatically using this feature.
Detailed Steps
Step 1![]() In the main ASDM application window, choose File > Reset Device to the Factory Default Configuration .
In the main ASDM application window, choose File > Reset Device to the Factory Default Configuration .
The Reset Device to the Default Configuration dialog box appears.
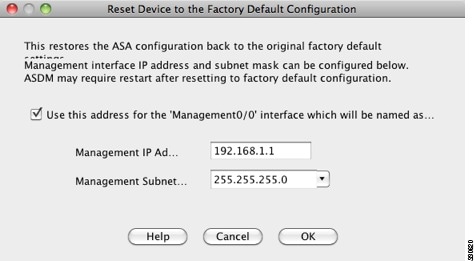
Step 2![]() (Optional) Enter the Management IP address of the management interface, instead of using the default address, 192.168.1.1. (For an ASA with a dedicated management interface, the interface is called “Management0/0.”)
(Optional) Enter the Management IP address of the management interface, instead of using the default address, 192.168.1.1. (For an ASA with a dedicated management interface, the interface is called “Management0/0.”)
Step 3![]() (Optional) Choose the Management Subnet Mask from the drop-down list.
(Optional) Choose the Management Subnet Mask from the drop-down list.
A confirmation dialog box appears.
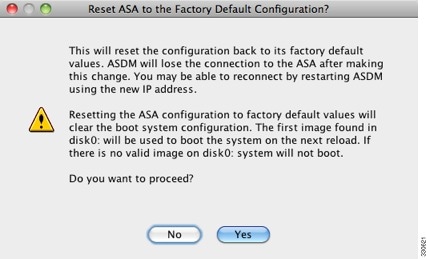

Note This action also clears the location of the boot image location, if present, along with the rest of the configuration. The Configuration > Device Management > System Image/Configuration > Boot Image/Configuration pane lets you boot from a specific image, including an image on the external memory. The next time you reload the ASA after restoring the factory configuration, it boots from the first image in internal flash memory; if you do not have an image in internal flash memory, the ASA does not boot.
Step 6![]() After you restore the default configuration, save this configuration to internal flash memory. Choose File > Save Running Configuration to Flash .
After you restore the default configuration, save this configuration to internal flash memory. Choose File > Save Running Configuration to Flash .
Choosing this option saves the running configuration to the default location for the startup configuration, even if you have previously configured a different location. When the configuration was cleared, this path was also cleared.
What to Do Next
See the “Getting Started with the Configuration” section to start configuring the ASA.
ASA 5505 Default Configuration
The default configuration is available for routed mode only. This section describes the default configuration and also provides a sample transparent mode configuration that you can copy and paste as a starting point. This section includes the following topics:
ASA 5505 Routed Mode Default Configuration
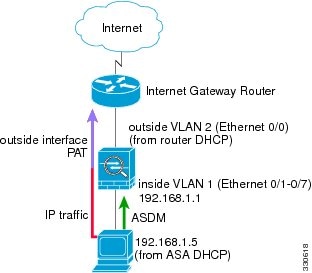
The default factory configuration for the ASA 5505 configures the following:
- Interfaces—Inside (VLAN 1) and outside (VLAN 2).
- Switchports enabled and assigned—Ethernet 0/1 through 0/7 switch ports assigned to inside. Ethernet 0/0 assigned to outside.
- IP addresses— Outside address from DHCP; inside address set manually to 192.168.1.1/24.
- Network address translation (NAT)—All inside IP addresses are translated when accessing the outside using interface PAT.
- Traffic flow—IPv4 and IPv6 traffic allowed from inside to outside (this behavior is implicit on the ASA). Outside users are prevented from accessing the inside.
- DHCP server—Enabled for inside hosts, so a PC connecting to the inside interface receives an address between 192.168.1.5 and 192.168.1.254. DNS, WINS, and domain information obtained from the DHCP client on the outside interface is passed to the DHCP clients on the inside interface.
- Default route—Derived from DHCP.
- ASDM access—Inside hosts allowed.
Figure 3-1 ASA 5505 Routed Mode
The configuration consists of the following commands:

Note For testing purposes, you can allow ping from inside to outside by enabling ICMP inspection. Add the following commands to the default configuration:
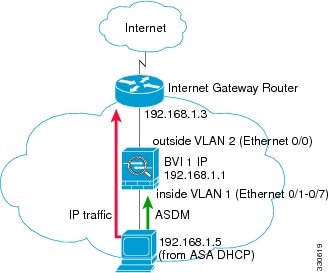
ASA 5505 Transparent Mode Sample Configuration
When you change the mode to transparent mode, the configuration is erased. You can copy and paste the following sample configuration at the CLI to get started. This configuration uses the default configuration as a starting point. Note the following areas you may need to modify:
- IP addresses—The IP addresses configured should be changed to match the network to which you are connecting.
- Static routes—For some kinds of traffic, static routes are required. See the “MAC Address vs. Route Lookups” section.
Figure 3-2 ASA 5505 Transparent Mode

Note For testing purposes, you can allow ping from inside to outside by enabling ICMP inspection. Add the following commands to the sample configuration:
ASA 5510 and Higher Default Configuration
The default factory configuration for the ASA 5510 and higher configures the following:
- Management interface—Management 0/0 (management).
- IP address—The management address is 192.168.1.1/24.
- DHCP server—Enabled for management hosts, so a PC connecting to the management interface receives an address between 192.168.1.2 and 192.168.1.254.
- ASDM access—Management hosts allowed.
The configuration consists of the following commands:
Getting Started with the Configuration
To configure and monitor the ASA, perform the following steps:
Step 1![]() For initial configuration using the Startup Wizard, choose Wizards > Startup Wizard .
For initial configuration using the Startup Wizard, choose Wizards > Startup Wizard .
Step 2![]() To use the IPsec VPN Wizard to configure IPsec VPN connections, choose Wizards > IPsec VPN Wizard and complete each screen that appears.
To use the IPsec VPN Wizard to configure IPsec VPN connections, choose Wizards > IPsec VPN Wizard and complete each screen that appears.
Step 3![]() To use the SSL VPN Wizard to configure SSL VPN connections, choose Wizards > SSL VPN Wizard and complete each screen that appears.
To use the SSL VPN Wizard to configure SSL VPN connections, choose Wizards > SSL VPN Wizard and complete each screen that appears.
Step 4![]() To configure high availability and scalability settings, choose Wizards > High Availability and Scalability Wizard .
To configure high availability and scalability settings, choose Wizards > High Availability and Scalability Wizard .
Step 5![]() To use the Packet Capture Wizard to configure packet capture, choose Wizards > Packet Capture Wizard .
To use the Packet Capture Wizard to configure packet capture, choose Wizards > Packet Capture Wizard .
Step 6![]() To display different colors and styles available in the ASDM GUI, choose View > Office Look and Feel .
To display different colors and styles available in the ASDM GUI, choose View > Office Look and Feel .
Step 7![]() To configure features, click the Configuration button on the toolbar and then click one of the feature buttons to display the associated configuration pane.
To configure features, click the Configuration button on the toolbar and then click one of the feature buttons to display the associated configuration pane.

Note![]() If the Configuration screen is blank, click Refresh on the toolbar to display the screen content.
If the Configuration screen is blank, click Refresh on the toolbar to display the screen content.
Step 8![]() To monitor the ASA, click the Monitoring button on the toolbar and then click a feature button to display the associated monitoring pane.
To monitor the ASA, click the Monitoring button on the toolbar and then click a feature button to display the associated monitoring pane.

