L3Out Template Overview
Beginning with release 4.1(1), Nexus Dashboard Orchestrator (NDO) introduced a number of new policies for creating and configuring L3Out for Cisco ACI fabrics, as well as a new template type specifically for IP-based L3Out and SR-MPLS VRF L3Out configurations.
As you may already know, prior releases of NDO provided the ability to create an L3Out object in Application templates that allowed you to create an L3Out and deploy it to your site. However, the actual L3Out configurations had to be done manually by logging in to the sites' controllers (Cisco APIC) and providing the details for each L3Out individually.
With release 4.1(1), the entire configuration of L3Outs and SR-MPLS L3Outs (including nodes, interfaces, and other settings) can be done directly in NDO and deployed to all fabrics in your Multi-Site domain. To achieve this, a new L3Out-specific template type has been added to contain the L3Out and SR-MPLS VRF L3Out configurations. Similar to Application templates, L3Out templates have a one-to-one association with tenants but unlike Application templates, an L3Out template must be associated to a single site only.
 Note |
The legacy L3Out objects in the Application templates remain functional for backward compatibility. However, if you want to define specific L3Out and SR-MPLS L3Out settings from NDO, you must use the new L3Out template type. The legacy SR-MPLS VRF L3Out object has been removed from the Application template and all SR-MPLS VRF L3Out configurations must be now done using the L3Out-specific template. The SR-MPLS Infra L3Out configuration is still performed as part of the site connectivity provisioning workflow. |
Templates and Policy Objects Dependencies
The following diagram illustrates the template and policy hierarchy across multiple templates that's required for defining a complete L3Out configuration:-
The VRF used by the L3Out and the External EPGs that are associated to the L3Out continue to be defined in the Application templates.
-
Node or interface routing policies, BGP peer prefix, and IP SLA policies are now defined in the Tenant Policy template.
These policies are used by the L3Out-specific template and the policies defined in that template as described in the following bullet point.
-
For IP-based L3Outs, the template includes the following:
-
Routing Protocol (BGP/OSPF), VRF, L3 Domain and Route Maps for route control.
-
Border leaf switches (nodes) where to deploy the L3Out routing protocol and node-level protocol configurations.
-
Border leaf switch interfaces where to deploy the L3Out routing protocol and interface-level protocol configurations.
-
Node- and interface-level common configuration using Node/Interface Group policies.
Node Group configuration includes BGP peers for loopback interfaces, BFD multi-hop settings, and association with Node Routing Group Policy described below.
Interface Group configuration includes OSPF and BFD protocol settings and association with Interface Routing Group Policy described below.
These policies consume policies defined in Tenant Policy templates mentioned in the previous bullet point. For example, the node and interface group policies require the node and interface routing policies defined in the Tenant Policy templates
-
-
For SR-MPLS VRF L3Outs, the template allows you to define labels and import/export route maps for route control.

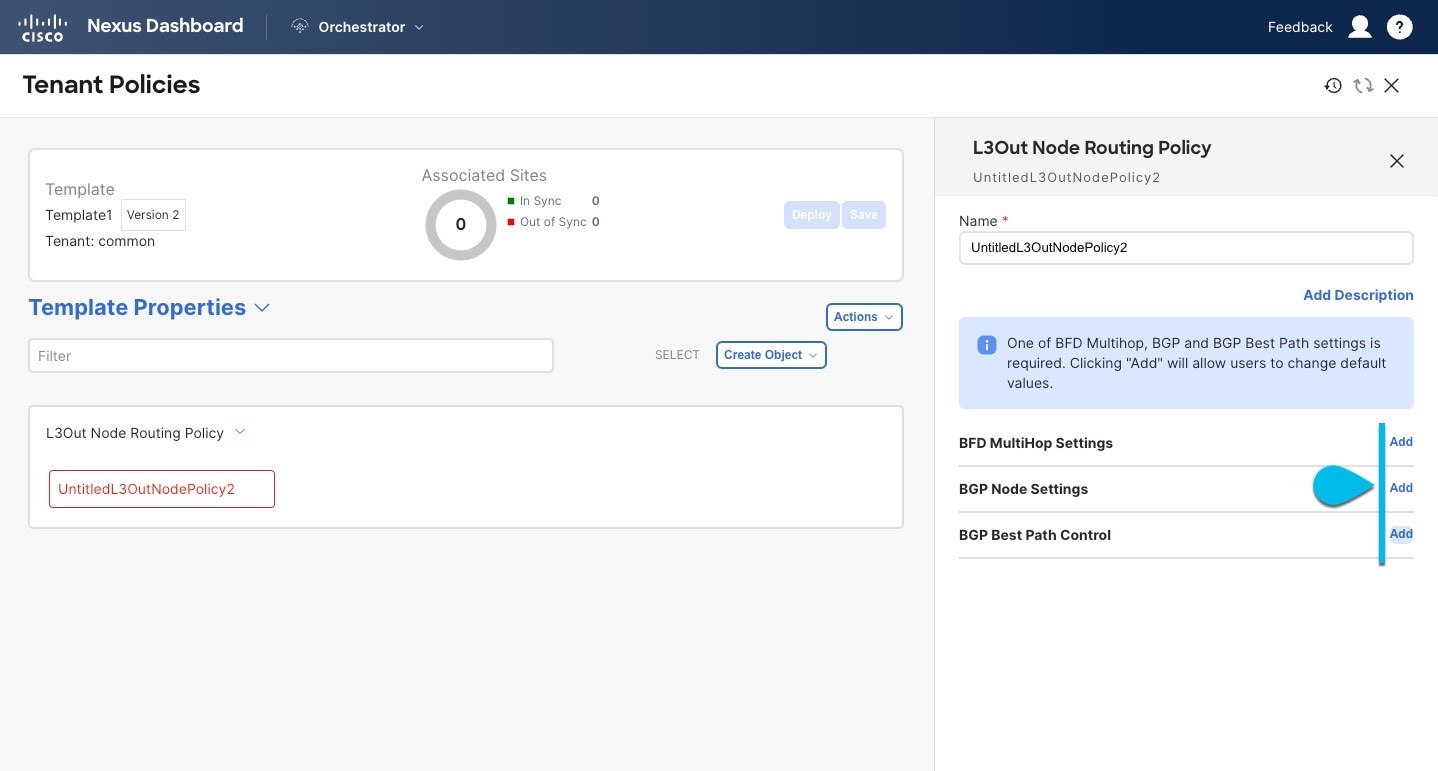
Tenant Policy Template: Node Routing Group Policy
The Node Routing Policy in Tenant Policy template is a set of protocol policies that can be applied at a node or border leaf level and can be used by node group policies in L3Out template. It includes the following 3 settings:
-
BFD MultiHop Settings – specifies BFD parameters for BFD sessions established between devices on interfaces that are not directly connected.
-
BGP Node Settings – allows you to configure BGP protocol timer and sessions settings for BGP adjacencies between BGP peers.
-
BGP Best Path Control – enables
as-path multipath-relax, which allows load-balancing between multiple paths received from different BGP ASN.
This policy is configured and deployed using Tenant Policy templates and is used by the L3Outs configured in L3Out templates.
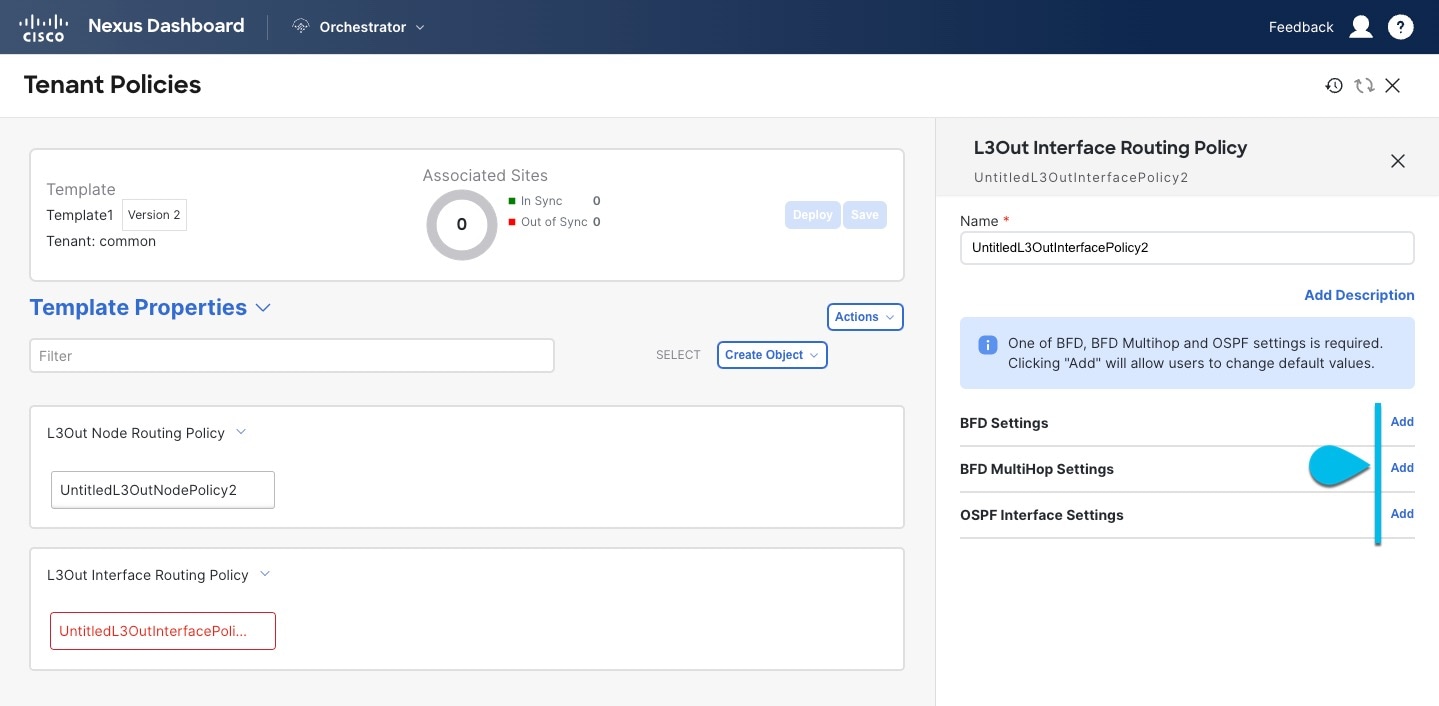
Tenant Policy Template: Interface Routing Group Policy
The Interface Routing Policy in Tenant Policy template is a set of policies that can be applied at an interface level and can be used by interface group policies in L3Out template. It includes the following 3 settings:
-
BFD Settings – specifies BFD parameters for BFD sessions established between devices on interfaces that are directly connected.
When multiple protocols are enabled between a pair of routers, each protocol has its own link failure detection mechanism, which may have different timeouts. BFD provides a consistent timeout for all protocols to allow consistent and predictable convergence times.
-
BFD MultiHop Settings – specifies BFD parameters for BFD sessions established between devices on interfaces that are not directly connected.
You can configure these settings at the node level as mentioned in the "Tenant Policy Template: Node Routing Group Policy" section above, in which case the interfaces inherit those settings, or you can overwrite the node-level settings for individual interfaces in the Interface Routing group policy.