Note![]() ASDM supports up to a maximum of a 512 KB configuration. If you exceed this amount, you may experience performance issues.
ASDM supports up to a maximum of a 512 KB configuration. If you exceed this amount, you may experience performance issues.
Using the Command Line Interface Tool in ASDM
This section tells how to enter commands using ASDM, and how to work with the CLI. This section includes the following topics:
- Using the Command Line Interface Tool
- Handling Command Errors
- Using Interactive Commands
- Avoiding Conflicts with Other Administrators
- Showing Commands Ignored by ASDM on the Device
Using the Command Line Interface Tool
This feature provides a text-based tool for sending commands to the ASA and viewing the results.
The commands you can enter with the CLI tool depend on your user privileges. See the “Authorization” section for more information . Review your privilege level in the status bar at the bottom of the main ASDM application window to ensure that you have the required privileges to execute privileged-level CLI commands.

Note![]() Commands entered via the ASDM CLI tool might function differently from those entered through a terminal connection to the ASA.
Commands entered via the ASDM CLI tool might function differently from those entered through a terminal connection to the ASA.
To use the CLI tool, perform the following steps:
Step 1![]() In the main ASDM application window, choose Tools > Command Line Interface .
In the main ASDM application window, choose Tools > Command Line Interface .
The Command Line Interface dialog box appears.
Step 2![]() Choose the type of command (single line or multiple line) that you want, and then choose the command from the drop-down list, or type it in the field provided.
Choose the type of command (single line or multiple line) that you want, and then choose the command from the drop-down list, or type it in the field provided.
Step 3![]() Click Send to execute the command.
Click Send to execute the command.
Step 4![]() To enter a new command, click Clear Response , and then choose (or type) another command to execute.
To enter a new command, click Clear Response , and then choose (or type) another command to execute.
Step 5![]() Check the Enable context-sensitive help (?) check box to provide context-sensitive help for this feature. Uncheck this check box to disable the context-sensitive help.
Check the Enable context-sensitive help (?) check box to provide context-sensitive help for this feature. Uncheck this check box to disable the context-sensitive help.
Step 6![]() After you have closed the Command Line Interface dialog box, if you changed the configuration, click Refresh to view the changes in ASDM.
After you have closed the Command Line Interface dialog box, if you changed the configuration, click Refresh to view the changes in ASDM.
Handling Command Errors
If an error occurs because you entered an incorrect command, the incorrect command is skipped and the remaining commands are processed. A message appears in the Response area to inform you whether or not any error occurred, as well as other related information.

Note![]() ASDM supports almost all CLI commands. See the command reference for a list of commands.
ASDM supports almost all CLI commands. See the command reference for a list of commands.
Using Interactive Commands
Interactive commands are not supported in the CLI tool. To use these commands in ASDM, use the noconfirm keyword if available, as shown in the following command:
Avoiding Conflicts with Other Administrators
Multiple administrative users can update the running configuration of the ASA. Before using the ASDM CLI tool to make configuration changes, check for other active administrative sessions. If more than one user is configuring the ASA at the same time, the most recent changes take effect.
To view other administrative sessions that are currently active on the same ASA, choose Monitoring > Properties > Device Access .
Showing Commands Ignored by ASDM on the Device
This feature lets you show the list of commands that ASDM does not support. Typically, ASDM ignores them. ASDM does not change or remove these commands from your running configuration. See the “Unsupported Commands” section for more information.
To display the list of unsupported commands for ASDM, perform the following steps:
Step 1![]() In the main ASDM application window, choose Tools > Show Commands Ignored by ASDM on Device .
In the main ASDM application window, choose Tools > Show Commands Ignored by ASDM on Device .
Step 2![]() Click OK when you are done.
Click OK when you are done.
Applying Configuration Changes to Connections
When you make security policy changes to the configuration, all new connections use the new security policy. Existing connections continue to use the policy that was configured at the time of the connection establishment. show command output for old connections reflect the old configuration, and in some cases will not include data about the old connections.
For example, if you remove a QoS service-policy from an interface, then re-add a modified version, then the show service-policy command only displays QoS counters associated with new connections that match the new service policy; existing connections on the old policy no longer show in the command output.
To ensure that all connections use the new policy, you need to disconnect the current connections so they can reconnect using the new policy.
To disconnect connections, enter one of the following commands.
 Feedback
Feedback