Note
BFD multi-hop configuration requires Cisco APIC release 5.0(1) or later.
-
OSPF Interface Settings – allows you to configure interface-level settings such as OSPF network type, priority, cost, intervals and controls.

Note
This policy must be created when deploying an L3Out with OSPF.
This policy is configured and deployed using Tenant Policy templates and is used by the L3Outs configured in L3Out templates.
Tenant Policy Template: Individual Policies
In addition to the group policies described above, the Tenant Policy templates also contain the following individual policies related to L3Out configuration:
-
BGP peer prefix policy – defines how many prefixes can be received from a neighbor and what action to take when the number of the allowed prefixes is exceeded.
This policy is configured and deployed using Tenant Policy templates and is used by the L3Outs configured in L3Out templates.
-
IP SLA monitoring policy – defines the type of probe (ICMP/TCP/HTTP) and respective settings to use for monitoring endpoints. This policy is associated with monitoring probe profiles known as "track members", which represent a network segment to be monitored. You can associate an IP SLA monitoring policy to a track list (which includes multiple track members) and associate this track list to a Static Route for monitoring availability of track list members over the route. In addition, you can associate IP SLA monitoring policy directly to next-hop address of a Static Route for monitoring its availability over the route.

Note
IP SLA monitoring policy of HTTP type requires Cisco APIC release 5.1(3) or later.
-
IP SLA track list - defines the IP addresses to be tracked, IP SLA Monitoring policy (probe frequency and type), and scope (bridge domain or L3Out). IP SLA track list aggregates one or more track members, defines what percentage or weight of track members must be
up/downfor the route to be considered available or unavailable. Based on the track list, the available routes remain in the routing table and the unavailable routes are removed until the track list recovers.This policy is configured and deployed using Tenant Policy templates and is used by the L3Outs configured in L3Out templates. In addition, an IP SLA track list can be configured in the same Tenant Policy template as the monitoring policy and consumed by it.
L3Out Template
The L3Outs defined in L3Out templates allow you to define all the required configurations to enable connectivity from the endpoints inside your ACI fabrics to outside network domains through routing protocols or static routes. The L3Out object in NDO contains settings necessary for the following:
-
Learning external routes via routing protocols or static routes.
-
Distribution of the learned external routes to other leaf switches.
-
Advertisement of ACI internal routes (BD subnets) to the outside networks.
-
Advertisement of learned external routes to other L3Outs (transit routing).
When you create an L3Out template and configure L3Out-specific objects and properties as described later in Creating L3Out Template, you will:
-
Define a number of common properties, such as the VRF, L3 Domain, and routing protocol (BGP and/or OSPF), for the L3Out.
-
Specify one or more border leaf switches (nodes) and optionally associate each node with a Node Group policy .
-
Specify one or more interfaces on those border leaf switches and optionally associate each interface with an Interface Group policy described above.
-
After you have created an L3Out template and deployed one or more L3Outs (and their associated External EPGs, defined inside Application templates), you can control traffic between the ACI EPGs and external networks using contracts in Application templates as you typically would.


















 Feedback
Feedback